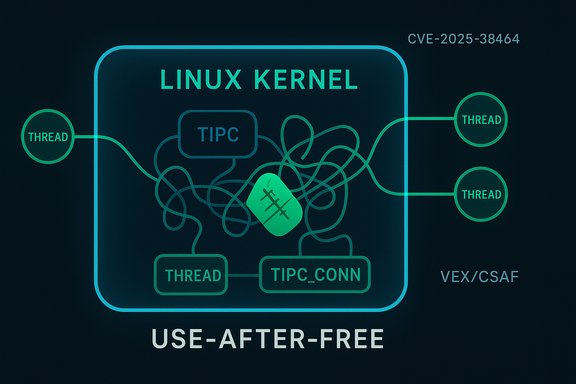
A high‑severity use‑after‑free in the Linux kernel’s TIPC subsystem (CVE‑2025‑38464) has been fixed upstream, and Microsoft’s Security Response Center (MSRC) has published a machine‑readable VEX/CSAF attestation that Azure Linux is known to include the implicated kernel component and is therefore potentially affected — but that attestation is product‑scoped and should not be read as proof that no other Microsoft artifact could contain the same vulnerable code.
TIPC (Transparent Inter‑Process Communication) is a kernel networking family designed for cluster‑wide IPC and high‑performance intra‑cluster messaging. It is implemented in the mainline Linux kernel and may be built in or as a module depending on kernel build configuration. The vulnerability tracked as CVE‑2025‑38464 is a classic use‑after‑free in the TIPC connection teardown path: a race between workqueue/netns teardown code paths can allow tipc_conn_close to operate on an already‑freed connection object. The issue was detected by syzbot and reproduced with KASAN traces; upstream maintainers applied a small, surgical fix to correct reference‑counting and locking order. Why this matters: kernel use‑after‑free defects can cause kernel oops/panics (availability impact) and, in some scenarios, be weaponized into more serious primitives by skilled attackers. For CVE‑2025‑38464 the immediate impact profile is availability and kernel stability; exploitation to full privilege escalation would require additional, platform‑specific conditions. Public trackers assigned this CVE an Important / High severity rating (CVSS in the 7.x–7.8 range depending on the database).
On a running Linux host (VM, bare metal, container host, WSL):
If you cannot find any kernel config or package metadata, treat the artifact as unknown and assume the component may be present until proven otherwise.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
TIPC (Transparent Inter‑Process Communication) is a kernel networking family designed for cluster‑wide IPC and high‑performance intra‑cluster messaging. It is implemented in the mainline Linux kernel and may be built in or as a module depending on kernel build configuration. The vulnerability tracked as CVE‑2025‑38464 is a classic use‑after‑free in the TIPC connection teardown path: a race between workqueue/netns teardown code paths can allow tipc_conn_close to operate on an already‑freed connection object. The issue was detected by syzbot and reproduced with KASAN traces; upstream maintainers applied a small, surgical fix to correct reference‑counting and locking order. Why this matters: kernel use‑after‑free defects can cause kernel oops/panics (availability impact) and, in some scenarios, be weaponized into more serious primitives by skilled attackers. For CVE‑2025‑38464 the immediate impact profile is availability and kernel stability; exploitation to full privilege escalation would require additional, platform‑specific conditions. Public trackers assigned this CVE an Important / High severity rating (CVSS in the 7.x–7.8 range depending on the database). What Microsoft published and what the wording actually means
Microsoft’s public advisory and CSAF/VEX attestation for this CVE map the upstream kernel component to the Azure Linux product family and state that Azure Linux “includes this open‑source library and is therefore potentially affected.” Microsoft also notes it began publishing machine‑readable CSAF/VEX outputs in October 2025 and that it will update CVE/VEX entries if further Microsoft products are identified as carriers of the same upstream component. That messaging is precise: it reports the inventory work Microsoft has completed so far and the plan to expand attestations. Key reading of Microsoft’s language:- Authoritative for the named product: The VEX/CSAF attestation is an explicit, machine‑readable statement that Microsoft inspected Azure Linux artifacts and found the implicated kernel code. Treat that attestation as definitive for the Azure Linux product family.
- Not a universal exclusivity guarantee: The attestation does not assert that no other Microsoft products ever include the same kernel component; it only reports what Microsoft has verified to date. The company explicitly commits to updating its VEX/CSAF outputs if additional Microsoft SKUs are found to contain the component. In practice that means the absence of a product name in Microsoft’s VEX feed is absence of attestation, not evidence of absence.
- Why vendors publish VEX product‑by‑product: Large vendors ship many artifacts (kernels, images, curated binaries) built with different kernel versions and CONFIG flags. Whether a particular kernel image contains the TIPC code is an artifact‑level property (it depends on the kernel tree, commit range and CONFIG_TIPC build flag). Microsoft’s phased rollout (Azure Linux first) is a pragmatic way to provide high‑quality, machine‑readable signals while inventorying the rest of the estate.
Cross‑checking the record (independent confirmations)
Multiple independent trackers and vendor advisories confirm the upstream technical details and the availability of fixes:- The National Vulnerability Database (NVD) records CVE‑2025‑38464 and includes the KASAN backtrace and description of the race in tipc_conn_close.
- Distribution security trackers (Debian, Amazon Linux, Red Hat, Ubuntu) have ingested the upstream fix and published package mappings or status updates for affected kernel branches. These trackers show which packaged kernels were patched or declared not affected.
- Microsoft’s VEX/CSAF JSON for the CVE lists Azure Linux kernel artifacts and the Microsoft remediation timeline (the VEX entry is visible in aggregated feeds and in CIRCL/third‑party mirrors). That VEX entry is the source of the Microsoft statement that Azure Linux includes the implicated component.
Is Azure Linux the only Microsoft product that includes the library and is therefore potentially affected?
Short, accurate answer: No — not necessarily. Microsoft has publicly attested that Azure Linux includes the vulnerable kernel code and must be treated as potentially affected; however, that attestation does not prove exclusivity across every Microsoft product or kernel artifact. Other Microsoft‑distributed artifacts that ship Linux kernels (for example the WSL2 kernel builds, linux‑azure kernel variants, Azure Marketplace images, AKS node images, or vendor appliances Microsoft distributes) could include the same upstream code depending on kernel version and build configuration. Microsoft said it will update VEX/CSAF entries if additional Microsoft products are identified as carriers. Why that nuance matters: kernel features like TIPC are build‑time choices. A vendor can enable or disable a subsystem via CONFIG_TIPC or compile it as a module. Two kernels from the same vendor can therefore differ greatly in what they include, and only artifact‑level inspection or explicit attestation can definitively answer whether a particular image is affected. Community analyses and Microsoft’s own documentation on the VEX/CSAF rollout make this point repeatedly.How to verify whether your Microsoft‑supplied instances are affected (practical checks)
You can determine carriage and patch status on a per‑host basis with a few, quick commands. These checks are intentionally artifact‑level (they inspect the running kernel or shipped image) — this is the correct approach when the vendor’s VEX feed does not yet list a given product.On a running Linux host (VM, bare metal, container host, WSL):
- Confirm kernel version:
- uname -r
- Check whether the TIPC module is present or built in:
- grepping kernel config (if available):
- zgrep CONFIG_TIPC /proc/config.gz
- or check /boot/config-$(uname -r): grep CONFIG_TIPC /boot/config-$(uname -r)
- if CONFIG_TIPC is built as a module, it will show:
- CONFIG_TIPC=m
- if built‑in:
- CONFIG_TIPC=y
- Check for a loaded tipc module (module name commonly "tipc"):
- lsmod | grep tipc
- modinfo tipc (modinfo will show if a tipc module is installed in /lib/modules)
- Inspect package changelog or vendor advisory mapping:
- Debian/Ubuntu: apt changelog linux-image-$(uname -r) | less
- RPM systems: rpm -q --changelog kernel | grep -i "CVE-2025-38464|tipc"
- For WSL2:
- WSL ships a Microsoft‑built kernel that is updated via Windows Update unless you configure a custom kernel. Check the WSL kernel version and config at the WSL kernel repository or with uname inside WSL. Microsoft’s WSL kernel source and configs are public and can be inspected in the WSL2‑Linux‑Kernel repo.
If you cannot find any kernel config or package metadata, treat the artifact as unknown and assume the component may be present until proven otherwise.
Recommended mitigations and remediation steps
- For Azure Linux customers:
- Prioritize installing the kernel update Microsoft published for the Azure Linux artifacts named in the VEX attestation. Use your normal patching pipeline and reboot into the patched kernel. Microsoft’s VEX entry and the Azure Linux update guidance provide the exact package versions and remediation date for those artifacts.
- For WSL2 users:
- If you rely on the default Microsoft‑supplied kernel, ensure Windows Update is applied (Microsoft distributes kernel updates through Windows Update) or follow Microsoft’s WSL guidance for updating to the latest Microsoft kernel releases in the WSL2 repo. If you run a custom WSL kernel, rebuild or reconfigure it to include the fix (or switch back to the Microsoft‑supplied kernel until you confirm the custom kernel is patched).
- For Azure Marketplace images, AKS node images, and other Microsoft‑distributed artifacts:
- Treat each image as an individual artifact. Consult the image vendor (Microsoft or third party) changelogs, and if necessary inspect the kernel config in the shipped image. Apply vendor kernel updates or replace with a patched image. If you manage your own images, rebuild them from patched kernel packages.
- Short‑term mitigations when patching is delayed:
- Restrict access to interfaces that can exercise TIPC (cluster networks, administration interfaces).
- Isolate potentially affected VMs/tenants and reduce attack surface by disabling TIPC if it is not required (rebuild kernel without CONFIG_TIPC or blacklist the tipc module).
- Collect and centralize kernel logs (journalctl -k, dmesg) and enable crash capture (kdump) to preserve evidence if an oops occurs.
- Monitor for KASAN or tipc‑related stack traces in kernel logs; these will indicate attempts to exercise the vulnerable paths.
Risk assessment — how likely and how bad
- Attack complexity and vector: CVE‑2025‑38464 is a local vulnerability (attack vector = local). An unprivileged local process or tenant‑adjacent workload that can manipulate TIPC state or network namespace teardown could trigger the race. For many traditional cloud configurations the exposure is limited but multi‑tenant hosts and managed environments with untrusted guest workloads increase the operational risk.
- Impact: immediate impact is availability (kernel WARN, oops, panic). The NVD entry and distro advisories classify the issue as Important/High due to the combination of local vector and potential high impact on confidentiality/integrity/availability in worst cases. Real‑world exploitation to RCE remains nontrivial and would be platform and timing specific; defenders should treat the vulnerability as high priority for patching, especially in multi‑tenant or cloud host contexts.
Policy and automation recommendations for enterprises
- Ingest Microsoft CSAF/VEX feeds automatically into your vulnerability management and SBOM tooling. VEX is designed for machine processing and helps eliminate false positives by indicating which product artifacts were actually inspected and what their status is. Microsoft’s VEX rollout started with Azure Linux; continue to monitor for other Microsoft attestations as inventory expands.
- Use artifact‑level checks as the authoritative source of truth. Don’t rely solely on vendor product lists; verify running kernels and image metadata (commands given above).
- Prioritize remediation by exposure and tenant model:
- Highest: multi‑tenant hosts, hypervisor guests with exposure to host‑exposed kernel subsystems.
- Medium: servers that host untrusted workloads or that are network‑adjacent to untrusted tenants.
- Lowest: single‑tenant desktops or VMs with no untrusted local workloads and no TIPC usage — still verify artifact though.
- Track distribution vendor advisories and stable kernel backports (Debian, Ubuntu, Red Hat, Amazon Linux) because vendors frequently backport fixes into maintained kernel branches; mapping by commit ID is more reliable than version number alone.
Notable strengths and potential risks in Microsoft’s VEX approach
Strengths:- Machine‑readable attestations reduce noise and give automated triage systems clear signals about which Microsoft products were inspected and what their status is. Microsoft’s VEX pilot (Azure Linux first) is a pragmatic approach to improve transparency.
- Mapping CVEs to product artifacts enables deterministic decisioning for defenders running those specific images.
- Phased coverage implies gaps: a single product attestation is not an exhaustive scan of all Microsoft artifacts. The absence of a product name in VEX is not a guarantee the product is unaffected; it may simply mean Microsoft hasn’t finished inventory for that product. Enterprises must not over‑rely on the current VEX coverage alone.
- Artifact variance: Microsoft and other large vendors publish many kernels and images built with different config flags; this variability means artifact‑level inspection remains essential even with VEX in place.
Conclusion
CVE‑2025‑38464 is a real kernel use‑after‑free in the TIPC subsystem with fixes available upstream and backported by multiple distributions. Microsoft’s published VEX/CSAF attestation that Azure Linux includes the implicated component is authoritative and means Azure Linux customers should prioritize applying the Azure Linux kernel updates identified in Microsoft’s VEX metadata. However, that attestation should not be read as proof that no other Microsoft product ever contains the same code: the VEX entry documents what Microsoft has completed inventorying so far and the company will update the attestation set as inventory expands. Operators must therefore perform artifact‑level checks — inspect kernel configs, modules and package changelogs — for every Microsoft‑supplied kernel artifact in their environment, apply vendor or upstream kernel updates, and apply short‑term mitigations where immediate patching is not possible.- Immediate checklist:
- Confirm whether a host’s kernel includes TIPC (config or module checks).
- Map kernel package to upstream commit or vendor changelog to verify whether the fix is present.
- Apply vendor kernel updates/reboots for Azure Linux and any other affected images.
- If unsure, restrict TIPC exposure and isolate the host until remediation is applied.
Source: MSRC Security Update Guide - Microsoft Security Response Center