Upwind’s arrival in the Microsoft ecosystem marks a deliberate push to make runtime-first cloud security a native option for Azure customers — a move that bundles runtime detection, container and registry scanning, posture management, and compliance controls into a single, Marketplace‑transactable offering and folds third‑party runtime telemetry into Azure’s operational model.
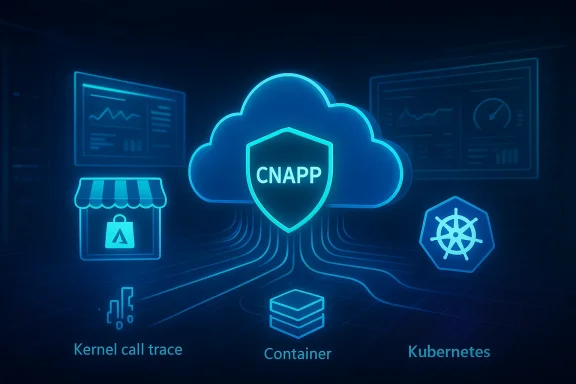
Cloud security historically split into two distinct worlds: slow, periodic posture assessments (CSPM/IaC scanning) and host-level protection that depended on agents (EDR/CWPP) or occasional registry scans. Upwind has built a platform that deliberately bridges those gaps with a runtime-first approach — combining live telemetry, eBPF‑powered sensors, and agentless scanning into a unified CNAPP-style product that is now listed and transactable on Microsoft’s Marketplace.
The commercial mechanics matter almost as much as the technical integration. Upwind’s Marketplace presence is not a simple listing: the company states the offering is transactable, co‑sell ready, and eligible to count toward a customer’s Azure consumption commitments (MACC), which materially shortens procurement friction for enterprises that already budget with Microsoft. Microsoft’s partner and Marketplace policies require specific technical and commercial validations for that status, and marketplace transactable offers are a key pathway for third‑party purchases to decrement a customer’s Azure Consumption Commitment.
For readers looking for the primary announcement and the immediate coverage, vendor materials and Marketplace pages show the Upwind offering and summarize the integration; community discussion and vendor press reprints mirror the same claims.
Microsoft’s own Defender for Cloud provides CSPM and agentless scanning natively for Azure, but third‑party vendors bring distinct runtime telemetry approaches and different detection models that customers may prefer for richer context or to address non‑Azure workloads in a multi‑cloud deployment. Upwind’s marketplace integration means customers can now choose that runtime telemetry without abandoning Microsoft vendor contracts or billing flows.
That said, prospective buyers must:
Marketplace transactable status removes a procedural barrier — but it doesn’t remove technical risk. Use the Marketplace convenience to accelerate trials and procurement, but keep the checklist above in hand before rolling any runtime control into production. For many organizations the payoff — fewer false positives, prioritized real‑world exploitability context, and tighter integration with Microsoft’s SOC stack — will be worth the work required to validate and tune the integration.
In short: Upwind plus Microsoft creates a practical, enterprise-friendly path to adopt runtime‑first cloud security inside Azure. Treat the Marketplace listing and partner badges as helpful enablers, not substitutes for rigorous PoV testing and an operational plan to manage telemetry, compatibility and post‑detection workflows.
Conclusion: runtime visibility is no longer optional. With Upwind now available through Microsoft’s Marketplace and integrated into Azure’s security fabric, organizations have a faster path to trial modern runtime defenses — but success will depend on careful validation, honest cost modeling, and clear operational playbooks that incorporate the new signals into the way your SOC and platform teams work.
Source: verdict.co.uk Upwind collaborates with Microsoft for enhanced runtime Azure security
 Background
Background
Cloud security historically split into two distinct worlds: slow, periodic posture assessments (CSPM/IaC scanning) and host-level protection that depended on agents (EDR/CWPP) or occasional registry scans. Upwind has built a platform that deliberately bridges those gaps with a runtime-first approach — combining live telemetry, eBPF‑powered sensors, and agentless scanning into a unified CNAPP-style product that is now listed and transactable on Microsoft’s Marketplace.The commercial mechanics matter almost as much as the technical integration. Upwind’s Marketplace presence is not a simple listing: the company states the offering is transactable, co‑sell ready, and eligible to count toward a customer’s Azure consumption commitments (MACC), which materially shortens procurement friction for enterprises that already budget with Microsoft. Microsoft’s partner and Marketplace policies require specific technical and commercial validations for that status, and marketplace transactable offers are a key pathway for third‑party purchases to decrement a customer’s Azure Consumption Commitment.
For readers looking for the primary announcement and the immediate coverage, vendor materials and Marketplace pages show the Upwind offering and summarize the integration; community discussion and vendor press reprints mirror the same claims.
What Upwind brings to Azure: a technical overview
Runtime telemetry, eBPF sensors, and agentless scanning
At the core of Upwind’s pitch is runtime visibility — actual, observable behaviour from running workloads rather than inference from build-time metadata or configuration snapshots. That visibility is delivered through two complementary techniques:- eBPF‑powered sensors that monitor Linux kernel events and decode runtime activity across containers, hosts, and serverless functions with low overhead.
- Agentless cloud scanners that query provider APIs and registries for large-scale posture, asset inventory, and image/registry metadata — enabling broad coverage without installing agents everywhere.
Integrated vulnerability and registry scanning (ACR, registries, SBOMs)
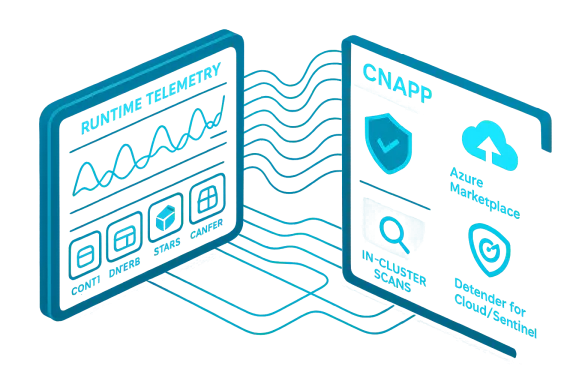
Upwind adds container image scanning that can operate in‑cluster and complements registry scanning such as Azure Container Registry (ACR) checks. The vendor positions these scan jobs to be faster and more resource‑efficient than conventional static scanning, and to provide runtime context for prioritizing truly exploitable vulnerabilities. That means image CVEs are scored alongside evidence of whether vulnerable code paths are actually executed in production.Posture, compliance frameworks and identity telemetry
The platform bundles CSPM‑style checks (benchmarks like CIS for AKS), compliance dashboards, and integrations with identity services like Microsoft Entra ID so customers can correlate identity events with runtime activity. Upwind’s Azure partner materials describe direct integrations with Azure audit logs, Defender for Cloud and Sentinel to enable unified incident context and a single pane for cloud and workload telemetry.Operational integration: Microsoft Marketplace, co‑sell and MACC eligibility
From an operational perspective, Upwind being transactable on the Azure Marketplace and claiming IP co‑sell readiness matters because it shortens procurement cycles, enables private offers, and — if correctly transacted via the Azure portal and eligible subscription — can decrement Azure Consumption Commitment (MACC) for customers. Microsoft’s IP co‑sell and Marketplace rules require partners to meet technical validation and offer type requirements before those benefits apply. Purchases that qualify for MACC decrement must follow specific checkout and billing paths to be counted.Why this move matters to enterprises
1) Faster procurement, smoother vendor consolidation
Being available as a Marketplace transactable offer lowers procurement friction for enterprises that already allocate Azure budgets. Instead of a separate vendor contract, purchases can often ride Microsoft’s billing rails, and private offers can be structured inside the portal — a tangible speed benefit for security teams under procurement timelines. However, customers must still confirm MACC eligibility on a per‑deal basis and use the right purchase flow.2) Reduced blind spots for modern cloud patterns
Serverless functions, ephemeral containers, and polyglot runtimes have historically created blind spots for security tooling. Upwind’s design claims to surface in‑use code, API calls, and system interactions — data often missing from build-time scanners — which lets teams find what’s actually being executed in production. For industries with sensitive data and regulatory needs (financial services, healthcare), that runtime evidence can materially change remediation priorities.3) A practical on‑ramp to unified observability and response
Integration with Microsoft Sentinel and Defender for Cloud aims to bring runtime signals into existing SOC workflows rather than forcing a parallel toolchain. The result should be quicker triage and less context switching for analysts who already rely on Microsoft tooling as a central hub. Microsoft Learn pages and Upwind partner materials both highlight this integration path.Industry context and competition
The CNAPP and cloud security markets are consolidating around platforms that can combine CSPM, workload protection, vulnerability management, and runtime detection. Upwind is one of several vendors trying to own the runtime layer and to differentiate through eBPF telemetry, while established players (including Microsoft Defender for Cloud, Wiz, Orca and others) offer varying mixes of posture, vulnerability scanning and runtime protection.Microsoft’s own Defender for Cloud provides CSPM and agentless scanning natively for Azure, but third‑party vendors bring distinct runtime telemetry approaches and different detection models that customers may prefer for richer context or to address non‑Azure workloads in a multi‑cloud deployment. Upwind’s marketplace integration means customers can now choose that runtime telemetry without abandoning Microsoft vendor contracts or billing flows.
Strengths: what Upwind + Microsoft delivers well
- Runtime fidelity: The combination of eBPF sensors and in‑cluster image scan jobs gives high‑resolution evidence of live behavior, which is crucial for prioritizing real risk.
- Operational convenience: Marketplace transactable listings, IP co‑sell readiness, and MACC‑eligible purchases remove real procurement friction for Azure‑first customers.
- Unified risk context: Correlating identity events, audit logs, posture checks and runtime signals into a single pane reduces alert noise and supports faster decision‑making.
- Multi‑cloud parity claims: Upwind has published releases claiming parity across AWS, GCP and Azure for runtime features — valuable for hybrid or multi‑cloud customers.
Risks, gaps and practical limitations
No single product is a silver bullet. The following are the highest‑impact risks and technical limitations organizations should evaluate:eBPF and platform compatibility
- Kernel and platform constraints: eBPF instrumentation depends on kernel features and capabilities. Customers with diverse Linux kernel versions, heavily controlled managed nodes, or certain hardened host configurations may face compatibility or functionality trade-offs. Organizations should validate kernel support matrices in their AKS/VM/host fleets before relying on eBPF features at scale.
Windows and non‑Linux workloads
- Visibility limitations for non‑Linux systems: eBPF is Linux‑centric. If an enterprise runs large Windows Server fleets or Windows containers, runtime coverage will be different; agents or alternate telemetry may still be required to secure those assets. Upwind’s Azure messaging emphasizes AKS, Azure Functions and Azure VMs with Linux coverage. Customers need to verify coverage for Windows workloads specifically.
Data volume, storage costs and SOC integration
- Telemetry scale: High-fidelity runtime telemetry can generate large volumes of data. Teams must account for ingestion, storage and SIEM costs (e.g., Sentinel billing) when feeding enriched events into analytics pipelines. This is a practical adoption cost that sometimes gets under‑estimated.
Vendor maturity and operational readiness
- Platform maturity: Upwind is a relatively newer entrant compared with long‑established security vendors and has experienced fast growth and product expansion. While rapid feature velocity is positive, customers should validate production stability, support SLAs, and integration behavior in their own staging environments. Some claims about market recognition and revenue growth are vendor‑reported; independent validation may lag vendor outreach. Flag any vendor‑provided growth percentages or customer counts as self‑reported unless verified through independent filings or analyst reports.
Compliance and procurement nuance (MACC caveats)
- MACC isn’t automatic: MACC decrement requires the correct Marketplace purchase flow (Azure portal checkout tied to eligible subscriptions) — web credit card flows or non‑portal purchases typically do not count. IT procurement must confirm the right path and validate with Microsoft or their reseller prior to relying on committed funds.
How to evaluate Upwind for your Azure estate: a short checklist
- Confirm which workload classes you need runtime visibility for (AKS, Azure Functions, Linux VMs, Windows VMs).
- Validate kernel and platform compatibility for eBPF on target hosts and managed Kubernetes node images.
- Run a proof‑of‑value that exercises image scanning, registry scanning (ACR), and a short incident workflow that sends telemetry into Sentinel.
- Quantify telemetry ingestion and SIEM costs for the expected retention window.
- Review procurement paths if you plan to apply MACC: ensure Marketplace transactions are completed through the Azure portal and tied to eligible subscriptions.
- Test identity and Entra integrations to ensure identity signals are mapped into your existing IAM and SSO processes.
The roadmap question: AI, identity, and internet exposure
Upwind has signalled future expansions to address identity protection, internet exposure and generative AI workloads. These are logical extensions — identity telemetry helps close detection loops around lateral movement and compromised service principals, internet exposure scanning maps external attack surfaces, and AI‑workload protections are increasingly relevant as models and agent‑style workloads become operational assets. BusinessWire and other vendor statements highlight emerging functionality for AI‑native traffic inspection and tracing LLM agent actions across call stacks. Buyers should treat these roadmapped capabilities as promising but subject to change, and ask for concrete implementation dates, test artifacts, and compliance implications before relying on them for high‑risk controls.Real customer and market signals
Independent coverage and vendor press releases converge on a few common themes: Upwind is growing quickly, it has raised significant funding, and hyperscaler partnerships are central to its go‑to‑market strategy. Recent funding announcements highlight both investor confidence and an aggressive expansion plan, including broader partnerships with cloud providers and ISV ecosystems. Those financial signals and partner badges are meaningful, but they are a complement to technical verification rather than a substitute for it. Organizations should validate PoV results and ask for references in similar regulated industries when considering Upwind for mission‑critical workloads.Practical deployment scenarios where Upwind adds clear value
- Financial services: High regulatory scrutiny and the need for forensic evidence of runtime operations make runtime telemetry and prioritized vulnerability context especially valuable.
- Healthcare: Runtime evidence can speed investigations and support HIPAA / data residency controls when combined with Sentinel and Defender.
- Digital‑native SaaS: Fast‑moving deployments with heavy use of serverless and containers benefit from continuous runtime detection and in‑cluster image scanning.
Verdict: a pragmatic addition to Azure security stacks — with caveats
Upwind’s Microsoft Marketplace entry is more than marketing; it reflects a broader market movement toward treating runtime telemetry as an operational requirement rather than an optional add‑on. For Azure‑native organizations, the ability to procure, onboard and route Upwind signals into existing Microsoft SOC tooling is a practical win that reduces friction and can speed time to value.That said, prospective buyers must:
- Validate technical compatibility (kernel, managed node images, Windows coverage).
- Account for telemetry scale and SIEM costs.
- Confirm MACC decrement mechanics with procurement (don’t assume all Marketplace purchases automatically decrement commitments).
- Treat vendor growth claims and roadmap promises as forward‑looking until independently validated in production PoVs.
Final guidance for WindowsForum readers and Azure security teams
If you are responsible for cloud security in an Azure environment, carve out time for a focused proof‑of‑value that exercises Upwind’s runtime detections, registry/image scanning against ACR, and integration into Sentinel workflows. Invite both security and platform engineering teams to the evaluation: runtime‑first detection changes remediation workflows and can surface new priorities that require platform‑level changes (image rebuilds, least‑privilege service principals, or runtime policy enforcement).Marketplace transactable status removes a procedural barrier — but it doesn’t remove technical risk. Use the Marketplace convenience to accelerate trials and procurement, but keep the checklist above in hand before rolling any runtime control into production. For many organizations the payoff — fewer false positives, prioritized real‑world exploitability context, and tighter integration with Microsoft’s SOC stack — will be worth the work required to validate and tune the integration.
In short: Upwind plus Microsoft creates a practical, enterprise-friendly path to adopt runtime‑first cloud security inside Azure. Treat the Marketplace listing and partner badges as helpful enablers, not substitutes for rigorous PoV testing and an operational plan to manage telemetry, compatibility and post‑detection workflows.
Conclusion: runtime visibility is no longer optional. With Upwind now available through Microsoft’s Marketplace and integrated into Azure’s security fabric, organizations have a faster path to trial modern runtime defenses — but success will depend on careful validation, honest cost modeling, and clear operational playbooks that incorporate the new signals into the way your SOC and platform teams work.
Source: verdict.co.uk Upwind collaborates with Microsoft for enhanced runtime Azure security