Microsoft’s answer to the Swiss question of “who controls my data?” is no longer a single checkbox in a contract — it is now a multi-tiered product, legal and operational commitment that blends in‑country infrastructure, customer‑controlled cryptography, human‑in‑the‑loop access approvals, and formal legal promises designed to withstand geopolitical pressure.
Digital sovereignty has moved from academic debate to boardroom priority. Swiss companies and public institutions are asking three concrete questions: *Where is my data stored? Who can access it? And can I keep using the latest cloud capabilities while remaining c Microsoft’s Swiss program aims to answer all three by matching technical controls to contractual and legal guarantees — a posture it laid out publicly in its Swiss briefings and European commitments.
At the same time, the legal backdrop is complex. The U.S. CLOUD Act, domestic e‑evidence regimes in the EU, and expanding national security laws worldwide mean that location alone is not a mmunity from foreign access. Independent legal analysis (including a recent CMS white paper) and Microsoft’s own explanations underscore that legal conflict is possible, but that providers and customers have technical and procedural mitigations to reduce exposure.
This article explains what Microsoft is offering in Switzerland, how those controls work in practice, which claims are verifiable, and—critically—where important risks remain for Swiss buyers and policymakers.
Key practical points:
Microsoft and independent legal experts emphasize an important truth: technical controls (keys, in‑region processingccess) reduce exposure, but they do not nullify transnational legal processes. The U.S. CLOUD Act clarifies when U.S. law enforcement can request data from providers even when data is stored abroad; it also creates a statutory route for providers to challenge requests where there is a conflict with foreign law. Microsoft’s public position is that it will challenge requests that violate foreign law and that disclosures of foreign enterprise content to U.S. law enforcement have been exceptionally rare in its transparency reports. The Microsoft briefings (provided to customers) include a set of myth‑busting clarifications about the CLOUD Act and its limits.
Independent legal review matters: a recent white paper by CMS (a major international law firm) describes the CLOUD Act as a real, but nuanced, risk — noting that comity challenges exist but have rarely been tested in court, and that extraterritorial access is not unique to the U.S. (many jurisdictions have comparable powers). The white paper aligns with Microsoft’s technical mitigations while underscoring the need frds and litigation readiness.
Important practical caveat: legal doctrine like comity and the ability to quash or narrow orders is time‑consuming and fact‑specific. For the highest‑value, mission‑critical systems, legal remedies are not a substitute for technical isolation and encryption under customer control.
But this is not a panacea. Legal tools like the CLOUD Act and broader extraterritorial access regimes remain in play; judicial comity and quash procedures are a safety valve — not a guarantee. The final verdict for any organization will depend on careful data classification, contractual rigor, independent verification and willingness to invest in local operational capability.
If Swiss institutions insist on the right controls, demand concrete contractual and audit evidence, and architect for portability and redundancy, they will find Microsoft’s sovereign portfolio a pragmatic, powerful option — one that should be judged against independent technical and legal testing, not marketing alone.
Source: Microsoft Source How Microsoft is addressing digital sovereignty in Switzerland - Source EMEA
 Background / Overview
Background / Overview
Digital sovereignty has moved from academic debate to boardroom priority. Swiss companies and public institutions are asking three concrete questions: *Where is my data stored? Who can access it? And can I keep using the latest cloud capabilities while remaining c Microsoft’s Swiss program aims to answer all three by matching technical controls to contractual and legal guarantees — a posture it laid out publicly in its Swiss briefings and European commitments.At the same time, the legal backdrop is complex. The U.S. CLOUD Act, domestic e‑evidence regimes in the EU, and expanding national security laws worldwide mean that location alone is not a mmunity from foreign access. Independent legal analysis (including a recent CMS white paper) and Microsoft’s own explanations underscore that legal conflict is possible, but that providers and customers have technical and procedural mitigations to reduce exposure.
This article explains what Microsoft is offering in Switzerland, how those controls work in practice, which claims are verifiable, and—critically—where important risks remain for Swiss buyers and policymakers.
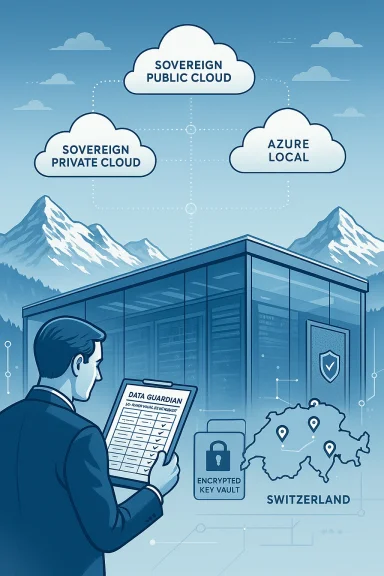
What Microsoft is offering in Switzerland: a layered sovereignty portfolio
Microsoft has movedereign cloud” label. Its product architecture for Switzerland (and the broader EU/EFTA region) is intentionally layered to map to different sovereignty needs:- Sovereign Public Cloud — sovereignty controls applied across existing European regions (including Swiss regions), enabling data residency, stronger encryption management, and regulated environment controls without forcing customers to migrate to completely separated datacenters.
- Sovereign Private Cloud / Azure Local — for organizations that require maximum operational autonomy, Microsoft offers Azure Local (and Microsoft 365 Local) to run workloads in customer‑controlled, partner‑operated, or on‑premises environmAzure management. Recent product updates moved disconnected and on‑premises modes closer to production readiness.
- Key technical capabilities:
- Data Guardian — Europe‑based access approval and monitoring that ensures remote engineer access to European systems is approved and overseen by European‑resident personnel and logged immutably.
- External Key Management / Customer‑controlled keys — customers can keep encryption keys in their own HSMs or trusted third parties via Azure Key Vault and Purview Customer Key.
- Regulated Environment Management — a centralized governance plane to apply, monitor and audit sovereignty controls.
Where data lives and who can access it — the technical, contractual and operational layers
Swiss customers care about three separate but related properties: residency (data physically stored in Switzerland), access control (who can view/process that data),ation** (where compute happens, including in‑country AI inference). Microsoft addresses each through a combination of infrastructure, policy and tooling.- Residency: Microsoft has operated cloud regions in Switzerland since 2019 (near Zurich and Geneva) and states that its EU/EFTA boundary d processing of customer data and professional services data within those regions for qualifying customers and services. That EU Data Boundary effort was completed in February 2025.
- Access controls and human oversight:
- Customer Lockbox (for Microsoft 365 and select services) enables customers to review and approve engineer access requests. Data Guardian extends this by requiring that any remote access to systems that store Europeanroved and monitored by Microsoft employees resident in Europe and recorded in a tamper‑evident ledger. Microsoft documents Data Guardian as a core sovereignty control.
- Confidential Compute and hardware‑protected enclaves reduce the risk that even platform operators can read customer data while it’s processed. Microsoft points to Confidential Compute as a way to create cryptographic guarantees that the cloud provider cannot access certain datasets.
- Cryptography and key control: Microsoft highlights options to keep keys outside Microsoft’s control (external key management) and to use tools like Azure Key Vault and Purview Customer Key to produce auditable key operations, plus Azure Confidential Ledger for immutable logs. These technical controls are central to any sovereignty posture because they materially change whether a provider can comply with an order that demands plaintext access.
- In‑country AI processing: Microsoft committed to expand in‑country processing for Copilot interactions and to include end‑to‑end AI data processing in the EU Data Boundary. That promises to keep AI interactions and associated training/telemetry inside the EU/EFTA unless a customer opts otherwise — a crucial detail for institutions concerned about AI‑related data flows. Independent coverage and Microsoft documentation confirm that in‑region AI processing is part of the EU Data Boundary rollout.
If you need full operational autonomy: Azure Local, Microsoft 365 Local and disconnected modes
Some Swiss public bodies and regulated firms must run services in physically controlled environments — sometimes fully air‑gapped. Microsoft’s response is a pragmatic one: bring Azure into the customer or partner datacenter.Key practical points:
- Azure Local delivers Azure services into a customer or partner‑operated, in‑country environment, supporting connected, hybrid and disconnected scenarios with consistent tooling. It aims to blend Azure’s management and security with local operational control. Recent product updates increased supported scale, added external SAN support and GPU options.
- Microsoft 365 Local offers a validated architecture to run core productivity workloads (Exchange Server, SharePoint Server, Skype for Business Server) natively on Azure Local, letting organizations retain familiar server‑based workloads under local operational control while still integrating with cloud management where appropriate. Industry reporting and Microsoft announcements indicate Microsoft 365 Local is generally available and intended to support sovereign, disconnected deployments.
- Foundry Local and local LLM hosting: Microsoft is extending the model to support large multimodal models in private environments (Foundry Local), designed for organizations that must keep LLMs and inference entirely on‑premises. Tech press coverage confirms Microsoft has been shipping capabilities for deploying models into private, air‑gapped hardware pools.
Legal and policy commitments: a new layer of contractual guarantees
Microsoft’s technical changes are reinforced with legal and contractual commitments aimed at reassuring European and Swiss customers:- EU Data Boundary: completed February 26, 2025, this engineering and contractual milestone restricts storage and processing of certain customer and professional services data to EU/EFTA regions for qualifying customers and services. Microsoft published the boundary and its scope in a corporate blog post.
- European Digital Resilience Commitment and board oversight: Microsoft has said it will contest any order to suspend or cease cloud operations in Europe and has committed to storing critical code backups in Switzerland alongside establishing European board oversight for datacenter operations. These are legal and operational safeguards aimed at limiting political leverage that might be exerted through continental outages or supply‑chain coercion. Independent reporting csels remarks and corroborated the resilience commitments.
- Transparency & audits: Microsoft centralizes certifications and audit reports in a Trust Center, allows qualified government reviews under specific programs, and publishes biannual transparency reporting on government requests. Those transparency measures are intended to let customers and auditors verify behavior.
Microsoft and independent legal experts emphasize an important truth: technical controls (keys, in‑region processingccess) reduce exposure, but they do not nullify transnational legal processes. The U.S. CLOUD Act clarifies when U.S. law enforcement can request data from providers even when data is stored abroad; it also creates a statutory route for providers to challenge requests where there is a conflict with foreign law. Microsoft’s public position is that it will challenge requests that violate foreign law and that disclosures of foreign enterprise content to U.S. law enforcement have been exceptionally rare in its transparency reports. The Microsoft briefings (provided to customers) include a set of myth‑busting clarifications about the CLOUD Act and its limits.
Independent legal review matters: a recent white paper by CMS (a major international law firm) describes the CLOUD Act as a real, but nuanced, risk — noting that comity challenges exist but have rarely been tested in court, and that extraterritorial access is not unique to the U.S. (many jurisdictions have comparable powers). The white paper aligns with Microsoft’s technical mitigations while underscoring the need frds and litigation readiness.
Important practical caveat: legal doctrine like comity and the ability to quash or narrow orders is time‑consuming and fact‑specific. For the highest‑value, mission‑critical systems, legal remedies are not a substitute for technical isolation and encryption under customer control.
Independent verification: what’s provable today
Some of Microsoft’s claims are fully verifiable in public records and independent reporting; others require greater scrutiny:- Verifiable and corroborated:
- USD 400 million investment announced June 2, 2025 — confirmed by Microsoft’s Switzerland press release and independent reporting.
- Completion of the EU Data Boundary (Feb 26, 2025) — documented in Microsoft’s public blog post and covered across trade press.
- Data Guardian capability and design — described in Microsoft Learn and covered by industry outlets. This is an engineering capability with explicit design details (European approvers, tamper‑evident ledger).
- Azure Local / Microsoft 365 Local availability and enhanced disconnected capabilities — corroborated by product announcements and press reporting that identify GA or production readiness and describe supported features.
- Claims that require careful interpretation or remain partially unverifiable externally:
- Absolute protection from any foreign government access — Microsoft states it does not provide governments with the ability to break encryption and that it will challenge improper orders; these are contractual and legal commitments rather than absolute technical impossibilities. They reduce risk but cannot eliminate it in every hypothetical. Independent legal commentary notes that the comity/quash route exists but is untested in many scenarios.
- Every operational promise in edge/disconnected scenarios at scale — product announcements and press coverage confirm GA or near‑GA in many areas, but large, air‑gapped, model‑hosting deployments are still complex and require validated architecture, testing and co‑engineering with partners. Organizations should treat these options as powerful but operationally non‑trivial.
Strengths: what Microsoft gets right for Swiss customers
- Comprehensive, layered approach — Microsoft no longer offers only one model; customers can choose public sovereign controls, private/partner operated clouds, or full on‑premises Azure Local options depending on their risk profile. This is a practical match for diverse Swiss needs.
- European operational oversight (Data Guardian) — human‑in‑the‑loop approvals routed to Europe‑resident staff plus tamper‑evident logging represent a mature operational control that directly addresses a core sovereignty worry: who can reach my systems?
- Contracts and legal commitments — EU Data Boundary, Digital Resilience Commitments, and board oversight create a contractual layer that augments technical protections and gives governments and large enterprises definable remedies and expectations.
- Investment and ecosystem integration — Microsoft’s USD 400M investment and collaborations with Swiss universities and innovation hubs strengthen local capability, create supplier ecosystems and make multi‑vendor, sovereign cloud architectures more realistic. For many Swiss buyers, a local partner ecosystem is as important as technology alone.
- Security telemetry and scale — Microsoft’s global security telemetry (tens of trillions of signals per day, blocking thousands of password attacks per second) underpins defensive services available to Swiss customers. Those signals make platform security stronger and are a valid argument for the defensive value of a hyperscale provider.
Risks, trade‑offs and open questions for Swiss organizations
No solution is risk‑free. The most important trade‑offs and risks include:- Legal unpredictability remains — comity tests and cross‑border quash procedures are fact‑specific and largely untested; legal remedies are not instantaneous. Organizations requiring absolute immunity must rely on technical isolation and customer‑held encryption keys, not legal promises alone.
- Operational complexity and cost — Azure Local and Microsoft 365 Local introduce distributed operational models that require co‑engineering, local ops skills, and potentially higher capital and operational expense compared with standard public cloud deployments. Expect multiyear projects for fully air‑gapped LLM hosting or disconnected enterprise productivity stacks.
- Vendor concentration risk — relying on one vendor for both sovereign tooling and local operations concentrates risk. Multi‑vendor strategies, open standards and exit rights remain essential procurement disciplines despite Microsoft’s portability claims. Microsoft asserts portability and open standards, but migration complexity can still be real.
- Verification and auditability — while Microsoft provides Trust Center materials and transparency reporting, Swiss customers should budget for independent audits, penetration testing, and contractually required evidence of operational practices (e.g., Data Guardian logs, key‑usage records). Transparency centers and code reviews exist, but access and scope are limited by program eligibility and legal protections.
- National policy harmonization — Swiss public authorities must define precise procurement standards and security baselines. Countries with clear sovereign cloud certification frameworks can more easily evaluate vendor claims. Absent standardized certification, each contract negotiation becomes an ad hoc evidence exercise. CMS and other legal commentators warn that policy gaps and uneven regulatory testing leave unresolved risks.
Practical checklist for Swiss buyers (what to demand and verify)
- Classify data and map to levels of protection — explicitly label data that requires in‑country processing, customer key custody, or air‑gapped compute.
- Choose the right cloud tier — Sovereign Public Cloud for broad workloads; Azure Local / Microsoft 365 Local for high‑control or air‑gapped needs.
- Insist on customer‑controlled keys for sensitive datasets — deploy HSMs under customer or trusted third‑party custody and log all key operations.
- Contractualize resilience and legal commitments — require express contract clauses that echo Microsoft’s public commitments (e.g., Digital Resilience Commitment), and specify dispute resolution, access to logs, and right to audit.
- Require independent verification — include audit windows, third‑party security attestations, and access to tamper‑evident logs (or extracts) for compliance teams.
- Build an exit and portability plan — validate data export procedures, test migration scripts, and budget for the work required to move off a sovereign configuration.
- Invest in local ops and hybrid skills — deploy internal teams or vetted partners capable of operating Azure Local, managing HSMs, and running LLMs in private environments.
- Run tabletop exercises for legal incident response — rehearse the procedure if a government request arrives, including legal, technical and communication steps.
Conclusion — a pragmatic path, not a perfect shield
Microsoft’s Swiss sovereignty package represents a major evolution: it ties together physical regions, customer‑controlled cryptography, human‑in‑the‑loop access controls, on‑premises Azure bricks and explicit legal commitments. For many Swiss enterprises and public bodies, that combination materially reduces practical exposure and provides a credible path to operational sovereignty while preserving access to hyperscale capabilities.But this is not a panacea. Legal tools like the CLOUD Act and broader extraterritorial access regimes remain in play; judicial comity and quash procedures are a safety valve — not a guarantee. The final verdict for any organization will depend on careful data classification, contractual rigor, independent verification and willingness to invest in local operational capability.
If Swiss institutions insist on the right controls, demand concrete contractual and audit evidence, and architect for portability and redundancy, they will find Microsoft’s sovereign portfolio a pragmatic, powerful option — one that should be judged against independent technical and legal testing, not marketing alone.
Source: Microsoft Source How Microsoft is addressing digital sovereignty in Switzerland - Source EMEA