Cloud sovereignty is only as strong as the thinnest, most ambiguous stream of data that crosses a border — and for many sovereign-cloud promises that stream is metadata.
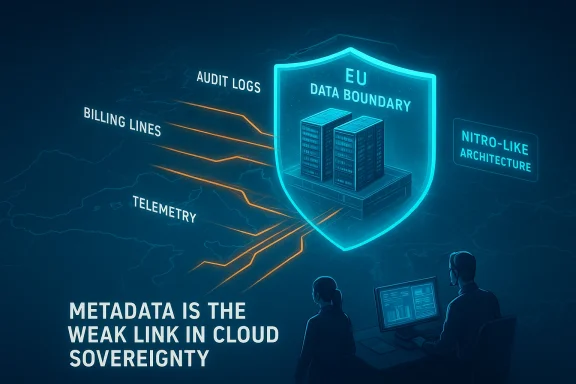
The recent conversations around the AWS European Sovereign Cloud and Microsoft’s EU Data Boundary have exposed a stubborn, uncomfortable truth: keeping files and application data physically inside a jurisdiction is necessary but not sufficient. Operational traces, telemetry, audit logs, routing records, billing details and other metadata can travel, be accessed, or be inferred in ways that defeat simple “data‑in‑region” assurances, and the industry’s current definitions and controls leave wide room for ambiguity and misunderstanding. This article unpacks what metadata actually means in cloud practice, maps the classes of metadata that matter for sovereignty, tests the claims made by hyperscalers and lawyers, and charts practical steps governments and enterprises should take to reduce risk — because in cloud sovereignty, the devil is not in the data; it’s in the data about the data.
Hyperscale providers advertise “sovereign” offerings and regional data boundaries to answer regulatory and political demand for local control. Those services promise that customer content — the files, databases and application payloads customers put in the cloud — will remain inside the agreed geographic boundary. AWS has publicly described architectural controls such as the Nitro System and contractual commitments designed to prevent operator access to customer content, and AWS argues customers retain ownership and control over their content.
Microsoft’s EU Data Boundary likewise sets out a commitment to keep customer and pseudonymized personal data within the EU/EFTA footprint for participating services, while acknowledging narrow exceptions and legal obligations.
Those commitments are real and operationally significant. But they do not end the story. Multiple independent technical and legal analyses — and media coverage of hearings with hyperscaler representatives — show that metadata and telemetry remain poorly defined, often intentionally so, and that this gray area can erode the practical assurance of sovereignty. The French Senate hearing where Microsoft France’s legal director declined to guarantee that EU data could never be disclosed to U.S. authorities crystallized the political dimension of the problem.
Another often‑cited example is the Strava heatmap controversy, where aggregated fitness metadata inadvertently illuminated forward operating military bases and patrol routes. What looked like innocuous activity traces became intelligence for adversaries because of correlation and geospatial analysis. That case shows the asymmetric sensitivity of metadata: a single seemingly banal stream, when aggregated and cross‑referenced, becomes highly revealing.
A legal memorandum cited in trade media argued that the AWS sovereign offering prevents AWS from accessing customer content and certain configuration metadata, but left open whether telemetry and operational metadata could still cross borders — precisely the ambiguity regulators and customers worry about. The law firm’s analysis (reported publicly) was later difficult to retrieve in full, and some referenced copies appear offline; that absence matters because it prevents independent verification of the more reassuring legal reading. Tech reporting that relied on that memo noted the split between “customer data” kept in the region and other operational metadata that may not be.
Two practical risks emerge from the AWS example:
Metadata cannot be treated as a footnote; it must be elevated to the same level of contractual and technical protection as files and application data. That requires transparency, verifiable architecture, stronger contractual guarantees and regulatory frameworks that demand auditable controls and clear rules on who may view which telemetry and where it can be stored.
The good news is practical mitigations exist: customer‑controlled keys, provable locality through attestation, hardened audit logs, and explicit contractual classification of telemetry. The hard part is political and organizational: buyers must insist on them, vendors must build them into standard offerings, and regulators must demand independent verification. Until that alignment happens, metadata will remain the weak spot in cloud sovereignty — a small, often invisible leak that is nevertheless capable of undoing the protections that sovereign clouds promise.
Source: Techzine Global Metadata, cloud sovereignty's weak spot
The recent conversations around the AWS European Sovereign Cloud and Microsoft’s EU Data Boundary have exposed a stubborn, uncomfortable truth: keeping files and application data physically inside a jurisdiction is necessary but not sufficient. Operational traces, telemetry, audit logs, routing records, billing details and other metadata can travel, be accessed, or be inferred in ways that defeat simple “data‑in‑region” assurances, and the industry’s current definitions and controls leave wide room for ambiguity and misunderstanding. This article unpacks what metadata actually means in cloud practice, maps the classes of metadata that matter for sovereignty, tests the claims made by hyperscalers and lawyers, and charts practical steps governments and enterprises should take to reduce risk — because in cloud sovereignty, the devil is not in the data; it’s in the data about the data.
 Background
Background
Hyperscale providers advertise “sovereign” offerings and regional data boundaries to answer regulatory and political demand for local control. Those services promise that customer content — the files, databases and application payloads customers put in the cloud — will remain inside the agreed geographic boundary. AWS has publicly described architectural controls such as the Nitro System and contractual commitments designed to prevent operator access to customer content, and AWS argues customers retain ownership and control over their content.Microsoft’s EU Data Boundary likewise sets out a commitment to keep customer and pseudonymized personal data within the EU/EFTA footprint for participating services, while acknowledging narrow exceptions and legal obligations.
Those commitments are real and operationally significant. But they do not end the story. Multiple independent technical and legal analyses — and media coverage of hearings with hyperscaler representatives — show that metadata and telemetry remain poorly defined, often intentionally so, and that this gray area can erode the practical assurance of sovereignty. The French Senate hearing where Microsoft France’s legal director declined to guarantee that EU data could never be disclosed to U.S. authorities crystallized the political dimension of the problem.
What we mean by “metadata” — and why it resists neat definition
Metadata is information about information — so it can be anything
At a conceptual level, metadata is any descriptor that contextualizes primary data: timestamps, IP addresses, file names, resource identifiers, roles and permissions, billing records, routing logs, telemetry on CPU and network usage, service‑level events, and audit logs. The problem for sovereignty is twofold:- The set of things that can be usefully called metadata is effectively unbounded. Anything that helps manage, observe, bill or secure a cloud service can be framed as metadata.
- Different stakeholders classify items differently. What an operator calls “operational telemetry” a privacy-conscious regulator might call “sensitive metadata” because, in aggregate or when correlated, it reveals patterns that are as revealing as files themselves.
Taxonomy: practical classes of metadata to watch
For the purposes of evaluation and policy design, it’s useful to treat metadata as several overlapping classes:- Administrative / Audit Metadata: Admin Activity logs, IAM changes, role assignments, resource creation events. These are often always recorded and cannot be fully disabled (Google Cloud’s Admin Activity logs are always on, for example).
- Operational Telemetry: VPC Flow Logs, CPU/memory metrics, routing and packet telemetry, autoscaling events, health checks. Used for capacity planning and availability engineering; often aggregated but sometimes quite granular. AWS CloudWatch and unified telemetry services are explicitly built to collect and centralize this type of data.
- Audit / Access Logs with Identity Data: Data Access logs and Cloud Audit Logs that can contain caller identities, IP addresses and resource access trails. These can be selectively configurable (e.g., Google Cloud’s Data Access logs require opt‑in for most services), but when generated they often expose precise “who/when/where” information.
- Billing and Metering Records: Measurements of resource consumption, costs by account, invoice items and SKU‑level usage. Alone they look benign; combined with region, account and timing they can effectively fingerprint a customer’s workload and scale.
- Support & Debugging Artifacts: Traces, crash dumps, and session recordings used for troubleshooting. Vendors provide opt‑outs for some training and behavior telemetry, but vendor-side packet routing and billing telemetry is generally treated as essential.
Who gets to see metadata — the critical question hyperscalers don’t fully answer
A core point in vendor marketing is the split between what data is kept regionally and who has access. AWS, Microsoft and Google emphasize that customer content remains controlled by the customer while operations teams may need limited access to certain telemetry to keep services healthy. But who — the nationality, location and legal status of the staff with access — matters immensely for sovereignty.- AWS describes architectural measures (e.g., Nitro) that limit operator access to customer content, and says routine operator access is logged and auditable. But the company also acknowledges some categories of operational metadata are required for services to function and are collected by centralized systems.
- Microsoft’s EU Data Boundary promises regional storage and processing for customer data for selected services, yet Microsoft’s testimony in France showed the legal exposure to U.S. demands under the CLOUD Act remains an unsolved cross‑jurisdictional risk.
- Vendors may staff “sovereign” regions with local employees — AWS has indicated the European Sovereign Cloud will be managed separately and transition to EU staff — but staffing rules are an operational control, not a legal firewall. Even when European employees handle support, centralized monitoring or aggregated telemetry can still cross borders. News reporting and vendor FAQs note that separate management entities and EU‑based teams are part of the design for some sovereign clouds, but they do not produce full transparency about what telemetry is viewable outside the region.
Why metadata is valuable — not just to vendors, but to adversaries
Metadata is not inert. When correlated, it becomes intelligence.- Billing and resource consumption spikes can reveal the scale and timing of sensitive computations — for example, a government customer spinning up large GPU clusters at predictable intervals is easily profiled by cost and usage telemetry.
- Network flow logs and VPC telemetry can reveal IP blocks, peering arrangements and traffic volumes that point to system interconnections and operational patterns.
- Audit logs expose who changed permissions, created resources, or accessed specific services; that can reconstruct organizational structure and operational tempo.
- Support traces and crash dumps often include environment variables, instance names or pointers to internal repository names that de‑anonymize operators or teams.
Another often‑cited example is the Strava heatmap controversy, where aggregated fitness metadata inadvertently illuminated forward operating military bases and patrol routes. What looked like innocuous activity traces became intelligence for adversaries because of correlation and geospatial analysis. That case shows the asymmetric sensitivity of metadata: a single seemingly banal stream, when aggregated and cross‑referenced, becomes highly revealing.
The AWS European Sovereign Cloud case — technical promises, legal gaps, and a missing independent report
AWS launched a separate European Sovereign Cloud to address data‑residency and regulatory concerns, emphasizing that management will be regionally organised and that core protections like Nitro limit operator access to customer content. The move is a concrete response to long‑running European anxieties about cloud dependency.A legal memorandum cited in trade media argued that the AWS sovereign offering prevents AWS from accessing customer content and certain configuration metadata, but left open whether telemetry and operational metadata could still cross borders — precisely the ambiguity regulators and customers worry about. The law firm’s analysis (reported publicly) was later difficult to retrieve in full, and some referenced copies appear offline; that absence matters because it prevents independent verification of the more reassuring legal reading. Tech reporting that relied on that memo noted the split between “customer data” kept in the region and other operational metadata that may not be.
Two practical risks emerge from the AWS example:
- Small customer pools reduce anonymity. Sovereign cloud regions, by design, will serve a smaller set of customers (governments and large regulated entities). Even aggregated telemetry can be deanonymized if there are few tenants in a given datacenter or availability zone. If a vendor can see resource labels, placement and billing at a granular level, identifying the tenant is often trivial.
- Operational metadata touches many centralized services. Telemetry systems (CloudWatch, flow logs, centralized control planes) sometimes centralize data for performance, analysis and product improvement. Vendors offer opt‑outs for some kinds of data used to train AI models or improve features, but they rarely allow opt‑outs for billing, packet routing and core telemetry that underpin the service. That telemetry is precisely the kind that can leak operational secrets.
What vendors say they collect, and what they don’t usually disclose
Cloud vendors publish extensive documentation about audit logs, telemetry and operational data, but the level of detail on where that telemetry is stored, who can access it, and under what legal process it might be disclosed varies.- Google Cloud: documents a clear separation of Admin Activity and Data Access audit logs, with Admin Activity logs always being recorded and Data Access logs often configurable. Google also offers Access Transparency to log staff access to customer content.
- Microsoft: the EU Data Boundary program lists the services included and the boundary commitments while acknowledging limited, enumerated exceptions where transfers may still occur. Those exceptions and the legal interplay with foreign access laws were the heart of the French Senate discussion.
- AWS: publishes its European sovereignty FAQ and emphasizes architectural controls like Nitro and operator‑access limitations, but also documents centralized telemetry and billing systems and practical opt‑out routes for non‑essential data collection. Vendor posts and FAQs explain how the CLOUD Act functions and reiterate the company’s practices when responding to law‑enforcement process.
Why independent verification matters — and the limits of vendor PR
Vendors can make credible technical claims — Nitro’s design, zero‑operator access attestations, audited controls — but sovereignty requires more than vendor assurances:- Independent architecture reviews and attestation (external auditors, red‑teams and publicly available architecture reports) are essential to test whether the boundary between content and metadata is enforced in practice and whether telemetry paths could leak outside the region. AWS has published independent assessments of Nitro’s operator‑access limitations; those are useful but do not answer every metadata question.
- Legal clarity and enforceable contract terms are required so customers know exactly what metadata may be accessed, who may access it, and where it is stored. Vague marketing commitments do not substitute for contractually binding technical controls and audit rights.
- Regulatory inspection and third‑party audit access allow sovereign purchasers (states, regulated industries) to verify compliance on the ground. Without that, vendors can credibly claim that “some telemetry stays local” while essential traces are centralised elsewhere.
- Transparency about exception handling and lawful disclosure is essential. Cloud vendors have policies describing how they handle lawful requests, but the interplay of local law, cross‑border process and service architecture requires far more granular transparency for sovereign customers.
Practical steps for buyers, regulators and vendors
Metadata risk is manageable — but only with clear technical, contractual and governance changes. Below are prioritized steps for the three key actors.For sovereign buyers (governments, regulated agencies)
- Treat metadata as first‑class regulated material. Contractually require vendors to classify and localize every telemetry stream, with auditable controls and technical proof of locality.
- Insist on observable controls (audit APIs, access transparency logs, cryptographic attestations) that show who accessed what metadata and when.
- Use customer‑controlled encryption and key management where possible; hold keys in national HSMs when lawful and technically feasible to sever the provider’s ability to decrypt support traces.
- Request staffed guarantees and sanctions. Staffing EU nationals in the region is useful but insufficient; contracts must include penalties for unauthorized metadata access and allow for independent audits.
For enterprises
- Map your metadata footprint. Know where your logs, metrics, billing records and support artifacts are stored and who can reach them.
- Minimize metadata leakage. Use resource naming policies, tag minimization, and avoid embedding PII in identifiers or labels.
- Segment workloads. Put the most sensitive workloads behind tenant‑isolated boundary designs and consider private or dedicated cloud solutions for high‑sensitivity operations.
For vendors
- Publish precise metadata classifications and region‑of‑origin maps for every telemetry class.
- Offer provable local processing modes with cryptographic attestation and immutable audit trails for metadata access.
- Provide contractual audit rights and transparent lawful disclosure reporting, including redacted examples of typical metadata disclosed under legal process.
Conclusion — metadata is the weak link, but not an intractable one
Sovereign cloud offerings are a meaningful evolution: they reflect hyperscalers responding to legitimate regulatory and operational needs. But the current model too often separates data from metadata in ways that privilege vendor operational freedom over customer sovereignty. As the AWS European Sovereign Cloud, Microsoft’s EU Data Boundary and the EU’s regulatory scrutiny show, we have reached a moment where technical design, legal process and public policy must meet.Metadata cannot be treated as a footnote; it must be elevated to the same level of contractual and technical protection as files and application data. That requires transparency, verifiable architecture, stronger contractual guarantees and regulatory frameworks that demand auditable controls and clear rules on who may view which telemetry and where it can be stored.
The good news is practical mitigations exist: customer‑controlled keys, provable locality through attestation, hardened audit logs, and explicit contractual classification of telemetry. The hard part is political and organizational: buyers must insist on them, vendors must build them into standard offerings, and regulators must demand independent verification. Until that alignment happens, metadata will remain the weak spot in cloud sovereignty — a small, often invisible leak that is nevertheless capable of undoing the protections that sovereign clouds promise.
Source: Techzine Global Metadata, cloud sovereignty's weak spot