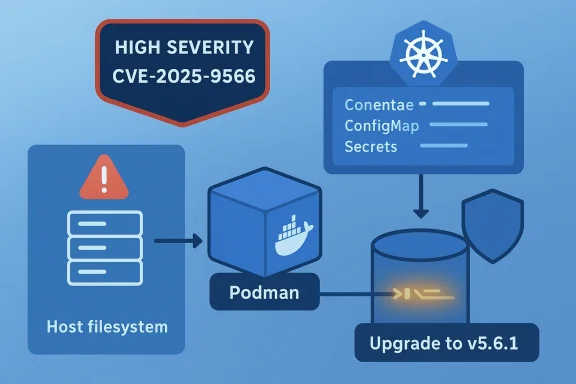
Podman’s kube play command contains a symlink traversal flaw that can let a malicious or compromised container cause Podman to overwrite arbitrary files on the host filesystem — a high‑severity integrity and availability risk that was fixed in Podman v5.6.1 but remains a critical operational concern for teams that run kube YAML with ConfigMap or Secret volumes.
In September 2025 a path‑traversal / symlink traversal vulnerability was disclosed in Podman’s implementation of the kube play functionality. The bug allows an attacker — under a set of specific but practical conditions — to create a symbolic link inside a ConfigMap or Secret volume that points at an arbitrary host file path. On subsequent executions of podman kube play on the same volume, Podman follows that symlink and writes the ConfigMap/Secret content to the target host path, effectively overwriting the host file. The attacker does not control the bytes written (those are taken from the YAML-defined ConfigMap/Secret), but they do control the destination path that gets overwritten.
Key technical facts that every administrator should know:
Look for:
Two developer and process lessons:
Prioritized action plan for administrators:
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
In September 2025 a path‑traversal / symlink traversal vulnerability was disclosed in Podman’s implementation of the kube play functionality. The bug allows an attacker — under a set of specific but practical conditions — to create a symbolic link inside a ConfigMap or Secret volume that points at an arbitrary host file path. On subsequent executions of podman kube play on the same volume, Podman follows that symlink and writes the ConfigMap/Secret content to the target host path, effectively overwriting the host file. The attacker does not control the bytes written (those are taken from the YAML-defined ConfigMap/Secret), but they do control the destination path that gets overwritten.Key technical facts that every administrator should know:
- Affected upstream range: Podman introduced the vulnerable behavior in the v4.x family and it persists through v5.6.0. The issue was fixed in v5.6.1.
- Exploitation prerequisites: use of podman kube play with a ConfigMap or Secret volume mount, a writable volume that ends up containing a malicious symlink (created during an earlier run), and running podman kube play more than once against the same volume.
- Impact: the attacker controls which host file is overwritten; they cannot directly control the content written, but overwriting critical system or application files can cause loss of availability and serious integrity problems.
- CVSS/Severity: the vulnerability has been assessed as high severity (CVSS in published advisories sits at an 8.1 / high level), reflecting network/local access dynamics and a capability to cause integrity and availability damage.
How the bug works — technical explanation
What podman kube play does in normal operation
podman kube play is a convenience command that reads Kubernetes YAML (Pods, Deployments, ConfigMaps, Secrets, volume definitions, etc.) and runs equivalent Podman containers and mounts locally. ConfigMaps and Secrets in Kubernetes are often materialized as files inside mounted volumes so that containers can read configuration files and keys at runtime.Where the symlink traversal arises
When podman kube play processes a ConfigMap or Secret volume, it expects to write the resources into a directory that will be mounted into the resulting container. The vulnerable behavior occurs when:- The target volume directory already contains a symbolic link (symlink) whose path resolves to a file on the host filesystem (for example, a symlink created inside the volume that points to /etc/hosts, /etc/resolv.conf, /var/lib/some-service/config, etc.).
- podman kube play is run again against the same YAML and volume. Instead of reliably canonicalizing and enforcing that writes stay inside the intended directory, the code follows the symlink and writes the ConfigMap/Secret file to the symlink target on the host.
Why this matters (privileges and access model)
Exploiting this bug requires two capabilities:- The ability to cause a symlink to be created inside an accessible volume (for example, by running a container or process that writes to the volume).
- The ability to run podman kube play (or otherwise cause an operator/CI job to re‑run the same kube YAML against that volume).
Realistic attack scenarios and scope
Understanding how this vulnerability would be used in the wild helps operators prioritize response and mitigation.Scenario 1 — compromised CI runner or developer laptop
- A CI job or developer runs a build/test container that writes artifacts into an attached volume.
- That job (or a prior job) creates a symlink within the mounted directory that points to an important host path (for example, /etc/hosts or a service configuration file).
- Later, another job or an operator runs podman kube play to materialize a ConfigMap into the same volume. Podman follows the symlink and overwrites the host path with ConfigMap contents — which may be benign data but can break services or DNS resolution on the host.
Scenario 2 — multi‑tenant container host
- Multiple users share a single host where Podman is available to non-privileged users.
- User A creates a container that writes a malicious symlink in a shared volume.
- User B or an automated process runs podman kube play using shared YAML with ConfigMap/Secret mounts, causing the symlink to be followed and a host file overwritten.
Scenario 3 — operator error combined with crafted input
- An operator uses podman kube play to apply YAML created from third-party input (for example, marketplace content or vendor-provided config) onto a host that contains reused volumes.
- The vendor YAML includes ConfigMaps/Secrets; an attacker who previously placed symlinks in those volumes can redirect writes to host files.
Impact analysis — why this is serious
This bug is more than a theoretical path traversal; it implicates three high‑value security properties:- Integrity: An attacker can force Podman to replace host files with content supplied inside YAML or created by benign workflows. Overwriting configuration, key files, or scripts can corrupt system behavior and open follow‑on opportunities for service compromise.
- Availability: Critical system files can be made unusable by being replaced with unexpected content. Services may fail to start; network configuration could be damaged; DNS or routing could be broken. The user-supplied description of the flaw explicitly notes potential total loss of availability scenarios while attacks run or persistence of damage afterward.
- Operational risk in multi‑tenant systems: Where Podman is available to multiple users or automation pipelines, privilege separation is often incomplete — this amplifies the exploitability. CI pipelines, PaaS offerings, and developer workstations are practical places where this attack could be staged.
- Replacing a systemd unit or configuration file with a deliberately malformed ConfigMap file can prevent a service from starting, causing downtime.
- Overwriting network or resolver configuration can break outbound connectivity, preventing updates and incident response.
- Replacing startup scripts or cron jobs with different but valid content may produce persistent misbehavior.
Detection: signs an exploitation attempt occurred
If you suspect exploitation or want to hunt proactively, focus on the intersection of podman kube play activity and unexpected host file changes.Look for:
- Unexpected invocations of podman kube play in logs, especially against namespaces/volumes that are shared or reused.
- Timestamp changes (mtime/ctime) on host files that are normally managed by package managers or system services.
- Newly created symlinks inside container volumes or directories used by kube play. A quick check:
- find /path/to/volume -type l -ls
- File integrity alerts: checksums or host integrity tools (AIDE, Tripwire) flagging changed system files.
- CI logs that show containers writing into volumes followed later by podman kube play or similar materialization steps.
- Attempts to create symlinks that resolve to paths outside expected directories (../ or absolute paths inside the same volume).
- Identify all recent uses of podman kube play and record the YAML and volumes used.
- Compare the set of files written by those ConfigMaps/Secrets with the set of host files that changed around the same timestamps.
- Inspect volumes for symlinks and examine symlink targets.
- If host files were overwritten, consult backups to restore integrity and collect forensic evidence (timestamps, process lists, container IDs).
Remediation — immediate and medium-term steps
If you manage Podman hosts, follow a staged approach: patch, contain, audit, and harden.1) Immediate (apply as soon as possible)
- Upgrade Podman to v5.6.1 or later. The upstream fix addresses the symlink traversal. Upgrade through your distribution package manager or Podman upstream packages as your operational model permits.
- If you cannot upgrade immediately, avoid using podman kube play with ConfigMap or Secret volume mounts until patched. This is the most reliable short-term mitigation.
2) Short-term mitigations if patching is delayed
- Do not reuse the same persistent volume for successive runs of podman kube play where the content might be untrusted or writable by other users. Consider creating fresh empty directories for each kube play run and removing them after use.
- Disallow or audit symlinks in any directory used as a ConfigMap/Secret volume source. For example:
- find /var/lib/containers/volumes -type l -exec ls -la {} \;
- Restrict who can run podman kube play on shared systems. If Podman is installed system-wide, enforce RBAC/ACLs that limit podman commands to trusted administrators.
- Run podman as unprivileged user namespaces where appropriate; isolate CI and developer runners in dedicated VMs or containers so that a symlink inside a build artifact cannot point to host-critical paths.
3) Medium-term steps (post‑patch)
- After upgrading, perform a host audit to ensure no critical host files were overwritten:
- Restore any corrupted files from backups or package-managed originals.
- Reinstall packages whose configuration files were modified.
- Rotate secrets, keys, and credentials that might have been exposed or affected during the event.
- Harden CI/CD pipelines: avoid sharing writable host volumes across jobs; use ephemeral volumes.
- Add pre‑flight checks to deployment tooling that examine ConfigMap/Secret volumes for symlinks before invoking kube play.
4) Long-term hardening
- Harden host file integrity monitoring and file change alerting to detect unexpected writes from container runtimes.
- Reduce attack surface: run podman only where necessary and remove access from untrusted users.
- Use sandboxed, ephemeral build agents (VMs or ephemeral containers) for untrusted workloads, preventing attackers from placing symlinks on persistent host volumes.
- Incorporate secure YAML validation into your pipeline: flag or reject ConfigMaps/Secrets that will be materialized against reused volumes without prior cleaning.
Incident response playbook (concise checklist)
- If Podman v5.6.1+ is not installed, assume potential exposure for past podman kube play runs involving ConfigMap/Secret volumes.
- Immediately stop workflows that call podman kube play against reused volumes.
- Identify runs: list recent podman kube play commands and correlate to host file modification times.
- Scan relevant volumes for symlinks:
- find /path/to/volume -type l -ls
- Inspect host files with changed mtimes and restore from backups or package-reinstall originals.
- Rotate secrets and credentials that may have been influenced by the event.
- Upgrade Podman to v5.6.1 or newer and re-run hygiene checks.
- Publish an internal post‑mortem and apply the hardening steps described above.
Why the vulnerability slipped in — lessons for container tool developers
This class of flaw is conceptually simple: failing to canonicalize or restrict file operations when copying or materializing user-supplied files allows symlink traversal. It reflects a perennial tradeoff in container tooling between convenient convenience features (materializing ConfigMaps/Secrets locally) and strict file-system isolation.Two developer and process lessons:
- Materialize user data into host directories only after explicit canonicalization and checks that deny writes outside the intended directory tree. This should include checks to detect and refuse to follow symlinks that resolve outside the destination namespace.
- Where materialization is necessary, prefer atomic operations that create temporary directories with known permissions and then move them into place using safe rename semantics that do not follow symlinks, or use copy-on-write approaches that do not follow symlinks by default.
- Automated tests for symlink traversal scenarios should be part of core regression suites for any tooling that copies user or external data into host paths.
Operational policy recommendations
To reduce the class of risk represented by CVE-2025-9566 and similar symlink traversal issues, organizations should adopt policy and tooling changes:- Enforce ephemeral volumes in CI: jobs should be isolated with per-job ephemeral directories that are deleted after job completion.
- Implement least privilege: limit who can execute podman kube play and who can write to shared volume directories.
- Add pre-deployment scanning: scan Kube YAML and volume directories for symlinks and reject deployments that rely on reused writable volumes.
- Integrate container runtime patching into standard maintenance windows and emergency patching processes. Runtime updates should not be treated as optional; they directly affect host integrity.
- Train operators to treat ConfigMap/Secret materialization as a privileged operation and to perform hygiene checks before materializing vendor-supplied YAML.
Practical command examples (safe checks and quick triage)
Use these checks to rapidly triage an environment for risky symlinks and Podman versions:- Check Podman version:
- podman --version
- Confirm reported version is v5.6.1 or later; if not, schedule an immediate upgrade.
- Find symlinks in a volume directory:
- find /path/to/volume -type l -ls
- Find host files that were modified recently (example: last 24 hours):
- find /etc -mtime -1 -ls
- Check for recent podman kube play commands in shell history or audit logs:
- grep -R "podman kube play" /var/log /home/*/.bash_history
Broader implications: containers, supply chain, and shared infrastructure
CVE-2025-9566 is symptomatic of a larger set of risks introduced as container tooling grows richer and operators increasingly “materialize” user content on hosts for convenience. The following are strategic implications:- Tooling that blurs host/container boundaries (materializing volumes, managing host resources on behalf of users) strengthens the need for formal access control and audit trails.
- Multi‑tenant systems and shared build infrastructure amplify symlink traversal risks because an attacker can use seemingly benign actions (writing a symlink into a volume) to subvert later privileged workflows.
- Supply chain defenses must include checks for weird filesystem artifacts (symlinks, device nodes) inside artifacts and directories before those artifacts are used in privileged operations.
- Runtime patching and fast distribution of fixes through OS vendors and package managers is critical; organizations should track advisories and have automation to push high‑severity updates quickly.
Final assessment and recommended priorities
CVE-2025-9566 is a high‑severity vulnerability with real operational consequences: it enables host file overwrites that can cause integrity loss and persistent or sustained availability failures. While exploitation requires some prerequisites, those prerequisites are realistically present in many modern development and CI/CD environments.Prioritized action plan for administrators:
- Immediately confirm Podman versions across hosts and upgrade any hosts running versions earlier than v5.6.1.
- Until patched, do not use podman kube play with ConfigMap or Secret volume mounts — treat kube play as an administrative, privileged operation.
- Audit shared volumes, CI runners, and developer workstations for symlinks that could be abused.
- Harden pipelines and adopt ephemeral volume practices to limit the reuse of writable host paths.
- Improve detection: add monitoring for podman kube play invocations and file‑integrity alerts for critical host paths.
Source: MSRC Security Update Guide - Microsoft Security Response Center