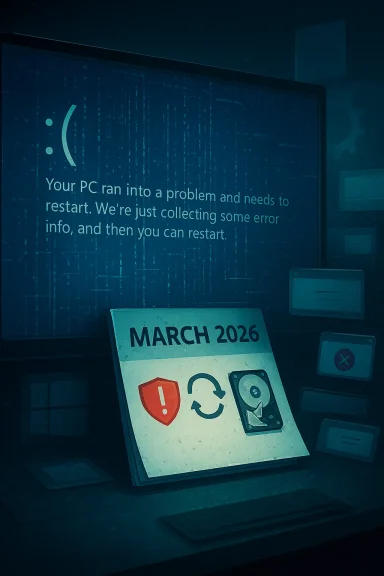
Microsoft’s March Patch Tuesday cumulative update for Windows 11 (KB5079473), released March 10, 2026, has triggered a small but noisy wave of user reports describing severe stability problems — complete freezes, repeated restarts, Blue Screens of Death (BSODs), and applications that simply refuse to open — even as Microsoft’s official release notes emphasize security fixes and list no known issues. ([support.microsoft.microsoft.com/en-gb/topic/march-10-2026-kb5079473-os-builds-26200-8037-and-26100-8037-9c222a8e-cc02-40d4-a1f8-ad86be1bc8b6)
Microsoft shipped KB5079473 for Windows 11 (covering both 24H2 and 25H2 channels) as the March 2026 Patch Tuesday cumulative update. The official changelog lists security patches (including fixes for actively exploited vulnerabilities), plus quality improvements focused on Secure Boot certificate handling, File Explorer search reliability, and Windows Defender Application Control (WDAC) COM allowlisting. The update advances Windows 11 to builds 26100.8037 (24H2) and 26200.8037 (25H2).
On the same rollout, community and forum threads began filling with reports from end users and admins about post-update instability. Those reports are presently anecdotal and scattered across Microsoft Q&A, Reddit, OEM forums and independent tech forums, but they cover a consistent set of symptoms that merit attention from IT pros and power users.
High‑risk / immediate actions
For individuals, caution and good backups are the immediate responses. For IT organizations, the right approach is a staged deployment with rigorous pilot testing that includes OEM and application stacks. Expect Microsoft and OEMs to investigate; until a formal Microsoft known‑issue entry or vendor driver patch appears, treat community reports as credible signals but not as exhaustive proof of a single root cause. The safe path is measured rollout, robust backup/rollback planning, and close monitoring of both Microsoft’s Release Health notices and vendor driver updates.
Source: channelnews.com.au Windows 11 March Update Reportedly Causing Crashes And Freezes For Some Users - channelnews
 Background / Overview
Background / Overview
Microsoft shipped KB5079473 for Windows 11 (covering both 24H2 and 25H2 channels) as the March 2026 Patch Tuesday cumulative update. The official changelog lists security patches (including fixes for actively exploited vulnerabilities), plus quality improvements focused on Secure Boot certificate handling, File Explorer search reliability, and Windows Defender Application Control (WDAC) COM allowlisting. The update advances Windows 11 to builds 26100.8037 (24H2) and 26200.8037 (25H2).On the same rollout, community and forum threads began filling with reports from end users and admins about post-update instability. Those reports are presently anecdotal and scattered across Microsoft Q&A, Reddit, OEM forums and independent tech forums, but they cover a consistent set of symptoms that merit attention from IT pros and power users.
What Microsoft changed in KB5079473 (short technical summary)
- The update is a cumulative security update that bundles the month’s security fixes and previously previewed quality changes.
- Notable non-security quality improvements called out in the release notes include:
- Secure Boot certificate handling tweaks.
- Enhancements to File Explorer search reliability, especially for multi-drive searches and “This PC”.
- WDAC COM allowlisting reliability improvements.
- A handful of small user-facing additions (example: built-in network speed test, Sysmon in-box components, and WebP wallpaper support in some reports).
What users are reporting — symptoms and patterns
Community reporting paints a multi-faceted picture. The most commonly reported problems include:- Hard crashes and complete system freezes that require a power-cySeveral users report repeated hard crashes minutes after boot.
- Intermittent or persistent BSODs after installation and reboot. Some threads include references to kernel-level errors and instantaneous system halts.
- Repeated restarts — reports of machines rebooting every 10–20 minutes in an apparent reboot loop on affected devices.
- Productivity software failing to launch — anecdotal reports indicate Microsoft Office/Outlook failing to open, or Outlook hanging unless restarted, in specific configurations. These reports appear on Microsoft Q&A and i
- Core tools or shortcuts stopping working — multiple posts describe Command Prompt / PowerShell binaries being unresponsive, or the Print Screen shortcut no longer capturing screenshots. Some of these reports are likely downstream symptoms of file-permission or binary-access issues.
- Hardware- or OEM-specific problems — the most prominent cluster involves some Samsung Galaxy Book laptop models reporting C:\ access denied or drives becoming inaccessible after the update, forcing factory restore or recovery in severe cases. Dell workstations and certain GPU-accelerated applications (CAD, GPU-heavy compute workloads) have been flagged with graphical glitches and crashes by other users. These are currently anecdotal but repeated enough to be concerning.
Verifying the claims: what the official record shows
- Microsoft’s published KB5079473 support entry confirms the update and lists the updated OS builds and the scope of security/quality fixes. The support entry does not, at the time of writing, list a platform‑wide “known issue” tied to crashes or drive inaccessibility.
- Microsoft’s Windows release health/message center references the update’s File Explorer search reliability improvements and guidance about Secure Boot certificate updates, but again shows no broad known‑issue advisory that matches the severity of the community complaints. This disconnect between community reports and Microsoft’s active “known issues” list is frequently observed during large rollouts: early signals appear in forums well before the vendor reproduces and formalizes a known‑issue advisory.
- Independent tech outlets are already reporting on user complaints. Outlets such as Windows Central and PCWorld are covering both the positive additions in KB5079473 and the user reports of post‑patch instability, underscoring that this is not limited to a single forum echo chamber. These journalistic pieces lean on forum and social media reporting while noting Microsoft’s official page shows no known issues as of their reporting.
Which machines and configurations appear most affected
Based on the community trace and OEM threads, the early clusters indicate:- Certain Samsung Galaxy Book models (2023–2025 series) reporting a severe C:\ access denied problem immediately after the update — a situation that can effectively lock users out of installed programs and data. These reports are concentrated and reproducible enough within the Samsung and sysadmin communities to raise red flags.
- Workstations with particular GPU driver + GPU‑accelerated applications (some Dell Precision models) report graphical glitches, app crashes, or BSODs in GPU workloads. This is consistent with the typical pattern where graphics drivers interact with new kernel or security changes and produce regressions.
- Enterprise environments that run extensive OEM management or security stacks may see higher incidence rates because those stacks touch low-level drivers and kernel interfaces that updates often affect. Several forum posts and IT discussions recommend conservative pilot testing in such environments.
Why these update problems happen (technical analysis)
Several technical realities make a small number of systems vulnerable to severe po- Windows updates modify kernel components, security policy enforcers (like WDAC), or the way the OS enumerates and permits access to device objects. Any of these changes can break assumptions made by OEM-supplied drivers or third‑party system utilities.- OEM utilities that hook file system permissions, encryption, or storage-layer drivers (for example, vendor-provided “Storage Share” or disk‑management helpers) can be brittle when an underlying OS contract changes. The Samsung Galaxy Book cluster appears to implicate a vendor utility interacting badly with post‑update permission/ACL changes — an archetypal compatibility failure.
- Graphics and GPU regressions commonly result from mismatches between driver expectations and updated kernel-mode interfaces or security policies for GPU scheduling and memory. When a driver assumes behavior that changes in an LCU (latest cumulative update), the driver may fault or the GPU subsystem can crash, producing BSODs or application failures.
- Finally, some problems that look like OS bugs are actually installer or file-permission anomalies produced during the update (for example, a vendor process running at install-time that locks files or modifies ACLs in a way that blocks post‑boot binaries). That can make diagnostics tricky because the visible failure (e.g., “Office won’t launch”) is downstream of a one-time failed step during update application.
How to triage and mitigate (for end users and IT admins)
If you or your users have installed KB5079473 and started seeing problems, follow these prioritized steps.High‑risk / immediate actions
- If a machine is in a reboot loop or experiencing repeated hard crashes, boot to Safe Mode and create a full image or backup before further remediation. Do not assume the next boot will be safe.
- For machines that become inaccessible (C:\ access denied) or exhibit file-permission anomalies, disconnect network shares and avoid further writes. Capture event logs if possible (in Safe Mode or using a rescue environment). Community posts indicate some Samsung Galaxy Book users needed recovery or factory reset; recover backups first.
- Run Wihooter and retry installing the update (some installs fail partially and subsequent attempts succeed).
- In Event Viewer, look for installer errors (WindowsUpdateClient), dismount/lock errors, or driver faults (WHEA, BugCheck codes) to narrow down a root cause.
- Check the Device Manager for driver errors, and if recent OEM drivers are present, consider rolling back to a vendor-provided older driver or reinstalling the latest OEM driver manually. For GPU issues, reinstall the OEM or vendor graphics driver (NVIDIA/AMD/Intel) from vendor packages, not only via Windows Update.
- If Office or Outlook fail after the update, attempt an Office repair from the Control Panel / Apps Settings and ensure Office itself is fully patched (Office updates can be released concurrently with Windows patch cycles).
- If you need rapid remediation, you can uninstall the cumulative update from Settings → Windows Update → Update history → Uninstall updates. This is a temporary relief in many cases, and systems often return to a stable state after rollback and reboot. Document the rollback and escalate to Microsoft support if rollback is not possible or fails.
- Pause deployment in broader environments. Use a staged rollout with a pilot group and validate the full stack: endpoint protection, Office suites, line-of-business applications, imaging tools, and OEM management utilities.
- For managed fleets, push hardware/driver updates from OEM channels alongside or before the OS update, and have rollback plans and recovery media ready.
- Monitor Microsoft’s Release Health dashboard and Windows message center for any formal known‑issue advisories or KIR (Known Issue Rollback) notices that Microsoft may publish once the vendor reproduces a problem. KIR has been used in prior months to quietly remediate troublesome changes.
How likely is Microsoft to issue a formal advisory or KIR?
Based on precedent, the vendor usually follows this pattern:- Community reports appear within 24–72 hours of a broad rollout.
- If the vendor can reproduce the failure and ties it to a specific change or driver interaction, it will either:
- Publish a Known Issues advisory on the KB support page and message center; or
- Perform a Known Issue Rollback (KIR) that silently mitigates the problem on affected systems, or
- Release an out-of-band patch to address the regression.
Strengths and risks: a critical assessment
Strengths- KB5079473 plugs a significant set of security holes, including zero-day fixes. The security benefits are tangible and important for threat mitigation, especially in enterprise contexts. Delaying security updates indefinitely is not a safe option in high-risk threat environments.
- Microsoft’s cumulative-update model bundles tested fixes and previously previewed changes, which reduces the number of separate update events for admins to manage.
- The update highlights the perennial trade-off between rapid security patching and ecosystem stability. When kernel or security-policy components change, third-party drivers and OEM utilities that run at privileged levels can break in ways that are disruptive and data‑impacting (e.g., inaccessible drives).
- Patch telemetry and vendor reproduction pipelines can lag the pace of community chatter; that means some users can be severely impacted before an official acknowledgement or mitigation is published.
- Vendor-supplied utilities (OEM “experience” apps, storage helpers, or custom driver stacks) are frequent culprits in severe post‑update regressions — yet Microsoft’s KB pages often cannot catalog that scope until OEMs confirm and provide driver updates.
Recommended policy for users and organizations (practical checklist)
- Individuals: If you’re non-technical or rely on a single personal machine, weigh the urgency of the security fixes against your tolerance for instability. If you value immediate system reliability more than shipping-zero-day protection, postpone the update for a week and watch for vendor advisories; if you hold sensitive data or face high exposure, patch but have recovery media/backups ready.
- Small businesses and admins:
- Pause auto-deploy for non-critical systems for 72–96 hours after a Patch Tuesday rollout.
- Run the update in a pilot group that represents diverse hardware and software stacks (include OEM laptops, workstations with discrete GPUs, and machines with vendor utilities).
- Validate Office, Outlook, printing workflows, GPU apps, and vendor management agents.
- Enterprises:
- Implement a staged rollout (pilot → broader pilot → phased production).
- Monitor Microsoft Release Health and vendor advisories for KIRs and hotfixes.
- Maintain a tested rollback procedure and ensure Windows recovery media is available for impacted endpoints.
- Coordinate with OEMs (Samsung, Dell, etc.) to confirm driver/utility compatibility before mass deployment.
What to watch next
- Microsoft’s support page for KB5079473 and the Windows Release Health dashboard for any updates to Known Issues or KIR activity. The vendor typically posts follow-ups if a regression proves widespread or severe.
- OEM forums and vendor advisories for patched drivers or guidance (especially Samsung and GPU vendors).
- Community telemetry — forums, Reddit, and enterprise-managed ticket streams — for reproducible patterns (specific hardware + driver + OS build combinations) that will help vendors reproduce the issue.
Conclusion
KB5079473 is the March 2026 security cumulative for Windows 11 that brings meaningful security coverage and quality refinements, but it has also coincided with a series of user reports describing crashes, freezes, BSODs, and even inaccessible system drives on a minority of devices. The evidence so far is consistent with an ecosystem compatibility problem — interactions between the cumulative update and certain OEM drivers or vendor utilities — rather than a universal OS‑level catastrophe.For individuals, caution and good backups are the immediate responses. For IT organizations, the right approach is a staged deployment with rigorous pilot testing that includes OEM and application stacks. Expect Microsoft and OEMs to investigate; until a formal Microsoft known‑issue entry or vendor driver patch appears, treat community reports as credible signals but not as exhaustive proof of a single root cause. The safe path is measured rollout, robust backup/rollback planning, and close monitoring of both Microsoft’s Release Health notices and vendor driver updates.
Source: channelnews.com.au Windows 11 March Update Reportedly Causing Crashes And Freezes For Some Users - channelnews
