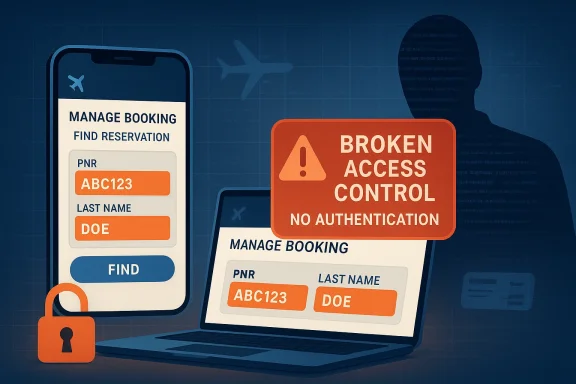
The newly disclosed SpiceJet Online Booking System vulnerabilities are the sort of defects that turn a simple airline lookup page into a privacy nightmare. CISA says the flaws affect all versions of the booking system and could let an attacker disclose sensitive passenger information without authentication, with both issues assigned a CVSS 3.1 score of 7.5 and mapped to classic access-control failures. The most troubling part is how little friction an attacker appears to need: one issue involves predictable PNR enumeration, while the other exposes full booking details using only a PNR and last name. CISA also notes that SpiceJet did not respond to coordination requests, which raises the pressure on customers to assess exposure quickly and defensively senger booking systems sit in an awkward and highly sensitive position. They are customer-facing enough to attract routine web abuse, yet privileged enough to expose travel itineraries, identity details, booking references, and other metadata that can be weaponized in phishing, fraud, stalking, or social engineering. That makes any control failure in such systems more than a garden-variety website bug; it becomes a privacy and safety issue with real-world consequences. CISA’s advisory frames the affected product as a transportation-sector system with worldwide deployment, which is exactly the sort of footprint that can magnify even a “small” access-control mistake .
The core pattern hyone who has tracked modern web disclosures: an endpoint intended for legitimate self-service access ends up trusting user-supplied identifiers too much. In this case, the booking system appears to expose passenger name records, or PNRs, in a way that allows unauthenticated enumeration. That is a textbook example of authorization bypass through a user-controlled key, the kind of flaw that is often easy to describe and hard to justify from a design perspective. If an attacker can predict the identifier space, the system has effectively done half the reconnaissance work for them .
The second issue is even more direct. Cking retrieval page permits full passenger booking details to be accessed using only a PNR and last name, with no authentication or verification mechanism beyond that weak combination. That means the service is treating two basic data points as if they were a security boundary. They are not. In practice, PNR plus surname is not an authorization factor; it is a lookup convenience, and convenience should never be mistaken for identity proof .
Historically, this sort of disclosure fits a broader trend iion platforms. Airlines and booking systems have long leaned on lightweight retrieval workflows because they must serve millions of users efficiently, often on mobile devices and through third-party integrations. But lightweight does not have to mean insecure. The best-designed systems layer identity checks, session controls, and rate limiting on top of convenience flows so that a booking reference alone cannot become a universal access token. When that discipline is missing, attackers can enumerate, scrape, and correlate data at scale.
There is also a governance lesson in the advisory’s publication. CISA’s note that the vendor did not coordinate is important because it suggests defenders may not get the luxury of a neat remediation package right away. That shifts the burden to operators, SOC teams, travel partners, and possibly downstream integrators to assess exposure independently. In other words, the warning is not only about code quality; it is about operational readiness and incident response maturity.
At a high level, the advisory is about broken trust boundaries. One vulnerability lets an unauthenticated user query PNRs because the booking API apparently fails to enforce access controls on an endpoint that should have been restricted. The other lets an unauthenticated user retrieve complete booking records with only a PNR and last name, which means the application is using a weak, guessable identity proxy in place of proper authentication. Together, they point to a system where “knowing something about a booking” is treated as if it were equivalent to being entitled to view it .
That distinction matters because modern attackers do not need to break encryptionted malware if the application itself is willing to hand over data. They can simply probe the interface, enumerate identifiers, and harvest records. The result may be names, itinerary details, seat assignments, contact information, or other metadata that can support later fraud. In travel systems, even metadata can be highly sensitive because it reveals patterns of movement, personal associations, and timing.
CISA classified both issues under familiar weakness categories: CWE-639, authorization bypass through user-controlled key, and CWE-306, missing authentication for critical function. Those labels are more than taxonomy. They tell defenders that this is not an exotic exploit chain; it is a direct failure to enforce the simplest rule in web security, which is that the system—not the user—must decide who may see what. A booking lookup page that accepts a PNR and surname may be fine as a convenience feature, but it is not acceptable as the only gate protecting full passenger data.
There is also the matter of scale. PNRs are not random secrets in the way a long cryptographic key mig follow a predictable pattern, enumeration becomes a scripting exercise rather than a research challenge. That means automation can turn one bug into many disclosures. For an airline, that can mean thousands of records. For travelers, it can mean a persistent privacy exposure long after the booking was made.
The threat model should not be narrowly technical either. Booking data can be repurposed for credential stuffing, impersonation, fraudulent service changes, targeted scams, or even physical risk if travel plans become known to a malicious party. In other words, disclosure here is not just about violating policy; it is about enabling downstream harms that can extend well beyond the booking portal.
What makes this especially risky is that enumeration is not noisy in the way brute force often is. A script can request oneith minimal variation in traffic patterns, and quietly harvest valid records. Unless rate limiting, anomaly detection, or strict server-side authorization is in place, the attacker may be able to operate for a long time before anyone notices. That makes the flaw operationally stealthy, which is often worse than a conspicuous crash.
A good booking system should treat any externally supplied reference as merely a lookup hint, not a permission grant. At minimum, the application should bind the record to an authenticated session, a second factor, a verified contact channel, or another robust proof of entitlement. Without that, the interface is effectively advertising a data oracle.
The larger lesson is that predictability is a security liability when combined with weak authorization. Systems that expose sequential or patterned identifiers often appear harmless during development because the lookup seems to work fine. But from an attacker’s perspective, every predictable field is a map, not a hurdle.
This matters because many people casually share booking references during customer service calls, in screenshots, or through email threads. Lastsecret. So the “secret” is not secret in any meaningful sense. If the system assumes those values are sufficient proof of ownership, then it has granted access based on data that is often already in circulation.
It also means the exposure could be dynamic. Booking details can change over time as itinerary segments are updated, seats are reassigned, or contact details are modified. An attacker with ongoing access to the page may be able to monitor changes, not just read a one-time snapshot. That creates a continuing privacy risk.
For defenders, the corrective mindset should be blunt: if a page can reveal “full passenger booking details,” then the page should be protected like a sensitive account portal, not a consumer convenience widget. Strong authentication, session binding, and careful authorization checks should be non-negotiable.
There is also a downstream ecosystem issue. Travel data does not live in isolation. It often flows to customer service platforms, airport systems, notification services, loyalty programs, and third-party agents. If one booking interface is weak, adjacent systems may inherit the consequences through integration, caching, or support workflows. That is why a single access-control bug can become an ecosystem problem rather than a standalone defect.
For consumers, the stakes are more personal. Exposure of itineraries can reveal where someone is going, when they are traveling, and who they may be traveling with. It can also support phishing attempts that look eerily legitimate, because the attacker already knows the booking reference and travel context. That makes the information immediately useful for impersonation.
The practical challenge is that travelers often assume booking data is “only” travel metadata. It is not. In the wrong hands, it becomes identity-adjacent data that can be turned into account recovery attempts, scam calls, or social engineering scripts. The attack does not need to be technically sophisticated to be harmful.
That distinction is important for remediation. If the issue were merely a bad parameter check, a quick patch might be enough. But when the underlying problem is a weix must be architectural. Developers need to rethink how booking records are retrieved, how sessions are established, and what proof of entitlement is required before sensitive data is returned. A better warning label is not a security control.
CISA’s CVSS 7.5 score also deserves attention. This is not an existential worm-level event, but it is serious enough to justify rapid defensive action. The score reflects a remote, unauthenticated disclosure with high confidentiality impact. That combination is exactly what many organizations underestimate until data starts appearing in logs, customer complaints, or public proof-of-concept demonstrations.
The exposure can also support reconnaissance for other crimes. Booking details may reveal contact patterns, loyalty identities, or support procedures, all of which can be used to prime phishing and account takeover. So while the immediate impact is disclosure, the downstream impact can be broader and more durable.
In practical risk terms, disclosure bugs in customer data systems are often the first step in a chain. They are not always the loudest vulnerabilities, but they are frequently the most reusable.
The second priority is control tightening. Even before a vendor patch exists, operators should reduce who can query booking records, limit the visibility of sensitive fields, and enforceomaly detection on lookup endpoints. If a workflow can be tied to an authenticated customer session, it should be. If it can be tied to a verified contact method, even better. The guiding principle should be least privilege by default.
The broader travel industry should also pay attention to the social consequence of disclosure. Passenger data may seem mundane to engineers, but it can be extremely sensitive to the people whose movement it reveals. That means privacy engineering and access control cannot be treated as optional UX enhancements. They are core safety features.
For security teams, that means reviewing every “retrieve my booking” or “find my reservation” flow with fresh eyes. If a page returns personal data based on something a customer can easily guess or share, then it needs more than cosmetic hardening. It needs a real identity check.
It will also be important to see whether SpiceJet issues guidance, whether affected customers are notified, and whether security researchers publish follow-on analysis. When a vendor does not initially engage, public scrutiny often becomes the main force pushing remediation. That is not ideal, but it is common. In the meantime, defenders should assume the exploitability is real and the privacy impact is immediate.
Source: CISA SpiceJet Online Booking System | CISA
The core pattern hyone who has tracked modern web disclosures: an endpoint intended for legitimate self-service access ends up trusting user-supplied identifiers too much. In this case, the booking system appears to expose passenger name records, or PNRs, in a way that allows unauthenticated enumeration. That is a textbook example of authorization bypass through a user-controlled key, the kind of flaw that is often easy to describe and hard to justify from a design perspective. If an attacker can predict the identifier space, the system has effectively done half the reconnaissance work for them .
The second issue is even more direct. Cking retrieval page permits full passenger booking details to be accessed using only a PNR and last name, with no authentication or verification mechanism beyond that weak combination. That means the service is treating two basic data points as if they were a security boundary. They are not. In practice, PNR plus surname is not an authorization factor; it is a lookup convenience, and convenience should never be mistaken for identity proof .
Historically, this sort of disclosure fits a broader trend iion platforms. Airlines and booking systems have long leaned on lightweight retrieval workflows because they must serve millions of users efficiently, often on mobile devices and through third-party integrations. But lightweight does not have to mean insecure. The best-designed systems layer identity checks, session controls, and rate limiting on top of convenience flows so that a booking reference alone cannot become a universal access token. When that discipline is missing, attackers can enumerate, scrape, and correlate data at scale.
There is also a governance lesson in the advisory’s publication. CISA’s note that the vendor did not coordinate is important because it suggests defenders may not get the luxury of a neat remediation package right away. That shifts the burden to operators, SOC teams, travel partners, and possibly downstream integrators to assess exposure independently. In other words, the warning is not only about code quality; it is about operational readiness and incident response maturity.
 Overview
Overview
At a high level, the advisory is about broken trust boundaries. One vulnerability lets an unauthenticated user query PNRs because the booking API apparently fails to enforce access controls on an endpoint that should have been restricted. The other lets an unauthenticated user retrieve complete booking records with only a PNR and last name, which means the application is using a weak, guessable identity proxy in place of proper authentication. Together, they point to a system where “knowing something about a booking” is treated as if it were equivalent to being entitled to view it .That distinction matters because modern attackers do not need to break encryptionted malware if the application itself is willing to hand over data. They can simply probe the interface, enumerate identifiers, and harvest records. The result may be names, itinerary details, seat assignments, contact information, or other metadata that can support later fraud. In travel systems, even metadata can be highly sensitive because it reveals patterns of movement, personal associations, and timing.
CISA classified both issues under familiar weakness categories: CWE-639, authorization bypass through user-controlled key, and CWE-306, missing authentication for critical function. Those labels are more than taxonomy. They tell defenders that this is not an exotic exploit chain; it is a direct failure to enforce the simplest rule in web security, which is that the system—not the user—must decide who may see what. A booking lookup page that accepts a PNR and surname may be fine as a convenience feature, but it is not acceptable as the only gate protecting full passenger data.
What makes these flaws high risk
The risk comes from the combination of network reachability, ease of abuse, and the sensitivity of the data exposed. An unauthenticated attacker does not need prior access, stolen credentials, or social engineering to begin probing the system. That lowers the bar dramatically and makes large-scale abuse more plausible. CISA’s CVSS 7.5 rating reflects that reality: the vulnerabilities are remote, low-complexity, and capable of exposing high-value confidential information without affecting integrity or availability .There is also the matter of scale. PNRs are not random secrets in the way a long cryptographic key mig follow a predictable pattern, enumeration becomes a scripting exercise rather than a research challenge. That means automation can turn one bug into many disclosures. For an airline, that can mean thousands of records. For travelers, it can mean a persistent privacy exposure long after the booking was made.
The threat model should not be narrowly technical either. Booking data can be repurposed for credential stuffing, impersonation, fraudulent service changes, targeted scams, or even physical risk if travel plans become known to a malicious party. In other words, disclosure here is not just about violating policy; it is about enabling downstream harms that can extend well beyond the booking portal.
The PNR Enumeration Problem
The first issue is the more elegant of the two in technical terms, but also the more dangerous at scale. CISA says an unauthenticated user can query passenger name records because the booking API lacks access controls, and because the PNR identifiers follow a predictable pattern, an attacker can systematically enumerate valid records. That is a classic user-controlled key problem: the server accepts an identifier from the client and then fails to verify whether the requester should be allowed to use it .What makes this especially risky is that enumeration is not noisy in the way brute force often is. A script can request oneith minimal variation in traffic patterns, and quietly harvest valid records. Unless rate limiting, anomaly detection, or strict server-side authorization is in place, the attacker may be able to operate for a long time before anyone notices. That makes the flaw operationally stealthy, which is often worse than a conspicuous crash.
Why predictable identifiers matter
Predictable identifiers compress the attacker’s workload. Instead of discovering secrets, they test a sequence. Instead of bypassing identity, they exploit application logic. And instead of needing an account, they need only access to the endpoint itself. The more structured the identifier space, the more feasible large-scale scraping becomes.A good booking system should treat any externally supplied reference as merely a lookup hint, not a permission grant. At minimum, the application should bind the record to an authenticated session, a second factor, a verified contact channel, or another robust proof of entitlement. Without that, the interface is effectively advertising a data oracle.
The larger lesson is that predictability is a security liability when combined with weak authorization. Systems that expose sequential or patterned identifiers often appear harmless during development because the lookup seems to work fine. But from an attacker’s perspective, every predictable field is a map, not a hurdle.
- Predictable PNRs make automation easier.
- Unauthenticated endpoints invite scraping.
- Server-side authorization is the real control, not the identifier format.
- Rate limiting can help, but it is not a substitute for access control.
- Even partial disclosures can support later fraud.
The Missing Authentication Exposure
The second vulnerability is more straightforward but no less serious. CISA says a public booking retrieval page can reveal full passenger booking details with only a PNR and last name, and that there are no authentication or verification mechanisms beyond those inputs. That means the page is effectively relying on two pieces of contextual data as a credential substitute. In security terms, that is not authentication; it is a guessable lookup ritual .This matters because many people casually share booking references during customer service calls, in screenshots, or through email threads. Lastsecret. So the “secret” is not secret in any meaningful sense. If the system assumes those values are sufficient proof of ownership, then it has granted access based on data that is often already in circulation.
Why this is worse than a simple data leak
A simple leak is bad enough, but a retrieval page with no verification logic turns the leak into an access path. That difference matters. A leaked database might expose data once; a live retrieval function can be queried repeatedly, at scale, and on demand. That makes it much more useful to attackers and much harder for victims to contain.It also means the exposure could be dynamic. Booking details can change over time as itinerary segments are updated, seats are reassigned, or contact details are modified. An attacker with ongoing access to the page may be able to monitor changes, not just read a one-time snapshot. That creates a continuing privacy risk.
For defenders, the corrective mindset should be blunt: if a page can reveal “full passenger booking details,” then the page should be protected like a sensitive account portal, not a consumer convenience widget. Strong authentication, session binding, and careful authorization checks should be non-negotiable.
- PNR plus surname is weak proof of entitlement.
- The page exposes more than minimal contact data.
- Repeated queries can reveal changing booking metadata.
- Convenience workflows should not double as security boundaries.
- Sensitive lookups deserve layered verification.
Operational Impact for Airlines and Travel Platforms
The most immediate operational consequence is loss of trust. Airline booking systems are customer-facing, and customers expect those systems to be reliable guardians of personal travel data. When a basic lookup page becomes a disclosure mechanism, the reputational damage can be as significant as the technical failure. Travelers may reasonably ask why a booking reference and surname are enough to surface data that should have remained private.There is also a downstream ecosystem issue. Travel data does not live in isolation. It often flows to customer service platforms, airport systems, notification services, loyalty programs, and third-party agents. If one booking interface is weak, adjacent systems may inherit the consequences through integration, caching, or support workflows. That is why a single access-control bug can become an ecosystem problem rather than a standalone defect.
Enterprise vs consumer implications
For enterprise travel managers, the risk is visibility into patterns. Corporate travel often reveals client visits, project timelines, executive movement, and internal event schedules. An attacker who can harvest booking data may infer business relationships, merger activity, or sensitive negotiations. That kind of intelligence can be monetized far beyond the value of the ticket itself.For consumers, the stakes are more personal. Exposure of itineraries can reveal where someone is going, when they are traveling, and who they may be traveling with. It can also support phishing attempts that look eerily legitimate, because the attacker already knows the booking reference and travel context. That makes the information immediately useful for impersonation.
The practical challenge is that travelers often assume booking data is “only” travel metadata. It is not. In the wrong hands, it becomes identity-adjacent data that can be turned into account recovery attempts, scam calls, or social engineering scripts. The attack does not need to be technically sophisticated to be harmful.
Why CISA’s Classification Matters
CISA’s use of CWE-639 and CWE-306 is telling because both categories point to design-level trust failures rather than implementation typos. CWE-639 flags a system that lets users manipulate a key or identifier to access resources they should not. CWE-306 flags a function that should require authentication but does not. In both cases, the defect is that the application trusted the wrong input to do the job of access control .That distinction is important for remediation. If the issue were merely a bad parameter check, a quick patch might be enough. But when the underlying problem is a weix must be architectural. Developers need to rethink how booking records are retrieved, how sessions are established, and what proof of entitlement is required before sensitive data is returned. A better warning label is not a security control.
CISA’s CVSS 7.5 score also deserves attention. This is not an existential worm-level event, but it is serious enough to justify rapid defensive action. The score reflects a remote, unauthenticated disclosure with high confidentiality impact. That combination is exactly what many organizations underestimate until data starts appearing in logs, customer complaints, or public proof-of-concept demonstrations.
Why the absence of integrity impact still matters
Some teams will look at the advisory and notice that the issue is about disclosure, not tampering. That should not soften the response. Confidentiality failures often precede more damaging attacks. Once an adversary has booking data, they may not need to alter the system directly to cause harm.The exposure can also support reconnaissance for other crimes. Booking details may reveal contact patterns, loyalty identities, or support procedures, all of which can be used to prime phishing and account takeover. So while the immediate impact is disclosure, the downstream impact can be broader and more durable.
In practical risk terms, disclosure bugs in customer data systems are often the first step in a chain. They are not always the loudest vulnerabilities, but they are frequently the most reusable.
- CWE-639 means the attacker controls the key.
- CWE-306 means the function skipped authentication.
- Confidentiality loss can still enable later fraud.
- Design flaws require design-level fixes.
- Low-friction access makes abuse scalable.
Defensive Priorities for Operators
The first priority is exposure assessment. Organizations that use or support SpiceJet booking workflows need to determine whether the affected booking endpoints are reachable, whether they are integrated into third-party systems, and whether cached or mirrored data may extend the risk beyond the primary portal. CISA’s advisory does not provide a vendor fix in the summary we have, and it explicitly says SpiceJet did not respond to coordination requests, so defenders should assume they may have to proceed without much vendor guidance .The second priority is control tightening. Even before a vendor patch exists, operators should reduce who can query booking records, limit the visibility of sensitive fields, and enforceomaly detection on lookup endpoints. If a workflow can be tied to an authenticated customer session, it should be. If it can be tied to a verified contact method, even better. The guiding principle should be least privilege by default.
Immediate steps worth taking
- Inventory any systems that expose PNR lookup or booking retrieval functions.
- Check whether those endpoints require authentication or merely knowledge of a booking reference.
- Review logs for repeated PNR queries, especially sequential patterns.
- Restrict internal and third-party access to booking data APIs.
- Alert customer support teams so they can recognize abuse or suspicious account questions.
- Prepare customer communications in case disclosure is confirmed or suspected.
Industry Lessons Beyond SpiceJet
This advisory is a reminder that not every critical vulnerability looks like a malware campaign or a memory corruption exploit. Some of the most damaging issues are still basic web security failures that should have been eliminated years ago. When a modern booking system can be queried without proper authentication, the real problem is not clever attacker tooling. The real problem is that the product has not enforced the minimum standards users reasonably expect.The broader travel industry should also pay attention to the social consequence of disclosure. Passenger data may seem mundane to engineers, but it can be extremely sensitive to the people whose movement it reveals. That means privacy engineering and access control cannot be treated as optional UX enhancements. They are core safety features.
What peers should learn
- Booking references are not secrets.
- Surnames are not authentication factors.
- Public lookup pages need server-side entitlement checks.
- Customer data systems must be built for abuse at scale.
- Vendor silence should trigger independent risk review.
For security teams, that means reviewing every “retrieve my booking” or “find my reservation” flow with fresh eyes. If a page returns personal data based on something a customer can easily guess or share, then it needs more than cosmetic hardening. It needs a real identity check.
Strengths and Opportunities
The good news is that this advisory is unusually clear about the failure modes, which gives defenders a useful starting point. CISA has identified the affected product, the vulnerable behaviors, and the likely impact with enough specificity that organizations can begin targeted review immediately. That clarity creates a narrow opportunity window for exposure reduction before the issue becomes more widely abused .- The advisory is specific about the affected product and version scope.
- The weakness classes are well understood and easy to map to controls.
- Predictable PNR abuse can often be detected with logging.
- s an opportunity to review all booking-access workflows.
- Security teams can tighten authentication without waiting for a perfect vendor fix.
- Customer support teams can be briefed quickly on likely abuse patterns.
- Travel platforms can use this as a catalyst for broader privacy hardening.
Risks and Concerns
The biggest concern is that the exploit path is simple enough for low-skill attackers to automate. When unauthenticated users can query or retrieve booking data, the barrier to abuse drops sharply. If the system is internet-facing, the odds of scanning and scraping rise quickly, and the damage can spread before defenders fully understand the scope .- Predictable identifiers make enumeration cheap.
- No-auth lookup pages are easy to script against.
- Sensitive travel metadata can fuel phishing and impersonation.
- Vendor non-response may slow coordinated remediation.
- Thirmay extend the exposure surface.
- Data disclosure may be hard to detect after the fact.
- Customer confidence can drop quickly once the issue becomes public.
Looking Ahead
The next thing to watch is whether additional evidence emerges about how broad the exposure really is. The advisory describes the flaw in a way that suggests direct access to sensitive booking data, but the real-world blast radius will depend on deployment, logging, API exposure, and any third-party tooling layered on top. If booking retrieval functions are reused across multiple channels, the effective scope could be wider than the public summary implies.It will also be important to see whether SpiceJet issues guidance, whether affected customers are notified, and whether security researchers publish follow-on analysis. When a vendor does not initially engage, public scrutiny often becomes the main force pushing remediation. That is not ideal, but it is common. In the meantime, defenders should assume the exploitability is real and the privacy impact is immediate.
- Verify whether booking lookups require only PNR and surname.
- Review for sequential or patterned PNR enumeration.
- Check whether any customer-facing APIs expose full booking details.
- Look for third-party portals or cached datasets mirroring the same data.
- Monitor for vendor guidance, patches, or revised access controls.
Source: CISA SpiceJet Online Booking System | CISA