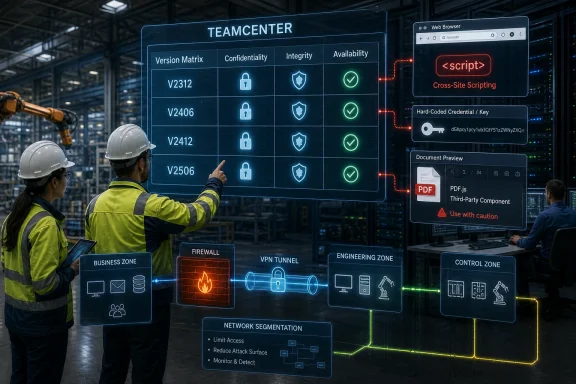
Siemens and CISA disclosed on May 14, 2026, that Siemens Teamcenter versions V2312, V2406, V2412, and V2506 are affected by three vulnerabilities that can expose confidentiality, integrity, and availability, with Siemens recommending updates to fixed maintenance releases across affected branches. The advisory is not a flashy emergency bulletin, but it is exactly the kind of notice that industrial IT teams ignore at their peril. Teamcenter is not just another business application; it is often the system of record for product lifecycle data, engineering workflows, supplier collaboration, and manufacturing handoff. When that layer carries web flaws, embedded third-party component risk, and hard-coded credential exposure, the story is less about a single patch and more about how deeply software supply chains now sit inside industrial operations.
The affected product is Siemens Teamcenter, a product lifecycle management platform used to connect engineering, manufacturing, documentation, and process data across organizations. In plain English, it is one of the systems companies use to know what they are building, how it changes, who approved it, and how those decisions move from design into production.
That context matters because the advisory lands in the “critical manufacturing” sector, not merely in generic enterprise software. Teamcenter may be deployed as an internal application, but the information it manages is often strategic: product designs, bills of materials, change records, supplier data, release workflows, and supporting documentation. A vulnerability in that environment does not have to shut down a factory to matter; it only has to undermine trust in the data that factory depends on.
The reported maximum severity is substantial rather than catastrophic. Siemens lists a CVSS v3.1 base score of 7.5 and a CVSS v4.0 base score of 8.7 for the advisory overall. That places the issue in the uncomfortable middle zone where executives may not hear “drop everything,” but security teams should hear “schedule this like it matters.”
CISA’s republication adds visibility but also a useful caveat. The agency says its page is a verbatim conversion of Siemens’ CSAF advisory and is provided as-is, which means Siemens ProductCERT remains the primary technical source. That distinction is important in ICS security: CISA amplifies, but the vendor owns the product-specific detail.
For newer release lines, the shape is simpler. Teamcenter V2412 needs V2412.0009 or later for CVE-2026-33862 and CVE-2026-33893. Teamcenter V2506 needs V2506.0005 or later for those same two vulnerabilities. Teamcenter V2512 is listed as not affected because the vulnerable component is not present.
That last point is easy to skim past, but it says something revealing about modern enterprise application security. Siemens did not simply say “latest version good, old versions bad.” It said a vulnerable component is absent from V2512, which suggests that some architectural or dependency change removed the exposure rather than merely patching it in place.
For administrators, this means inventory comes before remediation. It is not enough to ask, “Do we run Teamcenter?” The practical question is which branch, which maintenance level, which components, and which exposure paths exist in the environment. In mature shops, that should be answerable from configuration management data; in less mature ones, this advisory may trigger the usual archaeological dig through app owners, integrators, and change windows.
The staggered version thresholds also create a familiar maintenance headache. An organization sitting on V2312.0008 may be exposed to all three CVEs. One on V2312.0010 may have cleared the PDF.js-related issue but still need the later fix for the 2026 flaws. The advisory is a reminder that “we patched Teamcenter last quarter” is not a security state; it is a conversation starter.
Cross-site scripting is sometimes treated as a solved or low-drama class of bug because the industry has talked about it for decades. That complacency is a mistake. In authenticated enterprise applications, XSS can be especially useful because the victim is already inside the perimeter, already logged into the application, and often already authorized to see data the attacker wants.
The advisory’s scoring reflects that tension. CVE-2026-33862 requires low privileges and user interaction, but it carries high confidentiality and integrity impact in the CVSS v3.1 vector. That combination tells a familiar story: an attacker may need a foothold or an application account, but once malicious content reaches the right viewer, the browser becomes a bridge into sensitive workflow context.
For Windows-heavy engineering environments, this is particularly relevant because the endpoint and the browser remain the daily interface to industrial software. A Teamcenter user may be an engineer, a release manager, a supplier coordinator, or an administrator moving through documents, dashboards, and records. The browser session is where application permissions meet human habit.
This is why XSS in business-critical applications should not be dismissed as “just JavaScript.” If the application is trusted enough to approve product changes, publish technical data, or coordinate suppliers, then injected script is not a nuisance. It is a way to borrow the user’s position inside a workflow.
Hard-coded credentials and keys are not just implementation errors; they are design shortcuts with long tails. They create secrets that cannot be rotated cleanly, cannot be scoped dynamically, and often cannot be monitored with the same rigor as identity-provider credentials or managed secrets. Once exposed, they tend to be exposed everywhere the affected version exists.
The advisory does not say that the key grants total system compromise, and it would be irresponsible to inflate the claim beyond what Siemens published. But the concern is clear enough. A credential-like artifact embedded in application code changes the attacker’s problem from “defeat the access control model” to “find and reuse what the software already trusts.”
That distinction matters for defenders. With normal credential compromise, incident response can disable an account, reset a password, revoke a token, or rotate a secret in a vault. With a hard-coded key inside a vendor application, the remedy is usually a software update because the trust mechanism itself lives in the product.
This is also where industrial software often collides with enterprise security expectations. Modern IT teams have spent years pushing toward managed identities, short-lived tokens, hardware-backed keys, and auditable secret stores. Legacy patterns still exist in complex platforms, and when they surface inside systems that govern production knowledge, the operational response is rarely as simple as “change the password.”
This is the reality of modern application risk: a vulnerability does not stay neatly confined to the product where it first made headlines. PDF rendering, image processing, compression libraries, document viewers, web frameworks, and JavaScript packages migrate into enterprise platforms. Months or years later, a known flaw can reappear in a very different operational setting.
For Teamcenter, document handling is not a peripheral convenience. Engineering and manufacturing workflows are document-heavy by nature. PDFs can include specifications, drawings, procedures, compliance records, supplier documents, test reports, and release packages. A document viewer embedded in a PLM workflow is exactly the sort of place where a third-party component becomes part of the security boundary.
There is also a WindowsForum angle here. Many administrators have learned to patch browsers aggressively, but they may not think of browser-adjacent components inside server applications with the same urgency. If PDF.js is bundled into a vendor platform, updating Firefox on endpoints does not necessarily update the copy inside Teamcenter.
That is the broader supply-chain lesson. Dependency risk is not solved by patching the famous upstream product. It is solved when every downstream product that embedded the vulnerable component updates, ships, and gets deployed. In industrial IT, that chain often moves more slowly than the public CVE conversation.
The challenge is that Teamcenter often sits in the borderland between engineering IT and operational technology. It may not be a PLC, HMI, or historian, but it supports the processes that feed manufacturing. It may integrate with ERP, CAD, MES, identity systems, file stores, visualization tools, and supplier portals. Drawing the network boundary around it is not always straightforward.
That is why the advisory’s risk cannot be measured only by whether Teamcenter is internet-facing. A non-internet-facing application can still be reachable by thousands of internal users, contractors, engineers on VPN, build systems, data integration jobs, and service accounts. In many intrusions, “internal only” is not a defense; it is a description of where the attacker goes after the first compromise.
Segmentation still matters, but it must be honest segmentation. If Teamcenter has broad trust relationships across engineering, manufacturing, and business networks, then it deserves the same threat modeling attention as any crown-jewel system. Firewalls help only when the access model they enforce matches the sensitivity of the application.
The VPN caveat is equally important. CISA notes that VPNs themselves can have vulnerabilities and must be kept current. That is not boilerplate anymore; remote access infrastructure has become a favorite target precisely because it offers a path into systems that organizations believe are safely tucked away.
Integrity deserves special attention. In many security programs, confidentiality gets the budget because stolen data is easy to explain. But in PLM, a subtle integrity failure can be just as damaging. If users cannot trust that a design record, approval trail, or manufacturing instruction is authentic, the business impact can cascade into delays, rework, compliance problems, and safety reviews.
That does not mean these specific vulnerabilities are known to enable silent product sabotage. Siemens has not said that, and neither has CISA. The point is that the affected application lives in a domain where data correctness has operational weight. A bug class that might be annoying in a generic intranet portal can become serious when the portal governs engineering truth.
Attackers understand that distinction. Ransomware crews want business disruption. Espionage actors want intellectual property. Insider-threat scenarios often revolve around access to design and process knowledge. A PLM platform can be attractive to all three, even if the vulnerability path differs.
For Windows administrators, the lesson is to treat Teamcenter not as “the Siemens app” but as a high-value enterprise application with industrial consequences. That means identity hygiene, browser security, privileged access controls, logging, backup validation, and patch governance all have a role. The vendor update is necessary, but it is not the entire security story.
Still, the patch path is the center of gravity. Siemens has released fixed versions, and the advisory does not present a workaround that substitutes for updating. General network protections reduce exposure, but they do not remove the vulnerable code. In security terms, compensating controls buy time; they do not retire the risk.
Organizations should therefore resist the temptation to rank this advisory only by its CVSS score. A 7.5 in a low-value internal application is one thing. A 7.5 in a system that stores engineering knowledge and supports manufacturing workflows is another. Context should drive urgency.
There is also a useful distinction between patch deployment and patch readiness. Even if a Teamcenter update cannot be deployed immediately, administrators can begin staging it, reviewing release notes, mapping integrations, confirming rollback options, and identifying the business owners who must approve downtime. The worst position is discovering the advisory and only then realizing nobody knows who owns the platform.
Security teams should also look for signs of exposure while patching is planned. That includes reviewing access paths, confirming whether the application is reachable from external networks, checking remote access groups, auditing privileged accounts, and making sure logs are retained long enough to investigate suspicious behavior. None of that proves exploitation, but it raises the odds that the organization can respond intelligently if something looks wrong.
Teamcenter environments can be especially difficult because ownership may be split. Engineering may own the business process. IT may own servers and Windows infrastructure. A Siemens partner or system integrator may manage customization. Security may own vulnerability tracking but not application change. That division is normal, but it becomes dangerous when nobody is accountable for coordinating the response.
The affected version ranges make that coordination unavoidable. V2312 and V2406 have separate thresholds for the PDF.js issue versus the two newer vulnerabilities. V2412 and V2506 have their own maintenance targets. V2512 is not affected. A generic ticket saying “patch Siemens Teamcenter” is not enough.
Good vulnerability management turns that complexity into a decision record. Which environments exist? Which are production, test, development, supplier-facing, or legacy? Which branches are below the fixed level? Which compensating controls apply while updates are staged? Which owners have signed off on residual risk?
That may sound bureaucratic, but it is the difference between security theater and operational defense. Industrial organizations do not need more dashboards full of red CVEs. They need an accurate chain from advisory to asset to owner to action.
Endpoint hardening still matters. If a vulnerability requires a user to visit an affected page or interact with malicious content, browser configuration, endpoint detection, script controls, and user privilege boundaries can influence outcomes. They are not replacements for the Teamcenter update, but they shape the attacker’s room to maneuver.
Identity is even more central. PLM systems often rely on enterprise authentication and role-based access, with privileged administrative roles that deserve close monitoring. If an attacker can exploit an application flaw from a low-privilege account or misuse a key for unauthorized access, defenders need clear visibility into which accounts touched what and when.
Backups and recovery planning also belong in the conversation. Availability impact is not merely about servers being online; it is about whether the organization can restore a trustworthy Teamcenter state after compromise or corruption. For systems that anchor engineering records, backup integrity and restore testing should be treated as security controls, not just disaster recovery paperwork.
This is where IT and OT cultures can usefully converge. Windows administrators bring patching discipline, identity management, and endpoint telemetry. Industrial teams bring process awareness, validation discipline, and operational risk assessment. Teamcenter sits at the intersection, so the response should too.
That lesson is that the perimeter has moved inward. It is no longer enough to secure firewalls, domain controllers, VPNs, and endpoints while treating engineering platforms as specialized business systems off to the side. PLM, CAD, MES, ERP, document viewers, supplier portals, and identity infrastructure now form a connected fabric that attackers can traverse and defenders must understand.
For administrators, the work begins with the version table but should not end there. Patch the affected Teamcenter branches, validate the update, restrict exposure, review access, and make sure the people who own the engineering process are in the room. The next advisory will have different CVEs and a different product name, but the strategic pattern will be the same: industrial software is software, software has dependencies, and the systems that define what a company builds are now squarely inside the security perimeter.
Source: CISA Siemens Teamcenter | CISA
 Teamcenter Turns a Routine Advisory Into an Industrial Risk Story
Teamcenter Turns a Routine Advisory Into an Industrial Risk Story
The affected product is Siemens Teamcenter, a product lifecycle management platform used to connect engineering, manufacturing, documentation, and process data across organizations. In plain English, it is one of the systems companies use to know what they are building, how it changes, who approved it, and how those decisions move from design into production.That context matters because the advisory lands in the “critical manufacturing” sector, not merely in generic enterprise software. Teamcenter may be deployed as an internal application, but the information it manages is often strategic: product designs, bills of materials, change records, supplier data, release workflows, and supporting documentation. A vulnerability in that environment does not have to shut down a factory to matter; it only has to undermine trust in the data that factory depends on.
The reported maximum severity is substantial rather than catastrophic. Siemens lists a CVSS v3.1 base score of 7.5 and a CVSS v4.0 base score of 8.7 for the advisory overall. That places the issue in the uncomfortable middle zone where executives may not hear “drop everything,” but security teams should hear “schedule this like it matters.”
CISA’s republication adds visibility but also a useful caveat. The agency says its page is a verbatim conversion of Siemens’ CSAF advisory and is provided as-is, which means Siemens ProductCERT remains the primary technical source. That distinction is important in ICS security: CISA amplifies, but the vendor owns the product-specific detail.
The Patch Matrix Is the Message
The most important operational detail is the version matrix. Teamcenter V2312 needs V2312.0014 or later for CVE-2026-33862 and CVE-2026-33893, and V2312.0009 or later for CVE-2024-4367. Teamcenter V2406 needs V2406.0012 or later for the two 2026 CVEs, and V2406.0006 or later for CVE-2024-4367.For newer release lines, the shape is simpler. Teamcenter V2412 needs V2412.0009 or later for CVE-2026-33862 and CVE-2026-33893. Teamcenter V2506 needs V2506.0005 or later for those same two vulnerabilities. Teamcenter V2512 is listed as not affected because the vulnerable component is not present.
That last point is easy to skim past, but it says something revealing about modern enterprise application security. Siemens did not simply say “latest version good, old versions bad.” It said a vulnerable component is absent from V2512, which suggests that some architectural or dependency change removed the exposure rather than merely patching it in place.
For administrators, this means inventory comes before remediation. It is not enough to ask, “Do we run Teamcenter?” The practical question is which branch, which maintenance level, which components, and which exposure paths exist in the environment. In mature shops, that should be answerable from configuration management data; in less mature ones, this advisory may trigger the usual archaeological dig through app owners, integrators, and change windows.
The staggered version thresholds also create a familiar maintenance headache. An organization sitting on V2312.0008 may be exposed to all three CVEs. One on V2312.0010 may have cleared the PDF.js-related issue but still need the later fix for the 2026 flaws. The advisory is a reminder that “we patched Teamcenter last quarter” is not a security state; it is a conversation starter.
The Web Front End Is Still the Soft Underbelly
The most conventional of the three vulnerabilities is CVE-2026-33862, an input handling flaw that can allow attacker-supplied code to execute in another user’s browser when that user visits an affected page. In normal security language, that is cross-site scripting. In PLM language, it means the collaborative interface that makes Teamcenter valuable can also become the place where trust is abused.Cross-site scripting is sometimes treated as a solved or low-drama class of bug because the industry has talked about it for decades. That complacency is a mistake. In authenticated enterprise applications, XSS can be especially useful because the victim is already inside the perimeter, already logged into the application, and often already authorized to see data the attacker wants.
The advisory’s scoring reflects that tension. CVE-2026-33862 requires low privileges and user interaction, but it carries high confidentiality and integrity impact in the CVSS v3.1 vector. That combination tells a familiar story: an attacker may need a foothold or an application account, but once malicious content reaches the right viewer, the browser becomes a bridge into sensitive workflow context.
For Windows-heavy engineering environments, this is particularly relevant because the endpoint and the browser remain the daily interface to industrial software. A Teamcenter user may be an engineer, a release manager, a supplier coordinator, or an administrator moving through documents, dashboards, and records. The browser session is where application permissions meet human habit.
This is why XSS in business-critical applications should not be dismissed as “just JavaScript.” If the application is trusted enough to approve product changes, publish technical data, or coordinate suppliers, then injected script is not a nuisance. It is a way to borrow the user’s position inside a workflow.
Hard-Coded Credentials Are a Design Debt, Not a Bug Class
CVE-2026-33893 is the vulnerability that should make security architects pause. Siemens describes it as a hard-coded key used for obfuscation and stored directly in the application, potentially allowing an attacker to obtain the key and misuse it for unauthorized access. The CVSS v3.1 score is 7.5, while the CVSS v4.0 score rises to 8.7.Hard-coded credentials and keys are not just implementation errors; they are design shortcuts with long tails. They create secrets that cannot be rotated cleanly, cannot be scoped dynamically, and often cannot be monitored with the same rigor as identity-provider credentials or managed secrets. Once exposed, they tend to be exposed everywhere the affected version exists.
The advisory does not say that the key grants total system compromise, and it would be irresponsible to inflate the claim beyond what Siemens published. But the concern is clear enough. A credential-like artifact embedded in application code changes the attacker’s problem from “defeat the access control model” to “find and reuse what the software already trusts.”
That distinction matters for defenders. With normal credential compromise, incident response can disable an account, reset a password, revoke a token, or rotate a secret in a vault. With a hard-coded key inside a vendor application, the remedy is usually a software update because the trust mechanism itself lives in the product.
This is also where industrial software often collides with enterprise security expectations. Modern IT teams have spent years pushing toward managed identities, short-lived tokens, hardware-backed keys, and auditable secret stores. Legacy patterns still exist in complex platforms, and when they surface inside systems that govern production knowledge, the operational response is rarely as simple as “change the password.”
The PDF.js Bug Shows How Browser Components Keep Escaping Their Original Box
CVE-2024-4367 is older than the two Siemens-specific 2026 entries, but it may be the most instructive. It originated in PDF.js, the JavaScript-based PDF rendering engine associated with Mozilla products, where a missing type check in font handling could allow arbitrary JavaScript execution in the PDF.js context. Siemens’ advisory ties that component issue to affected Teamcenter V2312 and V2406 branches below specific maintenance levels.This is the reality of modern application risk: a vulnerability does not stay neatly confined to the product where it first made headlines. PDF rendering, image processing, compression libraries, document viewers, web frameworks, and JavaScript packages migrate into enterprise platforms. Months or years later, a known flaw can reappear in a very different operational setting.
For Teamcenter, document handling is not a peripheral convenience. Engineering and manufacturing workflows are document-heavy by nature. PDFs can include specifications, drawings, procedures, compliance records, supplier documents, test reports, and release packages. A document viewer embedded in a PLM workflow is exactly the sort of place where a third-party component becomes part of the security boundary.
There is also a WindowsForum angle here. Many administrators have learned to patch browsers aggressively, but they may not think of browser-adjacent components inside server applications with the same urgency. If PDF.js is bundled into a vendor platform, updating Firefox on endpoints does not necessarily update the copy inside Teamcenter.
That is the broader supply-chain lesson. Dependency risk is not solved by patching the famous upstream product. It is solved when every downstream product that embedded the vulnerable component updates, ships, and gets deployed. In industrial IT, that chain often moves more slowly than the public CVE conversation.
CISA’s Network Advice Is Boring Because It Is Still Right
CISA’s recommended practices in the advisory are the standard ICS security refrain: minimize network exposure, keep control systems and remote devices off the public internet, put them behind firewalls, isolate control networks from business networks, use secure remote access such as updated VPNs, and perform impact analysis before defensive changes. None of that is new. All of it remains painfully relevant.The challenge is that Teamcenter often sits in the borderland between engineering IT and operational technology. It may not be a PLC, HMI, or historian, but it supports the processes that feed manufacturing. It may integrate with ERP, CAD, MES, identity systems, file stores, visualization tools, and supplier portals. Drawing the network boundary around it is not always straightforward.
That is why the advisory’s risk cannot be measured only by whether Teamcenter is internet-facing. A non-internet-facing application can still be reachable by thousands of internal users, contractors, engineers on VPN, build systems, data integration jobs, and service accounts. In many intrusions, “internal only” is not a defense; it is a description of where the attacker goes after the first compromise.
Segmentation still matters, but it must be honest segmentation. If Teamcenter has broad trust relationships across engineering, manufacturing, and business networks, then it deserves the same threat modeling attention as any crown-jewel system. Firewalls help only when the access model they enforce matches the sensitivity of the application.
The VPN caveat is equally important. CISA notes that VPNs themselves can have vulnerabilities and must be kept current. That is not boilerplate anymore; remote access infrastructure has become a favorite target precisely because it offers a path into systems that organizations believe are safely tucked away.
The Real Exposure Is the Engineering Data Graph
The advisory says the vulnerabilities could compromise availability, integrity, and confidentiality. That triad sounds abstract until it is mapped onto what PLM systems actually contain. Confidentiality may mean product designs, process details, supplier relationships, and intellectual property. Integrity may mean the trustworthiness of change approvals, configuration data, document versions, and release states. Availability may mean whether engineering and manufacturing teams can keep moving.Integrity deserves special attention. In many security programs, confidentiality gets the budget because stolen data is easy to explain. But in PLM, a subtle integrity failure can be just as damaging. If users cannot trust that a design record, approval trail, or manufacturing instruction is authentic, the business impact can cascade into delays, rework, compliance problems, and safety reviews.
That does not mean these specific vulnerabilities are known to enable silent product sabotage. Siemens has not said that, and neither has CISA. The point is that the affected application lives in a domain where data correctness has operational weight. A bug class that might be annoying in a generic intranet portal can become serious when the portal governs engineering truth.
Attackers understand that distinction. Ransomware crews want business disruption. Espionage actors want intellectual property. Insider-threat scenarios often revolve around access to design and process knowledge. A PLM platform can be attractive to all three, even if the vulnerability path differs.
For Windows administrators, the lesson is to treat Teamcenter not as “the Siemens app” but as a high-value enterprise application with industrial consequences. That means identity hygiene, browser security, privileged access controls, logging, backup validation, and patch governance all have a role. The vendor update is necessary, but it is not the entire security story.
Version Discipline Beats Heroic Incident Response
The straightforward remediation is to update to the Siemens-fixed versions. That sounds simple until it meets the reality of industrial software: validation cycles, integrations, customizations, user acceptance testing, maintenance windows, and change advisory boards. Teamcenter is rarely a throwaway web app that can be bounced after lunch.Still, the patch path is the center of gravity. Siemens has released fixed versions, and the advisory does not present a workaround that substitutes for updating. General network protections reduce exposure, but they do not remove the vulnerable code. In security terms, compensating controls buy time; they do not retire the risk.
Organizations should therefore resist the temptation to rank this advisory only by its CVSS score. A 7.5 in a low-value internal application is one thing. A 7.5 in a system that stores engineering knowledge and supports manufacturing workflows is another. Context should drive urgency.
There is also a useful distinction between patch deployment and patch readiness. Even if a Teamcenter update cannot be deployed immediately, administrators can begin staging it, reviewing release notes, mapping integrations, confirming rollback options, and identifying the business owners who must approve downtime. The worst position is discovering the advisory and only then realizing nobody knows who owns the platform.
Security teams should also look for signs of exposure while patching is planned. That includes reviewing access paths, confirming whether the application is reachable from external networks, checking remote access groups, auditing privileged accounts, and making sure logs are retained long enough to investigate suspicious behavior. None of that proves exploitation, but it raises the odds that the organization can respond intelligently if something looks wrong.
The Advisory Also Tests Asset Management
Every industrial vulnerability story eventually becomes an asset management story. If an organization cannot rapidly answer which Teamcenter versions it runs, who administers them, how they are exposed, and which business processes depend on them, then the vulnerability is only the visible symptom. The deeper problem is a weak map of critical software.Teamcenter environments can be especially difficult because ownership may be split. Engineering may own the business process. IT may own servers and Windows infrastructure. A Siemens partner or system integrator may manage customization. Security may own vulnerability tracking but not application change. That division is normal, but it becomes dangerous when nobody is accountable for coordinating the response.
The affected version ranges make that coordination unavoidable. V2312 and V2406 have separate thresholds for the PDF.js issue versus the two newer vulnerabilities. V2412 and V2506 have their own maintenance targets. V2512 is not affected. A generic ticket saying “patch Siemens Teamcenter” is not enough.
Good vulnerability management turns that complexity into a decision record. Which environments exist? Which are production, test, development, supplier-facing, or legacy? Which branches are below the fixed level? Which compensating controls apply while updates are staged? Which owners have signed off on residual risk?
That may sound bureaucratic, but it is the difference between security theater and operational defense. Industrial organizations do not need more dashboards full of red CVEs. They need an accurate chain from advisory to asset to owner to action.
The Windows Angle Is Not Incidental
Although this is a Siemens advisory, WindowsForum readers should not treat it as outside the Windows ecosystem. Many engineering workstations, server components, identity integrations, browsers, document workflows, and administrative tools around Teamcenter live in Windows-heavy environments. The exploitation path may involve a web session, but the operational blast radius can run through familiar Microsoft-centered infrastructure.Endpoint hardening still matters. If a vulnerability requires a user to visit an affected page or interact with malicious content, browser configuration, endpoint detection, script controls, and user privilege boundaries can influence outcomes. They are not replacements for the Teamcenter update, but they shape the attacker’s room to maneuver.
Identity is even more central. PLM systems often rely on enterprise authentication and role-based access, with privileged administrative roles that deserve close monitoring. If an attacker can exploit an application flaw from a low-privilege account or misuse a key for unauthorized access, defenders need clear visibility into which accounts touched what and when.
Backups and recovery planning also belong in the conversation. Availability impact is not merely about servers being online; it is about whether the organization can restore a trustworthy Teamcenter state after compromise or corruption. For systems that anchor engineering records, backup integrity and restore testing should be treated as security controls, not just disaster recovery paperwork.
This is where IT and OT cultures can usefully converge. Windows administrators bring patching discipline, identity management, and endpoint telemetry. Industrial teams bring process awareness, validation discipline, and operational risk assessment. Teamcenter sits at the intersection, so the response should too.
The Practical Reading of Siemens’ May Advisory
The most useful response to this advisory is neither panic nor shrugging. It is a disciplined, version-specific update plan paired with exposure reduction while testing proceeds. Siemens has provided the fixed maintenance targets, and CISA has amplified the defensive baseline.- Organizations running Teamcenter V2312 should verify whether they are below V2312.0014 for CVE-2026-33862 and CVE-2026-33893, and below V2312.0009 for CVE-2024-4367.
- Organizations running Teamcenter V2406 should verify whether they are below V2406.0012 for the two 2026 vulnerabilities, and below V2406.0006 for the PDF.js-related issue.
- Organizations running Teamcenter V2412 or V2506 should prioritize the maintenance releases V2412.0009 and V2506.0005, respectively, if they have not already deployed them.
- Organizations already on Teamcenter V2512 should document that status rather than assume it, because Siemens lists that branch as not affected due to the vulnerable component not being present.
- Security teams should treat Teamcenter as a high-value application, reviewing network exposure, remote access paths, privileged roles, logging, and backup integrity while application owners schedule updates.
- Administrators should remember that bundled components such as PDF.js are not fixed just because endpoint browsers are patched; the vendor application must be updated too.
Industrial Software Is Now Part of the Security Perimeter
This advisory is modest in tone but broad in implication. Siemens Teamcenter is the sort of platform that sits quietly behind the scenes until an incident reminds everyone how much institutional knowledge flows through it. The vulnerabilities disclosed this week are not a single cinematic zero-day; they are a web flaw, a hard-coded key problem, and a third-party component issue bundled into one industrial application security lesson.That lesson is that the perimeter has moved inward. It is no longer enough to secure firewalls, domain controllers, VPNs, and endpoints while treating engineering platforms as specialized business systems off to the side. PLM, CAD, MES, ERP, document viewers, supplier portals, and identity infrastructure now form a connected fabric that attackers can traverse and defenders must understand.
For administrators, the work begins with the version table but should not end there. Patch the affected Teamcenter branches, validate the update, restrict exposure, review access, and make sure the people who own the engineering process are in the room. The next advisory will have different CVEs and a different product name, but the strategic pattern will be the same: industrial software is software, software has dependencies, and the systems that define what a company builds are now squarely inside the security perimeter.
Source: CISA Siemens Teamcenter | CISA