The push to hard‑wire AI and cloud services into mainstream desktop operating systems has pushed privacy, hardware longevity, and user choice to the center of the conversation — and for a growing number of users the practical answer is clear: move to Linux now rather than accept a future of forced AI features, tighter hardware gates, and opaque data flows. A wave of recent commentary argues that Microsoft’s Copilot/Recall architecture and Apple’s expanded cloud processing policies meaningfully change the privacy calculus, while the end of Windows 10 support and Windows 11’s installation/account gates create a one‑two punch that makes Linux the most sensible alternative for many users.
Background / Overview
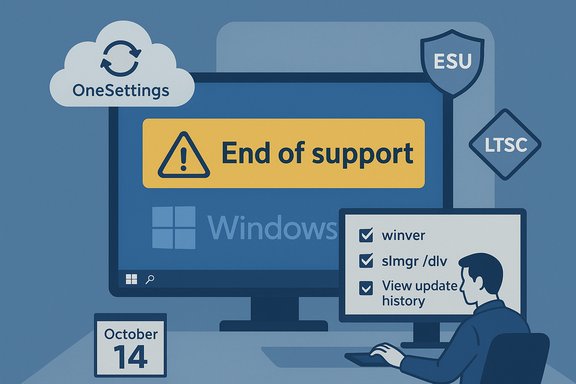
Windows 10’s official support window ended on October 14, 2025, which leaves unpatched installations exposed unless users upgrade, enroll in Extended Security Updates, or migrate to another OS. That deadline has been the practical inflection point behind renewed interest in Linux as a real desktop option rather than a hobbyist curiosity. At the same time, Windows 11’s hardware and account requirements — TPM 2.0, Secure Boot, newer CPU families, and a setup flow that nudges or requires a Microsoft account in consumer channels — have made upgrades expensive or impossible for many older but perfectly usable PCs.Apple’s macOS remains the polished alternative for users already deep in the Apple ecosystem, but its privacy posture and cloud dependencies are not absolute safeguards. Recent debates about Siri contractor practices, Apple Intelligence processing, and iCloud encryption nuance the “Apple = privacy” narrative and deserve careful scrutiny before relying on macOS as a privacy sanctuary.
Linux, by contrast, offers an explicit trade: more initial setup learning and hands‑on configuration in exchange for local control, minimal vendor telemetry by default, and the ability to run long‑term supported releases on older hardware. Modern desktop distributions have closed many usability gaps, and community migration guides make testing and migration straightforward.
Why Windows and macOS are being questioned now
Microsoft’s AI push: Copilot, Recall, and the cloud trade-off
Microsoft’s Copilot strategy stitched AI deeply into the Windows experience: Copilot is advertised to help with search, summaries, writing, and system features — and in doing so it draws on local context, history, and cloud‑based models. A related component, Microsoft Recall (and other context‑capture features), has raised specific concerns because it collects contextual data about what the user does and, at least initially, had implementation and storage questions that alarmed privacy advocates. Observers warn that once context and personal data are routed to cloud services for model inference, it becomes subject to corporate control and legal access patterns that differ from strictly local use. That cloud boundary is the core privacy worry: when data leaves your device, you lose direct control.Important nuance: Microsoft has iterated on storage and security models for these features, and some data remains local or encrypted in transit and at rest under certain settings. Still, the design of a cloud‑native assistant that mines personal context is a structural change in how operating systems handle user data — and for many that change is unacceptable. Community writeups and migration pieces treating Copilot and Recall as risk multipliers for privacy are increasingly common.
Apple’s “privacy” limitations
Apple’s marketing positions itself as a privacy proselytizer, and for many core scenarios it does better than competitors. Yet Apple’s own policies and product architecture reserve broad rights: the company documents how certain categories of data may be processed, shared with third parties, or used for service delivery. Whistleblower reporting from contractor review programs showed that voice assistant data (Siri) sometimes included extremely sensitive recordings and that human inspection was part of quality‑control loops — a practice that undercut customers’ assumptions of privacy for all voice data. Apple’s newer “Apple Intelligence” frameworks and private cloud processing blur the line between local safeguards and cloud‑assisted features, meaning some personal content will be processed off device, which requires trust in Apple and its subcontractors.Put simply: Apple’s model is not “no one can see” — it’s “Apple and vetted processors can see or process when needed.” That’s materially different from local‑first models Linux users often prefer, and it should change how privacy‑focused users think about trust and isolation.
The hardware and account gates
Windows 11’s emphasis on TPM, Secure Boot, and certain processor families means many perfectly functional machines are excluded from a Microsoft‑supported upgrade. Meanwhile, Out‑Of‑Box Experience changes that make purely local accounts harder to create push users toward cloud identities. For those who want to keep all activity offline or avoid tying their device to an online profile, these installation and policy changes are a strong incentive to consider alternatives that respect local control by default — and Linux distributions do.Why Linux is the practical alternative (strengths and real, verifiable benefits)
1) Local control and privacy by default
- Linux distributions generally allow creation of fully local user accounts during installation, with no forced cloud tethering.
- The open‑source model means system code, configuration, and telemetry (where present) are auditable, forkable, and removable.
- Community norms and tooling favor minimizing surprise outbound data flows.
2) Extended hardware life and cost savings
- Many desktop Linux distributions run comfortably on machines that fail Windows 11 checks.
- Lightweight desktop environments (Xfce, MATE, LXQt) and distros (Lubuntu, Linux Lite, Puppy, and lightweight spins) are designed to run on low‑RAM, older CPUs.
- There are no per‑device licensing fees for most desktop distributions, reducing TCO for households and small organizations.
3) Performance and modularity
- Linux installations can be minimal and modular; you choose what runs.
- Many users report faster boot times, lower idle RAM usage, and cooler operation on older notebooks after migrating.
- Package managers and reproducible repositories make software delivery predictable and auditable.
4) A much more flexible update model
- Choose LTS channels or rolling releases depending on your needs.
- Apply updates on your schedule, or configure unattended security patches only.
- Snapshot tools (Timeshift and others) provide safe restore points that make upgrades reversible and low‑risk.
5) Growing gaming and software compatibility
- Valve’s Proton and the broader Wine ecosystem have dramatically improved the ability to run Windows games on Linux.
- Many single‑player and indie titles run well; SteamOS/Proton efforts and the Steam Deck have accelerated vendor testing and fixes.
- Caveat: anti‑cheat and kernel‑level protections remain a blocker for some competitive titles; check compatibility on a per‑title basis.
The counterpoints: real risks and practical drawbacks
Linux is not a one‑size‑fits‑all panacea. Responsible migration planning requires acknowledging the real limitations.- Application parity: Professional suites like Adobe Creative Cloud, some specialized audio/video production tools, and industry‑specific Windows apps may not have full Linux equivalents. Workarounds include cross‑platform web apps, native alternatives, Wine, Proton, or a Windows VM for a limited set of tasks.
- Anti‑cheat and multiplayer: Titles that rely on kernel‑level anti‑cheat systems may refuse to run. Some anti‑cheat providers offer Linux support, but publisher adoption is inconsistent. Verify critical game titles before committing.
- Peripheral and vendor drivers: Very new Wi‑Fi chips, scanner/printer suites, fingerprint readers, and docking station power management can require vendor drivers not always available on day one for Linux. Test with a Live USB before reinstalling.
- Enterprise management: Corporate environments using Active Directory, Intune, and Windows‑centric compliance tooling may not allow employee devices to move to Linux without IT support and policy changes. Enterprise migrations require planning and tooling investments.
- Learning curve: While many desktop distros avoid the terminal for daily use, some troubleshooting still invites command‑line steps. Expect a short learning period and leverage community forums and vendor docs.
A practical migration playbook (step‑by‑step)
- Backup everything first
- Full disk image plus separate copy of documents/media. Verify backups are readable.
- Test with a Live USB
- Create a bootable Live USB for Ubuntu, Linux Mint, Zorin OS, or another friendly distro.
- Boot “Try without installing” and verify Wi‑Fi, display scaling, audio, webcam, and printer basics.
- Check the heavy hitters
- Verify the most important apps and games: native Linux versions, web apps, Wine/Proton compatibility, or VM feasibility.
- Use ProtonDB and community reports for gaming checks.
- Choose an install strategy
- Dual‑boot to keep Windows while you migrate gradually, or erase the disk for a clean install once confident.
- If you dual‑boot, suspend BitLocker and disable Fast Startup before resizing partitions.
- Verify installers and media
- Download the distro ISO and verify the SHA256 checksum before writing to USB. Corrupted or tampered ISOs are a real risk.
- Make a rescue plan
- Create recovery media for both OSes, and enable Timeshift snapshots after install so you can roll back easily.
- Post‑install steps
- Enable proprietary drivers where needed (NVIDIA GPU, printer bundles).
- Set up firewall, automatic security updates per the distro’s recommendations, and Timeshift.
- Keep a short‑term fallback
- Run legacy Windows apps in a lightweight Windows VM or keep a Windows partition for anything mission‑critical until you’re fully comfortable.
Verifying the major technical claims (what’s provable and what needs caution)
- Windows 10 end of support date (October 14, 2025) is an official, verifiable lifecycle milestone and the central factual driver behind many migration decisions. Treat this date as definitive when planning post‑EOL strategies.
- Windows 11 hardware requirements (TPM 2.0, Secure Boot, CPU generations) and OOBE account changes are observable in Microsoft’s released builds and public Insider commentary; hardware gating has materially limited upgrades for certain systems. This is verifiable in Microsoft documentation and widely reported testing.
- Microsoft Copilot/Recall raises privacy questions that are technically grounded (data leaving the device, cloud model inference, and potential access by vendor processes). Specific claims about insecure local storage at launch or exact internal practices should be treated carefully and cross‑checked against Microsoft statements and change logs. Some earlier implementation choices prompted backlash; later changes improved encryption and storage practices. Where press reporting alleges insecure defaults, treat those as reported incidents and verify against vendor corrections.
- Apple’s Siri contractor reviews and the broader Apple Intelligence/cloud processing model are factual events in the public record; reporting established that human review occurred and that some off‑device processing happens. That does not mean Apple broadly misuses user data by default, but it does mean trust assumptions about total local privacy are overstated. Anyone making decisions on privacy should weigh Apple’s promises against these documented practices.
Who should switch now — and who should wait
Switch now if:- Your PC is blocked from Windows 11 by hardware checks and you want a supported, secure OS without buying new hardware.
- Privacy and local control are top priorities and you’re willing to learn a bit of system management.
- Your daily apps are web‑based, cross‑platform, or have Linux equivalents, or you can run a small set of Windows apps in a VM.
- You rely on proprietary, Windows‑only professional apps or vendor‑specific drivers with no workable Linux alternative.
- Competitive multiplayer gaming that requires kernel‑level anti‑cheat is essential and the specific titles you play have no Linux path yet.
- Your device is company‑managed and corporate policy requires Windows/Intune/Group Policy compliance.
Final analysis: why this moment favors Linux — and the realistic case for a switch
Two hard forces have converged: a firm end‑of‑support deadline for Windows 10, and an ecosystem trend that embeds cloud‑native AI services and account linkages deeper into mainstream desktop OSes. For users with older hardware, strict upgrade gates, and high privacy expectations, Linux offers a practical, tested, and cost‑effective escape hatch. Modern distributions have reduced the friction dramatically — Live USBs, polished installers, and migration assistants make testing trivial and reversible.That said, Linux is not a universal cure: application compatibility, anti‑cheat issues, and vendor driver gaps are real constraints. The safest path for most is incremental: test, dual‑boot, migrate non‑critical machines first, and retain a Windows image for exceptional cases. When done deliberately, switching to Linux can restore years of usable life to older devices, reduce exposure to opaque cloud processing, and put control back in the hands of users.
In short: if you value privacy, local control, and stretching hardware life — and you’re willing to take a planned, stepwise approach — now is a sensible time to try Linux. The tools, documentation, and community support exist to make that switch low‑risk and reversible, and the hard calendar pressures around Windows 10’s lifecycle make testing Linux a responsible planning step for virtually every Windows 10 user.
Acknowledgement: some vendor claims and internal product‑design decisions evolve rapidly; where public vendor statements or direct documentation conflict with press reporting, treat the latter as reporting and seek direct vendor confirmation before making irreversible decisions in enterprise or regulated environments.
Source: How-To Geek Now's the Best Time to Ditch Windows and Mac for Linux