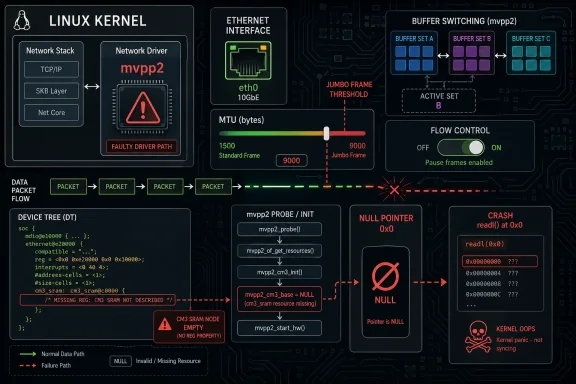
A newly tracked Linux kernel flaw in the Marvell mvpp2 Ethernet driver shows how a tiny missing condition can still bring down a system, and this one is now cataloged as CVE-2026-23438. The bug is a NULL pointer dereference in the buffer-switching path, triggered when the driver updates flow-control state without first checking whether global TX flow control is actually enabled. In practical terms, that means a routine action such as an MTU change can crash the kernel on affected systems when the CM3 SRAM block is absent from the device tree. The fix is small, but the operational lesson is large: even mature networking code can still hide a single unchecked assumption that turns configuration changes into outages. lnerability sits inside the Linux kernel’s mvpp2 driver, which supports Marvell packet-processing hardware used in certain embedded and networking platforms. According to the CVE description,
This kind of defectbecause it does not require an exotic attack chain. The CVE text says an MTU change that crosses the jumbo-frame threshold is enough to enter the vulnerable path, which means a normal administrative operation can trigger the fault. The crash trace included in the advisory shows the path moving through
The root cause is not a malformed packeton primitive in the usual sense. It is a logic bug: the code assumes a hardware resource exists and then tries to program flow-control registers unconditionally. The fix, as described in the CVE entry, is to guard both the disable and re-enable calls in buffer switching with
What makes this case interesting from an operations perspectigether kernel networking internals, device-tree topology, and platform-specific hardware wiring. If the CM3 SRAM entry is missing, the driver’s internal state says flow control should not be touched globally, but the old code still touched it anyway. That gap between state and behavior is exactly where many kernel CVEs live.
Marvell’s mvpp2 driver has long been part of the Linux network embedded Ethernet use cases, where packet processing, buffer management, and flow-control behavior all have to line up with the platform’s hardware description. In that ecosystem, the device tree matters as much as the driver itself because it tells the kernel what memory regions and functional blocks are actually available. The CVE description explicitly references the third
That detail is important because it explains why the bug is not universal across all mvpp2 deployments. the CM3 SRAM resource can initialize the flow-control path and avoid the null-pointer crash, while systems that do not include it leave
From a kernel-maintenance standpoint, the issue is a familiar one. Networking drivers often grow support for optional hardwaand the code path that handles an older or fallback configuration can easily diverge from the newer, hardware-backed path. When that happens, small inconsistencies become dangerous. Here, the inconsistency was not in the packet datapath itself but in the logic that decides whether to touch a piece of auxiliary hardware at all. That is a subtle distinction, but it matters because the crash is caused before any packet forwarding is even involved.
The published record also shows that this is already being tracked through the usual security channels. The NVD entry assigns a CVSS 3.1 base socal attack vector and high availability impact, and maps the weakness to CWE-476: NULL Pointer Dereference**. NVD’s enrichment is still noted as ongoing, but the classification itself makes the operational risk clear: this is an availability bug that a local actor or privileged management path could plausibly trigger.
Another useful clue is the way the change history ties the CVE to upstream and stable-kernel patches. The advisory lists multiple kernel.org references and stable bacsupported kernel lines, which is the usual sign that maintainers considered the defect concrete enough to fix in production branches. That does not make the issue flashy, but it does make it real. Kernel bugs like this rarely go viral; they get fixed because they are structurally correct to fix.
The stack trace is valuable because it shows a normal administrative workflow leading into the fault. The crash passes through
Why
The heart of the patch is the
That matters because kernel fixes are best when they are narrow and semantic. A narrow fix reduces regression risk; a semantic fix preserves the driver’s intended behavior. In this case, the driver should only touch CM3 flow-control registers when CM3-backed global flow control actually exists. Anything else hardware access, which is exactly what caused the crash.
Consistency also matters for long-term maintainability. If the driver’s rule is “touch the CM3 registers only when global TX flow control is active,” then buffer-switching logic must obey that rule too. Otherwise future changes can silently reintroduce the same class of fault. A single missing conditional can become a pattern if it is not corrected in tf the code.
That device-tree dependency is common in embedded Linux, but it also makes bugs harder to spot in development. A test board may have all the expected entries present, so the flow-control path works fine in lab conditions. Then a smaller production variant omits one memory region, and the same code suddenly dereferences a null pointer during a harmless-looking interface change. That is exactly the kind of configuration drift that can nto a crash vector.
This is a classic availability issue: no data exposure, no integrity corruption, just a crash. But availability is often the most important security property for infrastructure gear. If a kernel panic takes down a router, edge host, or appliance, the outage can be just as costly as a confidentiality breach. In some environments, it may be more costly because the affected system is part of the network’s control plane.
That restraint is worth emphasizing because networking patches that change behavior too broadly tend to be controversial. If a fix alters packet handling, buffer allocation, or throughput characteristics, maintainers have to think hard about regressied behavior remains intact for platforms that actually support the global flow-control path, while unsupported configurations simply skip the dangerous register access. That is the right balance.
The CVE record’s reference history reinforces that point. Multiple kernel.org patch references were added, and the record’s change log shows the issue moving through the standard upstream-to-stable pipeline. That suggests the bug was treated as a straightforward correctness and harden design dispute.
Consumer impact is narrower, but not zero. Home lab machines, small-office servers, and enthusiast platforms sometimes use bonding, MTU tuning, or vendor-specific Ethernet hardware that still sits on the mvpp2 line. If those syt include the vulnerable code and expose the same device-tree omission, the crash can happen there too. The difference is not whether the bug exists; it is whether the environment is likely to exercise it.
It is also worth watching whether other mve similar scrutiny. The CVE says this function was the only one that omitted the guard, but bugs like this sometimes reveal a broader pattern of state-handling assumptions around optional hardware resources. If maintainers spot another path that touches CM3-backed logic without checking
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
mvpp2_bm_switch_buffers() always invoked mvpp2_bm_pool_update_priv_fc() when toggling between per-CPU and shared buffer-pool modes, even when the hardware path for global TX flow control was not present. That helper eventually calls into CM3 register accessors that dereference priv->cm3_base, and if the device tree does not provide the CM3 SRAM resource, that pointer remains NULL. The result is a kernel crash instead of a harmless mode switch.This kind of defectbecause it does not require an exotic attack chain. The CVE text says an MTU change that crosses the jumbo-frame threshold is enough to enter the vulnerable path, which means a normal administrative operation can trigger the fault. The crash trace included in the advisory shows the path moving through
mvpp2_change_mtu(), mvpp2_bm_switch_buffers(), and then into the CM3 flow-control helpers before hitting readl() on address zero. That is classic kernel-space availability failure territory.The root cause is not a malformed packeton primitive in the usual sense. It is a logic bug: the code assumes a hardware resource exists and then tries to program flow-control registers unconditionally. The fix, as described in the CVE entry, is to guard both the disable and re-enable calls in buffer switching with
priv->global_tx_fc, matching the rest of the driver’s flow-control call sites. In other words, the patch teaches one hot path to follow the same rule the other paths already obeyed.What makes this case interesting from an operations perspectigether kernel networking internals, device-tree topology, and platform-specific hardware wiring. If the CM3 SRAM entry is missing, the driver’s internal state says flow control should not be touched globally, but the old code still touched it anyway. That gap between state and behavior is exactly where many kernel CVEs live.
 Background
Background
Marvell’s mvpp2 driver has long been part of the Linux network embedded Ethernet use cases, where packet processing, buffer management, and flow-control behavior all have to line up with the platform’s hardware description. In that ecosystem, the device tree matters as much as the driver itself because it tells the kernel what memory regions and functional blocks are actually available. The CVE description explicitly references the third reg entry added by commit 60523583b07c, which introduced CM3 SRAM memory to the cp11x Ethernet device tree. If that entry is missing, the hardware path that expects CM3 access should not be exercised.That detail is important because it explains why the bug is not universal across all mvpp2 deployments. the CM3 SRAM resource can initialize the flow-control path and avoid the null-pointer crash, while systems that do not include it leave
priv->cm3_base unset. The driver already tracks this difference through the priv->global_tx_fc flag, so the vulnerability exists precisely because one function ignored a state check that other functions were already using. The CVE text says this directly: every other flow-control call site already guards hardware access with either priv->global_tx_fc or port->tx_fc.From a kernel-maintenance standpoint, the issue is a familiar one. Networking drivers often grow support for optional hardwaand the code path that handles an older or fallback configuration can easily diverge from the newer, hardware-backed path. When that happens, small inconsistencies become dangerous. Here, the inconsistency was not in the packet datapath itself but in the logic that decides whether to touch a piece of auxiliary hardware at all. That is a subtle distinction, but it matters because the crash is caused before any packet forwarding is even involved.
The published record also shows that this is already being tracked through the usual security channels. The NVD entry assigns a CVSS 3.1 base socal attack vector and high availability impact, and maps the weakness to CWE-476: NULL Pointer Dereference**. NVD’s enrichment is still noted as ongoing, but the classification itself makes the operational risk clear: this is an availability bug that a local actor or privileged management path could plausibly trigger.
Another useful clue is the way the change history ties the CVE to upstream and stable-kernel patches. The advisory lists multiple kernel.org references and stable bacsupported kernel lines, which is the usual sign that maintainers considered the defect concrete enough to fix in production branches. That does not make the issue flashy, but it does make it real. Kernel bugs like this rarely go viral; they get fixed because they are structurally correct to fix.
How the Crash Happens
The crash path matters because it shows exactly why this defect is not theoretical. According to the CVE record, an MTU change that forces the driver to croreshold can invokemvpp2_bm_switch_buffers(). That function unconditionally calls the private flow-control updater, which in turn reaches mvpp2_cm3_read() and mvpp2_cm3_write(). Those helpers dereference priv->cm3_base, and when the CM3 SRAM resource is absent, that pointer is NULL. The kernel then falls over in readl() at address zero.The stack trace is valuable because it shows a normal administrative workflow leading into the fault. The crash passes through
mvpp2_change_mtu(), __dev_set_mtu, dev_set_mtu, dev_ioctl, and `sock_iocterator using routine interface-management tools could trigger the bug without any packet crafting or special device abuse. That is the kind of failure mode that makes network driver bugs operationally painful: the trigger is a legitimate configuration step.The missing guard
The technical mistake is straightforward.mvpp2_bm_switch_buffers() changes buffer-pool behavior and then tries to update flow-control state even when global TX flow control is not active. The driver alret hardware path is available; the field is there and the condition exists. The problem is simply that this one function skipped the guard, while the rest of the driver did not. That makes the bug easier to explain and, fortunately, easier to fix.Why NULL dereferences still matter
A NULL pointer dereference in kernel code is often dismissed as “just a crash,” but that undersells the risk. In a network-facing driver, a crash can take down a host, interrupt service traffic, or force failovloyment. The NVD classification reflects that reality by giving the issue availability impact only, but availability is often the first thing operators care about when the kernel panics in a production appliance.- The bug is triggered by a legitimate MTU change.
- The crash occurs in the buffer-switching path, not a rarely used debug routine.
- The fault is tied to missing CM3 SRAM in the device tree.
- The null dereference occurs in CM3 flow-control register access.
- The failutic once the vulnerable path is reached.
Why global_tx_fc Is the Real Fix Point
The heart of the patch is the priv->global_tx_fc flag. That flag already exists to indicate whether the hardware-backed global flow-control path is valid, and the CVE description says the other flow-control call sites already use it correctnction was the outlier. Fixing it means aligning buffer switching with the driver’s own state model instead of inventing a new workaround.That matters because kernel fixes are best when they are narrow and semantic. A narrow fix reduces regression risk; a semantic fix preserves the driver’s intended behavior. In this case, the driver should only touch CM3 flow-control registers when CM3-backed global flow control actually exists. Anything else hardware access, which is exactly what caused the crash.
Consistency across the driver
The CVE text says every other flow-control call site in the driver already performs the relevant guard check. That is a strong sign the bug was not conceptual but accidental. The codebase had already established a rule for safe access, and one path simply failed to follow it. Fixes like that are ofview because they restore consistency instead of redefining behavior.Consistency also matters for long-term maintainability. If the driver’s rule is “touch the CM3 registers only when global TX flow control is active,” then buffer-switching logic must obey that rule too. Otherwise future changes can silently reintroduce the same class of fault. A single missing conditional can become a pattern if it is not corrected in tf the code.
Why the buffer-switching path was special
Buffer switching sits at a boundary between memory management and traffic behavior. It is not just shuffling pointers; it is changing the packet-buffering model between per-CPU and shared modes. That makes it a natural place for subtle side effects, especially if the code needs to temporarily adjust flow control while the buffeproblem here is that the temporary adjustment assumed a hardware resource that might not exist.global_tx_fcalready encodes whether the hardware path is valid.- The fix does not redesign flow control.
- The patch simply blocks access when the hardware block is absent.
- The corrected behavior matches the rest of the driver.
- The change is small enough to backport cleanly.
Device Tree Assumptions and Hardware Reality
This CVE is a reminder that Linux networking drivers arheir platform description. The advisory explicitly ties the failure to the absence of the CM3 SRAM resource in the device tree, which means the kernel is making decisions based on a hardware map that may differ from one board file or SoC configuration to another. When that map does not i` entry, the code must assume CM3-backed global flow control is unavailable.That device-tree dependency is common in embedded Linux, but it also makes bugs harder to spot in development. A test board may have all the expected entries present, so the flow-control path works fine in lab conditions. Then a smaller production variant omits one memory region, and the same code suddenly dereferences a null pointer during a harmless-looking interface change. That is exactly the kind of configuration drift that can nto a crash vector.
Optional hardware is where bugs hide
Optional blocks are tricky because they create a split personality in the code. The driver must work both with and without the block, and the logic often becomes littered with checks that gate access to one auxiliary feature or another. Missing one of those checks is enough to create a security-relevant crash. In this case, the optional hardware was CM3 SRAM, and the gating condition already existed. The bug was a that gate, not the absence of the gate itself.Why this is more than an embedded nuisance
It would be easy to treat this as a niche board-specific issue, but that would be too casual. Embedded networking hardware often ends up in gateways, appliances, storage systems, and edge platforms where uptime matters a great deal. A kernel panic during interface reconfiguration can knock those systems offline just as effectively as it can on a general-purpose server. The smaller the device, the less forgiving the operational maMissing device-tree entries can disable hardware assumptions silently.- Drivers must treat optional resources as genuinely optional.
- Lab hardware may not expose the same failure as production boards.
- The bug appears only when the buffer mode changes.
- Embedded network systems often run with minimal tolerance for crashes.
Severity and Attack Surface
The available scoring places this flaw in the medium range, which is a good fit for a local, availability-only crash that requir administrative access to the interface. The published CVSS vector is AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H, which maps to a scenario where the attacker or operator needs local access and sufficient permission to trigger the change, but no user interaction is required. That makes the bug less dramatic than a remote code executionous enough to matter on systems where interface changes are routine.Local does not mean low impact
It is easy to underestimate “local” in CVSS vectors, but local administrative access is exactly how a lot of production network configuration happens. Orchestration tools, shell scripts, management agents, and provisioning systems all operate with local privileges on Linux hosts. If one of those systems changes MTU values automatically or during a rollout, the vulnerable path can be exercised without any unusual human action. That makes the practical attack surface broader than the metric alone may suggty is the real payloadThis is a classic availability issue: no data exposure, no integrity corruption, just a crash. But availability is often the most important security property for infrastructure gear. If a kernel panic takes down a router, edge host, or appliance, the outage can be just as costly as a confidentiality breach. In some environments, it may be more costly because the affected system is part of the network’s control plane.
Why the metric still matters
The CVSS score helps distinguish this issue from more dangerous kernelnot be read as “safe to ignore.” A medium score is still enough to justify prompt patching in supported branches, especially when the affected subsystem is a production networking driver. The absence of a write primitive or a remote trigger narrows the risk; it does not eliminate the operational consequences.- Local access is required, but that is normal for network administration.
- No user interaction is needed.
- Impact is availability-only, not code appliances can feel the effect more than desktops.
- Automation can turn a local bug into a fleet-wide problem.
The Patch in Context
The kernel fix is described as adding the missingpriv->global_tx_fc guard to both the disable and re-enable calls inside mvpp2_bm_switch_buffers(). That is the kind of patch that looks tiny in a diff but large in effect. It closes the exact hole the crash trace exposed, and it does so witid flow-control configuration.That restraint is worth emphasizing because networking patches that change behavior too broadly tend to be controversial. If a fix alters packet handling, buffer allocation, or throughput characteristics, maintainers have to think hard about regressied behavior remains intact for platforms that actually support the global flow-control path, while unsupported configurations simply skip the dangerous register access. That is the right balance.
Why the fix is easy to backport
Kernel stable maintainers generally prefer fixes that are clearly tied to a specific crash and do not require broad architectural changes. Thise well. It is local to one subsystem, it has a concrete null-dereference trace, and the resulting change is easy to reason about. Those are the ingredients stable trees like to see.The CVE record’s reference history reinforces that point. Multiple kernel.org patch references were added, and the record’s change log shows the issue moving through the standard upstream-to-stable pipeline. That suggests the bug was treated as a straightforward correctness and harden design dispute.
Why this matters to vendors
For downstream vendors, a patch like this is the ideal kind of security update. It is narrow, low-risk, and directly tied to a visible failure mode. Vendors can backport it without dragging in large chunks of unrelated networking code, which lowers the chance of shipping a regression in a critical driver. That is especially importatros and embedded vendor kernels.- The patch only touches one conditional path.
- It preserves behavior on supported hardware.
- It prevents register access when the path is invalid.
- It is likely to backport cleanly.
- It reduces the chance of regression in packet handling.
Enterprise and Consumer Impact
Ent most likely to care about this vulnerability because they are also the most likely to automate interface changes, run network appliances, or deploy embedded Ethernet hardware in production systems. A kernel panic on a managed switch, gateway, or appliance can disrupt services immediately and may trigger failover, failback, or monitoring alarms across dependent systems. In that setting, even a medium-severity bug can beaintenance item.Consumer impact is narrower, but not zero. Home lab machines, small-office servers, and enthusiast platforms sometimes use bonding, MTU tuning, or vendor-specific Ethernet hardware that still sits on the mvpp2 line. If those syt include the vulnerable code and expose the same device-tree omission, the crash can happen there too. The difference is not whether the bug exists; it is whether the environment is likely to exercise it.
Operational realities matter more than labels
A desktop user may never touch the MTU settings that trigger the path, while an infrastructure operator might change them as part of routine tuning. That is why kernel CVEs should be judged against workload behavior, not just the label “local” or the word “medium.” Inrol plane itself is often a privileged local interface, and that makes local bugs operationally significant.Why this is not just theoretical
The advisory’s stack trace proves the issue is not a speculative paper cut. It is a real null-pointer crash in a live code path, and the fix addresses a concrete omission. When kernel bugs reach that level of specificity, the question is no longer whether they matter. The question is how quickly the affected.- Enterprises should treat the issue as a routine but real kernel update.
- Appliances and edge devices may be disproportionately exposed.
- Desktop users are less likely to hit the trigger path.
- Automation can make the crash more likely during rollouts.
- Operational impact can exceed what the CVSS label suggests.
Strengths and Opportunities
The good news is that this vulnerability has the kind of fix security teams like to seed aligned with existing code patterns. It also gives operators a clear exposure test, because the risk depends on whether the CM3 SRAM resource is present and whether the driver is allowed to enter the buffer-switching path. That makes the issue easier to assess than a vague memory-safety bug buried in a large subsystem.- The patch is narrow and low-risk.
- The failuproduce conceptually.
- The driver already had the correct guard elsewhere.
- The bug is bounded to a specific hardware configuration.
- Administrators can reason about exposure from the device tree.
- Stable backporting should be straightforward.
- The fix preserves intended behavior on valid platforms.
Risksin concern is that this is a kernel crash in a networking driver, and those bugs have a habit of surfacing during normal maintenance windows. Even if exploitation is limited to denial of service, the real-world consequences can include lost connectivity, failover storms, or service interruption on systems that depend on the affected interface. The fact that the trigger is an MTU change makes the risk feel especially operational, not just theoretical.
- MTU changeserable code path.
- A missing device-tree entry can silently leave the system exposed.
- Kernel crashes can cascade into service outages.
- The bug may be overlooked because it is not remote-code-execution grade.
- Automation can trigger the crash across multiple systems at once.
- Embedded and appliance deployments may be hard to audit quickly.
- A false sense of “medium sremediation.
Looking Ahead
The main thing to watch is how quickly downstream vendors fold the fix into supported kernel streams. Because the record already points to stable references, the patch path should be familiar, but distribution cadence still matters. Systems that run embedded or vendor-custom kernels can lag upstream fixes longer than desktop Linux releases, and that often determines how long the exposure window stays open.It is also worth watching whether other mve similar scrutiny. The CVE says this function was the only one that omitted the guard, but bugs like this sometimes reveal a broader pattern of state-handling assumptions around optional hardware resources. If maintainers spot another path that touches CM3-backed logic without checking
global_tx_fc, the fix could expand into a larger hardening pass.What to monitor next
- Vendor kernel advisories and backport notes.
- Whether distrlude the fix.
- Any follow-up cleanups in mvpp2 flow-control code.
- Device-tree descriptions for affected cp11x platforms.
- Reports of MTU-change crashes on embedded hardware.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center