Nvidia’s move to wrap the runaway popularity of OpenClaw in a structured, policy-driven runtime is both pragmatic and strategic: NemoClaw promises to keep the promise of always-on, local-first AI agents while reducing the very real security and privacy risks that have made enterprises and governments nervous over the last few months.
OpenClaw—an open-source, local-first agent framework that rose to prominence for its ability to run autonomous tasks on a user’s device—sparked a torrent of real-world experimentation and rapid adoption. Its core innovation is simple and powerful: instead of being a single chat model, OpenClaw orchestrates multiple models and tools (often combining cloud-hosted frontier models and local models) and gives those agents permission to take actions on the host machine and across the web. That autonomy is what made OpenClaw so compelling: scheduling, email triage, file management, browsing, and multi-step automation could all happen without a human in the loop.
But that same autonomy exposed a new attack surface. Security researchers, vendors, and some national governments raised alarms about unguarded tool access, malicious “skills,” credential aggregation, and the potential for rapid, automated data exfiltration or destructive commands. In response to that security scramble, Nvidia announced NemoClaw at GTC as a layered approach—an infrastructure and runtime stack designed to make agentic AI safer for enterprises, while preserving local capabilities and the flexibility that made OpenClaw popular.
This article explains what NemoClaw claims to do, how its pieces fit together, the trade-offs and blind spots security teams should watch for, and what NemoClaw’s debut means for the larger ecosystem of open models and agentic AI.
Nvidia frames NemoClaw as an integration of several components:
For enterprises that need auditable, adaptable models—and for developers who want to fine-tune base models for specialized tasks—an open coalition makes sense. Open foundations reduce lock-in and let organizations build domain-specific capabilities on top of a commonly audited base.
That said, open models and agent runtimes together can increase diffusion of capabilities. NemoClaw attempts to offset that risk by coupling an open model strategy with hardened runtime controls (OpenShell). The net result is a bet that open weights plus strong runtime policy = broad innovation without wholesale operational risk.
But success depends on adoption and, critically, on community scrutiny. The open-source model for the runtime and toolkit helps: independent researchers can probe OpenShell and the NeMo Agent Toolkit for gaps. The industry needs timely disclosures, bug bounties, and a transparent governance model for the coalition models to build real trust.
Yet implementation details and operational realities will determine whether NemoClaw is an incremental improvement or a genuinely transformative platform for secure agent deployment. The hard work remains in the trenches—policy design, secure skill management, telemetry hygiene, and human governance.
For IT leaders and security teams, the right posture is measured curiosity: pilot NemoClaw where the business benefit is clear, run aggressive adversarial tests, and insist on transparency about policy semantics, audit guarantees, and coalition model provenance before entrusting agents with high-value work. Agentic AI can be a force multiplier—when it is respectfully constrained and vigilantly managed.
Source: ZDNET Nvidia bets on OpenClaw, but adds a security layer - how NemoClaw works
 Background
Background
OpenClaw—an open-source, local-first agent framework that rose to prominence for its ability to run autonomous tasks on a user’s device—sparked a torrent of real-world experimentation and rapid adoption. Its core innovation is simple and powerful: instead of being a single chat model, OpenClaw orchestrates multiple models and tools (often combining cloud-hosted frontier models and local models) and gives those agents permission to take actions on the host machine and across the web. That autonomy is what made OpenClaw so compelling: scheduling, email triage, file management, browsing, and multi-step automation could all happen without a human in the loop.But that same autonomy exposed a new attack surface. Security researchers, vendors, and some national governments raised alarms about unguarded tool access, malicious “skills,” credential aggregation, and the potential for rapid, automated data exfiltration or destructive commands. In response to that security scramble, Nvidia announced NemoClaw at GTC as a layered approach—an infrastructure and runtime stack designed to make agentic AI safer for enterprises, while preserving local capabilities and the flexibility that made OpenClaw popular.
This article explains what NemoClaw claims to do, how its pieces fit together, the trade-offs and blind spots security teams should watch for, and what NemoClaw’s debut means for the larger ecosystem of open models and agentic AI.
Overview: What Nvidia is trying to solve
OpenClaw’s rapid rise revealed a hard truth: agents that can act autonomously and connect to tools are inherently useful, but their usefulness scales the impact of any misconfiguration or compromise. Key enterprise concerns included:- Unauthorized lateral access when agents obtain OAuth tokens, API keys, or SaaS permissions.
- Execution of local commands or scripts by unaudited third-party “skills.”
- Data leakage from long-running agents that aggregate sensitive materials.
- Difficulty applying standard endpoint controls because agent behavior spans local, cloud, and third-party models.
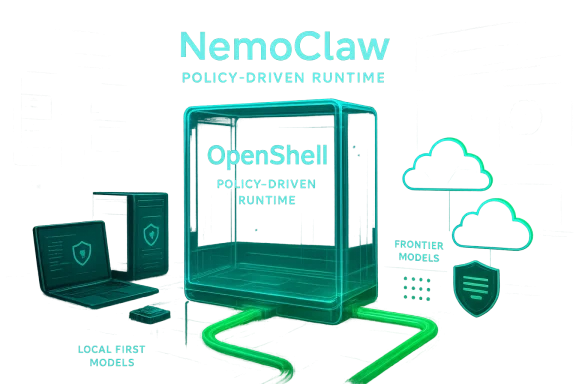
Nvidia frames NemoClaw as an integration of several components:
- NeMo Agent Toolkit — an open-source library to manage teams of agents.
- OpenShell — a runtime that enforces policies, sandboxes models, and integrates with security tools.
- Privacy Router — a mediation layer that blends local and cloud models while preserving policy.
- Nemotron Coalition / Nemotron models — a parallel initiative to advance open frontier models that agents can use.
How NemoClaw works — component deep-dive
NeMo Agent Toolkit: the orchestration layer
Nvidia’s NeMo Agent Toolkit is the glue that organizes agents and their capabilities. It provides:- APIs to connect agents to data sources and tools.
- Conventions for agent teams and task delegation.
- Utilities to orchestrate long-running jobs and handle retries and state.
OpenShell: the runtime sandbox and policy engine
At the heart of NemoClaw’s security claims is OpenShell, a new open-source runtime that Nvidia says sandboxes models, enforces policy, and integrates with cybersecurity tooling. OpenShell provides these capabilities:- Policy enforcement: Organizations can define rules that limit which agents can access which files, network endpoints, or tools. Policies can be scoped to user, agent, time, and data sensitivity.
- Sandboxing and isolation: Models and “skills” run in constrained environments that limit system call surface and executable permissions.
- Telemetry and audit: OpenShell records agent actions for audit and forensic review, creating tamper-evident logs that security teams can inspect.
- Integration with security vendors: Nvidia designed OpenShell to work alongside endpoint protection, detection, and response tools; the company highlighted collaborations with established security vendors to ensure compatibility.
Privacy Router: bridging local and cloud models safely
A major operational benefit of OpenClaw-style agents is hybrid capability: local models for speed and privacy, and cloud models for cutting-edge capability. NemoClaw’s Privacy Router mediates that relationship by:- Routing requests to cloud models only when policies permit.
- Tokenizing or redacting secrets before they leave the host.
- Offering configurable “teaching loops” where cloud model outputs are used to refine local behavior—while preserving guardrails.
What Nvidia claims NemoClaw will deliver for enterprises
Nvidia’s pitch is straightforward: NemoClaw turns agentic AI from a risky experiment into an enterprise-grade platform. Promised benefits include:- Policy-first security — Administrators can codify allowed actions and network flows.
- Reduced insider risk — Agents run in constrained sandboxes, lowering the chance of accidental data exposure.
- Hybrid model workflows — Organizations can leverage local models and cloud frontier models without losing visibility or control.
- Scalability — A managed runtime that encourages 24/7 agent operations with predictable telemetry and resource controls.
- Vendor compatibility — Designed to plug into existing enterprise security stacks (endpoint detection, SIEMs, CASBs).
The Nemotron Coalition: why Nvidia is doubling down on open models
NemoClaw did not arrive alone. Nvidia also launched a coalition of labs and companies to cultivate open-source frontier models—part of a strategic push to make high-quality, adaptable models broadly available. The coalition includes several model developers and labs that will jointly train an open model on Nvidia infrastructure and use that as a foundation for future Nemotron releases.For enterprises that need auditable, adaptable models—and for developers who want to fine-tune base models for specialized tasks—an open coalition makes sense. Open foundations reduce lock-in and let organizations build domain-specific capabilities on top of a commonly audited base.
That said, open models and agent runtimes together can increase diffusion of capabilities. NemoClaw attempts to offset that risk by coupling an open model strategy with hardened runtime controls (OpenShell). The net result is a bet that open weights plus strong runtime policy = broad innovation without wholesale operational risk.
Strengths: what NemoClaw gets right
- Practical threat modeling. Nvidia recognizes the core enterprise concerns—credential aggregation, lateral movement, and untrusted skills—and surfaces specific mitigations (sandboxing, policy enforcement, telemetry). This realistic threat model is a needed first step for agent adoption.
- Integration-first design. By building OpenShell to interoperate with existing security vendors and enterprise controls, Nvidia lowers the friction for security teams that already rely on tools from established vendors.
- Hybrid model support. Agents benefit from both local and cloud models. The privacy router concept addresses a real engineering challenge: how to use cloud reasoning without leaking secrets.
- Open-source components. Making the NeMo Agent Toolkit and OpenShell open-source invites external auditing, contribution, and faster iteration—critical for a technology that will be scrutinized by security researchers.
- Ecosystem leverage. Nvidia controls a dominant share of the GPU infrastructure on which many models train and run. By providing a software layer that encourages more agent workloads, Nvidia can drive the economics for GPU-backed agentic workloads and simplify deployment for enterprises.
Risks and blind spots: where NemoClaw may fall short
No runtime can make an insecure policy secure; it only gives defenders better tools. NemoClaw reduces but does not eliminate the fundamental risks of agentic AI. Key concerns:- Policy misconfigurations remain a risk. Enterprises are already familiar with catastrophic failures due to overly permissive policies. If OpenShell policies are misconfigured, agents could still obtain broad access that leads to data loss.
- Supply-chain issues for skills. The ecosystem around agent “skills” (third-party plugins) will grow fast. OpenShell can sandbox execution, but malicious or trojanized skills could still exploit vulnerabilities in the runtime or in other system components to escalate privileges.
- Telemetry and privacy trade-offs. Audit logs and telemetry are essential for incident response—but collecting more telemetry increases exposure. Organizations must balance forensic visibility with the risk that logs themselves could contain sensitive content.
- Endpoint heterogeneity. Enterprises run Windows, macOS, and Linux endpoints. A robust runtime needs consistent behavior across all of them, and platform-specific bugs could create gaps attackers exploit.
- Human factors. Agents will increasingly automate repetitive tasks. The organizational practice of blindly trusting automation—for example, allowing agents to execute destructive commands—remains a human governance problem. Runtime controls help, but governance and training are still required.
- Dependency on cloud providers for updates and rollback. If enterprise deployments rely on cloud-hosted components (for model updates, patches, or telemetry aggregation), attacker control of those channels is another vector. The “privacy router” helps, but reliance on cloud services carries operational dependencies.
- Attacker innovation. The agent landscape changes attacker economics: once an agent can aggregate tokens and make authenticated API calls on behalf of a user, attackers may target the agent layer proactively. Security tooling will need to evolve to detect agent-specific indicators of compromise.
Open questions and unverifiable claims
NemoClaw’s initial messaging includes a number of product claims that are sensible but require validation in deployment:- Nvidia states NemoClaw can be installed “in a single command” and “runs on any platform.” That claim is plausible for a preview distribution but will need verification across complex enterprise environments where package managers, administrative policies, and endpoint protection may block single-command installs.
- The exact mechanism of OpenShell’s tamper-evident logs and the cryptographic guarantees around audit integrity have not been exhaustively documented in public materials; teams should verify those properties before treating them as authoritative.
- The cadence, governance, and data-sharing rules of the Nemotron Coalition are not fully spelled out. Organizations should be cautious about trusting coalition-built models for sensitive workloads until model provenance, dataset curation, and licensing are clear.
What security teams should do now
If you run a security or DevOps team and the prospect of enterprise agents is on your roadmap, here are concrete next steps:- Inventory and risk-assess:
- Identify which teams and users are experimenting with agent frameworks (OpenClaw, local agents, automation scripts).
- Map where those agents can reach: SaaS, internal APIs, cloud consoles, and privileged systems.
- Pilot with strict policies:
- Run NemoClaw/OpenShell in a controlled lab with aggressive deny-by-default policies.
- Test real-world use cases and deliberately attempt to escalate privileges or exfiltrate data to validate mitigations.
- Harden skill publishing:
- Treat agent skills like software packages—require signing, provenance metadata, and code reviews.
- Use allowlists and runtime policies that restrict which skills can be installed and executed.
- Integrate telemetry and detective controls:
- Ensure OpenShell audit logs feed into your SIEM and EDR workflows.
- Create specific alerts for agent patterns: rapid token access, unusual outbound connections, tool-chain invocation sequences.
- Update identity and access controls:
- Apply least privilege to machine identities agents use.
- Use short-lived tokens and consented token exchange where possible, and enforce strong multi-factor authentication for any user-facing agent operations.
- Prepare incident playbooks:
- Define how you will triage an agent compromise. Steps should include sandbox isolation, token revocation, forensic preservation, and rollback of agent skills.
- Educate users:
- Train staff on the distinction between helpful automation and policy-protected operations. Make policies visible and explain why certain agent actions require approval.
Developer and IT operations guidance
For teams building with NemoClaw or integrating agents into workflows:- Use the NeMo Agent Toolkit to formalize agent roles and responsibilities. Treat agents as first-class services with versioning and deployment pipelines.
- Prefer immutable, auditable skill artifacts (containers, signed binaries) over ad-hoc scripts.
- Ensure local models that access private data run in partitions with limited network privileges unless the privacy router explicitly allows outbound flows.
- Windows user account control and local privilege elevation paths remain a primary risk; agents should never run with persistent elevated privileges.
- Endpoint protection products should be configured to recognize and allow approved OpenShell processes while still enforcing behavior-based detection for unexpected activity.
- Group Policy and Windows Defender Application Control (or equivalent) can be used to lock down permitted skill execution contexts.
The broader market: why this matters
NemoClaw is not just a product—it's a signal. Nvidia is leveraging its massive position in compute infrastructure to standardize how the next generation of software (agentic, always-on automation) will be deployed. By coupling an open model coalition with an enterprise runtime, Nvidia attempts to:- Reduce enterprise friction to adopt agentic automation.
- Make hybrid local/cloud agent workflows predictable and auditable.
- Ensure a ready market for compute and model training on Nvidia infrastructure.
But success depends on adoption and, critically, on community scrutiny. The open-source model for the runtime and toolkit helps: independent researchers can probe OpenShell and the NeMo Agent Toolkit for gaps. The industry needs timely disclosures, bug bounties, and a transparent governance model for the coalition models to build real trust.
Practical guide: how to evaluate NemoClaw in a pilot
Use this checklist for an evaluation pilot:- Define a narrow business use case (e.g., calendar automation for a single team).
- Deploy NemoClaw/OpenShell in a contained VLAN with net egress controlled.
- Create a minimal skill set with signed artifacts and restrict capabilities via policy.
- Simulate real user tasks and inject malicious inputs (prompt injection, malicious file access) to observe behavior.
- Validate audit logs and test integrity guarantees by attempting to tamper with logs.
- Test recovery: if an agent is compromised, can you kill it, revoke tokens, and restore service quickly?
- Run red-team scenarios that mimic lateral movement and token theft.
- Iterate policy and controls until the risk profile matches organizational tolerance.
Final assessment: cautious optimism
NemoClaw is an important step toward practical, secure agentic AI. Nvidia has targeted the right problem set: agents need a runtime that enforces policies and provides enterprise observability. OpenShell and the NeMo Agent Toolkit, paired with a privacy router and an open-model coalition, create a coherent stack that many organizations will find alluring.Yet implementation details and operational realities will determine whether NemoClaw is an incremental improvement or a genuinely transformative platform for secure agent deployment. The hard work remains in the trenches—policy design, secure skill management, telemetry hygiene, and human governance.
For IT leaders and security teams, the right posture is measured curiosity: pilot NemoClaw where the business benefit is clear, run aggressive adversarial tests, and insist on transparency about policy semantics, audit guarantees, and coalition model provenance before entrusting agents with high-value work. Agentic AI can be a force multiplier—when it is respectfully constrained and vigilantly managed.
Source: ZDNET Nvidia bets on OpenClaw, but adds a security layer - how NemoClaw works