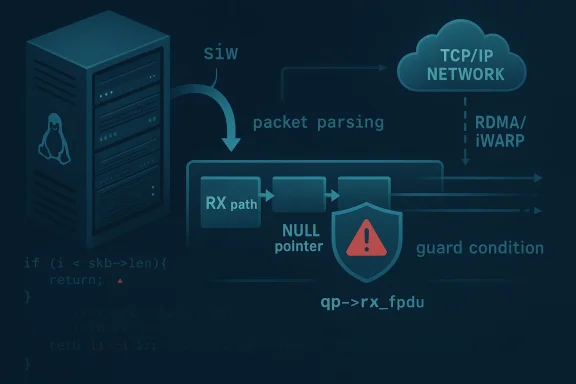
The recent RDMA/siw kernel fix for a potential NULL pointer dereference is a small patch with outsized relevance for anyone running software iWARP in Linux-based infrastructure. The bug lives in the receive path, where an error condition could leave
Software iWARP, or siw, is the Linux kernel’s software implementation of RDMA over TCP/IP. It exists for environments that want RDMA semantics without specialized hardware, which makes it especially important in virtualized, lab, and cost-sensitive deployments. The module is explicitly available in current kernel lines, and the driver’s role is to expose a verbs-compatible RDMA stack on top of ordinary TCP networking.
The new fix was posted to the stable kernel stream on February 24, 2026, by Greg Kroah-Hartman, and it traces back to an upstream commit by YunJe Shin. The stable note explains the failure mode plainly: if
That detail matters because kernel networking bugs often sit at the intersection of correctness and resilience. A one-line missing check may not sound dramatic, but in kernel space the consequence can be a panic, a service outage, or an avoidable disruption in an RDMA-dependent workload. The reported KASAN splat in the stable note reinforces that this was not merely theoretical; the issue was exercised in testing and reproduced as a null-pointer dereference. (spinics.net)
This is also another reminder that Microsoft’s now-missing CVE page sits atop a broader Linux ecosystem story. Microsoft’s Security Update Guide page for CVE-2026-23242 is unavailable, but the kernel patch text provides the substance: the issue is in RDMA/siw, not in a Windows component, and it is fundamentally about Linux receive-path error handling. That mismatch between a Microsoft CVE shell and Linux kernel internals is unusual enough to warrant careful reading before assuming the vulnerability affects a Microsoft product directly. (spinics.net)
The error path is also the part most likely to get less testing than the happy path. High-throughput receive code is usually optimized around expected packet sequences, and developers often focus on steady-state performance. That makes these edge-condition checks especially valuable, because they harden the code exactly where packet parsing, state transitions, and cleanup logic intersect. (spinics.net)
At the same time, software implementations often live closer to the surface of kernel error handling. A hardware device may absorb or shortcut some conditions, but a software stack has to parse, validate, and react in code paths that can be stress-tested by malformed inputs. That can make bugs like this one more visible in fuzzing and more consequential when they escape into stable branches. (spinics.net)
The broader lesson is that crash-only bugs still deserve attention in network stacks. If the affected service is exposed to untrusted traffic or sits in a critical path, an attacker may not need code execution to create real damage. Interrupting storage access, RDMA messaging, or cluster control traffic can be enough to trigger failover storms, degraded performance, or operator intervention. (spinics.net)
A stable backport also signals that the maintainers considered the patch narrow enough to ship broadly. In practice, that often translates into faster adoption by downstream vendors and distro security teams, especially when the change touches a single conditional rather than a core algorithm. It is the sort of fix that can travel quickly once identified. (spinics.net)
This is a good reminder that CVE branding can be misleading when the underlying ecosystem is cross-vendor. A CVE can appear in one portal while the technical root cause lives elsewhere, and security teams need to read the actual patch language rather than assume product ownership from the URL alone. That is especially true for infrastructure CVEs where upstream Linux, downstream distributions, and vendor security portals may all reference the same identifier differently. (spinics.net)
In competitive terms, robustness is part of the product story. Whether the conversation is about cloud platforms, hyperconverged infrastructure, or software-defined storage, customers tend to reward systems that fail gracefully and patch predictably. The better a vendor can demonstrate that kernel issues are quickly contained, the less likely a small defect becomes a strategic liability. (spinics.net)
In the meantime, the practical advice is simple: patch the kernel, confirm exposure, and do not overread the Microsoft URL. The vulnerability story here is Linux-first, receive-path specific, and operationally relevant precisely because it is narrow. Small kernel fixes often look unremarkable in isolation, but they are the kind that keep enterprise systems from turning a packet edge case into an outage. (spinics.net)
Source: MSRC Security Update Guide - Microsoft Security Response Center
qp->rx_fpdu unset and still allow later code to dereference it during header processing. In practical terms, that means a malformed or unexpected packet sequence could crash the affected kernel path, turning a networking edge case into a denial-of-service risk. (spinics.net)
 Overview
Overview
Software iWARP, or siw, is the Linux kernel’s software implementation of RDMA over TCP/IP. It exists for environments that want RDMA semantics without specialized hardware, which makes it especially important in virtualized, lab, and cost-sensitive deployments. The module is explicitly available in current kernel lines, and the driver’s role is to expose a verbs-compatible RDMA stack on top of ordinary TCP networking.The new fix was posted to the stable kernel stream on February 24, 2026, by Greg Kroah-Hartman, and it traces back to an upstream commit by YunJe Shin. The stable note explains the failure mode plainly: if
siw_get_hdr() returns -EINVAL before set_rx_fpdu_context() runs, qp->rx_fpdu can remain NULL, but the error path in siw_tcp_rx_data() still inspects qp->rx_fpdu->more_ddp_segs. The patch adds a guard so that more_ddp_segs is checked only when rx_fpdu exists. (spinics.net)That detail matters because kernel networking bugs often sit at the intersection of correctness and resilience. A one-line missing check may not sound dramatic, but in kernel space the consequence can be a panic, a service outage, or an avoidable disruption in an RDMA-dependent workload. The reported KASAN splat in the stable note reinforces that this was not merely theoretical; the issue was exercised in testing and reproduced as a null-pointer dereference. (spinics.net)
This is also another reminder that Microsoft’s now-missing CVE page sits atop a broader Linux ecosystem story. Microsoft’s Security Update Guide page for CVE-2026-23242 is unavailable, but the kernel patch text provides the substance: the issue is in RDMA/siw, not in a Windows component, and it is fundamentally about Linux receive-path error handling. That mismatch between a Microsoft CVE shell and Linux kernel internals is unusual enough to warrant careful reading before assuming the vulnerability affects a Microsoft product directly. (spinics.net)
What the Patch Actually Changes
The code change is minimal, but the logic is important. The old branch treated the existence ofmore_ddp_segs as if qp->rx_fpdu were always valid, while the corrected branch explicitly checks qp->rx_fpdu && qp->rx_fpdu->more_ddp_segs. That is the classic shape of a kernel null-deref fix: preserve the intended control flow, but make the data dependency explicit. (spinics.net)Why this kind of fix is deceptively small
In user space, a null pointer might mean a segmentation fault in one process. In kernel space, especially in networking and RDMA, the same error can knock over the whole machine or at least disrupt an interface path that upper layers depend on. The patch therefore improves robustness even if the visible symptom is “only” a crash rather than memory corruption. (spinics.net)The error path is also the part most likely to get less testing than the happy path. High-throughput receive code is usually optimized around expected packet sequences, and developers often focus on steady-state performance. That makes these edge-condition checks especially valuable, because they harden the code exactly where packet parsing, state transitions, and cleanup logic intersect. (spinics.net)
- The fix is a guard condition, not a redesign.
- It addresses a reachable error path.
- It reduces the chance of a kernel crash.
- It preserves the intended behavior of the receive completion logic.
- It is tightly scoped to
drivers/infiniband/sw/siw/siw_qp_rx.c. (spinics.net)
The significance of the KASAN report
The stable note includes a KASAN splat showing a null-pointer dereference insiw_tcp_rx_data(). That matters because KASAN is designed to catch memory safety violations during testing, which suggests the issue was not guessed at but observed concretely. In other words, this was a verified bug with a reproducible fault signature, not merely a speculative hardening patch. (spinics.net)RDMA/siw in Context
RDMA is often associated with specialized adapters, datacenter fabrics, and low-latency storage or cluster workloads. siw is different: it offers the RDMA programming model in software, carrying traffic over TCP/IP and making the technology accessible where hardware offload is unavailable. That makes it attractive for labs, development, and certain production scenarios where consistency matters more than absolute performance.Why software RDMA still matters
The existence of siw is a reminder that not all RDMA is about expensive NICs. Some organizations want compatibility with RDMA-aware applications without re-architecting the network, and software transport can be enough to validate workflows or support moderate-scale deployments. In those settings, the kernel module becomes part of the reliability story, not just an experimental feature.At the same time, software implementations often live closer to the surface of kernel error handling. A hardware device may absorb or shortcut some conditions, but a software stack has to parse, validate, and react in code paths that can be stress-tested by malformed inputs. That can make bugs like this one more visible in fuzzing and more consequential when they escape into stable branches. (spinics.net)
- siw implements Soft-iWARP in the Linux kernel.
- It exposes RDMA semantics over standard TCP/IP.
- It is used in environments where hardware RDMA is unavailable or impractical.
- It depends on careful receive-path validation to stay stable.
- It is not a niche toy; it is part of real enterprise networking stacks.
Enterprise versus lab impact
For enterprises, the issue is not just a crash but the operational blast radius. A kernel fault in RDMA path handling can interrupt application connectivity, storage traffic, or cluster communication, depending on how the stack is deployed. For labs and development environments, the risk is lower in business terms but still important because reproducibility and test fidelity can be undermined by a fragile transport layer. (spinics.net)Why NULL Pointer Dereferences Still Matter in 2026
A NULL pointer dereference is one of the oldest classes of software bugs, but it remains relevant because kernel code still relies on complex object lifecycles and stateful protocols. In this case, a receive-path error leaves one pointer unset while a later conditional assumes it is valid. That is a textbook example of how state transition bugs survive even in mature codebases. (spinics.net)Security impact is not always about code execution
Not every kernel vulnerability is a remote code execution candidate. Sometimes the most realistic outcome is a denial of service, especially when the flaw is in a parser or error path and the fix simply avoids dereferencing invalid memory. That does not make the issue trivial; in infrastructure software, service interruption can be serious enough to justify urgent patching. (spinics.net)The broader lesson is that crash-only bugs still deserve attention in network stacks. If the affected service is exposed to untrusted traffic or sits in a critical path, an attacker may not need code execution to create real damage. Interrupting storage access, RDMA messaging, or cluster control traffic can be enough to trigger failover storms, degraded performance, or operator intervention. (spinics.net)
- Availability can be a security impact.
- Parser and state-machine bugs are often the hardest to eliminate.
- Kernel-space mistakes have outsized operational consequences.
- “Only a crash” is still a meaningful exploitation target.
- Early validation remains the best defense against these classes of bugs. (spinics.net)
The role of fuzzing and sanitizers
The presence of a KASAN report is a strong hint that testing infrastructure played a role in surfacing the problem. Kernel sanitizers and fuzzers have become indispensable because they catch edge cases that normal workloads rarely explore. In that sense, this CVE is less a surprise than proof that continuous testing is still uncovering meaningful defects in mature subsystems. (spinics.net)Stable Kernel Backporting and Patch Flow
The patch was distributed as part of a stable review series, which means the issue was important enough to warrant backporting into maintained kernel lines. That is often a sign that the fix is small, low-risk, and directly tied to correctness rather than a broader redesign. The stable note also identifies the originating upstream commit and the older code path it corrects, helping downstream maintainers judge applicability. (spinics.net)How fixes move from upstream to stable
Kernel maintainers commonly take a fix from upstream, tag it with aFixes: line, and then queue it for stable release series where regression risk is managed carefully. Here, the Fixes: 8b6a361b8c48 ("rdma/siw: receive path") tag shows exactly which earlier change introduced the vulnerable behavior. That kind of traceability is valuable because it helps distributors and enterprise users determine whether their builds include the flawed logic. (spinics.net)A stable backport also signals that the maintainers considered the patch narrow enough to ship broadly. In practice, that often translates into faster adoption by downstream vendors and distro security teams, especially when the change touches a single conditional rather than a core algorithm. It is the sort of fix that can travel quickly once identified. (spinics.net)
- Identify the faulty upstream behavior.
- Reproduce it with sanitizers or a crash trace.
- Add a minimal guard or check.
- Tag the fix with the original
Fixes:commit. - Backport to supported stable branches. (spinics.net)
- The patch has a clear origin story.
- It is suitable for stable maintenance.
- It helps downstream vendors assess exposure.
- It likely requires no architectural change.
- It demonstrates the value of traceable kernel development. (spinics.net)
Microsoft’s Missing CVE Page and the Attribution Problem
The source page referenced by the user is unavailable, which creates a common but frustrating security-information problem: the CVE identifier exists, but the advisory page does not. In those cases, the patch text and related kernel discussion become the authoritative evidence for what changed, while the missing page leaves open questions about severity, affected versions, and official vendor guidance. (spinics.net)What can and cannot be inferred
We can infer that Microsoft’s page likely existed or was intended to exist because the URL is formatted as an MSRC vulnerability entry. We cannot, however, safely infer Microsoft-specific product impact, especially when the underlying issue is clearly in a Linux kernel subsystem. Without the original page, any claim about Microsoft product exposure would be speculative. (spinics.net)This is a good reminder that CVE branding can be misleading when the underlying ecosystem is cross-vendor. A CVE can appear in one portal while the technical root cause lives elsewhere, and security teams need to read the actual patch language rather than assume product ownership from the URL alone. That is especially true for infrastructure CVEs where upstream Linux, downstream distributions, and vendor security portals may all reference the same identifier differently. (spinics.net)
- The CVE ID is real, but the MSRC page is missing.
- The technical fix is documented in kernel stable mail.
- Product impact should not be assumed from the portal alone.
- Cross-vendor CVE handling can blur attribution.
- Teams should verify exposure against the actual subsystem, not the web page title. (spinics.net)
Practical guidance for administrators
If you run Linux systems with RDMA/siw enabled, the first step is inventory. Then check your kernel version against stable backports and vendor errata, because the fix may already be included in a distribution update even if the CVE page is absent. If you do not use siw, your exposure is likely much lower, but kernel hardening still benefits from keeping the subsystem updated. (spinics.net)Competitive and Market Implications
This kind of bug does not usually move markets in the way a zero-day in a consumer browser might. But it does have competitive relevance in enterprise infrastructure, where reliability, maintainability, and patch velocity all shape purchasing decisions. RDMA features are often part of broader platform evaluations, and a stable kernel fix helps maintain trust in Linux-based networking stacks. (spinics.net)Why vendors care
Vendors building on Linux RDMA stacks need confidence that software transports are as boring as possible in production. Every kernel crash ticket takes time away from performance tuning, storage integration, and customer support. A narrowly scoped patch like this helps protect the reputation of software RDMA as a viable fallback when hardware offload is not available. (spinics.net)In competitive terms, robustness is part of the product story. Whether the conversation is about cloud platforms, hyperconverged infrastructure, or software-defined storage, customers tend to reward systems that fail gracefully and patch predictably. The better a vendor can demonstrate that kernel issues are quickly contained, the less likely a small defect becomes a strategic liability. (spinics.net)
- Reliability is a competitive feature in infrastructure software.
- Patch quality affects customer confidence.
- RDMA stacks are judged on both latency and stability.
- Software transports need to look predictable under failure.
- Fast backports reduce operational anxiety. (spinics.net)
Consumer impact is limited, but not nonexistent
Most consumers will never knowingly touch siw, but they may still be affected indirectly through virtualization platforms, storage appliances, or lab images built on the same kernel. In that sense, “enterprise-only” bugs often trickle down through packaged systems and admin tooling. The fact that this patch is in stable kernels means the downstream footprint can be broader than it first appears. (spinics.net)Strengths and Opportunities
The good news is that this is the kind of issue the kernel ecosystem is well equipped to fix quickly. The patch is small, the risk is contained, and the problem is easy to reason about once the state transition is understood. That gives vendors and operators a straightforward path to remediation, which is exactly what you want in a kernel networking bug. (spinics.net)- Minimal code change reduces regression risk.
- Clear root cause makes validation easier.
- Stable backporting should speed downstream adoption.
- Sanitizer evidence improves confidence in the fix.
- The patch improves defensive coding discipline in a sensitive path.
- It strengthens trust in software RDMA as a production option.
- It gives distributors a clear
Fixes:anchor for tracking exposure. (spinics.net)
Risks and Concerns
The main concern is not that this patch is complex, but that bugs like it can linger in hidden deployment niches. Software RDMA is not always visible in inventory, and organizations may not realize they are using siw until a failure occurs or a dependency is discovered during an audit. That makes patch discovery and asset awareness as important as the fix itself. (spinics.net)Operational exposure remains the real issue
If the affected code path is reachable from traffic, the bug becomes a reliability problem with security overtones. If it is not reachable in a given deployment, the risk falls sharply, but administrators still need to verify that assumption rather than infer it. Kernel crashes in a shared or clustered environment can ripple beyond the individual host and trigger unnecessary failover or service churn. (spinics.net)- Hidden siw deployments may go unpatched.
- Exposure depends on actual RDMA/siw usage.
- Crash-only bugs can still cause significant downtime.
- Missing vendor pages can slow response and create uncertainty.
- Misattribution may lead teams to ignore a Linux issue as a Microsoft-only entry.
- Asset inventories often underreport kernel module usage.
- Edge-case receive paths are easy to under-test. (spinics.net)
What to Watch Next
The next step is straightforward: watch for the stable release note to propagate into downstream kernel builds and distribution advisories. Security teams should also check whether their vendor has mapped the fix to its own package streams, because that is often where operational decisions get made. The absence of the Microsoft advisory page makes downstream confirmation even more important. (spinics.net)Key follow-up items
- Confirm whether your Linux kernel build includes the
qp->rx_fpduguard. - Check distribution errata and enterprise kernel backports.
- Inventory systems that load siw or use software RDMA.
- Validate whether any virtualization or storage platform depends on the module.
- Monitor for any additional CVEs tied to the same receive path. (spinics.net)
In the meantime, the practical advice is simple: patch the kernel, confirm exposure, and do not overread the Microsoft URL. The vulnerability story here is Linux-first, receive-path specific, and operationally relevant precisely because it is narrow. Small kernel fixes often look unremarkable in isolation, but they are the kind that keep enterprise systems from turning a packet edge case into an outage. (spinics.net)
Source: MSRC Security Update Guide - Microsoft Security Response Center