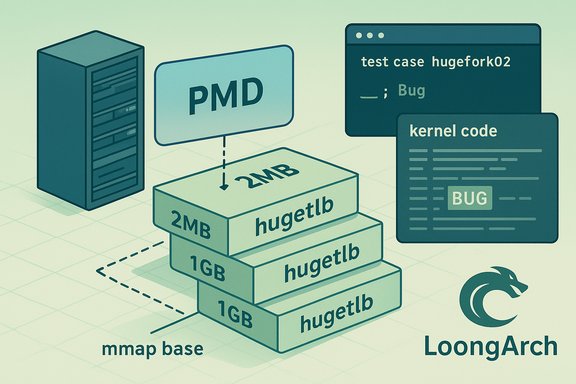
A Linux kernel correctness bug affecting LoongArch hugetlb mappings — tracked as CVE-2025-21949 — can produce a kernel BUG during hugetlbfs unmapping when the hugetlb mmap base is not aligned to the PMD (Page Middle Directory) size. The vulnerability is availability-first: reproducible kernel oopses and host instability are the observable outcomes, and maintainers have patched the upstream kernel to align hugetlb mmap bases with PMD size to remove the failure condition.
The CVE record for CVE-2025-21949 describes a defect discovered in LoongArch support within the Linux memory-management hugetlb paths: when a base address returned for a hugetlb mmap is not aligned with the architecture’s PMD size, subsequent unmap operations can hit an assertion or BUG path inside mm/hugetlb.c, producing a kernel oops. The failure surfaced during the LTP test case "testcases/bin/hugefork02" and was reproduced on a LoongArch QEMU virtual machine running kernel builds like 6.14.0-rc2+. Vulnerability trackers uniformly score the defect as medium (CVSS v3 base score ~5.5) with an AV:L/AC:L/PR:L/S:U/C:N/I:N/A:H vector — emphasizing the local or host-adjacent attack surface and the availability impact rather than data confidentiality or integrity loss. Distribution advisories and kernel maintainers applied a surgical fix that performs an architecture-aware alignment check and adjusts hugetlb mmap base addresses to PMD granularity when appropriate. This article dissects the technical root cause, explains why the bug matters operationally, outlines detection and mitigation steps, and highlights the practical trade-offs for operators running LoongArch or mixed-architecture deployments. It also contrasts the realistic exploitation model against worst-case public perceptions and provides a prioritized remediation playbook for infrastructure teams.
On LoongArch, an upstream testing run exposed a case where the hugetlb mmap path returned a base address that was not properly aligned to the PMD size for huge pages. That misalignment created an inconsistent state that later code paths could not safely handle during unmapping — the kernel reached a BUG check in mm/hugetlb.c (observed at line 5550 in the failing build). The fix adds a specific check for hugetlbfs mappings and forces the mmap base address to a PMD-aligned value before returning it to userspace. This ensures subsequent unmap and page-table operations see consistent alignment semantics.
Treat the CVE as an availability problem with real operational consequences for hosting providers, CI/CD runners, and multi-tenant infrastructure. While it does not enable data theft or direct code execution in the disclosed reports, availability primitives are tactically valuable to attackers who seek denial-of-service in shared environments — so remediation should be treated as urgent for exposed systems. Cross-check package changelogs against upstream commits before marking systems remediated, and maintain vigilant log retention so any future incidents are traceable and actionable.
Acknowledgement: The technical advisories and CVE records summarized here are drawn from vendor and aggregator entries documenting CVE-2025-21949, including upstream kernel test-case traces and distribution mapping data used by administrators to prioritize patches.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The CVE record for CVE-2025-21949 describes a defect discovered in LoongArch support within the Linux memory-management hugetlb paths: when a base address returned for a hugetlb mmap is not aligned with the architecture’s PMD size, subsequent unmap operations can hit an assertion or BUG path inside mm/hugetlb.c, producing a kernel oops. The failure surfaced during the LTP test case "testcases/bin/hugefork02" and was reproduced on a LoongArch QEMU virtual machine running kernel builds like 6.14.0-rc2+. Vulnerability trackers uniformly score the defect as medium (CVSS v3 base score ~5.5) with an AV:L/AC:L/PR:L/S:U/C:N/I:N/A:H vector — emphasizing the local or host-adjacent attack surface and the availability impact rather than data confidentiality or integrity loss. Distribution advisories and kernel maintainers applied a surgical fix that performs an architecture-aware alignment check and adjusts hugetlb mmap base addresses to PMD granularity when appropriate. This article dissects the technical root cause, explains why the bug matters operationally, outlines detection and mitigation steps, and highlights the practical trade-offs for operators running LoongArch or mixed-architecture deployments. It also contrasts the realistic exploitation model against worst-case public perceptions and provides a prioritized remediation playbook for infrastructure teams.Why this bug exists: technical anatomy
The hugetlb / PMD alignment mismatch
Linux supports "huge pages" through the hugetlb subsystem and hugetlbfs. Huge pages are mapped at larger granularities (for example, 2 MiB or 1 GiB) and the kernel must keep huge-page VMAs and page-table structures consistent with the PMD (or analogous) boundaries used by the architecture.On LoongArch, an upstream testing run exposed a case where the hugetlb mmap path returned a base address that was not properly aligned to the PMD size for huge pages. That misalignment created an inconsistent state that later code paths could not safely handle during unmapping — the kernel reached a BUG check in mm/hugetlb.c (observed at line 5550 in the failing build). The fix adds a specific check for hugetlbfs mappings and forces the mmap base address to a PMD-aligned value before returning it to userspace. This ensures subsequent unmap and page-table operations see consistent alignment semantics.
Reproducibility and how developers found it
The defect was reproducible with the LTP (Linux Test Project) case "hugefork02", which is designed to exercise fork/unmap semantics on hugetlb-backed mappings. The stack traces recorded in the CVE entries show a deterministic call chain ending in __unmap_hugepage_range and unmap_vmas. Developers traced the root cause to the base address allocation logic in the hugetlb mmap path and fixed it by aligning the base to the PMD size, referencing similar logic in a prior generic mmap fix (commit 7f24cbc..., which taught generic_get_unmapped_area to handle hugetlb mappings).Impact and exploitability: what this CVE means in practice
Primary impact: availability, not data theft
CVE-2025-21949 is an availability vulnerability. Triggering the failing sequence produces kernel warnings, oopses, and in some cases a kernel panic, which can terminate processes or require a host reboot. It does not provide a direct path to remote code execution, privilege escalation, or silent data exfiltration as published advisories emphasize. The scoring and vendor advisories reflect that: the common CVSS vector highlights AV:L/PR:L and A:H while marking confidentiality and integrity as unaffected.Where the risk is highest
- Multi-tenant hosts and public cloud hypervisors: hosts that run untrusted guest workloads or accept third-party images are most at risk because an attacker with the ability to run a guest (or local unprivileged workloads in shared runners) can try to exercise hugetlb mapping flows that interact with host or guest hugetlb semantics.
- CI systems and shared developer clusters: systems that run arbitrary user code or compile/test kernels may encounter test cases or workloads that trigger the failure.
- LoongArch-specific deployments and cross-architecture test beds: the bug is LoongArch-focused in upstream reports, so LoongArch hardware and QEMU-based LoongArch VMs are the primary exposure vector.
Exploit complexity and likelihood
- Complexity: Low-to-moderate. The sequence requires local or host-adjacent ability to create specific hugetlb mappings and exercise fork/unmap flows. Test cases show the issue is reproducible under controlled conditions.
- Likelihood of mass exploitation: Low. There are no authoritative public reports of active exploitation in the wild. However, availability primitives that reliably crash kernels are valuable to attackers aiming for denial-of-service in multi-tenant contexts. Treat the lack of PoC or telemetry as non-conclusive.
Affected kernels, distributions, and CVSS
Multiple security trackers (NVD, Debian, Ubuntu, Amazon Linux) indexed CVE-2025-21949 and list it with a CVSS v3.1 base score of 5.5 (Medium) and vector AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H. Vendors published distribution-specific advisories noting the condition and mapping fixes into stable kernel branches or backports; some vendor trackers mark some kernel variants as “Not Affected” while others list “Pending Fix” until patches are shipped. Operators should consult their distribution's security tracker or kernel package changelog to confirm whether their installed kernel includes the upstream fix. Key details to verify on your systems:- The failing trace references mm/hugetlb.c line ~5550 in the upstream report; check dmesg for matching BUG traces.
- The LTP testcase that reproduces the problem is "testcases/bin/hugefork02".
- Distribution package advisories reflect upstream stable commits that align hugetlb mmap base addresses with PMD size; verify your distro’s changelog lists the commit or CVE.
Detection and telemetry: what to look for in logs
Operators should hunt for the following high-value indicators:- Kernel messages in dmesg or journalctl matching the BUG pattern: "kernel BUG at mm/hugetlb.c:5550!" or stack traces that include __unmap_hugepage_range and unmap_vmas.
- Reproducible crashes when running hugetlbfs LTP tests such as hugefork02.
- Unexpected kernel oops/panic patterns on LoongArch virtual machines or hardware during workloads that allocate or unmap huge pages.
- Inspect kernel logs for BUG traces:
- journalctl -k | grep -i 'hugetlb|__unmap_hugepage_range|unmap_vmas'
- Check whether your kernel package changelog mentions CVE-2025-21949 or references an upstream fix for hugetlb mmap/PMD alignment.
- If you can run tests safely in a staging environment, execute the LTP hugetlb tests to verify whether your kernel shows the failing behavior.
Remediation and mitigation: a prioritized playbook
Patch management is the only reliable long-term fix for kernel bugs. The upstream kernel change for CVE-2025-21949 is small and surgical — adjust hugetlb mmap base addresses to PMD size on LoongArch — and has been applied and backported into stable branches used by distributions. The practical steps for remediation are:- Inventory and prioritize (first 0–24 hours)
- Identify LoongArch hosts and VMs, and any systems that mount hugetlbfs or run workloads that use huge pages.
- Enumerate kernel versions: uname -r on each host and compare with your distro’s advisory for CVE-2025-21949.
- Apply vendor patches (24–72 hours)
- Upgrade to a vendor-supplied kernel package that explicitly lists CVE-2025-21949 or the associated upstream commit ID in the changelog.
- Reboot hosts into the patched kernel (kernel fixes require reboot).
- Validate by rerunning the LTP hugetlb tests in staging when feasible.
- Short-term mitigations if you cannot immediately patch
- Avoid running untrusted hugetlb workloads on vulnerable hosts.
- For cloud operators, restrict tenants from mounting hugetlbfs or deny access to privileged hugetlb interfaces on hosts accepting untrusted guests.
- Consider isolating high-risk nodes (cordon/drain) until patched, especially multi-tenant nodes.
- Post-patch validation
- Confirm the kernel changelog or package metadata contains the upstream fix or lists the CVE.
- Re-run the LTP "hugefork02" test or simulate typical hugetlb workloads to ensure the application no longer triggers the BUG trace.
- Communication and scheduling
- For cloud providers and hosting operators: schedule rolling reboots to minimize tenant disruption and communicate planned maintenance windows to customers.
- For edge or embedded vendors: plan for firmware or kernel updates in your update pipeline and inform integrators about the required backport.
Operational considerations for cloud and multi-tenant environments
- Prioritization: treat hosts that accept untrusted guests, shared CI runners, and public cloud hypervisors as high-priority for remediation.
- Test and rollback plan: kernel upgrades require reboots; prepare rollback images and snapshotting in case the patched kernel interacts unexpectedly with vendor drivers or vendor-specific modules.
- Automation: use your configuration-management and inventory tooling to identify all images and VMs shipping LoongArch kernels; cross-reference with vendor VEX/CSAF or distro security feeds where available.
- For operators using Microsoft-published Linux artefacts (e.g., Azure Linux), do not assume coverage: check vendor attestations for the particular image or SKU before marking systems remediated.
Why the patch is low-risk and how maintainers addressed it
Kernel maintainers chose a small, localized change: when hugetlbfs is involved, ensure the mmap base is aligned to the PMD size so subsequent unmap and page-table operations see consistent alignment. This approach is consistent with upstream policy for correctness fixes — minimal invasiveness and easy backportability. Because the change does not alter hugetlb semantics for other architectures or generic mm semantics, it is considered low risk for regressions and straightforward to ship in stable kernels and vendor backports.Risk analysis: strengths of the fix and residual concerns
Strengths
- Surgical fix: corrects alignment at the source of the inconsistency without reworking hugetlb semantics.
- Easy to backport: minimal lines of code changed make distribution backports and vendor patches straightforward.
- Deterministic mitigation: alignment is a clear invariant and can be validated in tests (LTP hugetlb tests pass after the patch).
Residual risks and caveats
- Local attack vector remains: although the fix removes the immediate BUG trigger, attackers who possess local or host-adjacent execution still hold other kernel-level primitives that may be valuable for DoS.
- Distribution lag: vendor images and OEM kernels can lag upstream; operators must verify package changelogs rather than assuming a kernel version implies the presence of the fix.
- Observability blind spots: if teams do not capture or retain kernel oops logs, detection can be delayed; preserving dmesg and crash logs is essential for forensic correlation.
Concrete checklist for administrators (quick reference)
- Inventory: list all LoongArch hosts and any systems that mount hugetlbfs (uname -r; check /proc/meminfo and mount points).
- Verify: check your distro’s security tracker and kernel package changelog for CVE-2025-21949 or the upstream commit reference.
- Patch: install the vendor-provided kernel package that contains the fix and reboot hosts.
- Validate: rerun the LTP hugetlb tests or reproduce hugetlb workloads in staging to confirm no kernel BUGs.
- Monitor: watch kernel logs (journalctl -k, dmesg) for any remaining hugetlb or page-table errors after rollout.
- Compensate: if immediate patching is impossible, reduce the attack surface by preventing untrusted hugetlb workloads and isolating hosts.
Final verdict and operational conclusion
CVE-2025-21949 is a narrowly scoped LoongArch-specific correctness bug that produces a deterministic host instability when hugetlb mmap base addresses are not aligned to PMD size. The fix is straightforward, low-risk, and available upstream; distributions have mapped the CVE into packages and rolled out backports in stable trees. For risk-conscious operators, the remediation path is simple: verify kernel packages that include the upstream patch, schedule reboots into patched kernels, and prioritize hosts that run untrusted or multi-tenant workloads.Treat the CVE as an availability problem with real operational consequences for hosting providers, CI/CD runners, and multi-tenant infrastructure. While it does not enable data theft or direct code execution in the disclosed reports, availability primitives are tactically valuable to attackers who seek denial-of-service in shared environments — so remediation should be treated as urgent for exposed systems. Cross-check package changelogs against upstream commits before marking systems remediated, and maintain vigilant log retention so any future incidents are traceable and actionable.
Acknowledgement: The technical advisories and CVE records summarized here are drawn from vendor and aggregator entries documenting CVE-2025-21949, including upstream kernel test-case traces and distribution mapping data used by administrators to prioritize patches.
Source: MSRC Security Update Guide - Microsoft Security Response Center