Microsoft’s short answer — that “Azure Linux includes this open‑source library and is therefore potentially affected” — is an authoritative, product‑level attestation, but it is not a technical guarantee that no other Microsoft product could contain the same vulnerable Linux kernel code; operators must treat Azure Linux as a confirmed carrier while performing artifact‑level verification across other Microsoft‑distributed kernels and images. rview
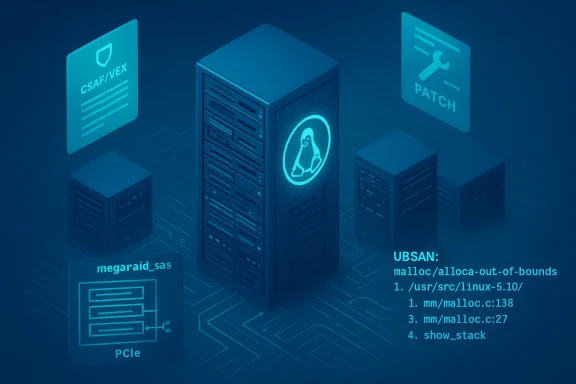
CVE‑2025‑38239 is a Linux kernel vulnerability affecting the SCSI megaraid_sas driver. The bug manifests as an invalid node index that can induce an out‑of‑bounds access when DRAM interleaving is enabled, producing UBSAN (Undefined Behavior Sanitizer) traces and kernel instability during megasas IRQ/vector allocation. Upstream kernel maintainers merged a small, surgical fix into stable kernel trees (for example, 6.1 and 6.6 stable branches), and multiple distributors have since mapped the fix into their errata.
The practical question posed by many operators is not only “what is the bug” but “which of my products are affected?” Microsoft’s Security Response Center (MSRC) pages for Linux CVEs frequently include this one‑line FAQ: “Is Azure Linux the only Microsoft product that includes this open‑source library and is therefore potentially affected?” followed by a statement that Azure Linux was inspected and that Microsoft began publishing CSAF/VEX attestations in October 2025, with a commitment to update CVE mappings if additional Microsoft products are identified. That phrasrefully.
This feature unpacks the technical details of CVE‑2025‑38239, explains precisely what Microsoft’s Azure Linux attestation means, cross‑references vendor trackers and upstream commits to verify the technical claims, and provides practical verification and remediation steps for operators running Azure, WSL, Marketplace images or other Microsoft‑supplied artifacts.
SUSE’s update notes explicitly mention scsi: megaraid_sas: Fix invalid node index as one of the git-fixes included in their kernel errata, which is a straightforward confirmation that the vendor took the upstream stable patch and packaged it for their customers.
Together, these independent sources corroborate the technical facts reported in the CVE: the buggy path, the UBSAN symptom, where the crash occurs, and that a specific upstream patch was merged and distributed.
Multiple independent community analyses and operational explainers emphasize the same nuance: treat the MSRC attestation as authoritative for Azure Linux, and treat the absence of attestations for other Microsoft artifacts as absence of attestation, not proof of absence. In plain terms: Azure Linux is the only Microsoft product Microsoft has publicly attested so far to include the implicated upstream component — but that does not conclusively prove other Microsoft products are free of it.
That’s why the operational recommendation is simple and robust: act on Microsoft’s VEX/CSAF attestations for Azure Linux immediately, but also run artifact‑level discovery and verification across other Microsoft‑supplied images in your fleet. Treat attestations as actionable confirmation, and missing attestations as unverified artifact until you confirm otherwisry and final verdict
Microsoft’s public statement is helpful and actionable: it tells you exactly which Microsoft product has been audited and confirmed to include the vulnerable upstream code (Azure Linux). But operational security is artifact‑by‑artifact work. Treat the Azure Linux attestation as a confirmed hit; treat other Microsoft images and kernels as not yet attested and verify them using VEX/CSAF, SBOMs, or direct artifact inspection. That combination — acting on the vendor’s attestation while independently verifying other artifacts — is the defensible, low‑risk posture for protecting complex cloud and hybrid environments against CVE‑2025‑38239 and similar kernel vulnerabilities.
Source: MSRC Security Update Guide - Microsoft Security Response Center
CVE‑2025‑38239 is a Linux kernel vulnerability affecting the SCSI megaraid_sas driver. The bug manifests as an invalid node index that can induce an out‑of‑bounds access when DRAM interleaving is enabled, producing UBSAN (Undefined Behavior Sanitizer) traces and kernel instability during megasas IRQ/vector allocation. Upstream kernel maintainers merged a small, surgical fix into stable kernel trees (for example, 6.1 and 6.6 stable branches), and multiple distributors have since mapped the fix into their errata.
The practical question posed by many operators is not only “what is the bug” but “which of my products are affected?” Microsoft’s Security Response Center (MSRC) pages for Linux CVEs frequently include this one‑line FAQ: “Is Azure Linux the only Microsoft product that includes this open‑source library and is therefore potentially affected?” followed by a statement that Azure Linux was inspected and that Microsoft began publishing CSAF/VEX attestations in October 2025, with a commitment to update CVE mappings if additional Microsoft products are identified. That phrasrefully.
This feature unpacks the technical details of CVE‑2025‑38239, explains precisely what Microsoft’s Azure Linux attestation means, cross‑references vendor trackers and upstream commits to verify the technical claims, and provides practical verification and remediation steps for operators running Azure, WSL, Marketplace images or other Microsoft‑supplied artifacts.
 What CVE‑2025‑38239 actually is
What CVE‑2025‑38239 actually is
Technical summary
- Component: Linux kernel SCSI driver — megaraid_sas (megasas subsystem).
- Symptom: UBSAN-detected array-index-out-of-bounds triggered when the driver requests and maps MSIX interrupt vectors; on certain hardware/configurations (DRAM interleave), an index value becomes -1 and is used to index a cpumask array, producing an out‑of‑bounds access and kernel oops. The trace shown in public advisories includes the megasas_alloc_irq_vectors function and the topology.h UBSAN complaint.
- Upstream response: A targeted validation/bounds check to prevent invalid node indices; patch backported to several stable kernel branches (announced into the stable-queue and picked up by distribution maintainers).
Why the risk is primarily availability
The bug is local and driver/hardware dependent. In most public advisories the impact is categorized as denial‑of‑service/instability rather than clear remote code execution. Triggering requires conditions such as specific PCI device behavior, the megaraid_sas module being built/loaded, and DRAM interleave or similar topology that exposes an invalid node computation. This combination makes large‑scale remote exploitation less likely, but for affected hosts the outcome can be immediate kernel crashes or persistent unreliability. Vendor trackers and distro advisories reflect that availability‑centric profile.How the upstream and vendors verified and fixed the issue
Upstream kernel maintainers merged a small patch titled “scsi: megaraid_sas: Fix invalid node index” into stable trees; the kernel stable announcement carried the patch into branches used by many downstream vendors. Distribution vendors (SUSE, Red Hat, Debian, Oracle Linux, Ubuntu, etc.) tracked the upstream fix and released patched kernel packages or backports. Public vulnerability trackers (NVD, Debian security tracker, Oracle CVE pages) list the CVE and map it to the upstream message and stable commits.SUSE’s update notes explicitly mention scsi: megaraid_sas: Fix invalid node index as one of the git-fixes included in their kernel errata, which is a straightforward confirmation that the vendor took the upstream stable patch and packaged it for their customers.
Together, these independent sources corroborate the technical facts reported in the CVE: the buggy path, the UBSAN symptom, where the crash occurs, and that a specific upstream patch was merged and distributed.
What Microsoft’s FAQ line means — prect’s public wording on MSRC CVE pages for Linux-code CVEs typically follows the pattern: “Azure Linux includes this open‑source library and is therefore potentially affected.” That is an inventory attestation for Azure Linux: Microsoft has inspected the Azure Linux product artifacts (kernel builds shipped as part of Azure Linux) and found the implicated upstream component present there. Accordingly, Azure Linux is a confirmed product to prioritize for remediation.
But that wording is not an exclusivity certificate. It does not assert that no other Microsoft product or image contains the same upstream code. Microsoft explicitly says it will publish CSAF/VEX attestations (machine‑readable product‑by‑product attestations) beginning with Azure Linux in October 2025 and that it will update the CVE mapping if additional products are identified. The phrasing is pragmatic and phased — it tells you what Microsoft checked and confirmed, not what Microsoft exhaustively checked and excluded.Multiple independent community analyses and operational explainers emphasize the same nuance: treat the MSRC attestation as authoritative for Azure Linux, and treat the absence of attestations for other Microsoft artifacts as absence of attestation, not proof of absence. In plain terms: Azure Linux is the only Microsoft product Microsoft has publicly attested so far to include the implicated upstream component — but that does not conclusively prove other Microsoft products are free of it.
Cross‑validation: key claims and independent evidence
- Claim: CVE‑2025‑38239 affects megaraid_sas and produces a UBSAN array-index-out-of-bounds.
Verification: The NVD entry and Debian security tracker record the UBSAN output and the exact trace (megasas_alloc_irq_vectors, topology.h array index -1). Independent vendor trackers (Oracle’s CVE repository, Rapid7, Wiz) reproduce the same technical description. - Claim: Upstream patch titled “scsi: megaraid_sas: Fix invalid node index” was added to stable kernel trees.
Verification: Linux stable commits / stable‑queue announcements and spinics mailings confirm the patch was added to 6.1‑stable and 6.6‑stable trees and available in the stable queue. Distributors subsequently included fixed kernels in their errata. - Claim: Microsoft’s MSRC wording confirms Azure Linux includes the implicated component and that Microsoft began publishing CSAF/VEX attestations in October 2025.
Verification: Microsoft’s MSRC blog and public announcements describe a phased rollout of machine‑readable VEX/CSAF attestations starting with Azure Linux on October 22, 2025; MSRC CVE pages reflect the same FAQ pattern and link to the VEX program commitment.
Answering the user’s question directly — careful, actionable response
Is Azure Linux the only Microsoft product that includes this open‑source library and is therefore potentially affected by CVE‑2025‑38239?- Short, vendor‑attested answer: Yes — Azure Linux is the only Microsoft product Microsoft has publicly attested so far to include the implicated upstream component. Microsoft’s public attestation is an authoritative inventory statement for Azure Linux.
- Short, operational answer for defenders: No — not necessarily. oduct‑scoped, not an exclusivity guarantee. Other Microsoft artifacts (WSL kernels, Azure Marketplace VM images, AKS node images, container base images, specialized kernel builds used by platform services) could include the same upstream code depending on the kernel version and build configuration; those artifacts must be verified independently until Microsoft publishes a VEX/CSAF attestation for them or explicitly lists them as not affected.
Practical verification and mitigation steps (recommended immediate actions)
Below are prioritized, practical steps you should run across your estate to verify exposure and remediate where necessary.1. Prioritize Azure Linux images (immediate)
- If you run Azure Linux (the Microsoft‑maintained distro formerly known as CBL‑Mariner), follow Microsoft’s published guidance and VEX/CSAF attestations for the CVE and install the updated kernel packages or images Microsoft provides. Microsoft explicitly maintains and updates Azure Linux and will publish VEX files indicating the exact status (Known Affected / Fixed).
2. Inventory Microsoft‑supplied artifacts (next 24–72 hours)
- Enumerate the Microsoft‑provided images and kernel artifacts in your environment:
- Azure Marketplace VM images you consume
- AKS node images and nodepool definitions
- WSL2 kernels distributed via Microsoft updates or the Microsoft Store
- Container base images from Microsoft registries that you run/rely on
- Any Microsoft‑maintained appliance or image used in managed services
- For each artifact, confirm the kernel version/build and whether megaraid_sas is present (module built-in or available). If you cannot verify, treat the artifact as Under Investigation until confirmed. The file search results and community guidance stress artifact‑level verification as the safe posture.
3. Use VEX/CSAF where available (automate)
- Ingest Microsoft’s CSAF/VEX feed for Azure Linux into your vulnerability management pipeline. The VEX files contain machine‑readable attestations that specify which product artifacts are Known Affected, Not Afrosoft started publishing these attestations in October 2025 as part of a phased rollout. Automating VEX ingestion will rapidly triage Azure Linux assets for you.
4. If you operate WSL2 or custom kernels, validate directly
- WSL2 uses a Microsoft-maintained kernel build in many Windows installs; whether that kernel includes megaraid_sas depends on the build configuration Microsoft used. Do not assume WSL2 is unaffected; verify the kernel configuration or SBOM for the specific WSL kernel binary in your environment. Community guidance notes explicitly that WSL2 and other Microsoft kernel artifacts are separate artifacts that require their own checks.
5. Patch and verify (apply vendor packages)
- For all impacted systems where megaraid_sas is present and the kernel version falls within affected ranges, apply the vendor‑supplied kernel update (distribution package or vendor image update) and reboot as required. Confirm the kernel now contains the stable commit or the vendor‑released fixed package version referenced in vendor advisories (Debian tracker, SUSE errata, Red Hat errata, Oracle CVE page etc.).
6. Monitor for kernel oops and related telemetry
- Watch host telemetry (dmesg, kernel oops logs, crash reports) for the UBSAN trace shown in public advisories (topology.h array-index-out-of-bounds with megasas_alloc_irq_vectors). If you see such traces on production hosts, treat them as high priority and perform a forensic capture before patching if you need to preserve evidence.
Why the attestation‑vs‑exclusivity nuance matters in practice
Large vendors ship many artifacts: VM images, WSL kernels, container base images, Marketplace appliances, managed node images for Kubernetes, and bespoke kernel builds used in specialized services. The presence of a vulnerable upstream source in any of those artifacts is a property of the artifact’s build inputs (kernel commit, config, and modules included) — not of the vendor organization as a whole. Microsoft’s attestation for Azure Linux confirms only the inventory work done to date for that specific product family. Assuming that a lack of attestation equals safety is risky; the community and expert analyses on this point are unanimous.That’s why the operational recommendation is simple and robust: act on Microsoft’s VEX/CSAF attestations for Azure Linux immediately, but also run artifact‑level discovery and verification across other Microsoft‑supplied images in your fleet. Treat attestations as actionable confirmation, and missing attestations as unverified artifact until you confirm otherwisry and final verdict
- Technical severity: CVE‑2025‑38239 is a kernel driver bug that produces out‑of‑bounds access and is primarily rated for availability impact; upstream fixes are merged and distributors have issued errata. Independent trackers corroborate the technical details. (nvd.nist.gov)
- Microsoft product mapping: Microsoft has publicly attested that Azure Linux includes the implicated open‑source library and is therefore potentially affected, and Microsoft began publishing machine‑readable VEX/CSAF attestations in October 2025, starting with Azure Linux. This makes Azure Linux a confirmed prioritization target.
- Exclusivity: The attestation is product‑scoped. It is not proof that no other Microsoft product includes the code. Other Microsoft artifacts may still include the vulnerable kernel code; they require artifact‑level inspection and verification.
Closing recommendations (concise checklist)
- Prioritize patching of Azure Linux images per Microsoft’s VEX/CSAF attestation.
- Inventory all Microsoft‑supplied artifacts in your estate (WSL kernels, Marketplace images, AKS node images, container base images). Verify kernel builds and module presence.
- Ingest Microsoft’s VEX/CSAF feed to automate triage for Azure Linux and watch for updated attestations for other products.
- Apply vendor patches (upstream stable commits or distribution packages) and reboot as required; validate the fix is present by checking the package changelog or kernel commit list.
- If you cannot immediately patch, increase monitoring for kernel oops, restrict access to hosts that can load megaraid_sas, and plan a short maintenance window to remediate.
Microsoft’s public statement is helpful and actionable: it tells you exactly which Microsoft product has been audited and confirmed to include the vulnerable upstream code (Azure Linux). But operational security is artifact‑by‑artifact work. Treat the Azure Linux attestation as a confirmed hit; treat other Microsoft images and kernels as not yet attested and verify them using VEX/CSAF, SBOMs, or direct artifact inspection. That combination — acting on the vendor’s attestation while independently verifying other artifacts — is the defensible, low‑risk posture for protecting complex cloud and hybrid environments against CVE‑2025‑38239 and similar kernel vulnerabilities.
Source: MSRC Security Update Guide - Microsoft Security Response Center