A small, surgical fix to the Linux kernel’s ROMFS loader was published this month after syzbot detected a mount-time path that could leave the kernel trying to perform I/O with an oversized block size and trigger a BUG that crashes the system; the issue is tracked as CVE-2026-23238 and has been patched upstream and backported into stable trees. (nvd.nist.gov) (spinics.net)
ROMFS (Read-Only Memory File System) is a tiny, simple read-only filesystem included in the Linux kernel for embedded and constrained environments. It deliberately implements a minimal superblock and block handling path to keep the code small and reliable, but that minimalism also means defensive checks must be explicit and correct.
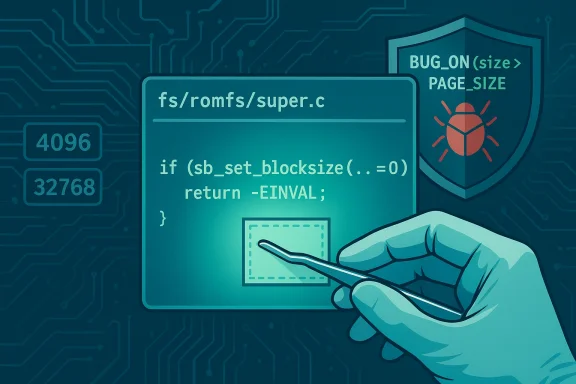
The recently assigned CVE-2026-23238 addresses a missing return-value check in romfs_fill_super(): the code previously called sb_set_blocksize() and ignored the return value. If the blocksize change failed — for example because the underlying block device reported an incompatible logical block size — the superblock could end up left with an unexpected, oversized block size. Later I/O using that oversized block size can hit an assertion in buffer management (BUG_ON(size > PAGE_SIZE)), which produces a kernel BUG and a panic/crash. (spinics.net) (nvd.nist.gov)
In plain terms: romfs assumed it could force a 4 KiB block size when mounting, but on some devices the device’s logical block size can be larger (for example 32 KiB), and if the kernel did not detect that sb_set_blocksize() failed it would continue as if everything were normal — with catastrophic results when the buffer subsystem rejects an I/O size larger than a page. The upstream patch adds an explicit check for sb_set_blocksize() and returns -EINVAL on failure, preventing the mount from proceeding into the faulty state. (spinics.net)
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
ROMFS (Read-Only Memory File System) is a tiny, simple read-only filesystem included in the Linux kernel for embedded and constrained environments. It deliberately implements a minimal superblock and block handling path to keep the code small and reliable, but that minimalism also means defensive checks must be explicit and correct.The recently assigned CVE-2026-23238 addresses a missing return-value check in romfs_fill_super(): the code previously called sb_set_blocksize() and ignored the return value. If the blocksize change failed — for example because the underlying block device reported an incompatible logical block size — the superblock could end up left with an unexpected, oversized block size. Later I/O using that oversized block size can hit an assertion in buffer management (BUG_ON(size > PAGE_SIZE)), which produces a kernel BUG and a panic/crash. (spinics.net) (nvd.nist.gov)
In plain terms: romfs assumed it could force a 4 KiB block size when mounting, but on some devices the device’s logical block size can be larger (for example 32 KiB), and if the kernel did not detect that sb_set_blocksize() failed it would continue as if everything were normal — with catastrophic results when the buffer subsystem rejects an I/O size larger than a page. The upstream patch adds an explicit check for sb_set_blocksize() and returns -EINVAL on failure, preventing the mount from proceeding into the faulty state. (spinics.net)
What the bug is (technical anatomy)
The API and the mistake
- sb_set_blocksize(struct super_block *sb, int size) attempts to set the filesystem's block size and returns non-zero on success; it can fail if the requested block size is incompatible with the block device (bdev_validate_blocksize).
- romfs_fill_super() previously called sb_set_blocksize(sb, ROMBSIZE) (where ROMBSIZE is 4096) but did not check the function’s return value. That omission means folio/buffer I/O later used sb->s_blocksize that could still reflect the block device’s (larger) logical block size. (spinics.net)
How the failure sequence looks, step by step
- An attacker or local operator configures a loop block device with a large logical block size — for example 32 KiB — using LOOP_SET_BLOCK_SIZE ioctl. This is a known and supported ioctl for loop devices and is what syzbot used to trigger the condition. (spinics.net)
- A ROMFS image is mounted onto that device. romfs_fill_super() calls sb_set_blocksize(sb, ROMBSIZE) to set a 4 KiB block size expectation.
- bdev_validate_blocksize() rejects the smaller requested size because the device’s logical block size is larger; sb_set_blocksize() therefore fails and returns 0.
- Because romfs ignored the return value, the superblock’s block size remains the device’s larger logical block size (for example 32 KiB).
- Later, sb_bread() or related buffer code attempts to allocate or operate on a buffer/follio with this oversized size. folio_set_bh() contains an assertion that the size must not exceed PAGE_SIZE; that assertion fires and the kernel hits a BUG and typically oopses / panics. (spinics.net)
How the issue was discovered and fixed
- The problem was reported by syzbot (the kernel fuzzing bot) and a developer submitted a concise patch that checks the return value of sb_set_blocksize(), emits a clear error message ("romfs: unable to set blocksize") and fails the mount with -EINVAL if the operation fails. The change is a straight defensive check and is intentionally minimal. (spinics.net)
- The patch was accepted upstream and applied to the stable kernel series; it was packaged into stable backports for multiple kernel versions as part of the usual stable release grooming. The stable tree discussions and backport notifications show the fix landing across maintained branches. (spinics.net)
Scope: who and what is affected
- The vulnerability affects systems that include the ROMFS filesystem code and expose the ability to configure or mount block devices with nonstandard logical block sizes. That includes many general-purpose distributions and embedded kernels compiled with ROMFS enabled. (nvd.nist.gov)
- Exploitation requires the ability to create/configure a loop device and perform mounts. That typically requires administrative capabilities (CAP_SYS_ADMIN) or similar privileges. In practice, the attack is therefore local and requires either a misconfiguration that gives untrusted users loop access or a compromised account that already has mount privileges. (spinics.net)
- The most likely realistic impact is local denial-of-service / kernel crash, not a remote code execution. There is no public evidence at the time of writing that the bug enables privilege escalation, arbitrary memory corruption exploitable for RCE, or remote network-based exploitation without local access. That said, any kernel BUG can be a starting point for deeper investigation, so defenders should treat it seriously. (nvd.nist.gov)
Exploitability and attack scenarios
- Easiest scenario (proof of concept / testing): a developer or researcher configures a loop device with a block size larger than PAGE_SIZE (for example 32768 bytes) and mounts a ROMFS image; the mount produces a kernel BUG in buffer code. This is reproducible and was used by syzbot to demonstrate the issue. (spinics.net)
- Real-world abuse: an attacker with a local foothold (a shell, a low-privileged user who can access loop devices due to permissive system configuration, or an automated build system running untrusted inputs) can induce a system crash by mounting a crafted romfs image. This can be used as a denial-of-service primitive to crash containers, VMs, or hosts where the attacker can trigger mounts. (nvd.nist.gov)
- Harder scenarios: turning this crash into a code-execution primitive would require additional, currently unreported, memory-corruption chains. No public reports indicate such an escalation. Treat any such speculation as unverified. (nvd.nist.gov)
The upstream patch (what changed)
- The patch replaces the blind call sb_set_blocksize(sb, ROMBSIZE) with a guarded call that checks the return value. If sb_set_blocksize() returns 0 (failure), romfs_fill_super() logs an error and returns -EINVAL, preventing the faulty mount from continuing. The change is small and localized to fs/romfs/super.c. (spinics.net)
- It enforces correct error propagation and avoids assumptions about the block device.
- It does not attempt to override or coerce underlying block-device behavior.
- It produces a clear error path that administrators and logs can observe.
Patching status and vendor response
- The commit was merged upstream and included in stable kernel updates; the kernel stable maintainers circulated the fix across supported trees. Distributions that regularly backport stable fixes (Debian, Ubuntu, Fedora, RHEL derivatives, and embedded vendors) are likely to include the patch in their next maintenance updates if they have not already. (spinics.net)
- The National Vulnerability Database has recorded CVE-2026-23238 with the descriptive details contributed from kernel.org; at the time of this writing NVD lists the issue and the kernel commits but has not yet posted a CVSS score — that is common for newly added kernel CVEs while scoring/enrichment is completed. Administrators should therefore monitor vendor advisories and distribution errata for backports. (nvd.nist.gov)
- Prioritize kernel updates that include the romfs sb_set_blocksize patch. If your distribution publishes a security advisory, follow the distro guidance for kernel updates. (spinics.net)
- If patching is not immediately possible, consider temporary mitigations:
- Restrict access to loop devices (device nodes under /dev/loop*). Ensure only trusted users or root can create/configure loop devices.
- Apply filesystem mount hardening: avoid mounting untrusted ROMFS images; audit automount or build pipelines that might mount third-party images.
- On multi-tenant systems, reduce the ability for containers or unprivileged users to create loop devices or perform mounts (e.g., via stricter cgroup or namespace configuration, or by dropping CAP_SYS_ADMIN where feasible).
- Watch kernel logs for mount failures or the specific BUG message: folio/buffer-related BUG_ONs originating from fs/buffer.c with "size > PAGE_SIZE" are the signature of this path. After the patch, a failed sb_set_blocksize will log "romfs: unable to set blocksize" and the mount will fail cleanly — that is an observable diagnostic difference. (spinics.net)
Detection, logging, and indicators
- Before patch: kernel logs will show an oops/BUG with a trace that includes fs/buffer.c and the BUG_ON(size > PAGE_SIZE) assertion. Systems experiencing unexpected kernel oopses during mounts of ROMFS images should be investigated for this condition. (spinics.net)
- After patch: attempts to mount an incompatible ROMFS image will produce a mount error and an explicit kernel error message from romfs_fill_super() (the patched code prints "romfs: unable to set blocksize"). This makes detection easier in logs. (spinics.net)
- Search for "romfs: unable to set blocksize" in kernel logs (dmesg, /var/log/kern.log).
- Search for recent kernel BUG/OOPS messages with fs/buffer.c and folio_set_bh in tracebacks.
- Correlate mount activity by UID/process with loop device ioctl usage if logs are available.
Risk analysis — strengths and limitations of the fix
Strengths- The fix is minimal, targeted, and low-risk: it checks an API return value and refuses to mount on failure. This avoids further side effects and is straightforward to audit. (spinics.net)
- The patch closes the specific crash path and produces clear log output, improving operational visibility and diagnosis. (spinics.net)
- The change has been accepted into stable kernel trees, which accelerates distribution backports and remediation for consumers. (spinics.net)
- The fix addresses the symptom (unchecked return) and prevents the crash, but it does not change the fact that block devices can report large logical block sizes; systems that rely on unusual block-size behavior should be aware of the constraints around page-sized I/O. Operators should not assume all filesystems can coerce block sizes arbitrarily. (nvd.nist.gov)
- The vulnerability is local: it requires privileged operations (loop device configuration, mount). As such, systems that already grant untrusted accounts access to mounts or loop devices remain vulnerable to local abuse. Operational controls must be considered in addition to software updates. (spinics.net)
- While current reporting shows a crash/DoS outcome, the long-term risk profile of any kernel BUG is that further research can sometimes convert crash conditions into code-execution or escalation primitives. There is no public evidence of such an escalation for CVE-2026-23238 at the time of writing; that remains an unverified possibility until a credible exploit chain is published. Treat such claims cautiously and prioritize patching to remove the crash surface. (nvd.nist.gov)
Practical mitigation checklist (actionable steps)
- Apply kernel updates
- Install distribution kernel updates that include the ROMFS sb_set_blocksize patch. Verify the kernel changelog or stable backport references the romfs fix. (spinics.net)
- Harden loop device usage
- Restrict access to /dev/loop* nodes with appropriate ownership and permissions.
- Avoid exposing loop device creation to untrusted users or automated build runners.
- Lock down mount capabilities
- Where possible, run untrusted workloads without CAP_SYS_ADMIN or without mount privileges.
- For container runtimes, use least-privilege container profiles and avoid bind-mounting loop devices into containers.
- Monitor logs
- Watch for kernel messages that match the crash signature or the new "romfs: unable to set blocksize" diagnostic after patching. (spinics.net)
- Inventory and assess
- Identify systems that compile or enable ROMFS (some embedded builds do not enable every filesystem by default).
- Confirm whether device images or build pipelines rely on runtime changes to loop device block size; if so, evaluate alternatives or compensating controls.
Guidance for maintainers and packagers
- For kernel maintainers: this is a safe, one-line defensive change that should be backported to all supported stable branches containing ROMFS. The stable patch queues indicate that maintainers have already done so; please ensure your downstream packaging includes the backport. (spinics.net)
- For distribution security teams: treat the update as a low-complexity, medium-impact local DoS fix. Communicate to operations teams that the update reduces liveliness risk when handling untrusted images or loop devices.
- For embedded vendors and appliance makers: confirm whether ROMFS is enabled in your kernel builds. If you do not require ROMFS, consider disabling the filesystem to reduce the attack surface. If ROMFS is used, ensure your firmware and kernel images include the patch or a safe backport.
Conclusion
CVE-2026-23238 is a small but meaningful reminder that even tiny filesystem implementations require careful error handling for block-device interactions. The vulnerability reflects a classic mistake — ignoring a critical API return value — and the fix is correspondingly simple: check the return and fail the mount cleanly. The tangible impact is local denial-of-service via a kernel BUG triggered on mount, and the operational mitigations are straightforward: install the patched kernel, restrict loop/mount privileges, and monitor kernel logs for the diagnostic messages introduced by the patch. Upstream and stable trees have received the change; distributions and vendors should prioritize backporting or shipping the updated kernels to close the DoS surface. (spinics.net)Source: MSRC Security Update Guide - Microsoft Security Response Center