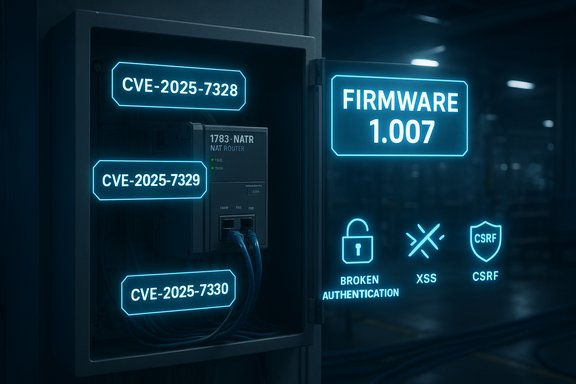
Rockwell Automation has published a critical security advisory for the 1783‑NATR Network Address Translation (NAT) router: three distinct vulnerabilities (CVE‑2025‑7328, CVE‑2025‑7329 and CVE‑2025‑7330) affect firmware versions 1.006 and earlier and are fixed in version 1.007; the flaws include a broken authentication condition that can permit unauthenticated administrative actions, a stored cross‑site scripting (XSS) vector and a cross‑site request forgery (CSRF) weakness — together these issues can produce denial‑of‑service, configuration manipulation, or administrative takeover of the device if left unpatched.
The 1783‑NATR is a dedicated NAT router used to map IP addresses between machine and control networks in industrial automation deployments. Rockwell’s advisory (SD1756) lists the three CVE identifiers and states that all firmware prior to 1.007 are affected; the vendor classifies the overall condition as critical and provides corrected firmware 1.007. CISA republished an advisory covering the 1783‑NATR that confirms the affected product and the requirement to upgrade to 1.007 where possible; CISA’s advisory adds an operational risk view and reiterates the usual ICS protective guidance: keep control devices off the public internet, segment networks, and guard remote access paths. Independent vulnerability trackers and national databases have indexed the CVEs and mirrored the vendor’s severity assessments; NVD currently shows vendor-provided vectors and notes that records are awaiting NVD enrichment, reinforcing that formal cataloging is in progress even as vendors and defenders must act. Why this matters: NAT routers like the 1783‑NATR sit in a high‑value network chokepoint. If an attacker can modify NAT rules or gain administrative control, traffic can be redirected, blocked, or sent to unintended endpoints — with direct consequences for device communication, control loop integrity, and plant availability. The combination of a remotely exploitable broken‑authentication issue and web UI vulnerabilities raises both remote‑network and human‑interaction attack paths for ICS operators.
Source: CISA Rockwell Automation 1783-NATR | CISA
 Background / Overview
Background / Overview
The 1783‑NATR is a dedicated NAT router used to map IP addresses between machine and control networks in industrial automation deployments. Rockwell’s advisory (SD1756) lists the three CVE identifiers and states that all firmware prior to 1.007 are affected; the vendor classifies the overall condition as critical and provides corrected firmware 1.007. CISA republished an advisory covering the 1783‑NATR that confirms the affected product and the requirement to upgrade to 1.007 where possible; CISA’s advisory adds an operational risk view and reiterates the usual ICS protective guidance: keep control devices off the public internet, segment networks, and guard remote access paths. Independent vulnerability trackers and national databases have indexed the CVEs and mirrored the vendor’s severity assessments; NVD currently shows vendor-provided vectors and notes that records are awaiting NVD enrichment, reinforcing that formal cataloging is in progress even as vendors and defenders must act. Why this matters: NAT routers like the 1783‑NATR sit in a high‑value network chokepoint. If an attacker can modify NAT rules or gain administrative control, traffic can be redirected, blocked, or sent to unintended endpoints — with direct consequences for device communication, control loop integrity, and plant availability. The combination of a remotely exploitable broken‑authentication issue and web UI vulnerabilities raises both remote‑network and human‑interaction attack paths for ICS operators. The Vulnerabilities — Technical Summary
CVE‑2025‑7328: Missing Authentication for Critical Function (Broken Authentication)
- Description: Multiple broken authentication issues exist due to missing authentication checks on critical functions. This can permit unauthenticated actors to perform administrative actions such as modifying NAT rules or changing configuration, or cause denial‑of‑service.
- Affected versions: 1.006 and prior; fixed in 1.007.
- Severity: Rockwell reports a CVSS v3 base score of 10.0 (AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H) and a CVSS v4 base score of 9.9 (AV:N/AC:L/AT:N/PR:N/UI:N/VC:H/VI:H/VA:H/SC:N/SI:N/SA:H). These vectors indicate network attackability with no required privileges or user interaction and high impact to confidentiality, integrity and availability.
This vulnerability is the highest operational risk because an unauthenticated admin‑level action on a NAT device can be used to break communications between controllers, HMIs and enterprise systems or to stealthily divert traffic — outcomes that quickly escalate into production disruption or safety concerns.
CVE‑2025‑7329: Stored Cross‑Site Scripting (XSS)
- Description: A stored XSS flaw arises from missing special‑character filtering/encoding in configuration fields; an attacker able to add content behind an admin login could embed script that later executes in the browser of an admin viewing the UI.
- Affected versions: 1.006 and prior; fixed in 1.007.
- Severity: Rockwell lists a CVSS v3 base score of 8.4 and a CVSS v4 base score of 8.5. The v3 and v4 vectors show this is network‑accessible but requires higher privileges (authenticated admin) and user interaction (an admin viewing a page) to exploit.
Stored XSS can be leveraged to capture session tokens, modify displayed content, or programmatically submit admin actions (in combination with the missing authentication weaknesses this creates a potent chain if attackers can gain initial configuration write access).
CVE‑2025‑7330: Cross‑Site Request Forgery (CSRF)
- Description: The product lacks CSRF protections on an impacted form, allowing an attacker to trick a logged‑in admin into submitting actions via a crafted link or page. If successful, unintended configuration changes can be made without reauthentication.
- Affected versions: 1.006 and prior; fixed in 1.007.
- Severity: Rockwell cites CVSS v3 = 8.0 and CVSS v4 = 7.0, reflecting a scenario that requires a logged‑in user but can be executed remotely with low technical complexity if social engineering succeeds.
Taken together, the three vulnerabilities create multiple, complementary attack paths: unauthenticated network‑level control (CVE‑7328), web UI scripting-based control and data theft (CVE‑7329), and CSRF‑driven silent configuration change (CVE‑7330). The effective severity of the overall situation is therefore multiplicative: a single unpatched device can allow a remote attacker to both cause immediate denial‑of‑service and gain ongoing administrative control.
Risk Evaluation — Operational Impact and Likely Attack Scenarios
Industrial NAT routers are not ornamental; they are functional chokepoints. The real operational consequences include:- Loss of availability: Deliberate or accidental NAT rule modification or device DoS can stop EtherNet/IP or other control‑plane communications between PLCs, HMIs and supervisory systems, halting production or key control loops.
- Traffic diversion / integrity loss: Maliciously modified NAT rules can send traffic to incorrect endpoints, silently breaking safety interlocks or feeding telemetry to attacker‑controlled destinations.
- Administrative takeover / persistent misconfiguration: If an attacker gains or forges admin actions (broken authentication + CSRF), they can implant persistent, hard‑to‑detect changes that survive reboots or require physical intervention to correct.
- Web UI abuse and credential theft: Stored XSS can lead to credential/session theft or force administrative actions via a victim admin’s browser — especially dangerous if web management is performed from a Windows engineering workstation that has elevated rights in the OT domain.
CISA and Rockwell note there are no confirmed reports of in‑the‑wild exploitation targeting these specific CVEs at the time of the advisories; however, both agencies and vendors stress that the absence of reports is not a guarantee of safety and that low complexity, network‑accessible vulnerabilities demand rapid action. Operational attack scenarios: - Remote unauthenticated actor sends crafted requests to the 1783‑NATR API/UI and modifies NAT rules, causing immediate loss of communication for a production cell.
- Attacker with some access to configuration fields (for example via a compromised vendor account) plants a stored XSS payload; when an on‑site admin visits the configuration page, the payload exfiltrates session cookies and executes privileged operations.
- Social engineering lures an authenticated admin into a malicious page that triggers CSRF‑based reconf, silently altering routing or disabling logging.
What Rockwell and CISA Recommend — Corrective Actions
- Primary fix: Upgrade every 1783‑NATR unit to firmware/software version 1.007 or later. Rockwell marks this advisory as corrected in 1.007 and strongly recommends updating.
- If immediate upgrade is not possible: Follow Rockwell’s published security best practices and CISA’s defensive measures:
- Minimize network exposure of control devices; do not expose 1783‑NATR to the public internet.
- Isolate control networks and devices behind firewalls; do not trust flat networks between IT and OT.
- When remote access is required, rely on hardened, monitored VPN/jump hosts and enforce MFA and strict allow‑lists. Recognize that VPN is only as secure as the endpoints and must be kept patched.
These high‑level mitigations are the same practical defense‑in‑depth controls ICS operators should use for any remote‑accessible control device: remove internet exposure, minimize attack surface, and log/monitor all management access. Rockwell and CISA both emphasize that upgrading is the definitive remediation; compensating controls are stopgaps only.
Practical, Prioritized Playbook (Windows‑Centric OT/Engineering Teams)
Applying firmware in industrial environments requires planning. The following checklist is prioritized for rapid, safe remediation and is derived from Rockwell and CISA guidance plus practical OT operations experience.Immediate (0–72 hours)
- Inventory every 1783‑NATR device (site, IP, firmware version). Verify versions by checking device UI or management tools.
- Block external access: ensure 1783‑NATR devices are not reachable from the internet; implement firewall rules to allow only explicit, logged management hosts.
- Restrict vendor remote access and require MFA on remote sessions; temporarily suspend any broad remote management tunnels to OT unless necessary and monitored.
- Increase logging and monitoring on jump servers and Windows engineering workstations used to manage 1783‑NATR; enable packet capture where safe to detect anomalous requests.
Short term (days–weeks)
- Acquire 1.007 firmware from Rockwell’s authenticated channels; verify checksums/signatures before distribution.
- Test the firmware in an isolated lab that mirrors production; validate controller/HMI compatibility and restore procedures.
- Prepare a staged deployment plan: patch non‑critical segments first, then roll forward to higher‑risk cells. Maintain a rollback plan and spares in case of unexpected regressions.
Medium / Long term (weeks–months)
- Harden Windows management hosts: keep engineering workstations and jump servers patched, run reputable endpoint protection, disable unnecessary services, and enforce least‑privilege administration.
- Enforce strict network segmentation: application‑aware firewalls, VLANs, and ACLs specific to EtherNet/IP/CIP protocols.
- Make third‑party component tracking a lifecycle policy: inventory RTOS and library dependencies across OT devices so future shared‑component advisories can be triaged quickly.
Detection and Monitoring Recommendations
- Deploy network IDS/IPS and IPS signatures that watch for unusual NAT‑related API calls, repeated malformed requests, or high volumes of UI requests that could indicate automated scanning or CSRF attempts.
- Monitor 1783‑NATR web UI logs (access logs and configuration change logs) for unusual POSTs, suspicious payloads, or repeated parameterized requests that may indicate XSS injection attempts.
- Instrument Windows jump hosts and engineering workstations to record all remote sessions to OT gear and alert on new or unapproved management hosts or binaries.
- Alert on unexpected NAT rule changes and configuration save events; route these alerts to both IT and OT owners for rapid verification.
Practical Hardening Tips (short list)
- Disable web management if not required; manage devices only via secure, internal management channels.
- Enforce allow‑listed IP addresses for device management and restrict SSH/HTTPS management ports to those hosts.
- Use centrally managed jump servers and MFA for all admin access; do not permit direct remote logons from general‑purpose endpoints.
- Keep recovery media and documented recovery steps available on‑site; ensure physical access procedures exist to recover a misconfigured device if administrative access is lost.
Cross‑Verification and Caveats
Key vendor claims — affected versions (1.006 and prior), remediation in 1.007, CVE identifiers and vendor‑provided CVSS vectors — are recorded in Rockwell’s security advisory (SD1756) and mirrored by CISA’s advisory; NVD entries exist but have been marked as awaiting NVD enrichment, meaning formal NVD scoring may follow vendor‑provided scores. These items were cross‑checked across Rockwell’s advisory and the government advisory to ensure consistency before publishing this guide. Caveats and items that still require local validation:- NVD and other third‑party databases may revise scores or vectors during enrichment; operators should rely primarily on vendor fixes and configuration guidance for remediation timing but watch NVD for any updated analysis.
- The absence of confirmed exploitation in the wild is not a guarantee of safety; low‑complexity, network‑accessible vulnerabilities are often weaponized quickly once public. Treat the advisory as urgent.
Wider Lessons — Supply Chain & Operational Security
This advisory is another example of how relatively small flaws in control‑plane devices can produce outsized operational risk. Two broader takeaways:- Treat network infrastructure in OT as critical assets. Devices that perform routing, NAT, or protocol translation are high‑impact targets — they must be included in high‑priority patch cycles and inventorying processes.
- Track component lineage. Several industrial advisories originate from shared third‑party software or libraries; a single vulnerable component can produce a broad blast radius across multiple SKUs and vendors. Proactive third‑party component tracking reduces surprise windows.
Conclusion
Rockwell Automation’s SD1756 advisory for the 1783‑NATR identifies three serious, complementary vulnerabilities — an unauthenticated broken‑authentication condition, stored XSS and CSRF — that together create realistic, low‑complexity attack paths for causing denial‑of‑service, traffic diversion, or administrative takeover of NAT routers deployed in industrial environments. The vendor’s fix (firmware 1.007) is the definitive remediation, and immediate inventory, isolation and staged patching should be treated as operational priorities. Where patching is delayed, apply strict segmentation, limit management access to hardened jump hosts, and increase logging and monitoring for anomalous NAT configuration activity. Acting now reduces the chance that a simple, network‑facing exploit turns into an extended outage or a clandestine compromise of critical manufacturing communications.Source: CISA Rockwell Automation 1783-NATR | CISA
Last edited: