Siemens and CISA warned on May 14, 2026, that CVE-2025-40833 affects a broad range of Siemens industrial networking, controller, drive, power, and automation devices worldwide, allowing unauthenticated network attackers to crash affected systems with specially crafted IPv4 requests. The advisory is not a cinematic “plant takeover” bug; it is a blunt availability failure in the connective tissue of industrial operations. That distinction matters because downtime, manual recovery, and patch sequencing are often more expensive than exploit sophistication. The uncomfortable lesson is that industrial security is still won or lost in the mundane places: firmware baselines, routed access, exposed management paths, and old devices that no one wants to reboot.
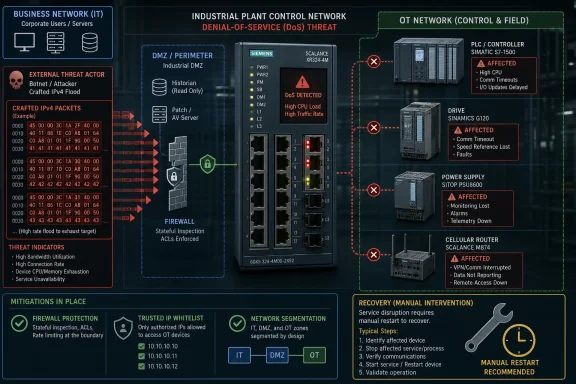
CVE-2025-40833 is a null pointer dereference vulnerability, a class of flaw that sounds almost pedestrian to software people and deeply consequential to operations teams. In plain terms, affected Siemens devices can mishandle crafted IPv4 traffic badly enough that the system enters a denial-of-service condition. Siemens says recovery requires a manual restart.
That last sentence is the heart of the story. A crash in an office application is irritation; a crash in a switch, router, PLC-adjacent communications device, or industrial power module can become a maintenance window, a truck roll, a production interruption, or a safety review. Industrial networks are built around predictability, and this bug attacks predictability rather than secrecy.
The vulnerability carries a CVSS 3.1 base score of 7.5, rated high. The vector is the classic availability nightmare: network reachable, low attack complexity, no privileges, no user interaction, no confidentiality or integrity impact, but high availability impact. That makes it easy to underestimate if your patch process is driven by data theft risk, and easy to overstate if your threat model assumes every high CVSS network bug is a route to full compromise.
It is neither trivial nor apocalyptic. It is the sort of bug that punishes weak segmentation, stale inventories, and the habit of treating industrial Ethernet as if it were a closed world.
This breadth suggests the vulnerable behavior sits in common network handling code or shared platform components rather than in one niche feature. For defenders, that matters because the inventory exercise cannot stop at the obvious edge routers. The affected population includes devices that may be treated as infrastructure, automation endpoints, power components, and legacy control hardware.
The advisory also divides the Siemens estate into several practical buckets. Some devices have firmware updates available, including version targets such as V10.2, V8.3, V6.6.0, V3.2.0, V2.0.0, and V1.3 depending on the product line. Other devices are listed as affected across all versions, with no fix available or no fix planned.
That is the reality of operational technology patching in miniature. A Windows admin can often think in Patch Tuesday cycles; an OT engineer may be staring at product generations, certification constraints, obsolete hardware, production seasons, and a vendor matrix that says “update this, isolate that, replace this eventually, and mitigate the rest forever.”
Many SCALANCE X-series switches, SIMATIC S7-300 and S7-400 CPUs, SINAMICS drives, SITOP devices, and other product families appear in the affected set as all-version cases. Some of these are exactly the kind of gear organizations expect to run for a decade or more. The hardware may be embedded in validated machinery, locked into vendor support contracts, or tied to process-control assumptions that make a firmware change feel riskier than the CVE.
That is why “patch now” is not a complete answer. It is the right answer for devices with available fixes and acceptable maintenance windows, but it does not solve the installed base problem. For devices without fixes, the security control moves outward: restrict who can send traffic, harden routing paths, disable unnecessary ports, and create compensating architecture around a component that cannot be made fully resilient by firmware alone.
This is where industrial cybersecurity becomes less like endpoint management and more like civil engineering. You do not simply fix every weak beam overnight. You identify load paths, reduce exposure, add barriers, monitor stress, and plan the replacement without pretending the replacement has already happened.
The advisory’s recommended mitigations reflect that. Siemens advises restricting access to affected systems to trusted IP addresses only. For certain CPU scenarios, Siemens recommends disabling Ethernet ports on the CPU and using a communications module instead. CISA repeats its familiar industrial control system guidance: minimize network exposure, avoid internet accessibility, place control networks and remote devices behind firewalls, separate them from business networks, and use secure remote access methods when remote access is unavoidable.
None of that is novel. That is precisely the problem. The fix for many ICS vulnerabilities is the same architectural hygiene we have been discussing for years, because the exploit path so often depends on whether an attacker can touch a device that was never meant to be touched from a broad network zone.
IPv4 itself is not exotic. It is the default language of most industrial and enterprise networks. A crafted request does not require the attacker to defeat an authentication system if the vulnerable parser or packet handler is reachable first. In operational environments, that puts special weight on firewalls, access control lists, industrial DMZs, jump hosts, routing discipline, and the boring art of knowing what talks to what.
This is why availability bugs in industrial devices deserve a different reading than availability bugs in consumer gear. A denial-of-service condition can mean loss of visibility, loss of network connectivity, interruption of automation communication, degraded process control, or a forced maintenance response. Even where safety systems remain separate and intact, operations teams may need to slow, stop, or inspect equipment before returning to normal.
The temptation is to ask whether this vulnerability enables ransomware, remote code execution, or data theft. Those are valid questions, but they are not the only questions. For a manufacturing line, water facility, energy site, transportation hub, or process plant, forced downtime can be the business impact by itself.
That is also why attackers do not always need elegance. A packet that knocks over a device and demands hands-on recovery can be attractive in extortion, disruption, sabotage, or diversion scenarios. The difference between “no code execution” and “no consequence” is enormous.
That distinction matters because industrial operators often receive vulnerability intelligence through different channels: vendor portals, national CERT feeds, managed security providers, sector ISACs, integrator bulletins, and government advisories. CISA’s republication gives the issue a U.S. critical infrastructure signal, even though Siemens is headquartered in Germany and the affected deployments are worldwide.
The advisory identifies critical manufacturing as the primary critical infrastructure sector. That is a broad bucket, and it should be. Siemens industrial gear is not confined to one narrow vertical. SCALANCE, SIMATIC, SINAMICS, SITOP, and related product lines are used across manufacturing and adjacent industrial environments where automation, networking, power, and motion control intersect.
For WindowsForum readers, the Windows angle is indirect but important. Many Windows administrators support the business networks, jump servers, engineering workstations, domain services, remote access systems, backup platforms, and monitoring tools that border OT networks. When an ICS advisory says “restrict access to trusted IPs,” the implementation often lands partly on the same people who manage Windows firewalls, VPN posture, Active Directory groups, privileged access workflows, and endpoint segmentation policies.
For devices with available updates, the version thresholds are the immediate targets. SCALANCE M and related lines have updates around V8.3. Several SCALANCE W families point to V6.6.0. WAM, WUM, WAB, and WUB families point to V3.2.0. SIMATIC CFU products point to V2.0.0. SIMATIC ET 200SP HA IM155-6 PN points to V1.3. S7-410 V10 systems point to V10.2, while S7-410 V8 systems point to V8.3.
Those version numbers are not interchangeable. They are product-line-specific gates, and treating them as a single “Siemens firmware update” would be operationally reckless. Firmware in OT has dependencies, release notes, compatibility constraints, and sometimes validation requirements that differ sharply from an enterprise software update.
The real work is sequencing. Security teams want exposure reduced quickly; operations teams want stability preserved; engineering teams want compatibility confirmed; management wants a risk statement that does not read like a ransom note. A good response plan translates the advisory into zones, device roles, firmware eligibility, maintenance windows, and compensating controls for assets that cannot be patched.
Legacy devices with “no fix planned” effectively become managed exceptions. They can remain in service, but only if the organization is honest about the new burden. Every unmanaged route to those devices becomes a risk. Every poorly controlled remote access path becomes more consequential. Every flat network segment becomes a larger blast radius.
There is a familiar pattern here. Vendors disclose a vulnerability in widely deployed OT equipment. Some firmware updates arrive. Some product lines age out. Asset owners patch what they can, isolate what they cannot, and document risk for the rest. Then the next advisory arrives, and the process repeats.
That cycle is not failure by itself. Industrial equipment cannot be replaced at the speed of browser updates. But pretending that unsupported devices are merely “temporarily unpatched” is failure. At some point, a compensating control becomes the real security boundary, and it must be engineered and monitored with the same seriousness as a patch.
That means an ICS denial-of-service bug can become a Windows team problem without ever exploiting Windows. If an attacker compromises a business endpoint and pivots into a poorly segmented plant network, the affected Siemens device does not care that the original foothold was a phishing email or a stolen VPN token. It sees crafted IPv4 traffic from a reachable host.
The classic IT/OT boundary is supposed to prevent exactly that. In practice, boundaries accumulate exceptions: vendor support tunnels, temporary firewall openings, engineering workstation dual-homing, unmanaged switches, shared credentials, and remote desktop paths that outlive the project that created them. CVE-2025-40833 is a useful forcing function for reviewing those exceptions.
Windows admins should not read this as “go patch Siemens gear.” They should read it as “prove that compromised Windows assets cannot freely reach Siemens industrial devices.” That is a segmentation, identity, firewall, logging, and remote access question — and those are very much in the WindowsForum wheelhouse.
CVE-2025-40833 does not claim to leak secrets or alter logic. It threatens to interrupt operation. For a plant manager, a network engineer, or an OT security lead, that may be more urgent than a technically fancier vulnerability with less plausible reachability.
The advisory also underlines why “air gap” rhetoric remains dangerous. Many industrial systems are not truly isolated, and even those with limited connectivity often have maintenance, monitoring, vendor, or enterprise data paths. The attacker does not need broad internet exposure if a compromised internal system can send the right traffic.
Availability defense is therefore layered. Patch where possible. Restrict source IPs. Block unnecessary routes. Monitor for malformed or anomalous traffic. Keep recovery procedures current. Know which devices require hands-on restart. Ensure spares, backups, and configuration exports exist. Test the plan before the emergency.
Those questions sound simple until an advisory names hundreds of variants. The list includes regional models, ruggedized variants, SIPLUS-branded versions, legacy switches, access points, routers, PLC families, drive components, and power systems. A generic CMDB entry will not carry the response.
This is where asset inventory becomes security infrastructure. Passive discovery, configuration management, procurement records, network diagrams, and maintenance logs all need to converge. If the first serious inventory effort begins after the advisory, the organization is already behind.
There is also a governance lesson for risk acceptance. “No fix available” should not mean “no action required.” It should trigger a documented control decision: isolate, restrict, monitor, replace, or accept with explicit business sign-off. Silent acceptance is how old vulnerabilities become permanent architecture.
The forward path is not mystery work: update where Siemens has shipped fixes, constrain traffic where it has not, and stop treating legacy industrial connectivity as an acceptable unknown. The next advisory will have a different CVE and a different packet shape, but the organizations that come out ahead will be the same ones that use this one to tighten inventory, segmentation, and recovery before an attacker turns a crafted IPv4 request into an unscheduled outage.
Source: CISA Siemens Industrial Devices | CISA
 A Denial-of-Service Bug Becomes a Plant-Floor Problem
A Denial-of-Service Bug Becomes a Plant-Floor Problem
CVE-2025-40833 is a null pointer dereference vulnerability, a class of flaw that sounds almost pedestrian to software people and deeply consequential to operations teams. In plain terms, affected Siemens devices can mishandle crafted IPv4 traffic badly enough that the system enters a denial-of-service condition. Siemens says recovery requires a manual restart.That last sentence is the heart of the story. A crash in an office application is irritation; a crash in a switch, router, PLC-adjacent communications device, or industrial power module can become a maintenance window, a truck roll, a production interruption, or a safety review. Industrial networks are built around predictability, and this bug attacks predictability rather than secrecy.
The vulnerability carries a CVSS 3.1 base score of 7.5, rated high. The vector is the classic availability nightmare: network reachable, low attack complexity, no privileges, no user interaction, no confidentiality or integrity impact, but high availability impact. That makes it easy to underestimate if your patch process is driven by data theft risk, and easy to overstate if your threat model assumes every high CVSS network bug is a route to full compromise.
It is neither trivial nor apocalyptic. It is the sort of bug that punishes weak segmentation, stale inventories, and the habit of treating industrial Ethernet as if it were a closed world.
Siemens’ Blast Radius Is Really an Architecture Map
The affected list is sprawling: SCALANCE industrial switches and routers, wireless access devices, RUGGEDCOM cellular routers, SIMATIC controllers and distributed I/O components, SINAMICS drives, SINUMERIK CNC systems, SITOP power supplies and UPS units, SIMIT units, SIPLUS variants, and IE/PB link devices. That is not a neat product family advisory. It is a cross-section of the industrial network stack.This breadth suggests the vulnerable behavior sits in common network handling code or shared platform components rather than in one niche feature. For defenders, that matters because the inventory exercise cannot stop at the obvious edge routers. The affected population includes devices that may be treated as infrastructure, automation endpoints, power components, and legacy control hardware.
The advisory also divides the Siemens estate into several practical buckets. Some devices have firmware updates available, including version targets such as V10.2, V8.3, V6.6.0, V3.2.0, V2.0.0, and V1.3 depending on the product line. Other devices are listed as affected across all versions, with no fix available or no fix planned.
That is the reality of operational technology patching in miniature. A Windows admin can often think in Patch Tuesday cycles; an OT engineer may be staring at product generations, certification constraints, obsolete hardware, production seasons, and a vendor matrix that says “update this, isolate that, replace this eventually, and mitigate the rest forever.”
“All Versions” Is the Phrase That Should Stop the Meeting
The most sobering entries are not the ones with a clean “update to version X or later” instruction. They are the “all versions” entries, especially where the advisory indicates no current fix or no planned fix. In enterprise IT, that often triggers a procurement conversation. In industrial environments, it may trigger a multi-year modernization plan.Many SCALANCE X-series switches, SIMATIC S7-300 and S7-400 CPUs, SINAMICS drives, SITOP devices, and other product families appear in the affected set as all-version cases. Some of these are exactly the kind of gear organizations expect to run for a decade or more. The hardware may be embedded in validated machinery, locked into vendor support contracts, or tied to process-control assumptions that make a firmware change feel riskier than the CVE.
That is why “patch now” is not a complete answer. It is the right answer for devices with available fixes and acceptable maintenance windows, but it does not solve the installed base problem. For devices without fixes, the security control moves outward: restrict who can send traffic, harden routing paths, disable unnecessary ports, and create compensating architecture around a component that cannot be made fully resilient by firmware alone.
This is where industrial cybersecurity becomes less like endpoint management and more like civil engineering. You do not simply fix every weak beam overnight. You identify load paths, reduce exposure, add barriers, monitor stress, and plan the replacement without pretending the replacement has already happened.
The IPv4 Detail Is Small, but It Tells Defenders Where to Look
The vulnerable condition is triggered while processing specially crafted IPv4 requests. That detail should focus defensive attention on network paths rather than credentials, phishing, or local access. This is an availability bug exposed through traffic handling, which means reachability is the practical exploit precondition.The advisory’s recommended mitigations reflect that. Siemens advises restricting access to affected systems to trusted IP addresses only. For certain CPU scenarios, Siemens recommends disabling Ethernet ports on the CPU and using a communications module instead. CISA repeats its familiar industrial control system guidance: minimize network exposure, avoid internet accessibility, place control networks and remote devices behind firewalls, separate them from business networks, and use secure remote access methods when remote access is unavoidable.
None of that is novel. That is precisely the problem. The fix for many ICS vulnerabilities is the same architectural hygiene we have been discussing for years, because the exploit path so often depends on whether an attacker can touch a device that was never meant to be touched from a broad network zone.
IPv4 itself is not exotic. It is the default language of most industrial and enterprise networks. A crafted request does not require the attacker to defeat an authentication system if the vulnerable parser or packet handler is reachable first. In operational environments, that puts special weight on firewalls, access control lists, industrial DMZs, jump hosts, routing discipline, and the boring art of knowing what talks to what.
Manual Restart Turns a Packet Bug Into an Operations Event
Manual recovery changes the severity calculus. If a device can crash and self-recover cleanly, the incident may appear as a blip. If it requires a manual restart, the incident becomes a process event, especially when the device sits in a cabinet, a remote substation, a production cell, or a location with strict safety procedures.This is why availability bugs in industrial devices deserve a different reading than availability bugs in consumer gear. A denial-of-service condition can mean loss of visibility, loss of network connectivity, interruption of automation communication, degraded process control, or a forced maintenance response. Even where safety systems remain separate and intact, operations teams may need to slow, stop, or inspect equipment before returning to normal.
The temptation is to ask whether this vulnerability enables ransomware, remote code execution, or data theft. Those are valid questions, but they are not the only questions. For a manufacturing line, water facility, energy site, transportation hub, or process plant, forced downtime can be the business impact by itself.
That is also why attackers do not always need elegance. A packet that knocks over a device and demands hands-on recovery can be attractive in extortion, disruption, sabotage, or diversion scenarios. The difference between “no code execution” and “no consequence” is enormous.
CISA’s Republication Makes the Advisory Harder to Ignore
CISA’s version is a republication of Siemens ProductCERT advisory SSA-392349 through the Common Security Advisory Framework. The agency’s role here is visibility and distribution rather than original discovery. Siemens ProductCERT reported the vulnerability to CISA, and the CISA advisory explicitly notes that the republished content is provided as-is from the vendor advisory.That distinction matters because industrial operators often receive vulnerability intelligence through different channels: vendor portals, national CERT feeds, managed security providers, sector ISACs, integrator bulletins, and government advisories. CISA’s republication gives the issue a U.S. critical infrastructure signal, even though Siemens is headquartered in Germany and the affected deployments are worldwide.
The advisory identifies critical manufacturing as the primary critical infrastructure sector. That is a broad bucket, and it should be. Siemens industrial gear is not confined to one narrow vertical. SCALANCE, SIMATIC, SINAMICS, SITOP, and related product lines are used across manufacturing and adjacent industrial environments where automation, networking, power, and motion control intersect.
For WindowsForum readers, the Windows angle is indirect but important. Many Windows administrators support the business networks, jump servers, engineering workstations, domain services, remote access systems, backup platforms, and monitoring tools that border OT networks. When an ICS advisory says “restrict access to trusted IPs,” the implementation often lands partly on the same people who manage Windows firewalls, VPN posture, Active Directory groups, privileged access workflows, and endpoint segmentation policies.
The Patch Matrix Rewards Inventory, Not Heroics
The practical first step is not downloading firmware; it is proving what you own. The affected list is long enough that product names alone are insufficient. Part numbers, regional variants, hardware revisions, firmware trains, and SIPLUS equivalents matter. A plant with “SCALANCE wireless” or “S7-1500 CPUs” in a spreadsheet does not yet have a usable vulnerability response.For devices with available updates, the version thresholds are the immediate targets. SCALANCE M and related lines have updates around V8.3. Several SCALANCE W families point to V6.6.0. WAM, WUM, WAB, and WUB families point to V3.2.0. SIMATIC CFU products point to V2.0.0. SIMATIC ET 200SP HA IM155-6 PN points to V1.3. S7-410 V10 systems point to V10.2, while S7-410 V8 systems point to V8.3.
Those version numbers are not interchangeable. They are product-line-specific gates, and treating them as a single “Siemens firmware update” would be operationally reckless. Firmware in OT has dependencies, release notes, compatibility constraints, and sometimes validation requirements that differ sharply from an enterprise software update.
The real work is sequencing. Security teams want exposure reduced quickly; operations teams want stability preserved; engineering teams want compatibility confirmed; management wants a risk statement that does not read like a ransom note. A good response plan translates the advisory into zones, device roles, firmware eligibility, maintenance windows, and compensating controls for assets that cannot be patched.
Legacy Gear Is Where the Risk Becomes Permanent
The hardest part of the advisory is not that Siemens has many affected products. It is that many affected products live in places where replacement is slow and downtime is expensive. The industrial world has always run on long lifecycles, and cybersecurity is now colliding with that economic model.Legacy devices with “no fix planned” effectively become managed exceptions. They can remain in service, but only if the organization is honest about the new burden. Every unmanaged route to those devices becomes a risk. Every poorly controlled remote access path becomes more consequential. Every flat network segment becomes a larger blast radius.
There is a familiar pattern here. Vendors disclose a vulnerability in widely deployed OT equipment. Some firmware updates arrive. Some product lines age out. Asset owners patch what they can, isolate what they cannot, and document risk for the rest. Then the next advisory arrives, and the process repeats.
That cycle is not failure by itself. Industrial equipment cannot be replaced at the speed of browser updates. But pretending that unsupported devices are merely “temporarily unpatched” is failure. At some point, a compensating control becomes the real security boundary, and it must be engineered and monitored with the same seriousness as a patch.
The Windows-Adjacent Risk Lives at the Boundary
Windows estates often form the soft connective layer around industrial systems. Engineering laptops run vendor tools. HMIs and historians may sit on Windows Server or Windows client builds. Remote access often terminates through Windows-managed identity. File shares, jump boxes, patch repositories, monitoring dashboards, and backup systems all touch the OT support workflow.That means an ICS denial-of-service bug can become a Windows team problem without ever exploiting Windows. If an attacker compromises a business endpoint and pivots into a poorly segmented plant network, the affected Siemens device does not care that the original foothold was a phishing email or a stolen VPN token. It sees crafted IPv4 traffic from a reachable host.
The classic IT/OT boundary is supposed to prevent exactly that. In practice, boundaries accumulate exceptions: vendor support tunnels, temporary firewall openings, engineering workstation dual-homing, unmanaged switches, shared credentials, and remote desktop paths that outlive the project that created them. CVE-2025-40833 is a useful forcing function for reviewing those exceptions.
Windows admins should not read this as “go patch Siemens gear.” They should read it as “prove that compromised Windows assets cannot freely reach Siemens industrial devices.” That is a segmentation, identity, firewall, logging, and remote access question — and those are very much in the WindowsForum wheelhouse.
Availability Deserves the Same Discipline as Data Protection
Security programs often prioritize confidentiality because breaches are visible, regulated, and reputationally painful. Industrial environments invert the equation. Availability is not a third column on a risk matrix; it is often the business.CVE-2025-40833 does not claim to leak secrets or alter logic. It threatens to interrupt operation. For a plant manager, a network engineer, or an OT security lead, that may be more urgent than a technically fancier vulnerability with less plausible reachability.
The advisory also underlines why “air gap” rhetoric remains dangerous. Many industrial systems are not truly isolated, and even those with limited connectivity often have maintenance, monitoring, vendor, or enterprise data paths. The attacker does not need broad internet exposure if a compromised internal system can send the right traffic.
Availability defense is therefore layered. Patch where possible. Restrict source IPs. Block unnecessary routes. Monitor for malformed or anomalous traffic. Keep recovery procedures current. Know which devices require hands-on restart. Ensure spares, backups, and configuration exports exist. Test the plan before the emergency.
The Siemens Advisory Is a Test of Governance
The organizations that handle this well will not be the ones that panic fastest. They will be the ones that can answer basic questions quickly. Which affected product families are deployed? Which firmware versions are running? Which assets are reachable from enterprise networks, remote access networks, wireless segments, vendor VPNs, and engineering stations? Which devices can be updated in the next maintenance window, and which require architectural mitigation?Those questions sound simple until an advisory names hundreds of variants. The list includes regional models, ruggedized variants, SIPLUS-branded versions, legacy switches, access points, routers, PLC families, drive components, and power systems. A generic CMDB entry will not carry the response.
This is where asset inventory becomes security infrastructure. Passive discovery, configuration management, procurement records, network diagrams, and maintenance logs all need to converge. If the first serious inventory effort begins after the advisory, the organization is already behind.
There is also a governance lesson for risk acceptance. “No fix available” should not mean “no action required.” It should trigger a documented control decision: isolate, restrict, monitor, replace, or accept with explicit business sign-off. Silent acceptance is how old vulnerabilities become permanent architecture.
The Siemens Packet That Should Rewrite the Maintenance Calendar
The most concrete response is a disciplined triage sprint, not a theoretical debate about whether denial-of-service bugs are “critical enough.” This advisory gives defenders enough specificity to act: one CVE, one attack pattern, a high availability impact, affected product families, firmware targets for many devices, and clear mitigations for the rest.- Organizations should identify affected Siemens devices by exact product family, part number, firmware version, and role in the process network.
- Devices with available Siemens firmware fixes should be scheduled for update after compatibility checks and operational impact review.
- Devices without fixes should be isolated with trusted-source restrictions, firewall rules, and removal of unnecessary network paths.
- Windows-managed remote access, engineering workstations, jump servers, and vendor support routes should be reviewed as possible paths to the affected devices.
- Recovery plans should assume that exploitation may require manual restart, not merely automatic service recovery.
- Unsupported or no-fix devices should be treated as modernization candidates rather than indefinite exceptions.
The forward path is not mystery work: update where Siemens has shipped fixes, constrain traffic where it has not, and stop treating legacy industrial connectivity as an acceptable unknown. The next advisory will have a different CVE and a different packet shape, but the organizations that come out ahead will be the same ones that use this one to tighten inventory, segmentation, and recovery before an attacker turns a crafted IPv4 request into an unscheduled outage.
Source: CISA Siemens Industrial Devices | CISA