Cisco SD‑WAN users woke up to a coordinated, high‑urgency warning on February 25, 2026: U.S. and allied cyber agencies have confirmed active exploitation of critical vulnerabilities in Cisco Catalyst SD‑WAN products and have issued prescriptive guidance — including a U.S. Emergency Directive for federal agencies — to inventory, patch, hunt, and harden SD‑WAN deployments immediately.
Cisco’s SD‑WAN platform is the network fabric connecting branch sites, data centers, and cloud services for thousands of enterprises and public‑sector organizations worldwide. The platform’s control plane and management components are high‑value targets because an attacker who gains administrative access can alter routing, inject policies, add rogue peers, and create persistent access that survives routine network changes.
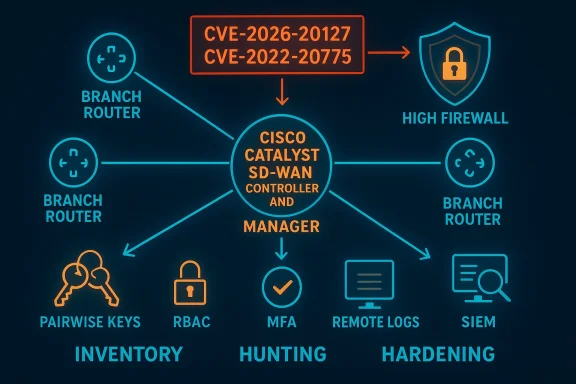
On February 25, 2026, CISA and international partners released an alert describing active, global exploitation of Cisco SD‑WAN systems and urging urgent mitigation steps. The alert named a newly tracked authentication bypass vulnerability, CVE‑2026‑20127, which has been observed as the initial access vector in ongoing intrusions. It also tied follow‑on activity to an older SD‑WAN privilege‑escalation flaw, CVE‑2022‑20775, which attackers have used to escalate privileges and establish long‑term persistence. In response, CISA published Emergency Directive ED 26‑03, directing federal civilian agencies to inventory affected Cisco SD‑WAN systems, apply updates, and assess for compromise. The authoring organizations also published a detailed hunt guide and recommended adoption of Cisco’s SD‑WAN hardening guidance.
This article summarizes what we know, verifies the technical claims where possible, explains why the threat is materially different from past SD‑WAN issues, and provides a practical, prioritized playbook for defenders responsible for SD‑WAN infrastructure.
Key requirements and expectations:
Caveat: Vendor hardening guidance evolves; operators must confirm exact configuration steps and supported options against the current Cisco hardening document before implementing changes in production.
Defenders must act now: inventory, capture artifacts, patch, hunt, and harden — in that order — and do so with the coordination and urgency the threat requires. Long‑term, this incident should push network owners toward stronger authentication models, immutable builds, comprehensive logging, and an operational posture that treats orchestration and control planes as crown jewels.
Prioritize containment and evidence preservation, lean on vendor hardening guidance, and treat this as the kind of operational emergency that justifies rapid, cross‑team collaboration. The window to prevent long‑term compromise is narrow; the cost of delay is high.
Source: CISA CISA and Partners Release Guidance for Ongoing Global Exploitation of Cisco SD-WAN Systems | CISA
 Background
Background
Cisco’s SD‑WAN platform is the network fabric connecting branch sites, data centers, and cloud services for thousands of enterprises and public‑sector organizations worldwide. The platform’s control plane and management components are high‑value targets because an attacker who gains administrative access can alter routing, inject policies, add rogue peers, and create persistent access that survives routine network changes.On February 25, 2026, CISA and international partners released an alert describing active, global exploitation of Cisco SD‑WAN systems and urging urgent mitigation steps. The alert named a newly tracked authentication bypass vulnerability, CVE‑2026‑20127, which has been observed as the initial access vector in ongoing intrusions. It also tied follow‑on activity to an older SD‑WAN privilege‑escalation flaw, CVE‑2022‑20775, which attackers have used to escalate privileges and establish long‑term persistence. In response, CISA published Emergency Directive ED 26‑03, directing federal civilian agencies to inventory affected Cisco SD‑WAN systems, apply updates, and assess for compromise. The authoring organizations also published a detailed hunt guide and recommended adoption of Cisco’s SD‑WAN hardening guidance.
This article summarizes what we know, verifies the technical claims where possible, explains why the threat is materially different from past SD‑WAN issues, and provides a practical, prioritized playbook for defenders responsible for SD‑WAN infrastructure.
What the alert says — a concise summary
- The primary, newly observed vector is an authentication bypass (CVE‑2026‑20127) that targets the peering authentication mechanism in Cisco Catalyst SD‑WAN Controller (formerly vSmart) and Cisco Catalyst SD‑WAN Manager (formerly vManage). Successful exploitation can allow an unauthenticated remote actor to obtain administrative privileges on the affected controller.
- Attackers have chained the bypass to previously disclosed privilege‑escalation flaws (notably CVE‑2022‑20775) to gain higher privileges, manipulate NETCONF and CLI, and add unauthorized peers or configuration changes that enable persistence and covert long‑term access.
- CISA added CVE‑2026‑20127 and CVE‑2022‑20775 to its Known Exploited Vulnerabilities (KEV) catalog and issued Emergency Directive ED 26‑03, requiring inventory, patching, artifact collection, and compromise assessment by federal civilian agencies.
- The authoring organizations — CISA, NSA, ASD/ACSC, Canada’s Cyber Centre, NCSC‑NZ, and NCSC‑UK — recommended immediate steps: inventory SD‑WAN systems, capture snapshots and logs, apply available vendor updates, conduct threat hunts for indicators of unauthorized peering and configuration changes, and implement vendor hardening guidance (network perimeter controls, certificate replacement, pairwise keys, session timeouts, remote logging).
Why this is urgent: the attack surface and real‑world impact
SD‑WAN controllers are high‑value targets
SD‑WAN controllers and managers centralize network policy, overlay routing, and certificate/peer orchestration. Compromise here is not a typical server breach — it can reshape network topologies, redirect traffic flows, and silently open lateral paths to critical assets. An attacker with administrative control over a controller can:- Insert or accept rogue peers that appear legitimate to branch edge devices.
- Push malicious configuration, route advertisements, or firewall/policy changes.
- Intercept, mirror or redirect traffic between sites and cloud services.
- Implant persistent backdoors in management or orchestration layers to survive updates.
The observed attack chain: initial access to persistence
Analysis published alongside the alert and vendor advisories describes a chained approach:- CVE‑2026‑20127 (authentication bypass) is used for initial, unauthenticated access to the controller.
- With foothold established, attackers leverage CVE‑2022‑20775 (existing privilege‑escalation issues in SD‑WAN CLI and access controls) to gain higher privileges that allow access to NETCONF and deeper configuration controls.
- Attackers add or manipulate peers and persistent configuration entries so that even if the controller is rebooted or some services are reconfigured, the rogue peer relationships and access paths remain.
- Long‑term persistence is established, enabling continued monitoring, lateral movement, and future exploitation.
Technical snapshot: CVE‑2026‑20127 and CVE‑2022‑20775
CVE‑2026‑20127 — authentication bypass (what we know)
- Nature: Authentication bypass in the peering authentication mechanism of Cisco Catalyst SD‑WAN Controller/Manager.
- Impact: Allows unauthenticated remote actors to bypass controller authentication and obtain administrative or high‑privileged non‑root accounts.
- Attack surface: Controllers with an internet‑exposed management or control plane and open ports are at increased risk; exposure via misconfigured VPN/management interfaces is a common problem.
- Observed exploitation: Attackers have used this flaw to create or accept rogue peering connections that appear legitimate to edge nodes.
CVE‑2022‑20775 — privilege escalation (context and role)
- Nature: Multiple CLI/authorization issues in SD‑WAN software allowing an authenticated local user to execute commands with elevated privileges (documented in 2022).
- Impact: Enables attackers who have any authenticated access to escalate to root‑equivalent privileges, manipulate underlying OS files, or modify NETCONF/CLI behavior.
- Role in campaign: Attackers observed chaining CVE‑2026‑20127 (initial access) with CVE‑2022‑20775 to move from a high‑privileged non‑root account to fully administrative control and modify management plane configurations.
What CISA’s Emergency Directive ED 26‑03 requires (federal focus with private‑sector relevance)
ED 26‑03 imposes several concrete obligations for U.S. Federal Civilian Executive Branch (FCEB) agencies and essentially prescribes the immediate defensive playbook. Organizations outside the FCEB should treat these requirements as best practice guidance.Key requirements and expectations:
- Inventory: Identify every in‑scope Cisco SD‑WAN instance (on‑prem, virtual, cloud‑hosted, managed services).
- Patch/Update: Apply vendor fixes and mitigation steps to each instance. Where immediate patching is impractical, agencies must follow compensating controls and report timelines.
- Evidence collection: Capture volatile artifacts, virtual machine snapshots, full configuration exports, AND controller logs to support hunt and forensic activities.
- Hunt & Assess: Perform threat hunts for known indicators (unauthorized peering, unexpected NETCONF calls, suspicious administrative sessions) and report compromise findings.
- Reporting & compliance: Agencies must report inventories and outcomes to CISA in line with ED deadlines for oversight and coordination.
Cisco’s guidance and recommended hardening steps
Cisco updated advisories and published a Catalyst SD‑WAN Hardening Guide. The high‑priority items defenders should implement are:- Network perimeter controls:
- Place control components behind firewalls; avoid direct internet exposure for controllers and managers.
- Isolate management interfaces (VPN 512 or equivalent) and restrict them to known management IPs.
- Use IP allow‑lists and blocklists for manually provisioned edge IPs.
- Management access and certificates:
- Replace self‑signed certificates for web‑UI and management interfaces with trusted, centrally managed certificates.
- Strongly restrict web UI access; require MFA for administrative sessions where supported.
- Control and data plane security:
- Use pairwise keying for device authentication rather than shared peer keys to limit lateral misuse.
- Limit session duration and enforce short session timeouts.
- Enforce strict role‑based access controls (RBAC) and tighten CLI command permissions.
- Logging and monitoring:
- Forward logs and audit trails to a remote, immutable syslog or SIEM.
- Enable detailed NETCONF/peer event logging; monitor for unexpected peering negotiation events.
- Retain logs long enough to support forensic investigations and threat hunts.
Caveat: Vendor hardening guidance evolves; operators must confirm exact configuration steps and supported options against the current Cisco hardening document before implementing changes in production.
Detection: what to hunt for now
The hunt guidance provided by CISA and partner CERTs focuses on these high‑value indicators:- Unexpected or new peering events on control connections — peers that were not provisioned by operations teams, with unusual timing or originating from atypical IP ranges.
- Changes to NETCONF calls or abnormal NETCONF session activity — particularly from non‑standard accounts.
- Administrative logins outside normal windows, from unusual IPs, or via accounts with recent credential resets.
- Configuration diffs that show added peers, modified routing policies, or policy pushes that were not approved.
- Signs of persistence: scheduled jobs, modified system files, unusual services, or opaque container/process changes that survive restarts.
- Collect full configuration exports and archive them for baseline comparison.
- Pull controller and manager logs, NETCONF session logs, and device audit trails.
- Use file‑integrity or configuration‑management tools to compute diffs against trusted baselines.
- Search for indicators of unauthorized peers or sudden additions to peer lists.
- If suspicious activity is identified, immediately isolate the affected controller from external networks (without powering off) and escalate to incident response.
Forensics and containment: recommended collection and response workflow
If you suspect compromise, follow a defensible, prioritized response:- Isolate but preserve: Disconnect affected SD‑WAN controllers from the internet but do not power them down. Preserve volatile memory and live network connections where possible.
- Capture snapshots: Generate hypervisor VM snapshots and filesystem images of affected controllers and managers.
- Export configurations: Immediately export running and startup configurations from controllers, managers, and edge routers.
- Collect logs: Pull all controller logs, NETCONF logs, VPN connection logs, and syslog exports. Centralized log storage makes triage far faster.
- Hash and document: Compute cryptographic hashes of collected artifacts, document chain‑of‑custody, and time‑stamp everything.
- Hunt and analyze: Search artifacts for rogue peers, unauthorized NETCONF commands, scheduled tasks, or unfamiliar user accounts. Use IOC lists and YARA/regex checks where available.
- Remediate: If compromise is confirmed, coordinate vendor guidance and consider rebuild/reimage of controllers from known‑good firmware, followed by configuration restore only from vetted backups.
- Report: For government customers, follow ED reporting rules; others should consider notifying their national CERT and affected partners.
Practical mitigation checklist (prioritized)
Use this checklist as an immediate action plan, ranked by impact and feasibility:- Inventory all SD‑WAN management and controller instances (on‑prem, virtual, and hosted). Mark any with public internet exposure.
- For internet‑exposed controllers, apply immediate compensating controls: restrict access to management interfaces with firewall rules and VPN only, and disable unauthenticated access points.
- Capture snapshots and export configurations and logs from every controller and manager.
- Apply available vendor patches and firmware updates as soon as they are validated in a test environment.
- Implement SD‑WAN hardening measures: replace self‑signed certs, enable pairwise keys, enforce RBAC, and set short session timeouts.
- Forward all SD‑WAN logs to a hardened, centralized SIEM or remote syslog server with strong retention.
- Conduct threat hunts for unauthorized peering, unexpected NETCONF commands, and suspicious admin sessions.
- If compromise is confirmed, isolate affected devices, plan for rebuilds from known‑good images, and rotate all credentials related to SD‑WAN management.
- Engage vendor support and, where applicable, national incident response teams or cyber CERTs.
- After remediation, perform a post‑incident review and change management to prevent recurrence.
Operational challenges and common pitfalls
- Patch windows vs. uptime: Many SD‑WAN deployments are critical; operators fear downtime. But leaving controllers unpatched during active exploitation is a larger risk. Plan controlled maintenance windows and test patches in isolated environments first.
- Managed services complexity: When SD‑WAN management is outsourced or provided from cloud instances, roles and responsibilities can be blurred. Establish a clear RACI for who performs patching, log collection, and forensic work.
- Log retention gaps: Short‑retention policies can destroy the only artifacts needed to demonstrate compromise. Extend retention for SD‑WAN logs during the active threat period.
- Configuration drift: Without strict configuration management, detecting unauthorized changes is hard. Use automated config backup and diff tooling to reduce mean time to detection.
- Overreliance on perimeter: Attackers in these campaigns exploited peering and management plane weaknesses. Perimeter controls alone won’t detect configuration tampering once the attacker uses legitimate orchestration channels.
Strategic implications — beyond emergency patching
Short‑term containment and patching are necessary, but SD‑WAN compromise makes the case for deeper architectural changes:- Zero trust for branch networking: Move away from implicit trust of branch devices. Strong mutual authentication, microsegmentation, and policy‑based access control reduce the blast radius of a compromised controller.
- Immutable builds and controlled upgrades: Use automated, reproducible images for controllers and managers, and manage updates through secure CI/CD pipelines.
- Defense in depth: Combine network controls, host hardening, EDR on management hosts, centralized logging, and anomaly detection to raise the bar for attackers.
- Vendor transparency and supply chain scrutiny: Demand clear patch timelines and reproducible advisories from vendors for critical infrastructure components.
What to tell leadership — a concise risk brief
- Risk: Compromise of SD‑WAN controllers allows attackers to manipulate enterprise network topology and traffic flows, enabling stealthy lateral movement and long‑term data access.
- Urgency: Active exploitation is confirmed. Delay in patching and hunting materially increases risk.
- Immediate asks:
- Approve emergency maintenance windows to apply fixes.
- Authorize forensic snapshots and extended log retention.
- Direct IT/security to prioritize SD‑WAN inventory and mitigation tasks across the environment.
- Business impact: Short maintenance windows now reduce the probability of extended outages and data losses later. The cost of immediate defensive action is dwarfed by the potential cost of widespread network compromise.
Strengths and gaps in the official guidance (critical analysis)
Strengths
- The joint alert and ED 26‑03 provide clear, concrete actions — inventory, patch, hunt, and harden — and they leverage cross‑national collaboration to share threat context quickly.
- Vendor hardening guidance focuses on implementable controls (certificates, pairwise keys, logging) that materially reduce risk if applied correctly.
- Mandating artifact collection and hunts ensures that compromised systems are less likely to be left infected and that forensic evidence is available for remediation.
Gaps and risks
- Operational friction: The directive assumes organizations have the staffing and tooling to perform large‑scale forensic collection and hunts quickly. Smaller orgs (and some cloud providers’ tenants) may not.
- Patch availability and compatibility: Rapid patch deployment risks breaking integrations; vendors and customers must coordinate regressions and compatibility testing under time pressure.
- Managed/hosted SD‑WAN: Guidance is less prescriptive about managed/hosted instances where operators and customers share responsibilities. Clear, contractual responsibilities are necessary to avoid missed remediation.
- Long‑tail exposure: Older SD‑WAN versions and unsupported appliances may not have fixes, forcing decommission or complex mitigations that agencies must manage quickly.
Final recommendations — an action plan for the next 72 hours
- Inventory: Complete a full inventory of SD‑WAN controllers, managers, and edge devices (0–8 hours).
- Isolate internet‑exposed management interfaces: Restrict to management‑only networks and allow‑list admin IPs (0–12 hours).
- Capture artifacts: Snapshots, configuration exports, and centralized log collection for every controller (0–24 hours).
- Apply vendor patches: Test and deploy fixes in priority order — internet‑exposed controllers first (24–72 hours).
- Hunt: Run targeted searches for rogue peers, unauthorized NETCONF activity, and abnormal admin sessions (24–72 hours).
- Harden: Implement Cisco’s recommended hardening steps — certificates, pairwise keys, session limits, remote logging (24–72 hours).
- Report & escalate: If you find compromise, follow applicable reporting obligations (CISA for U.S. federal), engage vendor/incident response, and initiate rebuilds as needed.
Conclusion
The February 25, 2026 alert and Emergency Directive ED 26‑03 mark another escalation in adversaries’ focus on network infrastructure: SD‑WAN controllers are now squarely in the crosshairs. The combination of a newly observed authentication bypass and existing privilege‑escalation flaws creates a high‑impact attack path that can yield stealthy, persistent control over enterprise WAN fabrics.Defenders must act now: inventory, capture artifacts, patch, hunt, and harden — in that order — and do so with the coordination and urgency the threat requires. Long‑term, this incident should push network owners toward stronger authentication models, immutable builds, comprehensive logging, and an operational posture that treats orchestration and control planes as crown jewels.
Prioritize containment and evidence preservation, lean on vendor hardening guidance, and treat this as the kind of operational emergency that justifies rapid, cross‑team collaboration. The window to prevent long‑term compromise is narrow; the cost of delay is high.
Source: CISA CISA and Partners Release Guidance for Ongoing Global Exploitation of Cisco SD-WAN Systems | CISA