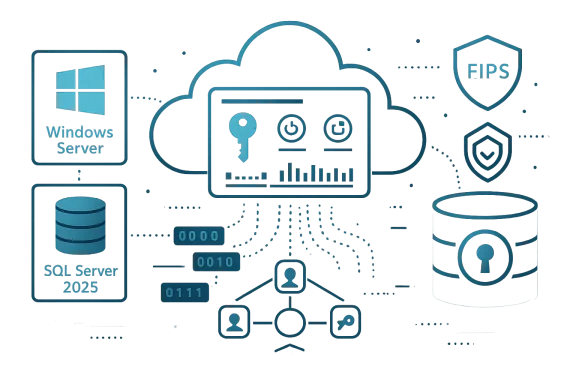
NetLib Security’s Winter 2026 release pushes transparent data-at-rest encryption into a more cloud-native, key‑centric era — adding first‑class support for Microsoft’s newest server stack, a new Azure Key Vault key-delivery plugin, and a significantly expanded Encryptionizer Key Manager (EKM) designed to centralize policy and lifecycle controls for keys across hybrid estates.
NetLib Security’s Encryptionizer has long billed itself as a transparent data encryption platform that protects databases and application files without requiring application code changes. That positioning matters for enterprises still running heterogeneous environments and long‑lived legacy applications. The vendor’s Winter 2026 announcement reaffirms that strategy while pivoting toward centralized key management and cloud integration as the primary control plane for modern deployments.
At a high level, the Winter 2026 package includes:
Why this matters: early support reduces migration friction for teams adopting SQL Server 2025 and Windows Server 2025. Enterprises that must modernize to gain new feature and performance benefits can still maintain consistent encryption controls across old and new platforms.
Benefits:
Benefits:
In short:
That architectural shift is the right move for organizations wrestling with hybrid estates, regulatory pressure, and the accelerating threat landscape driven by AI automation. But centralization brings concentrated risk. Successful adoption will depend on rigorous testing, clear key governance, and careful attention to high‑availability and recovery patterns. Organizations evaluating Winter 2026 should treat NetLib’s enhancements as a platform-level capability: powerful when combined with mature operational practices, and potentially risky if treated as a turnkey silver bullet.
In short: Winter 2026 gives Windows and SQL Server administrators new tools to make stolen data useless — but only if those organizations pair the technology with tested key governance, resilient architecture, and a skeptical eye toward unverifiable marketing claims.
Source: The National Law Review NetLib Security Announces Winter 2026 Release with AI-Driven Enhancements and Major Upgrades to Encryptionizer Key Manager for Data Security That Moves at the Speed of Reality
 Background
Background
NetLib Security’s Encryptionizer has long billed itself as a transparent data encryption platform that protects databases and application files without requiring application code changes. That positioning matters for enterprises still running heterogeneous environments and long‑lived legacy applications. The vendor’s Winter 2026 announcement reaffirms that strategy while pivoting toward centralized key management and cloud integration as the primary control plane for modern deployments.At a high level, the Winter 2026 package includes:
- Native support for Microsoft SQL Server 2025 and Microsoft Windows Server 2025, aimed at organizations adopting the latest Microsoft server releases.
- Continued compatibility with older Windows releases (NetLib’s materials list support back to Windows 7 and earlier server SKUs), preserving protection for legacy installations.
- A Key Delivery Plugin that enables Encryptionizer to use Azure Key Vault as an external key store.
- Upgrades to Encryptionizer Key Manager (EKM) for centralized key lifecycle, policy enforcement, and distributed administration.
What’s actually new in Winter 2026
Platform support: SQL Server 2025 and Windows Server 2025
NetLib states that Encryptionizer now supports Microsoft’s server releases through the 2025 wave, allowing organizations to deploy transparent encryption on the newest SQL Server and Windows Server builds without reworking application layers. This aligns with Microsoft’s ongoing release cadence and the security investments in SQL Server 2025 (for example, OAEP‑256 and TDS/TLS improvements on the database side). NetLib’s announcement emphasizes parity with modern Microsoft features while preserving support for legacy workloads.Why this matters: early support reduces migration friction for teams adopting SQL Server 2025 and Windows Server 2025. Enterprises that must modernize to gain new feature and performance benefits can still maintain consistent encryption controls across old and new platforms.
Azure Key Vault Key Delivery Plugin
The Winter 2026 release adds a Key Delivery Plugin capable of using Azure Key Vault as a backing store for Encryptionizer keys. In practical terms, this lets organizations:- Store encryption keys in an Azure-backed HSM or managed vault.
- Leverage Azure’s identity and RBAC models for key access.
- Create auditable key usage trails and align with cloud‑centric compliance models.
Encryptionizer Key Manager (EKM)
EKM is presented as the management tier that centralizes:- Key lifecycle operations (creation, rotation, revocation).
- Enterprise-wide encryption policy enforcement.
- Centralized administration for geographically distributed systems.
Technical implications and engineering analysis
Transparent encryption vs. native DB encryption (practical differences)
Encryptionizer uses a transparent interception approach between the database engine and the file system (NetLib’s documented architecture), which differs from native SQL Server Transparent Data Encryption (TDE) and column‑level encryption approaches. The practical implications are:- Deployment without code change: Encryptionizer operates largely without schema or application modification, which is advantageous for legacy apps or embedded databases.
- Control over keys: When combined with EKM and Azure Key Vault, Encryptionizer shifts key custody to centralized services, enabling enforced rotation policies and centralized audit.
- Performance tradeoffs: Transparent interception layers typically add some overhead. Historically, vendors in this space report modest performance costs for encryption‑at‑rest approaches; NetLib’s own FAQs discuss small overheads in certain scenarios. Administrators should performance‑test workloads (especially high‑throughput OLTP systems) under real conditions.
Azure Key Vault integration: advantages and operational realities
Integrating Azure Key Vault as the key store provides clear benefits, but introduces operational considerations:Benefits:
- Hardware‑backed keys (Managed HSM) or Microsoft‑backed cryptographic protection.
- Centralized access control via Azure AD and RBAC.
- Native logging and integration with cloud SIEM, supporting compliance workloads.
- Latency and availability: depending on topology (on‑prem SQL Server communicating with Key Vault in Azure), key fetch latency and transient connectivity must be handled robustly. Architectures that use local key caches, offline wrap/unwrap, or proxy HSMs can mitigate but must be validated.
- Authentication model: Encryptionizer will need service identity integration with Azure AD. Teams must plan controlled service principals or managed identities and defend their credentials/workflows.
- Key sovereignty and compliance: storing keys in Azure Key Vault can satisfy many compliance mandates but may conflict with strict data localization or sovereign cloud requirements.
- Backup and disaster recovery: Key backup and export policies must be agreed; organizations must understand Key Vault export constraints (e.g., non‑exportable keys in Managed HSM).
Centralized EKM and policy enforcement: benefits and risks
Centralized key management simplifies administration and reduces human error, but concentrates risk.Benefits:
- Uniform policy application across databases and file systems.
- Easier compliance reporting and key lifecycle automation.
- Reduced key sprawl and fewer silos of unmanaged key material.
- Single target for attackers: a centralized key manager becomes a high‑value target. Harden EKM servers, use network segmentation, multi‑factor admin access, and proximity HSMs where possible.
- Operational single point of failure: design EKM for high availability and test failover. Use secondary key recovery paths where regulatory rules permit.
- Change control complexity: broad policy changes can have widespread effects. Implement staged rollouts, preflight testing, and access controls for policy changes.
Compliance, validation, and cryptographic assurances
NetLib highlights that Encryptionizer has received FIPS validations and is represented in NIST cryptographic module documentation. That validation is a meaningful indicator for regulated environments that require FIPS‑validated cryptographic modules. However, the vendor’s statement that the product uses “the strongest available ciphers” is a marketing claim that requires technical verification — organizations should review module security policies and CMVP/FIPS certificates to confirm algorithm suites and allowable modes for their risk posture.In short:
- FIPS/CMVP entries are verifiable and represent an independent validation point. Use those documents to confirm supported algorithms and security levels.
- Vendor marketing statements about unspecified “strongest” ciphers should be treated as claims until cross‑checked with the module’s security policy and certification artifacts. NetLib publishes NIST‑facing security policy documents for Encryptionizer that should be reviewed during procurement.
Real‑world deployment guidance for Windows administrators
If you’re responsible for Windows servers, SQL estates, or mixed hybrid infrastructure, here’s a practical playbook for evaluating and deploying Encryptionizer Winter 2026 and EKM.- Inventory and risk classification
- Map databases (SQL Server versions, Express/LocalDB, PostgreSQL, MySQL, embedded DBs) and file containers that hold regulated or sensitive data.
- Prioritize systems that cannot be refactored quickly (legacy apps, appliances, medical devices).
- Proof of concept (PoC)
- Stand up a PoC environment that mirrors production topology (include on‑prem to Azure network links).
- Validate encryption/decryption behavior for common operations: backups/restores, index maintenance, DB mirroring/replication, and vendor apps.
- Measure latency and throughput under realistic load. NetLib documentation counsels preflight testing for patch and update scenarios.
- Key management design
- Decide whether keys will be stored on EKM, Azure Key Vault, or a hybrid model.
- Define rotation, backup, and emergency recovery SOPs.
- For Azure Key Vault: choose Managed HSM vs Key Vault based on exportability and compliance constraints, and validate authentication flows (managed identity/service principal).
- High availability and disaster recovery
- Plan EKM for HA across data centers or availability zones.
- Test key recovery from catastrophic failure, including third‑party escrow if required by law or policy.
- Access controls and telemetry
- Apply least privilege policies for key access.
- Integrate key usage logs with SIEM and incident response playbooks.
- Regulatory evidence collection
- Capture FIPS/CMVP certificate snapshots, module security policies, and internal control evidence to satisfy auditors.
- Document architecture diagrams showing where keys are stored and how access is mediated.
Potential pitfalls and red flags
- Vendor claims vs. verifiable capability: marketing statements about being “patented” or using the “strongest ciphers” should be corroborated with patent records and module security policies/certificates. NetLib’s site references a patented platform and FIPS validations; procurement teams should request the exact certification documentation and patent identifiers for legal review.
- Latency during key fetch: on‑prem agents talking to cloud key vaults can encounter transient issues. Ensure your architecture provides a resilient key cache or local HSM proxy where business continuity demands it.
- Feature coverage gaps for non‑Windows systems: while Encryptionizer advertises support for PostgreSQL, MySQL, MongoDB, and more, verify platform‑specific limitations and test backups, restore workflows, and replication scenarios. Transparent encryption approaches can interact with DB internals differently than native DB encryption mechanisms.
- Licensing and TCO tradeoffs: NetLib markets EKM as cost‑effective, but centralization invariably has recurring operational costs. Account for HA, management, and potential cloud key management fees in total cost calculations.
How Winter 2026 fits broader security trends
Three trends make NetLib’s Winter 2026 moves strategically sensible:- AI‑amplified attacks: automated phishing, faster account compromise, and more efficient lateral movement increase the need for data protection that doesn’t depend on detecting adversary behavior. Cryptography reduces the attacker’s payoff by making exfiltrated data unusable without keys. NetLib frames the release explicitly around that threat model.
- Cloud as control plane: enterprises increasingly use cloud key stores (Azure Key Vault, AWS KMS, Google KMS) as the canonical key store. Encryptionizer’s plugin architecture and EKM’s centralization align with that pattern.
- Heterogeneous estates: many organizations must protect a mix of modern and legacy systems. Transparent encryption that doesn’t force application rewrites reduces friction for those migrations. NetLib’s continued support of legacy Windows versions is positioned for this reality.
Recommendations for IT decision makers
- Treat Winter 2026 as a capability expansion, not a drop‑in cure. Centralized key control solves many problems but introduces new operational demands. Build operational runbooks and test them frequently.
- Verify cryptographic details: request NetLib’s module security policy, FIPS/CMVP certificate numbers, and the list of supported ciphers/modes for the specific Encryptionizer build you intend to deploy. Use those documents in procurement risk assessments.
- Validate Azure Key Vault flows in a staging environment representing real network conditions. Measure latency, retry behavior, and how the product responds to intermittent Key Vault unavailability.
- Plan for DR of keys: ensure you have documented and tested recovery paths that meet your compliance obligations, including offline recovery options where necessary.
- If you run embedded or regulated devices (medical, industrial), confirm firmware and vendor compatibility. Legacy devices often present non‑obvious integration constraints.
Conclusion
NetLib Security’s Winter 2026 release is a meaningful evolution for a vendor that has long focused on transparent encryption for Windows and database stacks. By adding first‑class support for SQL Server 2025 and Windows Server 2025, integrating Azure Key Vault as a key‑delivery option, and expanding the Encryptionizer Key Manager, NetLib is aligning its product strategy with a world where keys — not just algorithms — are the central control point for data security.That architectural shift is the right move for organizations wrestling with hybrid estates, regulatory pressure, and the accelerating threat landscape driven by AI automation. But centralization brings concentrated risk. Successful adoption will depend on rigorous testing, clear key governance, and careful attention to high‑availability and recovery patterns. Organizations evaluating Winter 2026 should treat NetLib’s enhancements as a platform-level capability: powerful when combined with mature operational practices, and potentially risky if treated as a turnkey silver bullet.
In short: Winter 2026 gives Windows and SQL Server administrators new tools to make stolen data useless — but only if those organizations pair the technology with tested key governance, resilient architecture, and a skeptical eye toward unverifiable marketing claims.
Source: The National Law Review NetLib Security Announces Winter 2026 Release with AI-Driven Enhancements and Major Upgrades to Encryptionizer Key Manager for Data Security That Moves at the Speed of Reality