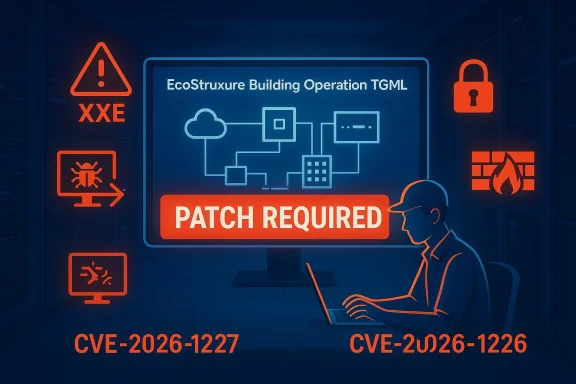
Schneider Electric has published an urgent security notice for EcoStruxure Building Operation (EBO) after researchers disclosed two high‑impact vulnerabilities—CVE‑2026‑1226 and CVE‑2026‑1227—that can be triggered by crafted TGML graphics files and may allow local file disclosure, denial‑of‑service, or the execution of untrusted code on Workstation and WebStation hosts.
EcoStruxure Building Operation (EBO) is Schneider Electric’s building management platform used to monitor and control HVAC, lighting, access, and other facility systems. It is widely deployed in commercial buildings, healthcare, data centers, transportation hubs, and other critical facilities where disruption or data loss has real operational consequences. Schneider Electric published a consolidated security notification (SEVD‑2026‑041‑02) describing multiple issues and identifying affected product branches and fixed builds.
CISA and several national cyber‑defense organizations republished or summarized Schneider’s advisory to increase visibility for asset owners and operators. Those agencies emphasize that organizations running EBO must treat these flaws as high priority and apply vendor patches or mitigations without delay.
Community and operator forums picked up the advisory quickly, and conversations in operational technology (OT) and bmunities reflect concern about attack vectors that rely on local user interaction or adjacent‑network access—typical threat paths for engineering workstations and operator consoles.
From the vendor’s description, the attack chain requires a user with some access to the Workstation (local or remote depending on deployment) to open or upload a crafted TGML file. Because XML External Entity (XXE) weaknesses allow an attacker-supplied XML payload to reference local filesystem or network resources, the primary risks are data exposure and triggering fault conditions in the parser or downstream components.
The vendor links both issues to TGML parsing and rendering logic—TGML being the platform’s graphics/design markup used in EBO projects—and recommends applying specific fixed builds that neutralize these parsing and processing weaknesses.
CISA and national cyber centers republished Schneider’s notice to emphasize the cross‑sector exposure and to encourage rapid mitigation across asset owners and integrators.
A note of caution: the vendor’s advisory provides the authoritative fix and exact package names/build numbers—when in doubt, use the vendor documentation included with the patch bundle and validate checksums and signatures on any downloaded files. Where the advisory refers to a mitigation (for example, EBO hardening guidelines), treat that guidance as complementary to patching, not as a substitute.
However, the weaknesses highlighted by these CVEs expose a recurring theme in OT/automation software: file parsing logic (graphics, project files, drivers) remains a high‑value attack surface because it routinely accepts structured content from contractors and engineers. Even though initial access often requires user action or local access, that requirement does not materially lower risk in real operations—engineering hosts are commonly reachable via VPNs, jump hosts, and shared media. The operational workflow around engineering project files is therefore the persistent systemic weakness.
Finally, while compensating controls can substantially reduce exposure, they are not a substitute for the vendor fixes. The only durable resolution is to apply the patches that modify the parsing behavior and close the unsafe code paths. Where organizations cannot immediately patch, layered mitigations (segmentation, MFA, strict file transfer policy, allowlisting) materially lower attack likelihood and impact.
Schneider’s advisory and the subsequent national republishing make clear that this is a time‑sensitive issue for any organization running EcoStruxure Building Operation Workstation or WebStation. Treat the affected hosts as critical assets: inventory them now, schedule a tested patch rollout, harden engineering workflows, and strengthen monitoring to reduce the chance that a single crafted TGML file could lead to data loss or operational disruption.
Source: CISA Schneider Electric EcoStruxure Building Operation Workstation | CISA
 Background
Background
EcoStruxure Building Operation (EBO) is Schneider Electric’s building management platform used to monitor and control HVAC, lighting, access, and other facility systems. It is widely deployed in commercial buildings, healthcare, data centers, transportation hubs, and other critical facilities where disruption or data loss has real operational consequences. Schneider Electric published a consolidated security notification (SEVD‑2026‑041‑02) describing multiple issues and identifying affected product branches and fixed builds.CISA and several national cyber‑defense organizations republished or summarized Schneider’s advisory to increase visibility for asset owners and operators. Those agencies emphasize that organizations running EBO must treat these flaws as high priority and apply vendor patches or mitigations without delay.
Community and operator forums picked up the advisory quickly, and conversations in operational technology (OT) and bmunities reflect concern about attack vectors that rely on local user interaction or adjacent‑network access—typical threat paths for engineering workstations and operator consoles.
What was disclosed: CVE‑2026‑1227 and CVE‑2026‑1226
CVE‑2026‑1227 — XML External Entity (XXE) weakness (CWE‑611)
Schneider reports an improper restriction of XML external entity reference vulnerability in EBO Workstation and WebStation that can be exploited when a local user uploads a malicious TGML graphics file. The issue can lead to unauthorized disclosure of local files, unintended interactions with the EBO system, or denial‑of‑service conditions if the XML parser processes external entity references. The vendor gives this cluster a high severity profile.From the vendor’s description, the attack chain requires a user with some access to the Workstation (local or remote depending on deployment) to open or upload a crafted TGML file. Because XML External Entity (XXE) weaknesses allow an attacker-supplied XML payload to reference local filesystem or network resources, the primary risks are data exposure and triggering fault conditions in the parser or downstream components.
CVE‑2026‑1226 — Improper control of generation of code / Code injection (CWE‑94)
The second issue Schneider disclosed is a code generation / code injection weakness that arises when maliciously crafted design content inside a TGML graphics file is processed by the application. Schneider warns this could “result in the execution of untrusted or unintended code within the application,” which elevates the potential impact to include local code execution on engineering hosts that process attacker‑controlled project or graphics assets.The vendor links both issues to TGML parsing and rendering logic—TGML being the platform’s graphics/design markup used in EBO projects—and recommends applying specific fixed builds that neutralize these parsing and processing weaknesses.
A technical look: how these flaws work (what operators need to know)
The TGML vector
TGML is used by EBO to store graphics and UI assets inside building‑management projects. Because TGML is a textual, structured format, it is parsed and rendered by the Workstation/WebStation components. When an application accepts TGML from user uploads or project imports and parses it with permissive XML handling and weak input sanitization, it can be exposed to classic XML and content‑parsing attacks: XXE, entity expansion, and crafted content that leads to unintended code paths during rendering. Schneider’s advisory explicitly ties both CVE‑2026‑1227 and CVE‑2026‑1226 to malicious TGML files.XXE (CVE‑2026‑1227) mechanics and consequences
An XXE weakness permits an XML document to include references that cause the parser to retrieve local files or external resources during processing, or to trigger expensive parsing operations. In practice for EBO, a crafted TGML file can cause the server or workstation process to read local files (exfiltration risk) or to allocate/unleash resources that lead to denial‑of‑service. The Schneider advisory lists unauthorized local file disclosure and DoS as realistic impacts. These are particularly sensitive in OT contexts where local files can include credentials, cached tokens, or configuration artifacts.Code injection (CVE‑2026‑1226) mechanics and consequences
Code generation or code injection vulnerabilities occur when content intended to define graphics or configuration is treated as executable instructions, or is unsafely injected into code generation or evaluation paths. The practical result can be execution of attacker‑controlled operations in the context of the application, which on a Windows engineering host often translates to arbitrary code execution at the privileges of the EBO process or user. Schneider labels this impact as “execution of untrusted or unintended code” and has issued fixes for it.Who’s affected — sectors and deployment patterns at risk
Schneider specifically calls out EBO Workstation and WebStation builds across the 6.x and 7.x maintenance lines—multiple build numbers are affected until patched. Because EBO is commonly used in sectors that operate critical and safety‑sensitive environments, the advisory explicitly lists widely critical sectors including commercial facilities, energy, government facilities, healthcare, IT, transportation, financial services, and critical manufacturing. That breadth means the vulnerability is not limited to a single vertical: any organization with EBO Workstation/WebStation in production or engineering environments should treat this as material risk.CISA and national cyber centers republished Schneider’s notice to emphasize the cross‑sector exposure and to encourage rapid mitigation across asset owners and integrators.
Vendor fixes and verified remediation steps
Schneider has published fixed builds addressing these issues. The vendor’s published remediation guidance enumerates specific patched builds for both the 7.x and 6.x branches:- For CVE‑2026‑1227 (XXE): apply the EBO Patch that updates Workstation/WebStation to 7.0.3.2000 (CP1) or 6.0.4.14001 (CP10) depending on your major version. The vendor package name referenced is “EcoStruxure Building Operation Patch v7.0” or “Patch v6.0” along with a readme that provides install instructions.
- For CVE‑2026‑1226 (code injection): apply the builds noted by Schneider—e.g., 7.0.2 for the 7.x branch and 6.0.4.7000 (CP5) for the 6.x branch—or the bundled patch that addresses both issues where available. Follow the vendor readme for ordering, prerequisites, and installation steps.
Immediate mitigations if you cannot patch right away
Schneider and government CERTs recommend immediate compensating controls for customers who cannot immediately apply the vendor fixes. These are pragmatic, operational mitigations that reduce the attack surface while you plan a tested patch rollout:- Implement strict access controls on Workstation and WebStation hosts; ensure only authorized engineers can upload or import project artifacts. Use strong, unique administrative accounts.
- Turn on and enforce multi‑factor authentication for EBO consoles where version support exists (EBO 7.0 or later). MFA reduces the risk of an attacker achieving the account access necessary to upload malicious TGML.
- Isolate BMS and engineering networks behind firewalls; do not expose EBO Workstation, WebStation, or Enterprise Server to the public Internet. Network segmentation is a foundational OT control recommended by Schneider and CISA.
- Limit file exchange vectors: prohibit or tightly control the use of removable media, shared network folders, and email attachments for transferring project files into the OT environment. Scan all imports for malicious content before touching engineering workstations.
- Increase monitoring and logging: look for anomalous TGML uploads, unexpected parser exceptions, process crashes, or unusual outbound file reads (local file access patterns) from Workstation/WebStation processes. Rapid detection will shorten dwell time.
Step‑by‑step patching checklist (recommended sequencing)
- Inventory: enumerate all EBO Workstation and WebStation hosts (including test and offline engineering laptops). Document versions, build numbers, and whether the node is connected to Enterprise Server.
- Backup: create full image and project backups for each host. Confirm recoverability before proceeding.
- Test: apply the vendor patch to a staging/test system that mirrors production. Validate project compatibility and third‑party driver behavior.
- Schedule: plan maintenance windows for staged rollout to production engineering hosts; coordinate with facilities and operations teams.
- Apply: follow Schneider’s readme instructions for the “EcoStruxure Building Operation Patch v7.0” or the equivalent v6.0 bundle for your branch. Where the vendor requires a specific sequence (Enterprise Server before Workstation, etc.), adhere to that order.
- Verify: post‑patch, validate project loading, UI rendering, scheduled control logic, and integration points (BACnet, Modbus, etc.). Check logs for parser errors or warnings.
- Monitor: increase log retention and monitoring in the next 30–90 days; watch for anomalous behavior that could indicate attempted exploitation.
Detection and incident response guidance
If you suspect exploitation or an attempted exploit, treat the incident as potentially high impact:- Isolate the affected host(s) from both OT and IT networks until containment is assured.
- Preserve volatile evidence: collect process memory, open file lists, and EBO application logs. Store copies on an isolated forensic server.
- Look for indicators of TGML misuse: recent or unexpecalformed TGML files, or parsing exceptions in the event logs. Also inspect the Workstation’s file access patterns for unauthorized file reads.
- Engage your vendor support and, where appropriate, national incident response contacts (CISA, regional CERT/CC) to coordinate forensic analysis and disclosure. These agencies have already republished Schneider’s advisory and can assist with broader situational awareness.
Why this matters: operational and strategic implications
- Attackers who achieve code execution or file disclosure on engineering workstations can pivot into adjacent OT systems. In building management, that pivot can impact temperature controls, access control timelines, or other safety‑relevant functions. The cross‑sector nature of the EBO installed base magnifies systemic risk.
- Even where the initial attack requires local access or user interaction, the practical attack surface for engineering workstations is large: contractors, integrators, and remote engineers regularly move project files, and shared engineering tools are a frequently abused vector in OT breaches. The community has flagged these operational patterns as ongoing risks in EBO deployments.
- From a compliance and resilience standpoint, organizations that delay remediation face not only operational downtime risk but also regulatory scrutiny if a successful exploitation leads to safety incidents, data loss, or service disruption in critical infrastructure sectors. National cyber centers are already amplifying the message to affected owners and operators.
Hardening checklist: beyond the immediate mitigations
- Enforce least privilege for engineering PCs: separate daily‑use workstations from engineering machines; disable internet browsing and email on engineering hosts where feasible.
- Apply application allowlisting for engineering processes and scripting tools to prevent arbitrary payloads from executing even if a parser flaw is present.
- Block or inspect TGML uploads at the perimeter where project import portals exist; if your environment allows it, disallow direct upload of TGML from untrusted sources.
- Adopt secure software development lifecycle (SSDLC) expectations with integrators: require code reviews and file‑format fuzz testing for any third‑party custom graphics or driver extensions.
- Maintain a prioritized inventory of OT software similar to IT asset management so you can rapidly identify affected systems when vendors publish advisories.
Cross‑referencing and verification notes
The core technical details, affected versions, and patched builds referenced in this article come directly from Schneider Electric’s SEVD‑2026‑041‑02 advisory. Independent confirmation and republication were made by national cyber centers and CISA, which republished the vendor’s advisory and summarized impacts for broader distribution. Vulnerability catalogs also index this advisory for tracking purposes. Operators should rely on Schneider’s published patch bundles and their own test procedures before applying updates in production.A note of caution: the vendor’s advisory provides the authoritative fix and exact package names/build numbers—when in doubt, use the vendor documentation included with the patch bundle and validate checksums and signatures on any downloaded files. Where the advisory refers to a mitigation (for example, EBO hardening guidelines), treat that guidance as complementary to patching, not as a substitute.
Practical recommendations for CISOs, OT managers, and integrators
- Immediate: inventory EBO hosts, prioritize patches for exposed systems, and implement network controls (segmentation, firewall rules) to isolate Workstation/WebStation hosts. Apply MFA to EBO administrative accounts where supported.
- Short term (days to weeks): schedule staged patch deployments with rollback plans and validation scripts; enforce stricter controls on file transfer into engineering environments; increase logging retention and perform targeted log hunts for anomalous TGML-related entries.
- Medium term (1–3 months): adopt hardened baseline images for engineering hosts, adopt allowlisting for engineering toolchains, and formalize integration testing for vendor patches. Consider a formal tabletop exercise for an EBO compromise scenario.
- Strategic: renegotiate integration and support SLAs with vendors and integrators to include timely vulnerability notification and testing windows; where possible, automate vulnerability ingestion into your patch‑management and asset‑inventory systems so critical advisories cannot be missed.
Final assessment — strengths, weaknesses, and risk posture
Schneider Electric responded in a coordinated manner by publishing a detailed security notice, fixed builds, and hardening guidance; national cyber centers mirrored that notice to increase awareness across critical sectors. That combination of vendor patching plus public‑sector amplification is a strength: it gives asset owners the technical fix and the urgency to prioritize remediation.However, the weaknesses highlighted by these CVEs expose a recurring theme in OT/automation software: file parsing logic (graphics, project files, drivers) remains a high‑value attack surface because it routinely accepts structured content from contractors and engineers. Even though initial access often requires user action or local access, that requirement does not materially lower risk in real operations—engineering hosts are commonly reachable via VPNs, jump hosts, and shared media. The operational workflow around engineering project files is therefore the persistent systemic weakness.
Finally, while compensating controls can substantially reduce exposure, they are not a substitute for the vendor fixes. The only durable resolution is to apply the patches that modify the parsing behavior and close the unsafe code paths. Where organizations cannot immediately patch, layered mitigations (segmentation, MFA, strict file transfer policy, allowlisting) materially lower attack likelihood and impact.
Schneider’s advisory and the subsequent national republishing make clear that this is a time‑sensitive issue for any organization running EcoStruxure Building Operation Workstation or WebStation. Treat the affected hosts as critical assets: inventory them now, schedule a tested patch rollout, harden engineering workflows, and strengthen monitoring to reduce the chance that a single crafted TGML file could lead to data loss or operational disruption.
Source: CISA Schneider Electric EcoStruxure Building Operation Workstation | CISA