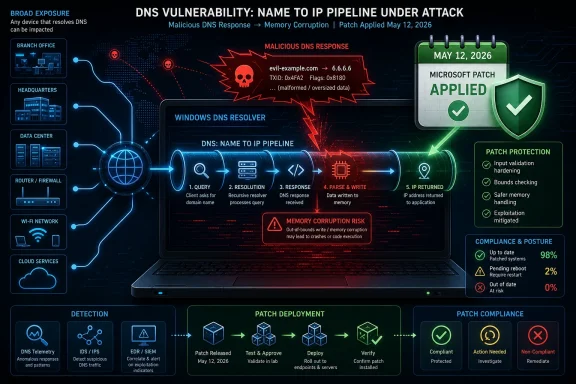
Microsoft’s May 12, 2026 Patch Tuesday fixes CVE-2026-41096, a critical Windows DNS Client remote code execution vulnerability rated CVSS 9.8 that affects supported Windows client and server systems and can be triggered over the network without authentication or user interaction. That is the dry version of the story. The more useful version is that Microsoft has patched a flaw in plumbing so ordinary that many administrators rarely think about it until it breaks. DNS is not an optional feature of modern Windows; it is the bloodstream.
The vulnerability is dangerous not because Microsoft has said attackers are already exploiting it, but because it lives in a component that every Windows estate depends on by design. A malicious DNS response is not a phishing attachment, a macro-laced spreadsheet, or a suspicious installer that can be blocked by user training. It is traffic Windows expects to receive all day, every day, from networks the machine may not fully control.
CVE-2026-41096 lands in the awkward category of vulnerabilities that are simultaneously simple to describe and difficult to operationalize. Microsoft’s description points to a heap-based buffer overflow in Windows DNS, allowing an unauthenticated attacker to execute code over a network. The CVSS vector tells the rest of the story: network attack vector, low attack complexity, no privileges required, no user interaction, and high impact to confidentiality, integrity, and availability.
That combination is why the 9.8 score matters. CVSS is not destiny, and administrators have learned to treat scoring systems with appropriate skepticism. But when the ingredients include remote reachability, no login requirement, and no click requirement, the score is not alarmism. It is a useful shorthand for “put this near the top of the queue.”
The important distinction is that this is not being reported as a vulnerability in a niche Windows role that only appears on domain controllers, DNS servers, or carefully segmented infrastructure. It is a Windows DNS Client flaw. Client-side DNS resolution is present on workstations, laptops, servers, jump boxes, virtual desktops, and cloud-hosted Windows workloads. That makes the affected population broad even before anyone starts counting versions.
Microsoft’s May 2026 security release was already a heavy one, with reporting from the patch-management ecosystem counting well over a hundred fixed flaws across Windows and Microsoft products. But CVE-2026-41096 stands out because of where it sits. It is not merely another remote code execution bug; it is a remote code execution bug in the path Windows uses to turn names into destinations.
That parsing code is the dangerous surface here. The problem is not that a Windows machine asks a bad question. The problem is that a malicious or attacker-influenced answer may be enough to corrupt memory in the Windows DNS Client path. In ordinary terms, a machine doing normal networking could be fed a response crafted to make Windows mishandle its own memory boundaries.
This is why the phrase no user interaction should make defenders pause. The user does not need to open a document or approve a prompt. The system merely has to perform the kind of background network activity that Windows, browsers, VPN clients, endpoint agents, updaters, identity components, and cloud sync tools perform constantly.
That does not mean every Windows computer on the internet is instantly exploitable from anywhere. Real-world exploitability depends on network position, DNS path control, resolver behavior, response validation, timing, and the details Microsoft has not publicly reduced into a step-by-step attack recipe. But it does mean the attack surface follows Windows wherever Windows goes: into branch offices, home networks, hotel Wi-Fi, developer labs, unmanaged VLANs, and hastily built cloud subnets.
This is why enterprise defenders should avoid the false comfort of “not internet-facing.” Client-side DNS bugs can become internal-network problems very quickly. Once an attacker is inside a network segment, the ability to answer or tamper with name resolution can become a privilege escalation and lateral movement tool, especially in environments where internal clients are allowed to query too broadly.
The scenario to worry about is not only the coffee-shop laptop. It is the compromised branch appliance, the forgotten lab DNS server, the over-permissive DHCP scope, the rogue access point, the malware-infected internal host advertising itself as a resolver, or the cloud network where egress rules were written for convenience rather than containment. DNS is often treated as benign because blocking it breaks everything. Attackers understand that cultural exemption.
Windows estates with mature DNS hygiene are better positioned. Environments that force clients through trusted resolvers, restrict direct outbound DNS, monitor resolver changes, and segment networks by role have more places to notice or disrupt abuse. Environments that allow any endpoint to talk UDP and TCP 53 to anywhere on the internet have fewer such chokepoints.
For defenders, the question is not whether exploitation was observed on May 12, 2026. The question is how long it will take for researchers and attackers to infer enough from the patch to build a working proof of concept. With memory corruption flaws in ubiquitous Windows components, reverse engineering the update can turn a theoretical risk into an operational one.
The absence of known exploitation does change the response shape. This is not necessarily a pull-the-network-cable emergency for every small business. It is, however, a patch-now issue for enterprises, managed service providers, schools, hospitals, local governments, and anyone running Windows systems across networks they do not fully trust.
The right response is urgency without theater. Administrators should test the May cumulative updates against representative systems, prioritize exposed and mobile endpoints, accelerate server patch windows, and verify deployment rather than merely approving updates in a console. If patch compliance reporting is noisy or delayed, this is the month to fix the reporting problem too.
The affected range appears to include current supported Windows 11 releases and supported Windows Server versions, including Windows Server 2022 and Windows Server 2025. Third-party vulnerability trackers list patched build thresholds for Windows 11 branches such as 23H2, 24H2, and 25H2, reinforcing the practical point: this is a mainstream Windows servicing issue, not an obscure legacy corner.
That matters for patch operations. In many organizations, the most sensitive servers are patched deliberately, while ordinary workstations move through staged rings. For this bug, ordinary workstations deserve more respect. They are the machines most likely to roam, attach to untrusted networks, receive DHCP-provided DNS settings, and generate large volumes of routine DNS traffic.
Servers are not off the hook. Windows servers also resolve names constantly, whether for domain services, update checks, telemetry, application dependencies, package repositories, monitoring agents, or backup software. A server does not need to be a DNS server to use the Windows DNS Client stack.
That creates blind spots. Security teams may have logs showing which resolver an endpoint queried, but not enough telemetry to understand whether a malformed response caused abnormal behavior. Endpoint detection tools may catch suspicious child processes or memory exploitation after the fact, but DNS itself can blend into background noise.
The defensive posture should therefore be layered. Patching is first. Resolver control is second. Detection is third. None of these compensates perfectly for the others, but each buys time and visibility.
Organizations that already enforce DNS egress through approved resolvers should verify the rule rather than assume it still holds. Shadow IT, VPN split tunneling, containerized workloads, developer tools, and cloud networking can quietly punch holes through old assumptions. The question is not whether the network diagram says DNS is controlled. The question is whether packet flow confirms it.
Small businesses face the harder middle ground. They may lack full patch orchestration, but they often have enough Windows laptops and servers to be attractive targets. They may also rely on consumer-grade routers, ISP-provided DNS, unmanaged switches, and VPN appliances that quietly become part of the trust chain.
For those environments, the practical move is to patch first and simplify DNS paths. Use trusted resolvers. Avoid letting endpoints choose arbitrary external DNS servers. Make sure remote workers connect through managed VPN profiles where appropriate. Confirm that routers and access points are not exposing clients to untrusted name-resolution behavior.
This is also a good moment to retire the idea that “we are too small to be targeted” applies to network worms, botnets, and opportunistic exploitation. If reliable exploit code emerges, attackers will not hand-select only Fortune 500 victims. They will scan, spray, phish for footholds, and abuse whatever infrastructure answers.
But focusing only on public Wi-Fi understates the enterprise problem. Many attacks begin inside supposedly trusted environments. A compromised router in a branch office, a malicious device on a flat guest network, or an attacker who has gained a limited foothold may be better positioned to tamper with DNS than a random café adversary.
The distinction matters because mitigations differ. Travelers need patched laptops and sane VPN behavior. Enterprises need internal DNS discipline, network access control, segmentation, and monitoring for unauthorized resolvers. Cloud teams need to review VPC and virtual network DNS settings, especially in hybrid environments where Windows workloads span on-premises and cloud address spaces.
The common denominator is that DNS should no longer be treated as harmless plumbing. It is a control plane for application behavior, identity reachability, update retrieval, and user navigation. When the client parser is vulnerable, that control plane can become an execution path.
Still, defenders can look for supporting signals. Unexpected resolver changes, endpoints querying unapproved DNS servers, unusual DNS response patterns, crashes or restarts in name-resolution-related processes, and suspicious child processes spawned around network activity all deserve attention. None of those signals proves exploitation by itself, but together they can narrow the hunt.
Endpoint detection and response platforms may help if exploit attempts move from memory corruption into payload execution. Network detection may help if malicious DNS responses are distinctive enough to fingerprint. But defenders should be careful not to confuse “we have telemetry” with “we can safely delay the patch.”
The more realistic role of detection is triage. It can identify systems that were exposed to risky DNS paths before patching, locate resolver misconfigurations, and reveal whether attackers are experimenting in the environment. It is not a substitute for removing the vulnerable code path.
A DNS Client RCE punishes that gap. The vulnerable activity can happen before a user opens a business application. It can happen while the device is checking for connectivity, resolving update endpoints, or syncing background services. If the machine is unpatched, its physical location and current network may matter more than the elegance of the corporate firewall.
That should push administrators toward faster compliance loops. The important metric is not when the update was approved, but when vulnerable systems actually installed it and rebooted if required. Patch dashboards that look healthy because powered-off laptops have not checked in are not healthy.
Windows Autopatch, Intune, Configuration Manager, WSUS, RMM tools, and third-party patch platforms all have roles to play depending on the estate. The principle is the same across them: shorten the distance between release, deployment, reboot, and verification. For this class of flaw, “pending restart” is not a comforting state.
That is the uncomfortable bargain of platform computing. Windows provides shared services so every application does not have to reinvent name resolution, authentication, printing, graphics, and file handling. When those shared services are robust, the platform gets safer. When they fail, the blast radius is enormous.
This is also why security teams should resist overly narrow asset prioritization. Internet-facing servers matter, but so do laptops. Domain controllers matter, but so do developer workstations. Crown-jewel databases matter, but so do the ordinary Windows machines that administrators use to reach them.
The attacker’s path rarely respects the asset inventory’s hierarchy. A modest endpoint flaw can become a privileged foothold. A resolver misconfiguration can become a payload delivery mechanism. A patch delay on a “low-risk” subnet can become the beginning of an incident report.
For organizations that cannot patch every system immediately, mitigations should focus on reducing the chance that vulnerable clients receive untrusted DNS responses. Restrict outbound DNS to approved resolvers. Block direct DNS to the internet where business operations allow. Audit DHCP options. Watch for endpoints that suddenly use unexpected resolvers. Treat unauthorized DNS infrastructure as a security incident, not a harmless network quirk.
But compensating controls should be framed honestly. They reduce exposure; they do not erase the vulnerability. A laptop that leaves the managed network, a server in a poorly governed subnet, or a VPN configuration that allows local network DNS can still create an opening.
Administrators should also prepare for the second-order work. After emergency patching comes validation, exception cleanup, and root-cause review for systems that missed the window. The machines that are hardest to patch during a critical event are usually the same machines that will be hardest to defend during an intrusion.
Source: cyberpress.org Critical Windows DNS Client Flaw Enables Remote Code Execution
The vulnerability is dangerous not because Microsoft has said attackers are already exploiting it, but because it lives in a component that every Windows estate depends on by design. A malicious DNS response is not a phishing attachment, a macro-laced spreadsheet, or a suspicious installer that can be blocked by user training. It is traffic Windows expects to receive all day, every day, from networks the machine may not fully control.
 This Is the Kind of Bug Patch Tuesday Was Built For
This Is the Kind of Bug Patch Tuesday Was Built For
CVE-2026-41096 lands in the awkward category of vulnerabilities that are simultaneously simple to describe and difficult to operationalize. Microsoft’s description points to a heap-based buffer overflow in Windows DNS, allowing an unauthenticated attacker to execute code over a network. The CVSS vector tells the rest of the story: network attack vector, low attack complexity, no privileges required, no user interaction, and high impact to confidentiality, integrity, and availability.That combination is why the 9.8 score matters. CVSS is not destiny, and administrators have learned to treat scoring systems with appropriate skepticism. But when the ingredients include remote reachability, no login requirement, and no click requirement, the score is not alarmism. It is a useful shorthand for “put this near the top of the queue.”
The important distinction is that this is not being reported as a vulnerability in a niche Windows role that only appears on domain controllers, DNS servers, or carefully segmented infrastructure. It is a Windows DNS Client flaw. Client-side DNS resolution is present on workstations, laptops, servers, jump boxes, virtual desktops, and cloud-hosted Windows workloads. That makes the affected population broad even before anyone starts counting versions.
Microsoft’s May 2026 security release was already a heavy one, with reporting from the patch-management ecosystem counting well over a hundred fixed flaws across Windows and Microsoft products. But CVE-2026-41096 stands out because of where it sits. It is not merely another remote code execution bug; it is a remote code execution bug in the path Windows uses to turn names into destinations.
DNS Is Not Just a Server Problem
Administrators often think of DNS risk in terms of authoritative servers, recursive resolvers, conditional forwarders, split-horizon zones, and Active Directory-integrated records. That view is understandable, but it misses the client-side reality. Every Windows system that asks “where is this name?” also has to parse the answer.That parsing code is the dangerous surface here. The problem is not that a Windows machine asks a bad question. The problem is that a malicious or attacker-influenced answer may be enough to corrupt memory in the Windows DNS Client path. In ordinary terms, a machine doing normal networking could be fed a response crafted to make Windows mishandle its own memory boundaries.
This is why the phrase no user interaction should make defenders pause. The user does not need to open a document or approve a prompt. The system merely has to perform the kind of background network activity that Windows, browsers, VPN clients, endpoint agents, updaters, identity components, and cloud sync tools perform constantly.
That does not mean every Windows computer on the internet is instantly exploitable from anywhere. Real-world exploitability depends on network position, DNS path control, resolver behavior, response validation, timing, and the details Microsoft has not publicly reduced into a step-by-step attack recipe. But it does mean the attack surface follows Windows wherever Windows goes: into branch offices, home networks, hotel Wi-Fi, developer labs, unmanaged VLANs, and hastily built cloud subnets.
The Scariest Attacker Is the One Already Near Your Resolver
The likely practical exploitation model is not a Hollywood attacker shouting packets across the open internet at random laptops. DNS is request-and-response infrastructure, and attackers generally need a way to influence what answer a target receives. That can mean control of a malicious DNS server, compromise of a local router, poisoning of a resolver path, man-in-the-middle positioning on a hostile network, or control of infrastructure a victim already queries.This is why enterprise defenders should avoid the false comfort of “not internet-facing.” Client-side DNS bugs can become internal-network problems very quickly. Once an attacker is inside a network segment, the ability to answer or tamper with name resolution can become a privilege escalation and lateral movement tool, especially in environments where internal clients are allowed to query too broadly.
The scenario to worry about is not only the coffee-shop laptop. It is the compromised branch appliance, the forgotten lab DNS server, the over-permissive DHCP scope, the rogue access point, the malware-infected internal host advertising itself as a resolver, or the cloud network where egress rules were written for convenience rather than containment. DNS is often treated as benign because blocking it breaks everything. Attackers understand that cultural exemption.
Windows estates with mature DNS hygiene are better positioned. Environments that force clients through trusted resolvers, restrict direct outbound DNS, monitor resolver changes, and segment networks by role have more places to notice or disrupt abuse. Environments that allow any endpoint to talk UDP and TCP 53 to anywhere on the internet have fewer such chokepoints.
Microsoft’s “Exploitation Less Likely” Does Not Mean “Patch Later”
Microsoft reportedly assesses exploitation as less likely at disclosure time. That judgment matters, but it is not a permission slip to defer. Vendor exploitability ratings are snapshots, not guarantees, and they often describe what Microsoft knows at release rather than what offensive researchers will know a week later.For defenders, the question is not whether exploitation was observed on May 12, 2026. The question is how long it will take for researchers and attackers to infer enough from the patch to build a working proof of concept. With memory corruption flaws in ubiquitous Windows components, reverse engineering the update can turn a theoretical risk into an operational one.
The absence of known exploitation does change the response shape. This is not necessarily a pull-the-network-cable emergency for every small business. It is, however, a patch-now issue for enterprises, managed service providers, schools, hospitals, local governments, and anyone running Windows systems across networks they do not fully trust.
The right response is urgency without theater. Administrators should test the May cumulative updates against representative systems, prioritize exposed and mobile endpoints, accelerate server patch windows, and verify deployment rather than merely approving updates in a console. If patch compliance reporting is noisy or delayed, this is the month to fix the reporting problem too.
Endpoint Patching Becomes Network Defense
CVE-2026-41096 is a useful reminder that endpoint patching is not separate from network security. A firewall can reduce exposure, and a controlled resolver architecture can make exploitation harder, but neither changes the fact that vulnerable client code may still parse hostile data if the attacker can get into the DNS answer path. The durable fix is Microsoft’s update.The affected range appears to include current supported Windows 11 releases and supported Windows Server versions, including Windows Server 2022 and Windows Server 2025. Third-party vulnerability trackers list patched build thresholds for Windows 11 branches such as 23H2, 24H2, and 25H2, reinforcing the practical point: this is a mainstream Windows servicing issue, not an obscure legacy corner.
That matters for patch operations. In many organizations, the most sensitive servers are patched deliberately, while ordinary workstations move through staged rings. For this bug, ordinary workstations deserve more respect. They are the machines most likely to roam, attach to untrusted networks, receive DHCP-provided DNS settings, and generate large volumes of routine DNS traffic.
Servers are not off the hook. Windows servers also resolve names constantly, whether for domain services, update checks, telemetry, application dependencies, package repositories, monitoring agents, or backup software. A server does not need to be a DNS server to use the Windows DNS Client stack.
The Enterprise Blast Radius Runs Through the Boring Stuff
The most dangerous Windows vulnerabilities are not always the flashiest. Sometimes they are the ones that exploit the enterprise’s assumptions about boring infrastructure. DNS is allowed because DNS is necessary. Endpoint DNS behavior is standardized because managing exceptions at scale is painful. Monitoring often focuses on the resolver, not the client parser.That creates blind spots. Security teams may have logs showing which resolver an endpoint queried, but not enough telemetry to understand whether a malformed response caused abnormal behavior. Endpoint detection tools may catch suspicious child processes or memory exploitation after the fact, but DNS itself can blend into background noise.
The defensive posture should therefore be layered. Patching is first. Resolver control is second. Detection is third. None of these compensates perfectly for the others, but each buys time and visibility.
Organizations that already enforce DNS egress through approved resolvers should verify the rule rather than assume it still holds. Shadow IT, VPN split tunneling, containerized workloads, developer tools, and cloud networking can quietly punch holes through old assumptions. The question is not whether the network diagram says DNS is controlled. The question is whether packet flow confirms it.
Small Businesses and Home Users Are Not Exempt
For home users, the answer is simple: install the May 2026 Windows security update. Most consumer systems will receive it through Windows Update, and for most people the security upside outweighs the familiar anxiety about Patch Tuesday regressions. A critical DNS Client RCE is not the kind of flaw to sit on for weeks because a printer driver once behaved badly.Small businesses face the harder middle ground. They may lack full patch orchestration, but they often have enough Windows laptops and servers to be attractive targets. They may also rely on consumer-grade routers, ISP-provided DNS, unmanaged switches, and VPN appliances that quietly become part of the trust chain.
For those environments, the practical move is to patch first and simplify DNS paths. Use trusted resolvers. Avoid letting endpoints choose arbitrary external DNS servers. Make sure remote workers connect through managed VPN profiles where appropriate. Confirm that routers and access points are not exposing clients to untrusted name-resolution behavior.
This is also a good moment to retire the idea that “we are too small to be targeted” applies to network worms, botnets, and opportunistic exploitation. If reliable exploit code emerges, attackers will not hand-select only Fortune 500 victims. They will scan, spray, phish for footholds, and abuse whatever infrastructure answers.
The Public Wi-Fi Angle Is Real, But It Is Not the Whole Story
Cybersecurity headlines will understandably lean into hostile public Wi-Fi. It is an easy image: a laptop in an airport lounge, a malicious network, and a Windows machine quietly accepting a poisoned DNS response. That scenario is plausible enough to matter, especially for executives, consultants, developers, and administrators who carry privileged devices between networks.But focusing only on public Wi-Fi understates the enterprise problem. Many attacks begin inside supposedly trusted environments. A compromised router in a branch office, a malicious device on a flat guest network, or an attacker who has gained a limited foothold may be better positioned to tamper with DNS than a random café adversary.
The distinction matters because mitigations differ. Travelers need patched laptops and sane VPN behavior. Enterprises need internal DNS discipline, network access control, segmentation, and monitoring for unauthorized resolvers. Cloud teams need to review VPC and virtual network DNS settings, especially in hybrid environments where Windows workloads span on-premises and cloud address spaces.
The common denominator is that DNS should no longer be treated as harmless plumbing. It is a control plane for application behavior, identity reachability, update retrieval, and user navigation. When the client parser is vulnerable, that control plane can become an execution path.
Detection Will Be Messy, So Do Not Bet on It Alone
Detecting exploitation of a memory corruption flaw in DNS Client processing is not as simple as writing a rule for a bad filename or a known command line. The triggering traffic may look like DNS, and the post-exploitation behavior may vary widely depending on the attacker’s payload. That makes patch state the most reliable control.Still, defenders can look for supporting signals. Unexpected resolver changes, endpoints querying unapproved DNS servers, unusual DNS response patterns, crashes or restarts in name-resolution-related processes, and suspicious child processes spawned around network activity all deserve attention. None of those signals proves exploitation by itself, but together they can narrow the hunt.
Endpoint detection and response platforms may help if exploit attempts move from memory corruption into payload execution. Network detection may help if malicious DNS responses are distinctive enough to fingerprint. But defenders should be careful not to confuse “we have telemetry” with “we can safely delay the patch.”
The more realistic role of detection is triage. It can identify systems that were exposed to risky DNS paths before patching, locate resolver misconfigurations, and reveal whether attackers are experimenting in the environment. It is not a substitute for removing the vulnerable code path.
Patch Management Has to Account for Mobile Windows
One of the most underappreciated changes in Windows security over the past decade is that the corporate perimeter dissolved faster than corporate patch discipline evolved. Laptops sleep through maintenance windows. Remote workers defer reboots. VPN clients connect after the machine has already joined a local network. BYOD-adjacent devices blur ownership.A DNS Client RCE punishes that gap. The vulnerable activity can happen before a user opens a business application. It can happen while the device is checking for connectivity, resolving update endpoints, or syncing background services. If the machine is unpatched, its physical location and current network may matter more than the elegance of the corporate firewall.
That should push administrators toward faster compliance loops. The important metric is not when the update was approved, but when vulnerable systems actually installed it and rebooted if required. Patch dashboards that look healthy because powered-off laptops have not checked in are not healthy.
Windows Autopatch, Intune, Configuration Manager, WSUS, RMM tools, and third-party patch platforms all have roles to play depending on the estate. The principle is the same across them: shorten the distance between release, deployment, reboot, and verification. For this class of flaw, “pending restart” is not a comforting state.
The Bigger May 2026 Lesson Is Infrastructure Fragility
CVE-2026-41096 is not the only serious issue in the May 2026 Microsoft release cycle. Reporting around the same Patch Tuesday also highlighted critical remote code execution vulnerabilities in areas such as Netlogon, Office, Dynamics, and cloud-connected Microsoft components. The DNS Client flaw, however, illustrates a particular kind of fragility: core infrastructure code can become a universal attack surface.That is the uncomfortable bargain of platform computing. Windows provides shared services so every application does not have to reinvent name resolution, authentication, printing, graphics, and file handling. When those shared services are robust, the platform gets safer. When they fail, the blast radius is enormous.
This is also why security teams should resist overly narrow asset prioritization. Internet-facing servers matter, but so do laptops. Domain controllers matter, but so do developer workstations. Crown-jewel databases matter, but so do the ordinary Windows machines that administrators use to reach them.
The attacker’s path rarely respects the asset inventory’s hierarchy. A modest endpoint flaw can become a privileged foothold. A resolver misconfiguration can become a payload delivery mechanism. A patch delay on a “low-risk” subnet can become the beginning of an incident report.
The Fix Is Straightforward; The Discipline Is Not
The immediate fix is to install Microsoft’s May 2026 security updates for affected Windows versions. That sentence is almost boring, which is precisely the problem. The most important security work in Windows administration often sounds mundane until the week it fails.For organizations that cannot patch every system immediately, mitigations should focus on reducing the chance that vulnerable clients receive untrusted DNS responses. Restrict outbound DNS to approved resolvers. Block direct DNS to the internet where business operations allow. Audit DHCP options. Watch for endpoints that suddenly use unexpected resolvers. Treat unauthorized DNS infrastructure as a security incident, not a harmless network quirk.
But compensating controls should be framed honestly. They reduce exposure; they do not erase the vulnerability. A laptop that leaves the managed network, a server in a poorly governed subnet, or a VPN configuration that allows local network DNS can still create an opening.
Administrators should also prepare for the second-order work. After emergency patching comes validation, exception cleanup, and root-cause review for systems that missed the window. The machines that are hardest to patch during a critical event are usually the same machines that will be hardest to defend during an intrusion.
The Windows DNS Warning Administrators Should Carry Into Friday
This patch deserves priority because it combines a critical score with a ubiquitous component and a low-friction attack model. The sensible response is not panic; it is disciplined acceleration. If an organization can turn this week’s DNS Client flaw into a better view of patch compliance and resolver control, it will come out stronger than it went in.- Organizations should deploy the May 2026 Windows cumulative updates to affected clients and servers as soon as operational testing allows.
- Security teams should treat roaming laptops and remote-worker devices as high-priority assets because they encounter the least trustworthy DNS environments.
- Network teams should restrict endpoint DNS traffic to trusted resolvers and verify that policy with observed traffic rather than diagrams.
- Detection teams should hunt for unexpected resolver changes, abnormal DNS paths, and suspicious process behavior following network activity.
- Administrators should not interpret “exploitation less likely” as “safe to defer,” because exploitability can change quickly after a patch is released.
Source: cyberpress.org Critical Windows DNS Client Flaw Enables Remote Code Execution