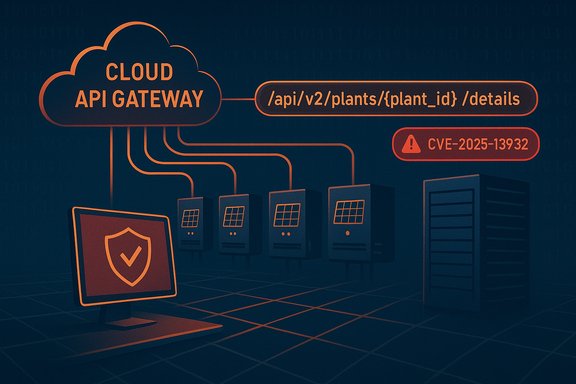
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has published an advisory warning that the SolisCloud Monitoring Platform — specifically its Cloud API and Device Control API — contains a serious Broken Access Control / Insecure Direct Object Reference (IDOR) that allows any authenticated user to retrieve detailed data for any plant by modifying the plant_id parameter in API calls, a flaw tracked as CVE‑2025‑13932 and assigned high severity scores (CVSS v3.1 base score 7.7; CVSS v4 base score 8.3).
SolisCloud is a cloud-based monitoring and device-control platform commonly deployed with grid‑connected inverters and dataloggers in energy and renewable‑generation environments. The platform’s APIs are used to query plant telemetry, configuration details, and status from remote clients and management systems. The issue disclosed by the researcher exposes a fundamental authorization failure: the API trusts a user-supplied identifier (plant_id) without verifying that the caller is permitted to access that plant’s data. That pattern — an IDOR — is a classic Broken Access Control problem in web and API security and is frequently exploited to escalate data exposure from “allowed” to “everything visible.”
This advisory follows the standard ICS/OT playbook: CISA published the coordinated disclosure and scoring; the vulnerability was assigned a CVE identifier; vendor engagement was attempted but, according to the advisory, SolisCloud did not cooperate with mitigation coordination at the time of publication. The advisory additionally lists the affected API versions (API v1 and API v2) and places the issue squarely in critical infrastructure in the Energy sector, with worldwide deployments.
Caveat: CVSS is a risk prioritization tool, not an operational guarantee. Your organization's exposure depends on how widely the API is reachable from untrusted networks, which credentials are in use, and whether engineering workstations or jump hosts are properly hardened.
Practical defensive steps for Windows and IT/OT teams:
Appendix: Key advisory details at a glance
Source: CISA SolisCloud Monitoring Platform | CISA
 Background / Overview
Background / Overview
SolisCloud is a cloud-based monitoring and device-control platform commonly deployed with grid‑connected inverters and dataloggers in energy and renewable‑generation environments. The platform’s APIs are used to query plant telemetry, configuration details, and status from remote clients and management systems. The issue disclosed by the researcher exposes a fundamental authorization failure: the API trusts a user-supplied identifier (plant_id) without verifying that the caller is permitted to access that plant’s data. That pattern — an IDOR — is a classic Broken Access Control problem in web and API security and is frequently exploited to escalate data exposure from “allowed” to “everything visible.”This advisory follows the standard ICS/OT playbook: CISA published the coordinated disclosure and scoring; the vulnerability was assigned a CVE identifier; vendor engagement was attempted but, according to the advisory, SolisCloud did not cooperate with mitigation coordination at the time of publication. The advisory additionally lists the affected API versions (API v1 and API v2) and places the issue squarely in critical infrastructure in the Energy sector, with worldwide deployments.
What the advisory actually says
Executive summary (concise)
- A Broken Access Control (IDOR) vulnerability in the SolisCloud Monitoring Platform allows any authenticated user to access another plant’s detailed data by modifying the plant_id parameter in API requests.
- The issue has been assigned CVE‑2025‑13932. The advisory reports a CVSS v3.1 base score of 7.7 (AV:N/AC:L/PR:L/UI:N/S:C/C:H/I:N/A:N) and a CVSS v4 base score of 8.3 (AV:N/AC:L/AT:N/PR:L/UI:N/VC:H/VI:N/VA:N/SC:H/SI:N/SA:N).
- CISA reports no known public exploitation of this specific vulnerability at the time of publication, but stresses that the API is network‑exposed and that the flaw is remotely exploitable with low attack complexity.
Affected products and scope
- Monitoring Platform (Cloud API & Device Control API): API v1 and API v2. The advisory treats these APIs as the primary attack surface because they return detailed plant metadata and telemetry that attackers can misuse.
Risk evaluation (as summarized by CISA)
- Successful exploitation could expose sensitive plant‑level data (configuration, operational telemetry, implicit credentials or API tokens in some implementations) that would enable reconnaissance, operational disruption, or follow‑on attacks such as targeted social engineering or credential theft. Because the API is network‑accessible and the attack requires only a valid authenticated session with low privileges, the practical risk is meaningful for operators who rely on SolisCloud for remote monitoring.
Technical analysis — how the flaw works
The failure mode: IDOR at the API layer
At its core, the issue is an Insecure Direct Object Reference (IDOR): the API accepts a resource identifier (plant_id) supplied by the client and returns the full resource representation without verifying that the authenticated principal is authorized to view that resource.- When an authenticated user issues a request like GET /api/v2/plants/{plant_id}/details, the server looks up the plant by the supplied identifier and returns details. If the server does not check that the caller’s account is associated with that plant, any valid credential can enumerate or enumerate arbitrary plant_ids to harvest data.
- Attackers can automate this process: enumerate plant identifiers (predictable numeric IDs, UUIDs, or derived from other metadata), collect responses, and aggregate telemetry or configuration information for later use.
Real‑world impact vectors
- Confidentiality breach: Plant configuration, historical telemetry, site owner data, and possibly device serials or network identifiers can be exfiltrated.
- Operational reconnaissance: Attackers can map an operator’s fleet, identify high‑value sites, and plan targeted intrusions.
- Follow‑on compromise: If the API leaks API keys, credentials, or internal endpoints, attackers can pivot to device control flows or social engineering campaigns against operations staff.
Why the CVSS scores matter (and what they mean)
CISA’s advisory presents both CVSS v3.1 and CVSS v4 scores to aid risk prioritization. The reported CVSS v3.1 7.7 highlights a high severity with meaningful confidentiality impact and notable scope change (the vulnerability can affect resources beyond a single principal). The CVSS v4 8.3 score — slightly higher — reflects v4’s expanded assessment vectors (including the vulnerability’s effect on veracity/confidentiality and scope considerations). These scores indicate the advisory’s view that the vulnerability is both network‑exposed and realistically exploitable by low‑privilege authenticated accounts. These formal scores are intended to help operators answer the standard question: “How urgently do we remediate?” — and the recommendation is to treat this as high priority.Caveat: CVSS is a risk prioritization tool, not an operational guarantee. Your organization's exposure depends on how widely the API is reachable from untrusted networks, which credentials are in use, and whether engineering workstations or jump hosts are properly hardened.
Mitigations recommended (CISA and practical hardening)
CISA includes fallback recommendations consistent with standard ICS guidance: minimize internet exposure, place the control/monitoring network behind firewalls and network segmentation, and use secure remote access paths (VPNs, jump hosts) when remote access is required. They also remind operators that VPNs require hardening and are only as secure as the endpoints that connect through them. Because SolisCloud reportedly did not cooperate with CISA’s mitigation coordination at the time of the advisory, operators must assume vendor fixes may not be available and should prioritize compensating controls.Practical defensive steps for Windows and IT/OT teams:
- Inventory: Identify every integration point and client that talks to SolisCloud APIs. Record which Windows engineering workstations, servers, and jump hosts can reach the management APIs.
- Isolate: Block direct internet access to the SolisCloud API endpoints from general purpose networks. Ensure only authorized management hosts and restricted subnets can reach the APIs.
- Harden remote access: Require jump hosts with MFA, endpoint posture checks and strict logging for any host permitted to reach the vendor cloud. Disable broad VPN split‑tunneling to prevent devices from becoming de facto bridges.
- Rotate credentials: If any API keys or shared credentials are used across multiple plants or accounts, rotate them and adopt least‑privilege API tokens scoped to a single plant.
- Audit & monitor: Enable and retain detailed API logs and look for anomalous requests that change plant_id values or enumerate resources. On Windows jump hosts, increase telemetry collection (Windows Event logs, EDR) and hunt for unexpected API client use.
- Compensating web‑app controls: If an on‑prem proxy or API gateway sits in front of SolisCloud traffic, implement server‑side authorization checks at the gateway (enforce that the authenticated principal’s assigned plant set matches requests).
- Incident readiness: Prepare playbooks for unauthorized data access: preserve logs, snapshot relevant hosts, and rotate credentials for exposed accounts. Follow internal reporting to CISA or local CERT if you detect suspicious activity.
Verification, corroboration, and gaps
- The core claims — IDOR via plant_id in SolisCloud’s Cloud API & Device Control API; CVE‑2025‑13932; the CVSS scores; and CISA’s mitigations — are summarized in the advisory material provided to this article and reproduced in the advisory text available in the uploaded CSAF material. Those details form the primary factual basis for this feature.
- Independent verification: While CISA is the coordinating authority for ICS advisories and is the primary source, multiple past coordinated advisories published by national authorities and vendors repeatedly show the same mitigation pattern (minimize exposure, segment networks, rotate keys). Cross‑referencing other ICS advisories in the uploaded files shows this advisory sits within a pattern of API and controller authorization failures being high‑risk in energy and industrial contexts. Those analogous advisories — while not the same vulnerability — reinforce that API authorization failures are commonly high‑impact and pragmatic to mitigate via network controls and rapid credential rotation.
- Unverifiable claims and caution: At the time of publication CISA reported no known public exploitation. That statement is time‑bounded and must be treated as such; absence of evidence is not evidence of absence. Organizations should assume the vulnerability could be discovered independently by attackers and should therefore prioritize mitigation. If your environment shows any signs of unexpected API access, treat it as potentially operationally significant and investigate immediately.
Threat modeling for Windows‑centric operators
Windows administrators and security teams will likely play a central role in containing this vulnerability even though the bug resides in a cloud API. Here’s how the typical attack chain could intersect with Windows infrastructure:- Engineering workstations or jump servers (commonly Windows) hold credentials, API keys, or session cookies used to authenticate to vendor APIs. Compromise of a Windows host via phishing or a malicious attachment could leak credentials that allow an attacker to exercise the IDOR remotely.
- Attackers exploiting the IDOR for reconnaissance can map plant topology and then target Windows‑based management servers, VPN concentrators, or developer systems that manage firmware or configuration rollouts. Once footholds exist on Windows hosts, the attacker can broaden access using standard lateral movement techniques.
- Defensive priorities for Windows teams therefore should emphasize credential hygiene (rotate keys), endpoint protection on engineering workstations, and strict least‑privilege access to cloud APIs. If possible, enforce conditional access policies and use authenticated proxies that attach caller identity and carry out server‑side enforcement.
Recommended incident response playbook (practical checklist)
- Confirm inventory: enumerate all accounts, API keys, and service principals that have access to SolisCloud APIs. Prioritize accounts with Editor/Manager privileges.
- Revoke and rotate: rotate API tokens and shared secrets; remove any tokens that are widely shared across plants. Issue scoped tokens with the narrowest possible privileges.
- Lock down network paths: restrict access to the cloud API to a limited set of management IPs; block the API from broad user networks.
- Examine logs: search API logs (if available), proxy logs, and Windows event/EDR telemetry for unusual GET/POST requests that manipulate plant_id or that enumerate resource identifiers. Preserve these logs for forensic analysis.
- Validate endpoints: for systems integrating with SolisCloud, confirm that client code does not construct requests from user‑supplied or unvalidated parameters. If client code does, apply immediate validation and server‑side checks at the gateway.
- Engage vendor support: open a ticket with SolisCloud support and document your findings. If the vendor is unresponsive, escalate to responsible disclosure channels and coordinate with national CSIRTs if necessary. CISA’s advisory notes the vendor did not respond to outreach at the time — operators should document vendor contact attempts in their incident record.
Broader lessons and long‑term remediation
- APIs must implement server‑side authorization checks that require cross‑validation of the authenticated principal’s entitlements against the requested resource. Relying on client‑side filtering or token scoping that is not validated server‑side invites IDOR issues.
- Architecture should assume network compromise and therefore minimize sensitive data returned by APIs unless absolutely necessary. Implement coarse‑grained records in telemetry-only endpoints and restrict detailed configuration data to privileged, audited management endpoints.
- Vendors should provide scoped API tokens by design (per‑plant tokens with limited read/write scopes), and API gateways should reject requests where the token does not map to the requested plant_id. If the product currently lacks such design, customers should demand remediation. Recent ICS advisories have repeatedly shown that vendor cooperation and timely patching make a material difference; where vendor cooperation is absent, strong network and procedural mitigations become the only practical defense.
Conclusion — what Windows and energy operators must do now
The SolisCloud Monitoring Platform vulnerability (CVE‑2025‑13932) represents a high‑priority authorization failure: a remotely exploitable IDOR that can disclose plant‑level telemetry and configuration to any authenticated account. Treat the advisory’s findings as urgent. Implement immediate compensating controls — inventory, isolate, rotate, harden, monitor — and do not wait for a vendor patch before raising the operational posture of your endpoint and network defenses. If your environment uses SolisCloud, treat any unexplained API traffic or sudden data exports as an incident and escalate accordingly; prepare to rotate credentials and tighten API access controls across management hosts, Windows jump servers, and engineering workstations. The advisory’s remediation window depends on local risk tolerance, but from a defensive operations perspective the right answer is to act now rather than later.Appendix: Key advisory details at a glance
- Vulnerability: Authorization Bypass through user‑controlled key / IDOR (plant_id).
- CVE: CVE‑2025‑13932 (per CISA advisory).
- Affected components: SolisCloud Monitoring Platform — Cloud API & Device Control API (API v1, API v2).
- CVSS (as published in advisory): v3.1 = 7.7; v4 = 8.3.
- Vendor engagement: SolisCloud did not respond to CISA coordination requests at time of advisory.
- Immediate mitigations: minimize internet exposure, place systems behind firewalls and segmented networks, adopt secure remote access (VPN/jump hosts), rotate credentials, and increase logging and monitoring.
Source: CISA SolisCloud Monitoring Platform | CISA