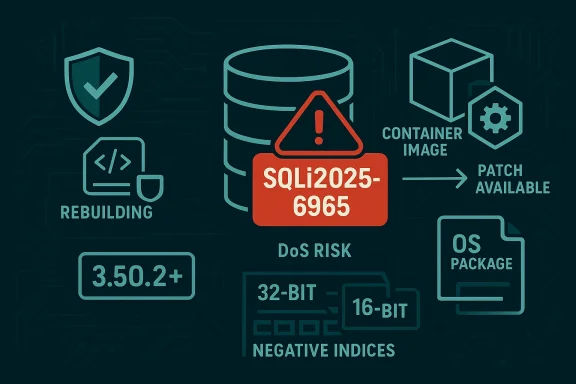
An integer-truncation bug in SQLite — tracked as CVE-2025-6965 — has been confirmed and fixed upstream; the flaw can cause memory corruption when an aggregate query references more columns than the engine expects, and defenders must treat any embedded or statically linked SQLite instances that are older than 3.50.2 as high-priority to inventory and remediate.
SQLite is a ubiquitous embeddable SQL engine shipped as a library (or as an amalgamated C file) inside countless applications, mobile apps, embedded appliances, container images, and OS packages. The bug fixed in the 3.50.2-era changeset arises in SQLite’s aggregate-handling path: when the number of distinct column references processed in an aggregate context grows large, an index used to track those columns can be truncated from a larger integer width to a signed 16-bit value, producing negative indices and subsequent out‑of‑bounds reads or writes. Upstream fixed the problem by changing how the engine detects and handles an excessive number of aggregate terms, raising an error or otherwise preventing bad indexing in the vulnerable code path.
Why this matters operationally: memory corruption in a widely embedded library can translate into three realistic outcomes depending on context — (1) repeated crashes and denial-of-service (the most commonly confirmed impact), (2) data corruption or integrity loss in the database or consumer application, and (3) under highly favorable and platform‑specific conditions, possible code‑execution primitives. Vendors and trackers therefore treat the vulnerability as high‑impact and assign urgent remediation guidance.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
SQLite is a ubiquitous embeddable SQL engine shipped as a library (or as an amalgamated C file) inside countless applications, mobile apps, embedded appliances, container images, and OS packages. The bug fixed in the 3.50.2-era changeset arises in SQLite’s aggregate-handling path: when the number of distinct column references processed in an aggregate context grows large, an index used to track those columns can be truncated from a larger integer width to a signed 16-bit value, producing negative indices and subsequent out‑of‑bounds reads or writes. Upstream fixed the problem by changing how the engine detects and handles an excessive number of aggregate terms, raising an error or otherwise preventing bad indexing in the vulnerable code path.Why this matters operationally: memory corruption in a widely embedded library can translate into three realistic outcomes depending on context — (1) repeated crashes and denial-of-service (the most commonly confirmed impact), (2) data corruption or integrity loss in the database or consumer application, and (3) under highly favorable and platform‑specific conditions, possible code‑execution primitives. Vendors and trackers therefore treat the vulnerability as high‑impact and assign urgent remediation guidance.
What the technical root cause is (concise)
- The vulnerable logic occurs in the aggregate bookkeeping functions (the code path that records and later refers to each distinct column referenced inside aggregate expressions).
- When the number of tracked columns exceeds the representable range used by the internal index, the value is truncated — e.g., a 32‑bit counter is implicitly or explicitly reduced to a signed 16‑bit value — producing a negative or otherwise invalid index.
- That corrupted index can be used later to read or write outside allocated arrays, producing heap corruption, assertion failures in debug builds, or crashes and memory corruption in release builds. Depending on memory layout and execution environment, a later use of the corrupted state may escalate beyond DoS.
Who and what is affected
- Canonical statement from vulnerability trackers: SQLite versions prior to 3.50.2 are affected; the upstream fix is represented in commits around late June 2025 and the 3.50.2 timeframe. Ifed library links a SQLite build older than 3.50.2, you should consider it vulnerable until proven otherwise.
- Important supply-chain nuance: many products don’t rely on the OS-provided sqlite3 package. They vendor the SQLite amalgamation (sqlite3.c / sqlite3.h) into their own source trees and compile it into their binaries. Those statically linked copies are vulnerable until the product is rebuilt with the fixed upstream code. This means patching the OS package is necessary but not sufficient in many deployments.
- Wide surface area: container images, SDK samples, embedded devices, third‑party applications, mobile apps, and appliances can all carry vulnerable SQLite instances. Large fleet risk is real because the same vulnerable binan appear in thousands of artifacts and images. Vendor advisories and distribution trackers have published fixes or backports; operators should check their specific vendor bulletins for package names and fixed versions.
How exploitable is this in practice?
Security communities and vendors have converged on a pragmatic view:- Confirmed and most likely impact: denial-of-service (application crash or process termination) when attacker-controlled SQL invokes the problematic aggregate pattern. Many vendor advisories and distro trackers list availability/DoS as the primary confirmed outcome.
- Elevated risk scenarios: If an attacker can both (a) reach a vulnerable SQLite instance and (b) execute arbitrary SQL that triggers the pathological aggregate expression with extremely large or crafted column counts, then an attacker can pron. In some environments, memory corruption may be chainable to data corruption or even code execution — but those chains are environment‑specific, fragile, and require additional conditions. Treat RCE claims as possible but not universally demonstrated unless you see a trustworthy, platform‑specific PoC or vendor confirmation.
- Attack vectors: network‑facing services that allow user-provided SQL, embedded web components exposed to untrusted content, management consoles that accept SQL fragments, and any service that exposes SQL execution (e.g., via embedded scripting) are the highest priority. Classic examples: custom server agents, management UIs, Sandboxable “SQL console” features, or web‑facing APIs that accept raw SQL fragments.
Vendor and distribution response (w)
- Upstream SQLite: fixes were checked into the repository in late June 2025; upstream notes explicitly raise an error or alter the bookkeeping so the truncation cannot occur. The check‑in and follow-ups are visible in the SQLite Fossil tree and the commit IDs are published in the project’s check‑in logs.
- Major distributions (Debian, Ubuntu, Red Hat, SUSE, Alpine, Oracle Linux, ries and updated packages or backports to provide patched binaries to users. Check your platform security tracker for the precise package name and fixed release.
- ISVs and device vendors: many vendors that statically link SQLite shipped hotfixes or updated firmware/apps; other vendors issued advisories asking customers to update to patched app/firmware releases. Because static linking requires rebuilds, vendor remediation timelines vary.
Immediate, prioritized playbook for defenders
If you operate systems, follow this prioritized sequence. Each step reduces risk quickly and produces evidence you can use to track progress.- Inventory: Find every instance of sqlite3 binaries and embedded amalgamations.
- Linux package checks: dpkg -l | grep -i sqlite or rpm -qa | grep -i sqlite.
- Container/OCI images: run SBOM and scanner tools (syft, trivy, grype) to list sqlite artifacts.
- Windows: search for sqlite3.dll s installed program folders and installer caches (Get-ChildItem -Path C:\ -Filter sqlite3.dll -Recurse).
- Verify runtime versions where possible:
- From a sqlite shell: sqlite3 --version prints the CLI version.
- From SQL: SELECT sqlite_version(); and SELECT sqlite_source_id(); or call sqlite3_libversion() at the application level to confirm the library source id and runtime version. Use these to prove whether the running library is qlite.org]
- Patch system packages: apply vendor updates from your distribution. Use vendor errata pages to confirm package release numbers. Reboot or restart services where the distro.
- Rebuild statically linked artifacts: hunt source trees and product bundles for sqlite3.c/sqlite3.h and schedule rebuilds with upstream 3.50.2+ (or apply vendor‑supplied patched binaries). Static embeds are the slowest but most critical remediation path.
- Short-term compensations where rebuild is not immediately possible:
- Disable or restrict any UI/API that accepts raw SQL, parameterize queries, and strictly validate any client‑supplied SQL fragments.
- Add request-size and column-count limits where application logic accepts user-supplied SQL generation parameters.
- Apply runtime contsses, cgroups, ulimits) to reduce blast radius if the DB engine crashes.
- Monitor and verify: add crash signatures tied to SQLite faults to your observability dashboards and check for disappearance of crash patterns after patching. Re-scan images and artifacts in CI/CD to ensure patched SBOMs are created and retained.
Detection and hunt queries you can copy
- Linux package inventory:
- dpkg: dpkg -l | grep -i sqlite
- RPM: rpm -qa | grep -i sqlite
- Embedded source search:
- grep -R --include="*.c" -n "sqlite3" .
- grep -R --include="*.h" -n "sqlite3.h" .
- Container inspection (without running containers):
- syft <image> -o json | jq '.artifacts[] | select(.name|test("sqlite"))'
- trivy image --severity HIGH,CRITICAL <image>
- Windows recursive seam -Path C:\ -Filter sqlite3.dll -Recurse -ErrorAction SilentlyContinue
- Look for code that constructs large aggregate queries or programmatically composes SQL column lists (these are high-priority review targets).
Practical validation and test recipes
- Reproduce in an isolated lab: if you find a suspect binary, run it in a disposable VM or container and exercise a PoC (only in a controlled environment). Public PoCs and fuzz testcases were published by some researchers and make good lab tests; treat PoCs as potentially hazardous and confine them.
- Use sqlite_version() and sqlite_sourceid() from SQL to confirm the exact runtime build/commit id. If the runtime reports an upstream source id that predates the fix commit, rebuild or update.
- After patching, re-run SBOM scans and CI pipeline checks to ensure new images and installers embed a fixed SQLite version and that no old copies remain in caches or third‑party bundles.
Risk analysis: strengths of the pubning gaps
Strengths- Upstream response was timely: SQLite maintainers committed a fix and followed up with related simplifications to the approach in branch updates. The fix is visible in upstream check-ins and in the source history. That makes a clear remediation target for packagers and product maintainers.
- Distribution vendors responded and published patched packages and errata. This gives administrators a standard package-based mitigation path for many systems.
- Detection and protection signatures were rapidly endors — useful to block or flag exploit attempts against public-facing services while remediations are deployed.
- Static linking and vendor-vendored amalgamations remain the largest operational problem: these require source-level rebuilds of every product that included sqlite3.c; OS updates alone will not fix those. For large organizations with many third‑party appliances or custom-built binaries, this can take weeks or months.
- Public discourse sometimes conflates DoS impact with remote code execution. Whi* in some exploit paths, it is not the default outcome; defenders should prioritize confirmed outcomes (DoS, data corruption) but remain alert for platform‑specific PoCs that expand the impact envelope.
- Vendor attestations that say “product X is not affected” are useful but not exhaustive. Customers must map SBOMs and product artifacts to attestations; a vendor statement about one artifact family (for example, a particular distribution image) does not automatically guarantee every vendor image, SDK sample, or appliance is clean. Hu
Recommendations for developers, packagers and integrators
- Treat third‑party library management as first‑class: maintain a registry of embedded versions and an action plan to rebuild after upstream security releases.
- In CI/CD, fail builds when the SBOM or installed libs contain known‑vulnerable sqlite versions (pre‑3.50.2).
- Avoid accepting or forwarding raw SQL fragments from untrusted inputs. Use parameterized queries and server-side prepared statements wherever possible.
- If you ship an appliance or SDK that includes a static sqlite amalgamation, plan an immediate rebuild and an update channel for customers; provide clear guidance and signed updates.
What to watch for next
- Watch your vendor security trackers and the SQLite repository for any subsequent follow‑ups. The SQLite upstream often issues mifications across different branches; follow both trunk and branch-3.xx relevant check-ins to make sure your platform’s applied fix matches upstream intent.
- Validate that all images, containers, and artifacts in registries have been rescanned and rebuilt; ephemeral artifacts in developer machines or CI caches are a frequent source of reintroduction. Add scanning and SBOM generation to your image-publishing step.
Conclusion — operational bottom line
CVE‑2025‑6965 is a serious, memory‑corruption vulnerability that impacts SQLite builds older than 3.50.2. The upstream fix is public and distributors have been issuing patches, but the real operational problem is discovery: many deployments run embedded or statically linked copies of SQLite that will remain vulnerable until their vendor or packager rebuilds and republishes updated artifacts. Prioritize (1) inventory, (2) patching OS packages, (3) rebuilding statically linked artifacts, and (4) short‑term compensations (disable raw SQL endpoints, sandbox, and monitor crash telemetry). The combination of upstream fixes, distribution updates, and your own artifact-level verification is the only reliable path to closing the window of risk.Source: MSRC Security Update Guide - Microsoft Security Response Center