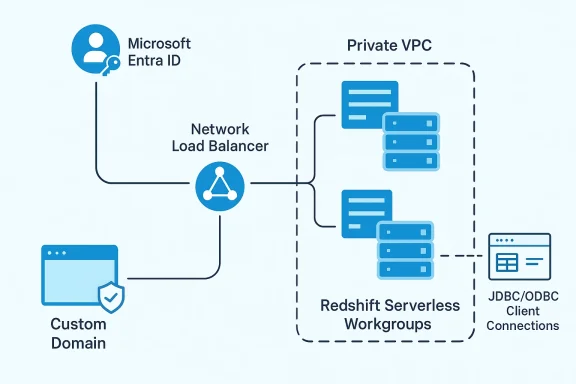
Amazon Web Services has published a detailed blueprint for securely fronting multiple Amazon Redshift Serverless workgroups with a Network Load Balancer while using Microsoft Entra ID for native authentication. The pattern is aimed at organizations that need one stable connection endpoint for tools such as DBeaver and Power BI, but also want to keep analytics traffic private, scalable, and aligned with enterprise identity standards. It is a timely design because Redshift Serverless already supports managed VPC endpoints and custom domain names, and AWS has been steadily expanding support for identity-aware driver workflows and multi-warehouse architectures. (aws.amazon.com)
For years, one of the hardest parts of enterprise analytics has been reconciling speed, scale, and security in the same architecture. Data teams want to spin up more compute as workloads increase, while security teams want predictable identity controls, private networking, and minimal exposure of backend endpoints. Amazon Redshift Serverless is AWS’s answer to the capacity side of that equation, and the recent NLB-based design extends that story into access management and connection consistency. (aws.amazon.com)
The architecture also reflects a broader shift in how modern warehouses are deployed. Instead of one monolithic platform serving every workload, organizations increasingly use multiple workgroups or warehouses to isolate business units, development stages, or high-concurrency workloads. Redshift data sharing lets those workgroups read the same data without copying it around, which supports horizontal scale while preserving a single source of truth. AWS explicitly frames this as a way to share live data across clusters, workgroups, AWS accounts, and Regions. (aws.amazon.com)
At the networking layer, AWS has already established the core primitives needed for this pattern. Redshift-managed VPC endpoints provide private access from another VPC, and the Redshift docs note that Serverless can be connected through managed VPC endpoints and cross-VPC access patterns. The new blog post simply combines those building blocks with a Network Load Balancer so that clients have one DNS name rather than a changing list of workgroup-specific endpoints. (aws.amazon.com)
Identity is the other half of the story. AWS has already said that Redshift JDBC, Python, and ODBC drivers can be used with corporate identity through AWS IAM Identity Center and external identity providers, including Microsoft Entra ID. The new blog post pushes that idea into a more concrete implementation pattern for SQL clients, showing how browser-based OAuth-style sign-in can be paired with a private NLB-fronted Redshift Serverless endpoint. (aws.amazon.com)
The result is an architecture that sits at the intersection of network abstraction and identity federation. On one side, administrators get a stable endpoint and the flexibility to add more workgroups later. On the other, users keep their familiar Microsoft Entra ID sign-in flow and connect through JDBC or ODBC without being forced into a completely different enterprise identity model. That combination is why this design matters beyond the narrow scope of one AWS blog post. (aws.amazon.com)
This matters most in organizations where the warehouse estate is already fragmented by purpose. One workgroup might serve production reporting, another might handle sandbox or development traffic, and a third might be dedicated to a high-concurrency analytics team. The more the environment scales, the less attractive it becomes to expose each workgroup directly to every client. (aws.amazon.com)
The larger benefit is architectural flexibility. A company can validate the pattern with a single workgroup and then expand to multiple workgroups later without changing users’ connection settings. That makes the design future-friendly in a way many enterprise access projects are not. (aws.amazon.com)
For users, this reduces friction. For administrators, it reduces the number of passwords, local database accounts, and one-off exceptions that tend to accumulate in analytics environments. That accumulation is often where security debt lives, because warehouse access can quietly outgrow the governance model that originally created it. A clean login experience is not just convenience; it is an access-control strategy. (aws.amazon.com)
The blog’s choice to support both DBeaver and Power BI is important because those represent two very different client profiles. DBeaver is commonly used by technical users and database practitioners, while Power BI is often a business intelligence endpoint for broader analyst and reporting audiences. By showing both, AWS is signaling that the pattern is meant to be operationally broad rather than niche. (aws.amazon.com)
That separation also has governance advantages. Centralized ETL or producer warehouses can expose curated datasets to multiple consumer workgroups while keeping the data model stable. When done well, this becomes a control boundary rather than a duplication problem. The warehouse becomes modular without becoming messy. (aws.amazon.com)
This design also preserves a network boundary that many enterprises want. Rather than exposing a public endpoint, the traffic stays inside AWS networking constructs and follows a controlled path. AWS’s Redshift documentation reinforces that managed VPC endpoints and cross-VPC access are built to avoid public IPs and internet routing. (docs.aws.amazon.com)
That matters because analytics tooling is often spread across teams with different levels of operational sophistication. One analyst may never need to know which workgroup they are hitting, only that the connection works and the sign-in is legitimate. The custom domain hides the moving parts and gives IT a place to make changes without retraining users. (docs.aws.amazon.com)
It also means the admin has to be careful with certificate and SSL settings. AWS’s custom-domain guidance notes that
This is one of those areas where operational ceremony is a feature, not a flaw. The extra steps make it harder to accidentally expose a warehouse under an unmanaged domain or trust boundary. In security terms, the DNS and certificate configuration are not overhead; they are the proof of intent. (aws.amazon.com)
That distinction matters. A database access path needs to be predictable, low-latency, and transparent to client drivers. An NLB preserves that model better than a more opinionated layer could. The architecture is therefore pragmatic rather than flashy, which is usually a good sign in infrastructure design. (aws.amazon.com)
That is important because SQL clients are often where identity modernizations stall. Teams can modernize SaaS sign-in easily enough, but database clients have historically been harder to align with corporate SSO. This pattern is an attempt to erase that inconsistency without changing the analyst’s workflow too dramatically. (aws.amazon.com)
The same is true for DBeaver, but from a different angle. Technical users generally need more direct access, more visibility into schema, and more flexibility in query behavior. The architecture does not force them into a different workflow; it simply inserts stronger identity and transport controls under the hood. That is the rare security change users may not hate. (aws.amazon.com)
It also supports least privilege in a more realistic way. Data teams often need temporary access for a project, a report refresh, or a troubleshooting exercise. When that access is federated rather than hard-coded, it is easier to remove later without leaving behind dormant local credentials. (aws.amazon.com)
The important operational insight is that the client does not need to know the load-balanced topology. From the user’s perspective, they are simply signing in and connecting to a trusted hostname. From the administrator’s perspective, the backend can evolve as long as the DNS and certificate layer remain consistent. (docs.aws.amazon.com)
The implication is that the architecture can serve both ad hoc and reporting use cases. That matters because many enterprises use one path for technical access and another for governed reporting access, creating duplicate security models. A single identity-backed connection pattern reduces that split. (aws.amazon.com)
A realistic rollout would still need a controlled pilot. You would want to test certificate chains, DNS propagation, driver versions, and user scopes before broad deployment. The blog is a deployment guide, not a substitute for an enterprise change-management plan. That caveat is easy to miss and very expensive when ignored. (aws.amazon.com)
That matters because the real competition in analytics is often not about raw query speed. It is about how quickly an enterprise can onboard users without creating security exceptions or operational debt. By making Entra-backed sign-in and custom endpoints part of the documented solution, AWS is clearly targeting that pain point. (aws.amazon.com)
This is especially relevant for organizations already standardized on Entra ID for workforce identity. They can extend that identity posture into Redshift without introducing a second major auth ecosystem for BI and SQL clients. In a mixed-cloud world, that kind of identity continuity is a strategic advantage. (aws.amazon.com)
The big idea is that data scale and governance scale must now move together. If organizations can add warehouses without multiplying access complexity, they have a better chance of keeping analytics agile without turning security into a bottleneck. That is the promise AWS is trying to sell here, and it is a persuasive one.
There is also a subtle maintenance challenge. Certificates expire, DNS records drift, driver versions change, and workgroups get added or removed over time. In other words, the architecture is easier to set up than to forget, which is exactly why good documentation and change control matter. (aws.amazon.com)
The upside is that observability may actually improve. A single ingress point gives security and operations teams one place to inspect connections, TLS settings, and routing behavior. Centralization is a double-edged sword, but it can be a very useful one. (aws.amazon.com)
The lesson is that the technical stack is only part of the answer. The other part is disciplined identity governance, certificate management, and client configuration hygiene. Without that, the “secure” in the architecture description becomes more aspirational than operational. (aws.amazon.com)
Finally, the architecture is best suited to organizations that already have enough scale to justify the control plane overhead. A small team with one warehouse may not need a load-balanced, custom-domain, federated setup. For them, the pattern could be more engineering than value. That is not a flaw in the architecture itself, only a reminder that good infrastructure is always contextual. (docs.aws.amazon.com)
For enterprises, the real question is whether they want to standardize around a single identity-aware access surface for analytics. If the answer is yes, then Microsoft Entra ID plus Redshift Serverless behind a Network Load Balancer is a sensible pattern to pilot now. If the answer is no, they may still borrow pieces of it later: custom domains, private endpoints, or Entra-backed client auth. (aws.amazon.com)
Source: Amazon Web Services Secure multi-warehouse Amazon Redshift access behind a Network Load Balancer using Microsoft Entra ID | Amazon Web Services
 Background
Background
For years, one of the hardest parts of enterprise analytics has been reconciling speed, scale, and security in the same architecture. Data teams want to spin up more compute as workloads increase, while security teams want predictable identity controls, private networking, and minimal exposure of backend endpoints. Amazon Redshift Serverless is AWS’s answer to the capacity side of that equation, and the recent NLB-based design extends that story into access management and connection consistency. (aws.amazon.com)The architecture also reflects a broader shift in how modern warehouses are deployed. Instead of one monolithic platform serving every workload, organizations increasingly use multiple workgroups or warehouses to isolate business units, development stages, or high-concurrency workloads. Redshift data sharing lets those workgroups read the same data without copying it around, which supports horizontal scale while preserving a single source of truth. AWS explicitly frames this as a way to share live data across clusters, workgroups, AWS accounts, and Regions. (aws.amazon.com)
At the networking layer, AWS has already established the core primitives needed for this pattern. Redshift-managed VPC endpoints provide private access from another VPC, and the Redshift docs note that Serverless can be connected through managed VPC endpoints and cross-VPC access patterns. The new blog post simply combines those building blocks with a Network Load Balancer so that clients have one DNS name rather than a changing list of workgroup-specific endpoints. (aws.amazon.com)
Identity is the other half of the story. AWS has already said that Redshift JDBC, Python, and ODBC drivers can be used with corporate identity through AWS IAM Identity Center and external identity providers, including Microsoft Entra ID. The new blog post pushes that idea into a more concrete implementation pattern for SQL clients, showing how browser-based OAuth-style sign-in can be paired with a private NLB-fronted Redshift Serverless endpoint. (aws.amazon.com)
The result is an architecture that sits at the intersection of network abstraction and identity federation. On one side, administrators get a stable endpoint and the flexibility to add more workgroups later. On the other, users keep their familiar Microsoft Entra ID sign-in flow and connect through JDBC or ODBC without being forced into a completely different enterprise identity model. That combination is why this design matters beyond the narrow scope of one AWS blog post. (aws.amazon.com)
Why This Pattern Matters
The practical appeal of this architecture is its simplicity at the edge and complexity underneath. Users connect to one name, authenticate once, and reach the correct Redshift endpoint without having to understand how many workgroups exist behind the scenes. That is exactly the sort of operational simplification enterprises pay for, even when the back end is becoming more distributed. (aws.amazon.com)One endpoint, many warehouses
The NLB acts as a stable front door for multiple Redshift Serverless managed VPC endpoints. AWS’s own explanation of the pattern emphasizes that the load balancer becomes the single point of contact for clients, while target groups forward traffic to the appropriate Redshift-managed endpoint IPs. In plain English, this reduces the coordination burden on BI tools, data scientists, and analysts who do not want to chase endpoint changes every time the warehouse architecture evolves. (aws.amazon.com)This matters most in organizations where the warehouse estate is already fragmented by purpose. One workgroup might serve production reporting, another might handle sandbox or development traffic, and a third might be dedicated to a high-concurrency analytics team. The more the environment scales, the less attractive it becomes to expose each workgroup directly to every client. (aws.amazon.com)
The larger benefit is architectural flexibility. A company can validate the pattern with a single workgroup and then expand to multiple workgroups later without changing users’ connection settings. That makes the design future-friendly in a way many enterprise access projects are not. (aws.amazon.com)
Identity without credential sprawl
Microsoft Entra ID federation gives the access layer a familiar enterprise control plane. AWS notes that customers can connect to Redshift using their preferred identity provider through IAM Identity Center, including Microsoft Entra ID, via JDBC and ODBC drivers. That means the authentication problem is moved out of application-specific credentials and into a managed identity workflow. (aws.amazon.com)For users, this reduces friction. For administrators, it reduces the number of passwords, local database accounts, and one-off exceptions that tend to accumulate in analytics environments. That accumulation is often where security debt lives, because warehouse access can quietly outgrow the governance model that originally created it. A clean login experience is not just convenience; it is an access-control strategy. (aws.amazon.com)
The blog’s choice to support both DBeaver and Power BI is important because those represent two very different client profiles. DBeaver is commonly used by technical users and database practitioners, while Power BI is often a business intelligence endpoint for broader analyst and reporting audiences. By showing both, AWS is signaling that the pattern is meant to be operationally broad rather than niche. (aws.amazon.com)
How the Architecture Works
At a high level, the design chains together Redshift data sharing, managed VPC endpoints, a Network Load Balancer, custom domains, DNS, and federated driver sign-in. Each piece does a specific job, and none of them by themselves solve the whole problem. The architecture works because they are layered in a very deliberate order. (aws.amazon.com)Redshift data sharing as the warehouse fabric
AWS describes Redshift data sharing as a way to securely share live data across clusters, workgroups, accounts, and Regions without manual copying. That is the enabling layer for multi-warehouse analytics, because it lets teams divide compute without fragmenting data ownership. The implication is subtle but powerful: scale the compute, not the truth. (aws.amazon.com)That separation also has governance advantages. Centralized ETL or producer warehouses can expose curated datasets to multiple consumer workgroups while keeping the data model stable. When done well, this becomes a control boundary rather than a duplication problem. The warehouse becomes modular without becoming messy. (aws.amazon.com)
Managed VPC endpoints behind the load balancer
Redshift-managed VPC endpoints provide the private IP targets that the NLB needs. AWS’s blog explains that each workgroup gets a dedicated private IP, which can then be registered into the target group behind the load balancer. That is the key trick that turns multiple warehouses into one reachable service surface. (aws.amazon.com)This design also preserves a network boundary that many enterprises want. Rather than exposing a public endpoint, the traffic stays inside AWS networking constructs and follows a controlled path. AWS’s Redshift documentation reinforces that managed VPC endpoints and cross-VPC access are built to avoid public IPs and internet routing. (docs.aws.amazon.com)
Custom domains and DNS as the human interface
Custom domain names are the user-facing glue. AWS’s Redshift docs say custom URLs make client connections easier to remember, support rerouting traffic centrally, and avoid exposing private server names in connection strings. In this architecture, the custom domain becomes the stable contract between the user and the back end. (docs.aws.amazon.com)That matters because analytics tooling is often spread across teams with different levels of operational sophistication. One analyst may never need to know which workgroup they are hitting, only that the connection works and the sign-in is legitimate. The custom domain hides the moving parts and gives IT a place to make changes without retraining users. (docs.aws.amazon.com)
Networking Details and Security Posture
The most interesting part of the design is not the NLB itself but how the networking choices constrain exposure. Redshift Serverless is typically accessed through private connectivity mechanisms, and AWS documents that managed VPC endpoints and private access patterns are intended to keep traffic off the public internet. That makes the architecture attractive for security-conscious organizations, especially those with regulated analytics workloads. (docs.aws.amazon.com)TCP passthrough and port consistency
The blog configures the NLB listener for TCP on port 5439, the common Redshift default. Because the NLB operates at the transport layer rather than terminating application traffic, the backend connection behavior remains close to what Redshift and the JDBC/ODBC drivers expect. That is useful when the primary goal is connection brokering rather than protocol translation. (aws.amazon.com)It also means the admin has to be careful with certificate and SSL settings. AWS’s custom-domain guidance notes that
sslmode=verify-full works for the custom endpoint, while the default endpoint may require verify-ca instead. In practice, this is a reminder that the endpoint abstraction is only as clean as the TLS configuration beneath it. (aws.amazon.com)DNS and certificate validation
The blog’s ACM and Route 53 steps do more than just “make names resolve.” They establish domain ownership, prove certificate control, and ensure that Redshift custom domain names are tied to a valid certificate chain. AWS’s custom-domain docs make clear that the custom domain association is created through the Redshift console and depends on an ACM certificate. (aws.amazon.com)This is one of those areas where operational ceremony is a feature, not a flaw. The extra steps make it harder to accidentally expose a warehouse under an unmanaged domain or trust boundary. In security terms, the DNS and certificate configuration are not overhead; they are the proof of intent. (aws.amazon.com)
Why the NLB is the right layer
A Network Load Balancer is a reasonable fit because the target is a private database endpoint, not a stateless web tier. AWS’s earlier Redshift Serverless NLB post describes the NLB as the single point of contact that distributes traffic across multiple managed VPC endpoints, increasing availability, scalability, and performance. That framing tells you the load balancer is there for connection management and routing stability, not application intelligence. (aws.amazon.com)That distinction matters. A database access path needs to be predictable, low-latency, and transparent to client drivers. An NLB preserves that model better than a more opinionated layer could. The architecture is therefore pragmatic rather than flashy, which is usually a good sign in infrastructure design. (aws.amazon.com)
Identity Integration with Microsoft Entra ID
The identity story is where this pattern becomes especially relevant for Windows and Microsoft-centric enterprises. AWS already supports Redshift driver sign-on through IAM Identity Center with corporate identity providers, and Microsoft Entra ID is explicitly one of the supported external identity providers in that flow. The blog’s instructions show how to configure native IdP authentication in JDBC and ODBC clients using Entra-specific values such as client ID, tenant, and scope. (aws.amazon.com)Browser-based authentication in SQL clients
The DBeaver workflow in the post relies on JDBC properties such as the browser OAuth plugin and an Entra tenant configuration. The Power BI workflow uses the ODBC driver and browser-based Azure AD authentication. Both follow the same idea: the user signs in through a browser, the identity provider issues the necessary tokens, and the client then reaches Redshift through the stable NLB endpoint. (aws.amazon.com)That is important because SQL clients are often where identity modernizations stall. Teams can modernize SaaS sign-in easily enough, but database clients have historically been harder to align with corporate SSO. This pattern is an attempt to erase that inconsistency without changing the analyst’s workflow too dramatically. (aws.amazon.com)
Enterprise identity meets analytics tooling
Power BI is a particularly meaningful example because it often sits at the boundary between business users and governed enterprise data. If a company can preserve Microsoft Entra ID sign-in while routing traffic privately to Redshift, it reduces the need for separate credentials or ad hoc gateway patterns. That makes policy enforcement easier to explain and easier to audit. (aws.amazon.com)The same is true for DBeaver, but from a different angle. Technical users generally need more direct access, more visibility into schema, and more flexibility in query behavior. The architecture does not force them into a different workflow; it simply inserts stronger identity and transport controls under the hood. That is the rare security change users may not hate. (aws.amazon.com)
Why federated identity matters operationally
Federated identity becomes valuable when access spans more than one warehouse, more than one tool, and potentially more than one team. If every connection can be linked back to Microsoft Entra ID, then account lifecycle events in Entra can be reflected in analytics access more naturally than if users were managed as local Redshift identities. That aligns security administration with the rest of the enterprise identity stack. (aws.amazon.com)It also supports least privilege in a more realistic way. Data teams often need temporary access for a project, a report refresh, or a troubleshooting exercise. When that access is federated rather than hard-coded, it is easier to remove later without leaving behind dormant local credentials. (aws.amazon.com)
Client Configuration and User Experience
The user-facing aspect of the solution is intentionally mundane, and that is a strength. The blog’s examples show administrators configuring the host as the custom NLB domain, pointing JDBC or ODBC to the Redshift database, and using Entra-backed browser authentication. That is exactly how enterprise infrastructure should feel when it succeeds: boring at the point of use. (aws.amazon.com)DBeaver and JDBC
In DBeaver, the host is the custom NLB CNAME, the database is specified, and the authentication mode is database-native with browser-based Entra support through the Redshift driver plugin. The blog also calls out properties likesslmode=verify-ca, client_id, idp_tenant, listen_port, and scope, which together steer the JDBC driver into the correct identity flow.The important operational insight is that the client does not need to know the load-balanced topology. From the user’s perspective, they are simply signing in and connecting to a trusted hostname. From the administrator’s perspective, the backend can evolve as long as the DNS and certificate layer remain consistent. (docs.aws.amazon.com)
Power BI and ODBC
The Power BI workflow is similar but uses the ODBC driver and a system DSN. The post shows the user selecting the Redshift ODBC driver, specifying the host, port, database, and identity provider settings, then completing Entra authentication in the browser before loading data into Power BI Desktop. That is a strong proof point because it demonstrates business intelligence integration rather than just database-client connectivity.The implication is that the architecture can serve both ad hoc and reporting use cases. That matters because many enterprises use one path for technical access and another for governed reporting access, creating duplicate security models. A single identity-backed connection pattern reduces that split. (aws.amazon.com)
Validation and troubleshooting
The blog’s validation steps are simple by design: test the connection, authenticate in the browser, and confirm success in the client. That simplicity matters because connection failures in identity-aware database setups can be hard to diagnose when DNS, TLS, driver plugins, and federation settings are all involved. The architecture’s virtue is that the moving pieces are clearly named, even if they are not trivial to configure. (aws.amazon.com)A realistic rollout would still need a controlled pilot. You would want to test certificate chains, DNS propagation, driver versions, and user scopes before broad deployment. The blog is a deployment guide, not a substitute for an enterprise change-management plan. That caveat is easy to miss and very expensive when ignored. (aws.amazon.com)
Competitive and Market Implications
This architecture is not just a technical how-to; it also signals where cloud analytics access is headed. Customers increasingly want private connectivity, federated identity, and stable logical endpoints that survive backend scaling. AWS is answering those demands by combining Redshift Serverless, data sharing, managed VPC endpoints, and driver-level identity support into a more cohesive story. (aws.amazon.com)AWS versus “lift-and-access” warehouse thinking
The old model was to expose a warehouse, tell users how to connect, and grow from there. That approach works until it doesn’t, especially once multiple teams and multiple tools enter the picture. AWS’s multi-workgroup pattern suggests a more modern model where network access, endpoint naming, and identity federation are all part of the product narrative rather than afterthoughts. (aws.amazon.com)That matters because the real competition in analytics is often not about raw query speed. It is about how quickly an enterprise can onboard users without creating security exceptions or operational debt. By making Entra-backed sign-in and custom endpoints part of the documented solution, AWS is clearly targeting that pain point. (aws.amazon.com)
The Microsoft angle
Microsoft benefits too, even though the workload is running on AWS. If Entra ID is the authoritative identity system across cloud analytics tools, then Microsoft remains central to the user experience regardless of where the warehouse lives. That is classic identity-platform leverage: own the login, and you stay in the middle of the workflow. (aws.amazon.com)This is especially relevant for organizations already standardized on Entra ID for workforce identity. They can extend that identity posture into Redshift without introducing a second major auth ecosystem for BI and SQL clients. In a mixed-cloud world, that kind of identity continuity is a strategic advantage. (aws.amazon.com)
Broader multi-warehouse trends
The market is also moving toward multi-warehouse governance. AWS’s newer Redshift messaging around federated permissions across multi-warehouse architectures shows that the platform is evolving beyond simple data sharing toward a more consistent permissions model across warehouses. That is a strong signal that the architecture in this blog is part of a larger trend, not a one-off pattern.The big idea is that data scale and governance scale must now move together. If organizations can add warehouses without multiplying access complexity, they have a better chance of keeping analytics agile without turning security into a bottleneck. That is the promise AWS is trying to sell here, and it is a persuasive one.
Operational Tradeoffs
No architecture is free of compromise, and this one is no exception. The design improves endpoint consistency and identity integration, but it also adds DNS, certificate, load balancer, and driver complexity. That is acceptable, but only if the organization is ready for the operational overhead. (aws.amazon.com)Configuration sprawl is still real
The blog’s steps are detailed because the solution spans multiple control planes: Redshift, EC2, ACM, Route 53, and client driver settings. That can feel heavy compared with a simple endpoint change, especially for smaller teams. The benefit is strong, but the admin burden is not imaginary. (aws.amazon.com)There is also a subtle maintenance challenge. Certificates expire, DNS records drift, driver versions change, and workgroups get added or removed over time. In other words, the architecture is easier to set up than to forget, which is exactly why good documentation and change control matter. (aws.amazon.com)
Failure domains and observability
The load balancer becomes a shared dependency, so it needs clear monitoring and capacity planning. If multiple workgroups depend on the same front door, any issue in that front door affects more than one analytical path. That is not necessarily a weakness, but it is a centralization risk that should be acknowledged. (aws.amazon.com)The upside is that observability may actually improve. A single ingress point gives security and operations teams one place to inspect connections, TLS settings, and routing behavior. Centralization is a double-edged sword, but it can be a very useful one. (aws.amazon.com)
Security is easier to promise than to sustain
The architecture supports secure access, but secure access is a process, not a feature. If identities are poorly governed, scopes are overbroad, or custom domains are managed casually, the design can still become brittle. That is true of almost every enterprise access model, and this one is no exception. (aws.amazon.com)The lesson is that the technical stack is only part of the answer. The other part is disciplined identity governance, certificate management, and client configuration hygiene. Without that, the “secure” in the architecture description becomes more aspirational than operational. (aws.amazon.com)
Strengths and Opportunities
The strongest argument for this architecture is that it solves several enterprise problems at once: private connectivity, identity federation, stable connection names, and scale-out warehouse design. It also creates a clean path for organizations that want to standardize analytics access around Microsoft Entra ID without redesigning every client workflow. The opportunity is especially compelling for mixed teams that use both BI tools and SQL clients. (aws.amazon.com)- Single connection endpoint for many workgroups, reducing client churn and operational confusion.
- Private networking through Redshift-managed VPC endpoints and NLB routing.
- Microsoft Entra ID federation for enterprise sign-in consistency.
- Custom domain names that simplify DNS, TLS, and user experience.
- Horizontal scale through Redshift data sharing and multiple consumer workgroups.
- Tool flexibility for both DBeaver and Power BI users.
- Better governance alignment by anchoring access to enterprise identity rather than local warehouse credentials. (aws.amazon.com)
Risks and Concerns
The biggest risk is implementation complexity creeping in through the side door. Although the user experience becomes cleaner, administrators must orchestrate ACM, Route 53, Redshift custom domains, target groups, and driver settings correctly. A misstep in any one layer can break access or weaken the security posture. (aws.amazon.com)- Certificate lifecycle management can become a recurring operational burden.
- DNS misconfiguration can make the stable endpoint unstable in practice.
- Driver version drift may cause authentication failures in client tools.
- Shared ingress dependencies can create a wider blast radius if the NLB or routing layer fails.
- Over-permissive identity scopes can turn federated sign-in into broad access rather than controlled access.
- Hidden backend complexity may make troubleshooting harder for smaller teams.
- Change management gaps can undermine trust in the whole access path. (aws.amazon.com)
Finally, the architecture is best suited to organizations that already have enough scale to justify the control plane overhead. A small team with one warehouse may not need a load-balanced, custom-domain, federated setup. For them, the pattern could be more engineering than value. That is not a flaw in the architecture itself, only a reminder that good infrastructure is always contextual. (docs.aws.amazon.com)
Looking Ahead
What makes this pattern interesting is not only what it does today, but how it positions Redshift for future multi-warehouse growth. AWS has already moved toward federated permissions across warehouses, which suggests a future where data sharing, access governance, and identity-aware connections become even more tightly integrated. That would make the NLB-plus-custom-domain pattern feel less like a workaround and more like an early building block of the platform’s direction.For enterprises, the real question is whether they want to standardize around a single identity-aware access surface for analytics. If the answer is yes, then Microsoft Entra ID plus Redshift Serverless behind a Network Load Balancer is a sensible pattern to pilot now. If the answer is no, they may still borrow pieces of it later: custom domains, private endpoints, or Entra-backed client auth. (aws.amazon.com)
- Expect more emphasis on multi-warehouse governance and cross-workgroup permissions.
- Expect client tooling to keep improving around browser-based federation.
- Expect custom domain and TLS management to remain central to private analytics access.
- Expect identity providers like Microsoft Entra ID to stay at the center of enterprise SQL access.
- Expect private networking patterns to be preferred over public endpoints in regulated environments.
Source: Amazon Web Services Secure multi-warehouse Amazon Redshift access behind a Network Load Balancer using Microsoft Entra ID | Amazon Web Services