Anthropic’s decision to donate the Model Context Protocol (MCP) to a new Agentic AI Foundation under the Linux Foundation marks a decisive step toward industry-standard plumbing for “agentic” AI — the class of systems that act autonomously by connecting models to tools, data stores and services. The move bundles MCP with two other donated projects — Block’s goose agent framework and OpenAI’s AGENTS.md — into a single, vendor-neutral home backed by some of the largest cloud and platform players, and aims to accelerate interoperability, enterprise readiness and community governance for AI agents.
However, this is not a panacea. Significant engineering and governance work remains — particularly around registry trust, credential management, observability and supply-chain security — before MCP-based agentic systems can be considered production-safe at scale. If AAIF and its members prioritize transparency, robust security baselines, and inclusive governance, MCP can become the durable connective tissue that lets agents do useful, auditable work across the enterprise landscape. If they fail to address the trust and governance gaps, MCP risks becoming another well-intentioned standard splintered by proprietary extensions and uneven security practices.
For Windows-focused enterprise teams and developers planning agentic projects, the immediate practical step is to treat MCP like any external integration: require internal vetting, deploy via curated registries and instrument for audit and incident response from day one. The protocol’s promise is real — but its promise will be realized only through disciplined engineering and community governance.
Source: IT Brief UK https://itbrief.co.uk/story/anthropic-donates-mcp-to-new-agentic-ai-foundation/
 Background
Background
What is the Model Context Protocol (MCP)?
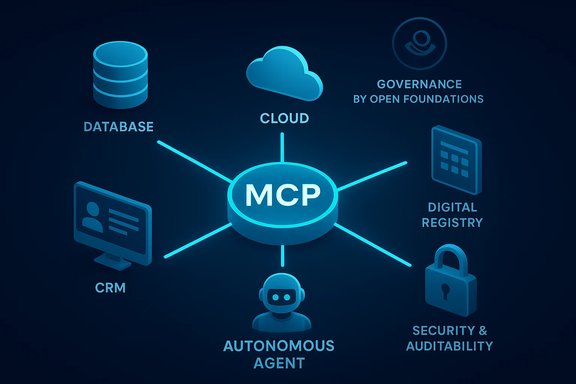
The Model Context Protocol (MCP) is an open protocol designed to standardize how AI systems discover, request, and use external resources — from document stores and databases to SaaS products and executable “tools.” It abstracts tool descriptions, resources and prompt templates into a consistent interface so any MCP-enabled agent can interact with any MCP server without bespoke integration work. That universality is the core value proposition: write one server connector, and multiple agent platforms can use it.The Agentic AI Foundation (AAIF)
The Agentic AI Foundation (AAIF) is a directed fund hosted by the Linux Foundation created to steward open standards and shared tooling for agentic AI. AAIF’s launch was co-led by Anthropic, OpenAI and Block and counts major technology firms — Google, Microsoft, Amazon Web Services, Cloudflare and Bloomberg — among its initial supporters. AAIF will incubate and govern founding projects (MCP, goose, AGENTS.md) using the Linux Foundation’s neutral governance model while funding shared infrastructure and community work.Why this matters now
Agentic AI is moving from demo to production
Over the past year the industry has shifted from demos of single-agent capabilities to production use cases that require reliable, auditable, and scalable access to enterprise systems. MCP’s architecture targets this exact transition by enabling agent workflows that can orchestrate multi-step tool usage while exposing security controls and auditability at the protocol level. Anthropic, OpenAI and other vendors have increasingly integrated MCP into platform tooling, meaning the protocol is no longer experimental — it’s becoming the interface layer many enterprises need.Network effects and reduced integration cost
One of MCP’s strongest pragmatic benefits is the network effect on integrations. Instead of building and maintaining N×M connectors (every agent to every tool), organizations can build an MCP server once and have it usable by any MCP-compatible agent. That efficiency explains rapid ecosystem growth and explains why cloud vendors and platform teams are investing in MCP support.The current technical state of MCP
Adoption and ecosystem metrics
Anthropic reports that MCP has seen broad adoption across AI platforms, infrastructure providers and corporate deployments. Company communications state there are more than 10,000 active public MCP servers, integrations into major agent platforms such as ChatGPT, Gemini, Microsoft Copilot, Cursor and Visual Studio Code, and cloud deployment options across AWS, Google Cloud, Cloudflare and Azure. Anthropic also highlights that Claude hosts a directory of 75+ connectors and that MCP SDKs have reached 97 million+ monthly downloads across Python and TypeScript — figures intended to demonstrate velocity and scale. These numbers are echoed by multiple industry outlets and the Linux Foundation announcement. Caveat: several of these counts are company-reported and reflect aggregate download or registration metrics; independent verification of precise, up-to-the-minute totals is non-trivial because registry crawlers, package mirrors and caching networks can inflate counts. Treat specific headline numbers as directional indicators of scale rather than immutable facts.Protocol features and recent spec work
The MCP specification has evolved rapidly. A late-2025 specification release added features aimed at production scenarios: asynchronous operations (for long-running tool invocations and event streams), statelessness (to ease scaling and server redeploy), explicit server identity mechanisms and an extensions model for vendor or domain-specific capabilities. Those capabilities are designed to make MCP usable in distributed, multi-tenant enterprise environments while balancing responsiveness and observability. Official SDKs and community-run registries and index sites provide implementations and discovery mechanisms for servers and connectors.Tooling: SDKs, registries and client features
MCP now has SDKs in major languages (TypeScript, Python, Go, Rust, Java, C#, etc., reference servers, a community registry for discovery, and integrations in both desktop and cloud client surfaces. Anthropic and other vendors have extended their APIs with features such as Tool Search and Programmatic Tool Calling to manage large numbers of tools and optimize latency in complex agent workflows. Those advances reflect real engineering work to make agents reliable at scale rather than ad-hoc lab experiments.What the donation to the Linux Foundation changes — and what it doesn't
Neutral stewarding and long-term sustainability
Placing MCP under the Linux Foundation / Agentic AI Foundation is primarily a governance shift intended to ensure vendor neutrality, sustainable community oversight, and shared infrastructure funding. Historically the Linux Foundation has successfully stewarded projects that became industry infrastructure (Kubernetes, Node.js, PyTorch), and AAIF aims to replicate that model for agentic AI primitives. The donation also bundles related projects (goose and AGENTS.md) to foster tighter interoperability between protocol, agent frameworks and project-specific guidance.Maintainers retained; governance formalized
Anthropic states the existing maintainers and governance processes for MCP will remain in place even after the transfer, signalling an intent to avoid abrupt changes that could break continuity. At the same time, AAIF’s structure introduces formal membership tiers and sponsorship models that will influence roadmaps, funding and operational priorities — a conventional trade-off between neutrality and corporate resource support.Not a takeover — but not a lockbox either
Donating code to a foundation is not the same as “locking down” a standard permanently. While the Linux Foundation provides neutral infrastructure and bylaws to prevent single-vendor capture, large corporate members inevitably have influence through funding, working groups and engineering contributions. The practical governance risk is influence, not outright control, and careful chartering and transparency will be required to keep MCP genuinely neutral.Benefits for enterprises and developers
- Reduced integration cost: build one MCP server and enable multiple agents and platforms.
- Standardized security posture: consistent authentication, auditing and server identity primitives allow enterprises to enforce policies everywhere agents run.
- Faster innovation: public registries, SDKs and community tooling shorten time-to-production for domain-specific connectors.
- Portability: AGENTS.md and MCP together make agent behavior more predictable across repositories and services, improving reproducibility for developer tools.
Risks, gaps and unresolved technical challenges
1. Trust and server vetting
A universal protocol increases the attack surface by making discovery and invocation of remote tools easier. If an MCP server is misconfigured, malicious, or compromised, an agent might be able to exfiltrate data, perform unauthorized actions, or execute unsafe workflows (so-called “tool poisoning”). Robust registry vetting, cryptographic signing of server descriptors, attestation, and enterprise-only whitelisting are critical mitigations that still need community-wide practices and tooling.2. Credential management and privilege scoping
Agents often need credentials to act on behalf of users (e.g., posting into Slack, querying financial systems). MCP supports identity primitives, but deploying securely requires mature practices: short-lived tokens, per-tool least-privilege, delegation protocols and detailed audit trails. Mistakes here could create systemic risk when agents have wide-ranging access. Enterprises will need hardened deployment patterns and gatekeeping to prevent privilege escalation.3. Governance capture and specification bloat
Even with the Linux Foundation as steward, dominant vendors can shape feature priorities. The more MCP grows to accommodate cloud provider-specific extensions, the higher the risk of fragmentation or “spec bloat,” which can undermine interoperability. A tight core spec plus extension registries, with strong compatibility guarantees, is essential to avoid recreating the very incompatibilities MCP is meant to solve.4. Observability and incident response
Statelessness and asynchronous operations improve scalability, but they complicate tracing and debugging distributed agent activity across multiple MCP servers and model providers. Standards for structured logging, trace context propagation and central observability will be required to make incident response practicable at enterprise scale.5. Supply-chain and package security
High SDK download numbers show adoption but also underscore the risk of supply-chain attacks through package repositories (npm, PyPI, etc.. Maintaining secure SDKs, reproducible builds, dependency pinning and signing toolchains must be treated as first-class engineering tasks for the MCP ecosystem. Several public package scanners already show large cumulative download counts for MCP packages — a strong signal to harden supply chain hygiene.Governance: what to watch for in AAIF’s early months
- Charter and membership rules: AAIF must publish an explicit charter that defines decision-making processes, contributor rights, and conflict-of-interest policies.
- Technical Steering Committee composition: ensure representation for independent maintainers, enterprise users, researchers and smaller vendors — not just platinum sponsors.
- Security baseline and certification: create and enforce a certification program (signed descriptors, security audits, CII-style badges) for MCP servers before they appear in the default public registry.
- Transparency in roadmap funding: AAIF should publish funding allocations and funded feature lists to avoid implicit vendor-driven roadmaps.
- Dispute and emergency response processes: formal procedures for vulnerability disclosure, spec rollback, and incident mitigation are necessary for enterprise trust.
Practical guidance for Windows and enterprise teams
- Treat MCP servers like external APIs: apply the same security reviews, code scanning and network segmentation you would for any third-party integration.
- Enforce least-privilege tokens and use ephemeral credentials — avoid hard-coded long-lived keys inside agents or servers.
- Use a privately curated registry for production: mirror public registries into a verified internal index and require policy checks before enabling a connector for production workloads.
- Instrument everything with structured logging and distributed traces to ensure auditability of agent actions across MCP servers and model providers.
- Establish incident playbooks focused on “agentic” failure modes (e.g., rapid automated actions, lateral movement via chained tool invocations).
Strategic implications for vendors and cloud providers
- Cloud and platform providers stand to benefit: MCP commoditizes connectors and makes platform-level provisioning of MCP servers a new value-add (managed MCP hosting, governance controls, and audited connectors).
- Model providers and LLM platforms gain a stronger ecosystem incentive to support MCP if it becomes the de facto agent connector; that increases choice for customers but also raises competitive pressure among platforms.
- Smaller tooling vendors can gain reach: a single MCP-conformant server can expose their product to multiple agent platforms, accelerating adoption without bespoke integrations.
- For enterprise software vendors, offering MCP-compatible servers will likely become a competitive requirement for being “agent-ready.”
The path forward — recommended safeguards and next steps
- Establish a rigorous registry trust model: signed capabilities, attestation, and an allowlist mechanism for enterprise-critical connectors.
- Define security conformance tests and automated CI checks for MCP SDKs and server templates.
- Fund independent audits of popular MCP servers and SDKs through AAIF grants to build trust quickly.
- Standardize observability primitives (trace IDs, structured events) to make cross-system auditing and compliance practical.
- Encourage interoperability testing events (plugfests) where competing agent clients and servers validate cross-compatibility on agreed scenarios.
Conclusion
Donating MCP to the Agentic AI Foundation and the Linux Foundation is a pragmatic recognition that agentic AI will only scale if the industry converges on neutral, interoperable interfaces. The move accelerates a transition from bespoke, fragile integration efforts to a shared infrastructure model where protocols, registries and certification create predictable behavior for agents across platforms. That’s a decisive win for enterprise adoption.However, this is not a panacea. Significant engineering and governance work remains — particularly around registry trust, credential management, observability and supply-chain security — before MCP-based agentic systems can be considered production-safe at scale. If AAIF and its members prioritize transparency, robust security baselines, and inclusive governance, MCP can become the durable connective tissue that lets agents do useful, auditable work across the enterprise landscape. If they fail to address the trust and governance gaps, MCP risks becoming another well-intentioned standard splintered by proprietary extensions and uneven security practices.
For Windows-focused enterprise teams and developers planning agentic projects, the immediate practical step is to treat MCP like any external integration: require internal vetting, deploy via curated registries and instrument for audit and incident response from day one. The protocol’s promise is real — but its promise will be realized only through disciplined engineering and community governance.
Source: IT Brief UK https://itbrief.co.uk/story/anthropic-donates-mcp-to-new-agentic-ai-foundation/