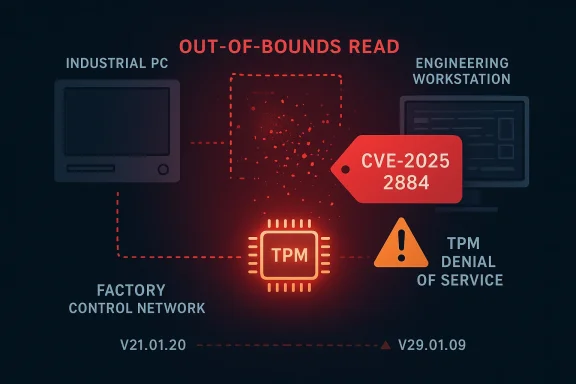
Siemens’ latest TPM 2.0 advisory is a reminder that even a low-level trust component can become a meaningful enterprise risk when it sits beneath industrial PCs, field engineering stations, and critical-manufacturing endpoints. The issue, tracked as CVE-2025-2884, is described as an out-of-bounds read in the TCG TPM 2.0 reference implementation’s
The advisory matters because TPM flaws are not ordinary application bugs. A Trusted Platform Module is supposed to harden identity, key storage, secure boot, and device trust flows, so weaknesses in that layer can undermine confidence in the entire machine, even if the immediate symptom looks limited to a crash or a read past the end of memory. Siemens’ description points to a problem in the TCG TPM2.0 reference implementation, not just a single device model quirk, which helps explain why the affected product list spans multiple SIMATIC IPC families and engineering platforms
The exposure is especially relevant in industrial environments because many of the listed systems are used as engineering workstations, embedded industrial PCs, or service laptops that bridge office and operational technology networks. In those contexts, a TPM weakness is not just a local reliability issue; it is part of the device-trust chain that protects firmware state, credentials, and platform attestation. If the TPM becomes unstable or leaks information, defenders have to think beyond the chip and assess what upstream controls may also be weakened
Siemens’ approach in this advisory is also typical of industrial security practice: patch what can be patched, prepare more fixes where needed, and rely on network isolation, protected access, and operational hardening where software remediation is not immediate. That is a pragmatic posture, but it also reflects a persistent reality in OT security: vendors often need time to validate firmware updates across hardware variants, and operators must manage risk in the interim rather than waiting for a perfect outcome
What makes this disclosure more than a routine CVE notice is the breadth of the affected catalog. The advisory names SIMATIC CN 4100, Field PG M5/M6, multiple SIMATIC IPC BX/PX/RW/MD models, several E-series IPCs, ITP1000, and SIPLUS IPC427E. Some product families are affected “all/*,” while others require specific version thresholds such as
The advisory’s impact statement is also important. Siemens says the flaw could lead to disclosure of information or denial of service of the TPM, not necessarily full system compromise. That narrower impact description should not lull operators into complacency. In industrial contexts, a TPM DoS can still trigger availability problems, break attestation-dependent workflows, or cause higher-layer software to fail in ways that are difficult to diagnose quickly
The version thresholds also reveal a common industrial-software challenge: different hardware generations do not converge on the same maintenance timeline. A patch that exists for one branch may still leave another branch waiting on validation, packaging, or a later release cycle. That is why Siemens can honestly say both that “new versions” are available and that it is still preparing “further fix versions” for other products
This is why industrial defenders tend to treat firmware and hardware-adjacent vulnerabilities as platform risk, not isolated defects. The TPM does not live in a vacuum. It supports whatever software stack depends on platform identity, device ownership, or secure boot state, and that can include line-of-business systems that were never designed to assume TPM instability
That matters for industrial teams because firmware and low-level component updates can affect device behavior in ways that ordinary software patches do not. Operators may need to consider boot sequencing, peripheral drivers, automation software compatibility, and whether the vendor’s new build changes anything in the hardware security lifecycle. Fast is important, but validated fast is better in OT
The advisory also raises the familiar problem of version drift. Two devices with the same model name may not be equally vulnerable if they are on different servicing branches. That makes static asset spreadsheets risky unless they are continuously reconciled against the vendor’s fixed-version guidance. Version labels can be misleading if the underlying branch line is not understood properly
User interaction requirements are another place where defenders should be cautious. Many enterprise endpoints rely on human workflows, support tools, or operational scripts that create interactions security teams do not always model well. If a flaw can be triggered when a user handles certain content or performs a routine task, the attack path may be more realistic than the score alone implies
A second thing to watch is whether this disclosure prompts broader review of TPM-dependent workflows. If the issue is not isolated to a single implementation path, organizations may decide to re-check how secure boot, attestation, credential protection, and device onboarding are configured on affected endpoints. That would be the best possible downstream outcome: a narrow vulnerability leading to a wider hardening effort
Source: CISA Siemens TPM 2.0 | CISA
CryptHmacSign helper, with Siemens warning that it can lead to information disclosure or a denial of service of the TPM. Siemens has already published fixed versions for several affected product lines and says additional fix versions are still being prepared, while also recommending compensating controls where a patch is not yet available
 Overview
Overview
The advisory matters because TPM flaws are not ordinary application bugs. A Trusted Platform Module is supposed to harden identity, key storage, secure boot, and device trust flows, so weaknesses in that layer can undermine confidence in the entire machine, even if the immediate symptom looks limited to a crash or a read past the end of memory. Siemens’ description points to a problem in the TCG TPM2.0 reference implementation, not just a single device model quirk, which helps explain why the affected product list spans multiple SIMATIC IPC families and engineering platformsThe exposure is especially relevant in industrial environments because many of the listed systems are used as engineering workstations, embedded industrial PCs, or service laptops that bridge office and operational technology networks. In those contexts, a TPM weakness is not just a local reliability issue; it is part of the device-trust chain that protects firmware state, credentials, and platform attestation. If the TPM becomes unstable or leaks information, defenders have to think beyond the chip and assess what upstream controls may also be weakened
Siemens’ approach in this advisory is also typical of industrial security practice: patch what can be patched, prepare more fixes where needed, and rely on network isolation, protected access, and operational hardening where software remediation is not immediate. That is a pragmatic posture, but it also reflects a persistent reality in OT security: vendors often need time to validate firmware updates across hardware variants, and operators must manage risk in the interim rather than waiting for a perfect outcome
What makes this disclosure more than a routine CVE notice is the breadth of the affected catalog. The advisory names SIMATIC CN 4100, Field PG M5/M6, multiple SIMATIC IPC BX/PX/RW/MD models, several E-series IPCs, ITP1000, and SIPLUS IPC427E. Some product families are affected “all/*,” while others require specific version thresholds such as
<29.01.09, <30.01.10, <32.01.09, <34.01.02, or <21.01.20, indicating a mixed estate of hardware generations and servicing linesWhat Siemens disclosed
Siemens characterizes the issue as a vulnerability that could let an attacker perform an out-of-bounds read by abusing the TPM 2.0 implementation’sCryptHmacSign helper. The core weakness is a lack of validation between the signature scheme and the signature key algorithm, which can result in improper memory access. That aligns with the advisory’s CWE mapping to CWE-125 Out-of-bounds Read and explains the medium-severity score of CVSS 3.1 6.6Why this matters technically
An out-of-bounds read is often underestimated because it does not automatically imply code execution. But in security engineering, information disclosure can be a powerful primitive, especially if the data revealed includes internal state, memory layout, or sensitive material adjacent to the read boundary. A TPM is a particularly sensitive place for such an error because even limited exposure can erode trust in secrets handling and platform integrityThe advisory’s impact statement is also important. Siemens says the flaw could lead to disclosure of information or denial of service of the TPM, not necessarily full system compromise. That narrower impact description should not lull operators into complacency. In industrial contexts, a TPM DoS can still trigger availability problems, break attestation-dependent workflows, or cause higher-layer software to fail in ways that are difficult to diagnose quickly
The key takeaways
- The bug is in the TPM 2.0 reference implementation helper path, not a broad Windows-style software stack.
- Siemens rates the issue medium severity, but the operational impact can still be significant.
- The vulnerability is tied to memory safety and validation logic, which are notoriously subtle to audit.
- The remediation story is uneven across product families, which makes inventory accuracy critical.
- Defensive controls are not optional when patch timing differs by platform family
Affected product families and version boundaries
The affected list is unusually long for a TPM advisory, and that breadth is one of the clearest signals that this is an ecosystem issue rather than a one-off defect. Siemens includes SIMATIC CN 4100, Field PG M5, Field PG M6, IPC227E, IPC277E, IPC627E, IPC647E, IPC677E, IPC847E, ITP1000, and SIPLUS IPC427E as affected in all versions, while several other families are affected only below specific firmware or software build thresholdsFixed versions and patch thresholds
Siemens says vendor fixes are available at or above V21.01.20, V29.01.09, V30.01.10, V32.01.09, and V34.01.02, depending on the product line. That means defenders should not assume a single patch number covers the whole Siemens fleet. Instead, they need to map each device to its own servicing branch and verify the applicable fixed build before declaring the fleet remediatedThe version thresholds also reveal a common industrial-software challenge: different hardware generations do not converge on the same maintenance timeline. A patch that exists for one branch may still leave another branch waiting on validation, packaging, or a later release cycle. That is why Siemens can honestly say both that “new versions” are available and that it is still preparing “further fix versions” for other products
Operational implications
For operators, the practical question is not just “Is the device affected?” but “What role does the device play?” A patchable engineering station that is offline for maintenance is very different from a production-facing industrial PC embedded in a machine cell. The advisory’s structure suggests that asset owners need a device-by-device remediation plan, not a blanket policy update- SIMATIC IPC BX-32A / BX-39A require builds at or above 29.01.09.
- SIMATIC IPC BX-56A / BX-59A require builds at or above 32.01.09.
- SIMATIC IPC MD-57A requires 30.01.10 or later.
- SIMATIC IPC RW-528A / RW-548A require 34.01.02 or later.
- SIMATIC IPC427E / IPC477E / IPC477E PRO / SIPLUS IPC427E require 21.01.20 or later
Why TPM bugs are different
TPM vulnerabilities are often treated as niche, but that view misses how deeply they are woven into modern endpoint trust. A TPM anchors secrets, device identity, measured boot, and sometimes remote attestation. If the TPM is unstable or its memory handling can be abused, the result may be less visible than a browser exploit but potentially more consequential for the host’s trust postureTrust chain pressure
In an enterprise or OT environment, a TPM issue can ripple outward into BIOS controls, credential storage, BitLocker-like workflows, or vendor tooling that expects TPM-backed integrity. Even if the immediate flaw is “only” a read operation, the long-term concern is whether the trust boundary has been weakened enough to make follow-on attacks easier or to complicate forensic confidence later onThis is why industrial defenders tend to treat firmware and hardware-adjacent vulnerabilities as platform risk, not isolated defects. The TPM does not live in a vacuum. It supports whatever software stack depends on platform identity, device ownership, or secure boot state, and that can include line-of-business systems that were never designed to assume TPM instability
Availability matters too
The advisory’s denial-of-service language deserves more attention than it usually gets. In field operations, a TPM DoS may not sound catastrophic until you remember how many management and security functions fail when platform trust components misbehave. A crashed or wedged TPM can mean failed boot checks, provisioning problems, or interruptions to remote administration tasks that are hard to troubleshoot under production pressure- TPM failure can affect boot trust and platform identity.
- Information disclosure can expose internal state even without code execution.
- Availability problems can cascade into maintenance delays and fleet-wide troubleshooting.
- Security tooling may misread the device as healthy while trust primitives are degraded.
- Root-cause analysis becomes harder when the affected layer is below the operating system
Siemens’ remediation strategy
Siemens has already released new versions for several affected products and recommends customers update to the latest versions available for each impacted branch. That is the ideal outcome in any advisory, but the company’s note that further fix versions are still being prepared tells a more realistic story: in industrial ecosystems, patch completion often comes in phases rather than all at onceWhat “update” really means here
In practice, “update to the latest version” is not a generic instruction. It means identifying the exact product branch, confirming the applicable fixed release, testing it against site-specific dependencies, and then rolling it out with appropriate maintenance windows. Because the affected product list spans multiple IPC families, one patch plan may need several version targets, several validation paths, and several rollback decisionsThat matters for industrial teams because firmware and low-level component updates can affect device behavior in ways that ordinary software patches do not. Operators may need to consider boot sequencing, peripheral drivers, automation software compatibility, and whether the vendor’s new build changes anything in the hardware security lifecycle. Fast is important, but validated fast is better in OT
Countermeasures while waiting
Siemens explicitly recommends countermeasures where fixes are not available or not yet available. The advisory’s general guidance is to protect network access to devices, follow Siemens’ operational security guidelines, and use the product manuals as part of the hardening process. Those recommendations are not dramatic, but they are practical and still among the best tools available when patching lags behind disclosure- Restrict direct network reachability to the affected devices.
- Place industrial assets behind firewalls and segment them from business networks.
- Use secure remote access methods when needed, and keep them updated.
- Validate device-specific version eligibility before scheduling maintenance.
- Treat the TPM issue as part of a broader platform-hygiene review
Enterprise impact versus shop-floor impact
For enterprises, the immediate concern is asset inventory. The advisory’s long product list means some organizations may have affected machines in engineering, support, or maintenance roles without realizing those endpoints carry the vulnerable TPM stack. A hidden Field PG or IPC in a spare-parts room can be just as relevant as a production workstation if it is used to touch critical systemsEnterprise exposure
Enterprise defenders will likely need to search beyond the OT network itself. These devices may sit on mixed-purpose segments, connect briefly for maintenance, or travel between sites. If they are used by integrators or external service teams, the exposure path becomes even messier because patch timing and ownership can be split across multiple organizationsThe advisory also raises the familiar problem of version drift. Two devices with the same model name may not be equally vulnerable if they are on different servicing branches. That makes static asset spreadsheets risky unless they are continuously reconciled against the vendor’s fixed-version guidance. Version labels can be misleading if the underlying branch line is not understood properly
Shop-floor exposure
On the shop floor, availability is usually the dominant concern. Operators care about uptime, but they also care about not interrupting control loops, batch operations, or maintenance schedules. A TPM-related defect may seem distant from production, yet if the device acts as a gateway, engineering terminal, or support appliance, a patch delay can leave an attack surface sitting in plain sight- Enterprises should focus on inventory, ownership, and version mapping.
- Shop-floor teams should focus on maintenance windows and operational continuity.
- External service partners may need to be included in the remediation workflow.
- Device roles matter as much as device names.
- Industrial segmentation can reduce exposure while fixes are staged
Why the CVSS score may understate the practical risk
The listed CVSS 3.1 score of 6.6 is medium severity, which is sensible given the advisory’s stated impact and attack conditions. But CVSS is a standardized measurement, not a full operational risk assessment. In industrial settings, a medium score can still represent a high-priority issue if the affected system is difficult to isolate, critical to production, or slow to patchLocal access does not always mean low risk
The advisory’s vector shows local access, low complexity, low privileges, and user interaction required. That combination can sound reassuring at first glance, but it also describes a situation where an attacker might only need a foothold on a machine that is already inside a trusted network. In industrial environments, “local” is often a much bigger problem than the term suggests because local footholds can be gateway footholdsUser interaction requirements are another place where defenders should be cautious. Many enterprise endpoints rely on human workflows, support tools, or operational scripts that create interactions security teams do not always model well. If a flaw can be triggered when a user handles certain content or performs a routine task, the attack path may be more realistic than the score alone implies
Impact in layered environments
The biggest discrepancy between score and consequence often appears in layered systems. A TPM crash may look minor until it affects a boot process, a secure enrollment workflow, or a service that assumes TPM availability for protected operations. That is why context beats score in critical manufacturing and industrial computing- Medium severity does not mean low operational importance.
- Local attack conditions still matter in segmented networks.
- User-interaction requirements may map to ordinary maintenance workflows.
- Industrial dependencies can multiply the downstream effects of a single TPM fault.
- The most serious outcome may be workflow disruption, not just memory disclosure
Strengths and Opportunities
The good news is that Siemens has already done the most important thing a vendor can do in a case like this: it acknowledged the flaw, mapped affected products, and published fixed versions for several branches while continuing to work on the remaining ones. That gives operators a concrete remediation path instead of forcing them to rely on vague guidance or third-party speculation. It also reinforces the value of coordinated disclosure in industrial security, where accurate branch-level data is often the difference between quick recovery and prolonged exposure- Siemens has clear affected-product mapping.
- Fixed versions are already available for multiple branches.
- The advisory gives defenders an actionable version threshold model.
- The flaw’s class is well understood, which helps incident responders reason about impact.
- Compensating controls are explicitly recommended where patches lag.
- The disclosure supports better asset hygiene across mixed Siemens fleets.
- Industrial teams can use the event to review broader device-trust dependencies
Risks and Concerns
The main concern is that the affected footprint is broad and the remediation picture is uneven. When some device families are already fixed and others are still waiting on future releases, organizations can end up with a false sense of closure if they only check one part of the fleet. Another concern is that TPM defects are easy to underestimate because the immediate symptom is “just” a read or a DoS, even though the platform-trust consequences can be more subtle and persistent- Some branches still need future fix versions.
- Affected devices may be hidden in maintenance or engineering roles.
- TPM problems can be underestimated because the exploit path is not flashy.
- Patch validation may take time in operational environments.
- Network segmentation gaps can amplify the risk of local exploitation.
- Mixed-version fleets can leave remediation incomplete by accident.
- Trust-chain effects may extend beyond the TPM itself
Looking Ahead
The next important step is seeing whether Siemens completes the remaining fix releases on schedule and whether customers can move from advisory response to sustained fleet normalization. For many industrial organizations, the real work starts after the bulletin: inventory confirmation, maintenance scheduling, compensating controls, and validation that the patch does not disturb production processes. That is especially true when multiple product families map to different fixed versions and different operational ownersA second thing to watch is whether this disclosure prompts broader review of TPM-dependent workflows. If the issue is not isolated to a single implementation path, organizations may decide to re-check how secure boot, attestation, credential protection, and device onboarding are configured on affected endpoints. That would be the best possible downstream outcome: a narrow vulnerability leading to a wider hardening effort
What to watch next
- Release of the remaining Siemens fix versions.
- Confirmation that patched branches are consistent across all IPC families.
- Any guidance changes for devices still awaiting remediation.
- Internal audits of TPM-dependent security and boot workflows.
- Evidence of exploitation or operational disruption in the field, if any emerges.
Source: CISA Siemens TPM 2.0 | CISA