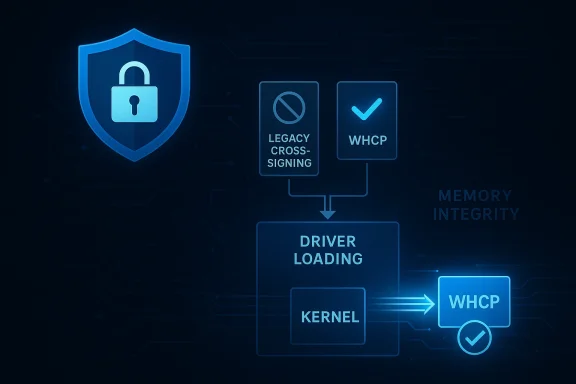
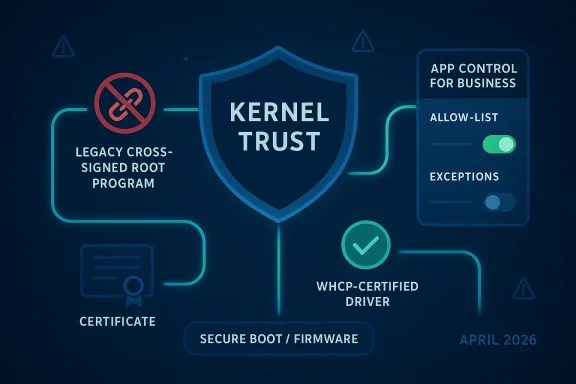
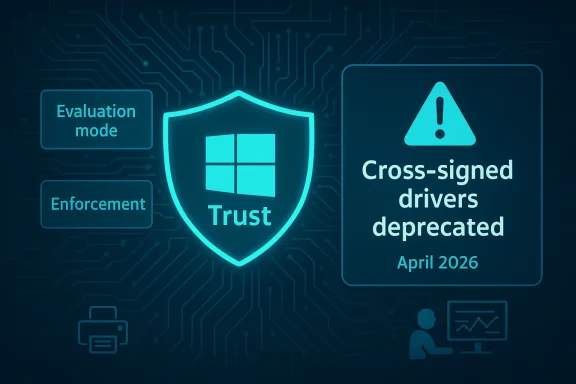
Microsoft is preparing one of the most consequential Windows kernel trust changes in years, and it lands at the intersection of security hardening, enterprise compatibility, and Microsoft’s broader effort to make Windows 11 feel more reliable. The company plans to stop loading kernel drivers signed through the old legacy cross-signed root program by default, while preserving a curated allow list for reputable older drivers and offering an evaluation mode so organizations can test the impact before enforcement. In practice, that means Microsoft is tightening one of the oldest trust paths in Windows without pretending the real-world ecosystem can be flipped overnight. The change is set to begin rolling out in April 2026 and will affect Windows 11 24H2, 25H2, 26H1, Windows Server 2025, and future client and server releases, according to the reporting and Microsoft’s own documentation on driver signing and trusted roots. ](Cross-Certificates for Kernel Mode Code Signing - Windows drivers))
For Windows veterans, the phrase “cross-signed driver” sounds like a relic from a different era because it is one. Microsoft’s old model let third-party certificate authorities establish chains of trust into the Windows kernel through cross-certificates, a design that made sense when the platform needed a flexible way to recognize commercially signed kernel-mode code. Microsoft’s documentation now treats that model as deprecated, explicitly warning that cross-signing is no longer accepted for driver signing and that using cross certificates for kernel-mode drivers violates Microsoft Trusted Root Program policy. (learn.microsoft.com)
That historical shift matters because the kernel is not just another part of Windows. It is the most privileged software layer on the machine, and anything that runs there can shape stability, security, and system integrity. Microsoft’s current trusted-root guidance makes clear that kernel-mode drivers are subject to heightened rules, and that modern Windows expects drivers to be signed through supported Microsoft pathways rather than legacy trust chains. In other words, this is not merely a certificate housekeeping story; it is a security boundary story. (learn.microsoft.com)
The practical reason this policy has survived so long is compatibility. Enterprises, hardware vendors, and niche device ecosystems often keep old drivers alive for years because replacement hardware is expensive, certification cycles are slow, and some products depend on legacy components that still “work” even when the trust model is no longer ideal. Microsoft has spent much of the last decade gradually nudging the ecosystem away from those older assumptions, first by tightening the rules for clean installs on Secure Boot-enabled devices and then by making WHQL and related program pathways the norm for newer systems. (learn.microsoft.com)
There is also a governance angle. Microsoft’s Trusted Root Program is increasingly explicit about the lifecycle of trust material, revocation behavior, audit requirements, and the need to keep CA hierarchies visible and enforceable. That is exactly the kind of machinery you would expect in a world where Windows security is moving from “can this driver run?” toward “should this driver still be trusted by default?” (learn.microsoft.com)
At the same time, the explicit allow list should not be mistaken for a free pass for legacy software. It is a narrow compatibility valve, not a rebirth of the old signing model. In practical terms, it protects organizations that still rely on older but reputable drivers while signaling to everyone else that the supported path is now WHCP.
This also mirrors the logic Microsoft has long used with other Windows security controls, especially WDAC and related application-control tooling. The company has repeatedly urged administrators to test policies in audit mode first, monitor events, and only then move to enforcement. In that sense, the kernel policy is not a one-off surprise; it is part of a familiar Microsoft pattern of measure first, enforce later.
The historical context matters here too. Microsoft has been tightening driver-signing requirements for years, especially on clean installs with Secure Boot enabled. The 2015 policy that required WHQL/Sysdev-style signing for new drivers on clean installations was one of the first major public signals that cross-signed trust would not remain a forever feature. The new policy is simply the next stage of rn.microsoft.com](Kernel checks for non-WHQL signed drivers - Compatibility Cookbook))
The change also reflects a broader Windows reality: modern security increasingly depends on trust being explicit rather than inherited. Microsoft’s Trusted Root Program has grown more specific about certificate lifecycle management, revocatexpectations, and Windows itself now treats old trust material as something that should be retired on schedule instead of tolerated indefinitely. (learn.microsoft.com)
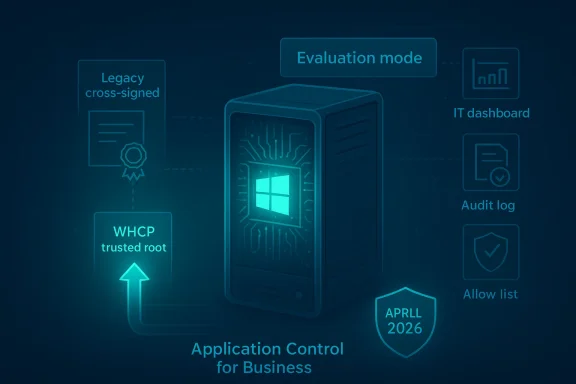
The good news is that Microsoft is not treating the enterprise as an afterthought. The evaluation-mode rollout gives IT staff a chance to discover which drivers are still depending on legacy cross-signed trust, and the option to override the default kernel policy througl for Business** gives administrators a supported mechanism to keep internal environments working where necessary. That is particularly useful for organizations that build or maintain custom drivers for specialized hardware or internal tooling.
That burden is familiar because Windows has already been through similar transitions. Microsoft’s earlier driver-signing enforcement on Windows 10 clean installs taught the industry that compatibility exceptions eexpand. The lesson for IT is simple: if a critical driver is still living on borrowed trust, it is time to find out whether a supported replacement exists. (learn.microsoft.com)
Still, consumer impact should not be underestimated. Hardware with older peripherals, specialty audio interfaces, obscure game controllers, and enthusiast add-ons is often supported by driver stacks that lag behind the mainstream. If those drivers are still relying on legacy trust assumptions, these the fact that “it works on my machine” is not the same thing as “it is supported by Windows.”
That said, the policy could also improve trust in the platform over time. Consumers rarely object to security hardening in principle; they object to mysterious friction. If Microsoft can make the change quietly and reliably, most users will simply experience fewer security anomalies without ever learning what cross-signing was.
Microsoft’s current driver documentation still reflects a world in transition. It describes release signing, cross-certificates, and older certificate flows, but it also makes plain that those mechanisms are being boxed in by newer policy requirements. In other words, the documentation is not just describing what is allowed; it is documenting the controlled retirement of what used to be normal. (learn.microsoft.com)
It also gives vendors a clearer target. A dated cross-signing model encourages workarounds and inconsistent support windows, while WHCP pushes vendors toward an ecosystem where trust is renewed through current tooling rather than grandfathered assumptions. That is less flexible, but it is also more sustainable. (learn.microsoft.com)
This is a classic Microsoft compromise: centralize the securphisticated administrators create exceptions through an explicit policy layer. That is a far cry from the old days, when legacy trust often lingered simply because nobody wanted to touch it. Now, if an organization wants to preserve custom behavior, it has to say so clearly.
For enterprises, that is actually a benefit. It reduces the number of undocumented exceptionspport nightmares later. A clean override record is easier to audit than a hidden legacy signing dependency that survived because nobody had time to investigate it.
There is also a market-clearing effect. Vendors who support old trust models because Windows allowed them to keep doing so now face a stronger incentive to modernize. That can benefit better-supported hardware ecosystems, but it can also accelerate the decline of niche or older peripherals that were already hanging on by inertia.
The biggest competitive implication may be reputational. Windows has long been criticized for carrying old compatibility baggage too far. By retiring a decades-old kernel trust path, Microsoft is trying to show that backward compatibility does not have to mean forever compatibility. That is a subtle but important pitch to enterprises deciding where to standardize.
The more interesting test is whether Microsoft uses this moment to keep pruning other old trust assumptions from Windows. The company has already shown in adjacent areas like Secure Boot, root program governance, and driver certification that it is willing to retire old mechanisms once replacement paths are in place. This kernel policy may therefore be less of an isolated event and more of a template for how Microsoft plans to modernize Windows in the second half of the decade. (learn.microsoft.com)
Source: Neowin Microsoft is changing a Windows kernel policy that's been around for decades
 Background
Background
For Windows veterans, the phrase “cross-signed driver” sounds like a relic from a different era because it is one. Microsoft’s old model let third-party certificate authorities establish chains of trust into the Windows kernel through cross-certificates, a design that made sense when the platform needed a flexible way to recognize commercially signed kernel-mode code. Microsoft’s documentation now treats that model as deprecated, explicitly warning that cross-signing is no longer accepted for driver signing and that using cross certificates for kernel-mode drivers violates Microsoft Trusted Root Program policy. (learn.microsoft.com)That historical shift matters because the kernel is not just another part of Windows. It is the most privileged software layer on the machine, and anything that runs there can shape stability, security, and system integrity. Microsoft’s current trusted-root guidance makes clear that kernel-mode drivers are subject to heightened rules, and that modern Windows expects drivers to be signed through supported Microsoft pathways rather than legacy trust chains. In other words, this is not merely a certificate housekeeping story; it is a security boundary story. (learn.microsoft.com)
The practical reason this policy has survived so long is compatibility. Enterprises, hardware vendors, and niche device ecosystems often keep old drivers alive for years because replacement hardware is expensive, certification cycles are slow, and some products depend on legacy components that still “work” even when the trust model is no longer ideal. Microsoft has spent much of the last decade gradually nudging the ecosystem away from those older assumptions, first by tightening the rules for clean installs on Secure Boot-enabled devices and then by making WHQL and related program pathways the norm for newer systems. (learn.microsoft.com)
Why Microsoft is doing this now
The timing is not random. Microsoft has been pushing a broader hardening agenda across Windows 11 and Windows Server 2025, andbeen vocal about improving reliability and security after enterprise feedback has repeatedly pointed to fragmentation and trust issues. The kernel-policy change fits neatly into that strategy because it reduces the chance that ancient signing paths remain a hidden exception in a platform that is supposed to be steadily modernizing.There is also a governance angle. Microsoft’s Trusted Root Program is increasingly explicit about the lifecycle of trust material, revocation behavior, audit requirements, and the need to keep CA hierarchies visible and enforceable. That is exactly the kind of machinery you would expect in a world where Windows security is moving from “can this driver run?” toward “should this driver still be trusted by default?” (learn.microsoft.com)
What Microsoft Is Changing
The core change is straightforward even if the implementation is noing will stop trusting legacy cross-signed roots by default, and instead will accept drivers signed through the Windows Hardware Compatibility Program. Microsoft is still preserving compatibility through a allow list for specific older drivers it has already vetted, which is a clear sign that the company is trying to avoid unnecessary breakage while still retiring the old trust mechanism.Default trust versus explicit allow lists
This is a meaningful distinction. A default-trust model lets code in auars to meet broad criteria, while an explicit allow list says the opposite: nothing gets in unless Microsoft has already made a judgment call about it. That shift gives Microsoft much tighter control over what can execute in the kernel, and it also makes the decision framework more legible for IT teams trying to diagnose why a driver works oanother.At the same time, the explicit allow list should not be mistaken for a free pass for legacy software. It is a narrow compatibility valve, not a rebirth of the old signing model. In practical terms, it protects organizations that still rely on older but reputable drivers while signaling to everyone else that the supported path is now WHCP.
Evaluation mode and why it matters
Microsoft says the new kernel trust policy will begin in evaluation mode, which is an important detail. Evaluation mode means systems can obserwhat would have been blocked before the policy is enforced, giving administrators a chance to see real-world impact before they switch to strict behavior. For organizations that manage fleets of hardware with weird peripherals or custom internal drivers, that is the difference between a manageable migration and a sudden outage.This also mirrors the logic Microsoft has long used with other Windows security controls, especially WDAC and related application-control tooling. The company has repeatedly urged administrators to test policies in audit mode first, monitor events, and only then move to enforcement. In that sense, the kernel policy is not a one-off surprise; it is part of a familiar Microsoft pattern of measure first, enforce later.
The Security Case
From a security perspective, Microsoft’s argument is hard to dismiss. Legacy cross-signing creates one more avenue for trust to persist longer than it should, and the kernel is the worst possible place for ambiguous trust. If the platform can reduce the number of dormant trust relationships that survive just because they are old, it reduces the attack surface for rootkits, persistence mechanisms, and abused third-party drivers. (learn.microsoft.com)The historical context matters here too. Microsoft has been tightening driver-signing requirements for years, especially on clean installs with Secure Boot enabled. The 2015 policy that required WHQL/Sysdev-style signing for new drivers on clean installations was one of the first major public signals that cross-signed trust would not remain a forever feature. The new policy is simply the next stage of rn.microsoft.com](Kernel checks for non-WHQL signed drivers - Compatibility Cookbook))
A kernel policy is not a normal policy
Kernel policy changes are different from app policies because their blast radius is larger and their failure modes are uglier. If a user-space app fails to launch, the user usually sees an error or an uninstall path. If a kernel driver fails to load, the effects can range from missing hardware features to boot-time problems, device instability, or support calls that are hard to reproduce. That is why Microsoft’s decision to use evaluation mode and compatibility exceptions is prudent rather than optional.The change also reflects a broader Windows reality: modern security increasingly depends on trust being explicit rather than inherited. Microsoft’s Trusted Root Program has grown more specific about certificate lifecycle management, revocatexpectations, and Windows itself now treats old trust material as something that should be retired on schedule instead of tolerated indefinitely. (learn.microsoft.com)
Enterprise Impact
For enterprises, this change will be judged less by its philosophy than by the inventory reports it generates. Large organizations often have hidden driver dependencies buried in point-of-sale hardware, industrial gear, VPN stacks, endpoint protection suites, an for a business function that no one has touched in five years. Those dependencies are exactly the kind of thing that can become expensive when a default trust path changes.The good news is that Microsoft is not treating the enterprise as an afterthought. The evaluation-mode rollout gives IT staff a chance to discover which drivers are still depending on legacy cross-signed trust, and the option to override the default kernel policy througl for Business** gives administrators a supported mechanism to keep internal environments working where necessary. That is particularly useful for organizations that build or maintain custom drivers for specialized hardware or internal tooling.
Why IT will care more than consumers
Most consumers do not know what kernel signing is, and they should not have to. Enterprises, by contrast, are the ones who own the operational debt. They must map which devices use which drivers, test whether vendor replacements exist, and determine whether a policy exception is temporary or permanent. Microsoft’s policy may be cleaner, but the migration burden will land squarely on administrators.That burden is familiar because Windows has already been through similar transitions. Microsoft’s earlier driver-signing enforcement on Windows 10 clean installs taught the industry that compatibility exceptions eexpand. The lesson for IT is simple: if a critical driver is still living on borrowed trust, it is time to find out whether a supported replacement exists. (learn.microsoft.com)
Likely enterprise response
Expect three immediate responses from organizations. First, they will audit which devices are affected. Second, they will pressure hardware vendors for WHCP-compliant updates. Third, they will reserve Application Control for Business overrides for the few cases where the business case for legacy support is stronger than the operational risk. That is the rational playbook, and it lines up with Microsoft’s own guidance for staged policy deployment. ([techcommunity.miechcommunity.microsoft.com/blog/coreinfrastructureandsecurityblog/deploying-windows-10-application-control-policy/2486267)- Inventory legacy drivers before April 2026.
- Validate vendor roadmaps for WHCP replacement builds.
- Test the new policy in audit mode before moving to enforcement.
- Reserve policy overrides for truly unavoidable internal dependencies.
- Track whether blocked drivers affes, or storage stacks.
- Build a rollback and support plan before broad deployment.
Consumer Impact
For most Windows 11 users, this will be invisible most of the time, which is exactly what Microsoft wants. Consumers typically benefit from a safer default trust model without needing to understand the mechanics behind it, and the presence of an allow list means Microsoft is trying to avoid a “surprise broken printer” moment on day one.Still, consumer impact should not be underestimated. Hardware with older peripherals, specialty audio interfaces, obscure game controllers, and enthusiast add-ons is often supported by driver stacks that lag behind the mainstream. If those drivers are still relying on legacy trust assumptions, these the fact that “it works on my machine” is not the same thing as “it is supported by Windows.”
The hidden cost of old hardware
The real consumer story here is lifecycle pressure. A driver policy may feel abstract, but its effects show up in everyday compatibility. A device that does not load correctly can look like a dead USB port, a broken microphone, or a suddenly unreliable piece of software, and users will blame Windows long before they blame an expired signing model. (learn.microsoft.com)That said, the policy could also improve trust in the platform over time. Consumers rarely object to security hardening in principle; they object to mysterious friction. If Microsoft can make the change quietly and reliably, most users will simply experience fewer security anomalies without ever learning what cross-signing was.
- Better default security without user action.
- Lower long-term exposure to stale driver trust.
- Possible compatibility issues for niche devices.
- Less confusion if Microsoft’s allow list covers common legacy cases.
- More pressure on enthusiasts to update old hardware ecosystems.
WHCP and the Future of Driver Signing
The fact that Microsoft is centering WHCP here is telling. WHCP is not just a certificate path; it is a broader ecosystem signal that a driver has gone through the current Windows hardware program and is aligned with the platform’s present-day requirements. That is the kind of trust anchor Microsoft wants at the kernel boundary because it stionship between signing, validation, and updateability. (learn.microsoft.com)Microsoft’s current driver documentation still reflects a world in transition. It describes release signing, cross-certificates, and older certificate flows, but it also makes plain that those mechanisms are being boxed in by newer policy requirements. In other words, the documentation is not just describing what is allowed; it is documenting the controlled retirement of what used to be normal. (learn.microsoft.com)
Why WHCP is the long-term answer
WHCP gives Microsoft a cleaner story acrost lets the company standardize the driver trust model, reduce surprise exceptions, and better align the Windows kernel with its broader security posture. That matters even more as Windows Server 2025 and future releases lean harder into policy-based manageability and default security.It also gives vendors a clearer target. A dated cross-signing model encourages workarounds and inconsistent support windows, while WHCP pushes vendors toward an ecosystem where trust is renewed through current tooling rather than grandfathered assumptions. That is less flexible, but it is also more sustainable. (learn.microsoft.com)
What this means for hardware makers
Hardware makers will need to think less about preserving ancient compatibility paths and more about shipping signed, supportable drivers that can survive policy changes. The winners will be vendors already treating Windows driver certification as a living process. The losers will be firms that still rely on decades-old binaries because “they haven’t broken yet.”- New products should target WHCP from the start.
- Existing vendors should audit legacy signing dependencies.
- Internal driver teams should plan for signed release pipelines.
- Support documentation should distinguish policy failure from hardware failure.
Application Control for Business as the Escape Valve
Microsoft’s choice to let Application Control for Business override the default kernel policy is one of the most interesting parts of the announcement. It acknowledges that not every environment fits a single trust model, and that some organizations must keep internal or specialty drivers alive for operational reasons.This is a classic Microsoft compromise: centralize the securphisticated administrators create exceptions through an explicit policy layer. That is a far cry from the old days, when legacy trust often lingered simply because nobody wanted to touch it. Now, if an organization wants to preserve custom behavior, it has to say so clearly.
Policy override is not a loophole
That distinction matters. A policy override is a controlled administrative choice, not a way to pretend the old model still exists. Microsoft has increasingly framed policy-based control as the right place to express exceptions, whether the topic is driver trust, application allow-listing, or update behavior. The philosophy is consistent: make the secure path automatic, and make exceptions intentional.For enterprises, that is actually a benefit. It reduces the number of undocumented exceptionspport nightmares later. A clean override record is easier to audit than a hidden legacy signing dependency that survived because nobody had time to investigate it.
- Central policy remains Microsoft’s preferred security model.
- Overrides are reserved for managed, documented exceptions.
- Auditability improves when legacy trust is explicit.
- Internal drivers get a support path without restoring default cross-signing.
- Security teams gain leverage over shadow IT behavior.
Competitive Implications
Microsoft’s kernel policy shift has implications beyond Windows itself because it reinforces a simple message: modern platforms should be harder to subvert at the kernel boundary. That puts pressure on driver vendors, device makers, and even rival operating systems that market and stability. The more Microsoft can show Windows as a tightening, policy-driven platform, the harder it becomes for competitors to frame Windows as the inherently lax option. (learn.microsoft.com)There is also a market-clearing effect. Vendors who support old trust models because Windows allowed them to keep doing so now face a stronger incentive to modernize. That can benefit better-supported hardware ecosystems, but it can also accelerate the decline of niche or older peripherals that were already hanging on by inertia.
Pressure on vendors and rivals alike
For Microsoft’s OEM and ISV partners, the message is blunt: align with the current program or risk becoming a compatibility exception. For rivals, especially in manaendpoint markets, the change raises the bar on what “secure by default” should mean in practice. Microsoft is not just claiming hardening; it is operationalizing it. (learn.microsoft.com)The biggest competitive implication may be reputational. Windows has long been criticized for carrying old compatibility baggage too far. By retiring a decades-old kernel trust path, Microsoft is trying to show that backward compatibility does not have to mean forever compatibility. That is a subtle but important pitch to enterprises deciding where to standardize.
- Vendors are pushed toward current signing and certification flows.
- Older peripherals may lose practical viability.
- Microsoft strengthens its security-first platform narrative.
- Managed-device competitors will be judged against the same trust expectations.
- The change could help Windows look more modern to cautious enterprise buyers.
Strengths and Opportunities
Microsoft’s move has several strengths, and the biggest one is that it narrows a long-standing security gap without pretending compatibility is disposable. The company is pairing a stricter default with an allow list and audit mode, which is the right blennization for a kernel-level change of this size. The result is a policy that is firmer than the old model but still realistic enough for enterprise deployment.- Stronger default trust posture for the Windows kernel.
- Reduced dependence on deprecated certificate paths.
- Better alignment between signing policy and modern Windows hardware programs.
- A staged rollout that gives admins time to react.
- Compatibility protections through a curated allow list.
- Administrative flexibility through Application Control for Business.
- Opportunity for vendors to refresh stale driver pipelines.
Risks and Concerns
The biggest risk is compatibility fallout, and it is not theoretical. Kernel driver failures can show up as missing devices, unstable endpoints, or application behavior that appears unrelated to signing policy. Even withllow lists, a policy change at this layer can still produce frustrating edge cases that are expensive to diagnose.- Legacy devices may break in ways that are hard for users to understand.
- Support teams may misdiagnose signing issues as hardware faults.
- Internal custom drivers may require time-consuming policy planning.
- Smaller vendors may not have easy WHCP migration paths.
- Users may blame Windows even when the issue is vendor neglect.
- Organizations with poor asset inventories may discover problems too late.
- Overreliance on allow lists could mask deeper modernization debt.
Looking Ahead
The key question now is not whether Microsoft will move forward, but how sharply and how fast it will enforce the new default. The evaluation phase should tell us how much legacy driver debt remains in the real world, and it will also reveal whether Microsoft’s allow list is broad enough to prevent unnecessary pain without becoming a permanent crutch. If the rollout is managed well, most users will never notice the policy at all.The more interesting test is whether Microsoft uses this moment to keep pruning other old trust assumptions from Windows. The company has already shown in adjacent areas like Secure Boot, root program governance, and driver certification that it is willing to retire old mechanisms once replacement paths are in place. This kernel policy may therefore be less of an isolated event and more of a template for how Microsoft plans to modernize Windows in the second half of the decade. (learn.microsoft.com)
What to watch next
- Whether Microsoft expands the allow list or keeps it tightly scoped.
- How quickly vendors issue WHCP-compliant replacements.
- Whether enterprise telemetry shows widespread blocked-driver events.
- How Application Control for Business overrides are documented and deployed.
- Whether the policy quietly expands to more Windows servicing branches.
Source: Neowin Microsoft is changing a Windows kernel policy that's been around for decades