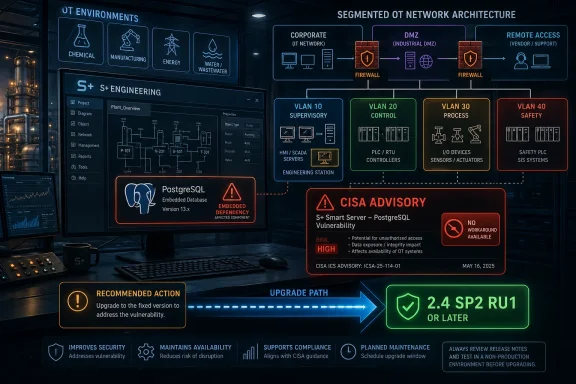
ABB Ability Symphony Plus Engineering versions 2.2 through 2.4 SP2 are affected by four high-severity PostgreSQL vulnerabilities disclosed in a CISA industrial-control-system advisory republished on April 30, 2026, with ABB directing customers to upgrade to S+ Engineering 2.4 SP2 RU1 or later. The uncomfortable part is not that PostgreSQL had bugs; mature infrastructure software always does. The real story is that a database component embedded inside an engineering workstation stack can become a control-system risk long after the original CVEs have left the front page. For operators in chemical, manufacturing, energy, and water environments, this is another reminder that software supply chain is not an abstract cloud problem — it lives inside the plant network, too.
The ABB advisory is narrow in one sense and broad in another. It names a finite list of affected products: ABB Ability Symphony Plus S+ Engineering 2.2, 2.3 and its release updates, and 2.4 through 2.4 SP2. It also says the affected component is PostgreSQL 13.11 and earlier, a mainstream open-source database whose security advisories were already public before this industrial-control notice arrived.
But the deployment context changes the meaning of the vulnerabilities. In a normal enterprise IT environment, PostgreSQL flaws are serious because databases hold sensitive information and frequently sit near business-critical applications. In an industrial environment, the database may be part of an engineering system used to configure, manage, or support automation assets. That makes the blast radius harder to model with a conventional server-security mindset.
ABB’s description is direct: if an attacker gains access to the S+ client/server network, exploitation could allow arbitrary code execution and potentially compromise the entire S+ system. That wording matters. The advisory is not describing an unauthenticated internet worm, but it is also not describing a harmless local bug buried behind six layers of impossible preconditions. It is describing the kind of post-compromise pivot that defenders of operational technology have learned to fear.
For Windows administrators who straddle IT and OT, this is familiar terrain. The attacker does not need every asset to be internet-facing if one workstation, VPN appliance, jump host, domain credential, or misconfigured firewall can become the bridge. Once inside the trusted engineering network, vulnerabilities that looked “internal only” on paper can become operationally meaningful.
All four issues require some level of access or privilege in the PostgreSQL environment. That does not make them benign. It means the practical risk depends on how well the S+ client/server network is segmented, how tightly database privileges are controlled, how remote access is brokered, and whether engineering workstations are treated as crown-jewel systems or merely as another set of Windows endpoints.
ABB’s mitigation language leans heavily on architecture: perimeter firewalls, proper network separation, no direct internet exposure, and restricting access to the S+ client/server network. CISA’s recommended practices echo the same worldview. Put control systems behind firewalls, isolate them from business networks, and treat remote access as a carefully managed exception rather than a convenience feature.
That advice can sound generic because it appears in almost every industrial advisory. It is not generic here. The vulnerabilities are not described as exploitable from anywhere on the public internet by default; they become dangerous when an attacker can reach the engineering network. In other words, segmentation is not a compliance checkbox. It is the compensating control that determines whether a known PostgreSQL flaw is a patch-management problem or a plant-security problem.
That mixture is important because it shows the limitations of thinking about database security as merely password security. Authentication is necessary, but it is not sufficient when authenticated users can manipulate database objects, extension behavior, backup workflows, or administrative routines in ways that cross privilege boundaries. In the real world, especially in older or long-lived environments, database accounts often accumulate more access than their original purpose required.
The PostgreSQL project has already issued fixes in upstream releases for these vulnerability classes. ABB’s industrial advisory is therefore not about discovering an unknown database catastrophe. It is about the lag between upstream vulnerability disclosure, vendor product integration, site qualification, and operational deployment.
That lag is one of the defining problems of OT security. Enterprise IT can often patch a database package within a routine maintenance window. A control-system operator may need vendor validation, outage planning, regression testing, backup images, rollback plans, and coordination with operations staff before touching an engineering system. Attackers understand this delay. Defenders have to design around it.
This is a familiar pattern in industrial advisories. The vendor has a corrected release, but the plant cannot always move at software-industry speed. So the interim plan becomes a hardening plan: confirm whether the affected versions are installed, verify that the S+ client/server network is isolated, examine firewall rules, restrict remote access, and monitor for suspicious database or engineering-system activity.
That is useful, but it is not the same as remediation. A firewall rule can be changed later by accident. A VPN can be compromised. A flat network can quietly expand as projects accumulate. A patched product version, properly tested and deployed, removes the known vulnerable component from the environment.
The absence of a workaround also means asset inventory becomes non-negotiable. ABB says customers can determine exposure simply by checking whether they run the listed affected product versions; no special analysis tools are needed. That sounds easy until an organization has multiple sites, inherited systems, vendor-managed machines, and engineering laptops that only connect during maintenance events.
That timeline deserves attention. It means some customers may already have had access to a fixed engineering release for well over a year, even if the security framing around these PostgreSQL CVEs is now receiving renewed visibility through CISA. This is not unusual in industrial software, where release updates may include security hardening, dependency refreshes, and defect fixes that do not always trigger immediate sitewide urgency.
The CISA republication changes the incentives. Once a vulnerability set appears in the ICS advisory stream, it becomes easier for auditors, insurers, regulators, and internal risk committees to ask whether a site is exposed. It also becomes easier for adversaries to map public product-version information against known CVE mechanics.
That does not mean every ABB Symphony Plus site is suddenly under active attack. ABB said it had not received information indicating exploitation of S+ Engineering when the advisory was originally issued. But “no known exploitation” is not a strategy. It is a temporary observation, and in OT environments temporary observations have a way of becoming permanent excuses.
If an attacker compromises an engineering workstation or the server components around it, the consequences can move beyond data loss. Configuration integrity, operational availability, and trust in the engineering toolchain all come into play. Even if functional safety systems are not affected, as ABB says in the advisory, the business impact of a compromised engineering environment can still be severe.
The lesson for Windows administrators is to collapse the artificial wall between “plant software” and “IT hygiene.” Engineering stations should have controlled software installation, tightly managed local admin access, strong logging, protected credentials, and remote access paths that assume eventual compromise of user endpoints. If the database component inside the engineering stack is vulnerable, the surrounding Windows environment becomes part of the exploitability story.
This is also where backup and restore practices matter. CVE-2024-7348’s relationship to PostgreSQL utility behavior is a reminder that administrative routines are part of the attack surface. Backups, exports, refreshes, migrations, and maintenance scripts often run with higher privileges than day-to-day users. In a compromised environment, those trusted routines can become execution paths.
Closed-source embedded components can have the same problem, only with less visibility. Open-source software at least gives defenders public CVEs, upstream release notes, and a broader community of researchers and maintainers. The hard part is turning that visibility into timely product-level updates and site-level deployment.
Industrial vendors sit in the middle of this chain. They must validate upstream fixes against their own applications, document affected versions, issue advisories, and support customers who cannot patch on demand. Customers, meanwhile, must stop treating vendor-integrated components as invisible. If PostgreSQL, OpenSSL, Java, .NET, or a web server is inside a control-system product, it eventually becomes part of the control-system risk register.
The ABB advisory is therefore less an indictment than a case study. It shows how mainstream software vulnerabilities travel downstream into specialized environments where patching is slower, exposure is harder to measure, and operational consequences are more complex than a database server reboot.
That model has benefits. It gives asset owners a centralized place to discover advisories across vendors. It also pressures organizations to process industrial vulnerabilities in a more standardized way, with CVEs, affected products, mitigations, and revision histories captured in machine-readable or semi-structured formats.
But republication can also create a false sense of completion. The advisory exists, the CVEs are named, the fix is listed, and the recommended practices are familiar. None of that proves a single plant has upgraded. The hard part begins after publication, when someone must reconcile the advisory against installed versions, maintenance windows, vendor support contracts, and operational constraints.
For defenders, the useful question is not “Did CISA publish this?” It is “Which of our sites run the affected versions, who owns the upgrade, and what compensating controls are verified until it is complete?” Anything less is advisory theater.
That is why the phrase “not internet-facing” is no longer enough. A control-system subnet can be non-public and still be reachable from the wrong internal VLAN. A jump server can be hardened and still share credentials with less protected systems. A firewall can exist and still permit broad access because an old integration required it years ago.
The PostgreSQL bugs in this advisory are post-access accelerants. They matter after an attacker has crossed the first boundary. That is precisely why they are dangerous in environments where internal trust is still over-granted.
The right model is not a castle wall. It is a set of compartments. Engineering systems should not merely be inside the plant network; they should be reachable only by the people, hosts, protocols, and maintenance workflows that genuinely require access. Database services should not be casually exposed across broad subnets. Administrative utilities should not run against untrusted database objects without scrutiny.
That difference is real, but it should not become an excuse for indefinite deferral. The ABB fix path is clear: move to S+ Engineering 2.4 SP2 RU1 or later. Organizations that cannot do so immediately should document why, define interim controls, and set a target date rather than leaving the issue in a permanent exception queue.
A mature response would start with version discovery. Security teams should determine which ABB Ability Symphony Plus Engineering installations exist, which versions are running, and which networks can reach the S+ client/server components. They should then map users and service accounts with PostgreSQL access, review remote-access paths, and confirm that backups and administrative routines are not creating unnecessary privilege exposure.
The final step is verification. It is not enough to say a control-system network is segmented because the architecture diagram says so. Firewall rules, routing tables, remote-access groups, and actual packet paths should be checked. In industrial security, diagrams often describe the network someone intended to build, not the network that exists after ten years of emergency exceptions.
The most concrete takeaways are these:
Source: CISA ABB Ability Symphony Plus Engineering | CISA
 A Database Bug Becomes an Industrial-Control Problem
A Database Bug Becomes an Industrial-Control Problem
The ABB advisory is narrow in one sense and broad in another. It names a finite list of affected products: ABB Ability Symphony Plus S+ Engineering 2.2, 2.3 and its release updates, and 2.4 through 2.4 SP2. It also says the affected component is PostgreSQL 13.11 and earlier, a mainstream open-source database whose security advisories were already public before this industrial-control notice arrived.But the deployment context changes the meaning of the vulnerabilities. In a normal enterprise IT environment, PostgreSQL flaws are serious because databases hold sensitive information and frequently sit near business-critical applications. In an industrial environment, the database may be part of an engineering system used to configure, manage, or support automation assets. That makes the blast radius harder to model with a conventional server-security mindset.
ABB’s description is direct: if an attacker gains access to the S+ client/server network, exploitation could allow arbitrary code execution and potentially compromise the entire S+ system. That wording matters. The advisory is not describing an unauthenticated internet worm, but it is also not describing a harmless local bug buried behind six layers of impossible preconditions. It is describing the kind of post-compromise pivot that defenders of operational technology have learned to fear.
For Windows administrators who straddle IT and OT, this is familiar terrain. The attacker does not need every asset to be internet-facing if one workstation, VPN appliance, jump host, domain credential, or misconfigured firewall can become the bridge. Once inside the trusted engineering network, vulnerabilities that looked “internal only” on paper can become operationally meaningful.
The CVSS Score Is High, but the Network Boundary Is the Real Control
The advisory assigns high CVSS scores, including 8.8 for CVE-2023-5869 and CVE-2024-7348, 8.0 for CVE-2024-0985, and 7.5 for CVE-2023-39417. Those numbers are useful triage signals, but they do not tell the whole story. In industrial systems, the difference between “reachable” and “not reachable” is often the difference between an incident and a bad audit finding.All four issues require some level of access or privilege in the PostgreSQL environment. That does not make them benign. It means the practical risk depends on how well the S+ client/server network is segmented, how tightly database privileges are controlled, how remote access is brokered, and whether engineering workstations are treated as crown-jewel systems or merely as another set of Windows endpoints.
ABB’s mitigation language leans heavily on architecture: perimeter firewalls, proper network separation, no direct internet exposure, and restricting access to the S+ client/server network. CISA’s recommended practices echo the same worldview. Put control systems behind firewalls, isolate them from business networks, and treat remote access as a carefully managed exception rather than a convenience feature.
That advice can sound generic because it appears in almost every industrial advisory. It is not generic here. The vulnerabilities are not described as exploitable from anywhere on the public internet by default; they become dangerous when an attacker can reach the engineering network. In other words, segmentation is not a compliance checkbox. It is the compensating control that determines whether a known PostgreSQL flaw is a patch-management problem or a plant-security problem.
Four PostgreSQL Flaws, One Operational Lesson
The named CVEs span different bug classes, but they converge on a single uncomfortable outcome: code or SQL execution under conditions where an attacker has already obtained some foothold. CVE-2023-5869 involves an integer overflow tied to crafted data supplied by an authenticated PostgreSQL user. CVE-2023-39417 concerns SQL injection behavior around extension scripts and quoting constructs. CVE-2024-7348 is a time-of-check/time-of-use race condition involving a PostgreSQL utility commonly run with elevated privileges. CVE-2024-0985 involves materialized views and the possibility of luring a higher-privileged user into executing attacker-controlled SQL functions.That mixture is important because it shows the limitations of thinking about database security as merely password security. Authentication is necessary, but it is not sufficient when authenticated users can manipulate database objects, extension behavior, backup workflows, or administrative routines in ways that cross privilege boundaries. In the real world, especially in older or long-lived environments, database accounts often accumulate more access than their original purpose required.
The PostgreSQL project has already issued fixes in upstream releases for these vulnerability classes. ABB’s industrial advisory is therefore not about discovering an unknown database catastrophe. It is about the lag between upstream vulnerability disclosure, vendor product integration, site qualification, and operational deployment.
That lag is one of the defining problems of OT security. Enterprise IT can often patch a database package within a routine maintenance window. A control-system operator may need vendor validation, outage planning, regression testing, backup images, rollback plans, and coordination with operations staff before touching an engineering system. Attackers understand this delay. Defenders have to design around it.
“No Workaround” Is the Phrase That Should Focus the Room
ABB says no workarounds are available. That is the line that should move this from “we will review it later” to “we need an owner and a date.” If an organization cannot upgrade immediately, the advisory points back to mitigating factors and recommended security practices, but those are not product-level fixes. They are exposure-management measures.This is a familiar pattern in industrial advisories. The vendor has a corrected release, but the plant cannot always move at software-industry speed. So the interim plan becomes a hardening plan: confirm whether the affected versions are installed, verify that the S+ client/server network is isolated, examine firewall rules, restrict remote access, and monitor for suspicious database or engineering-system activity.
That is useful, but it is not the same as remediation. A firewall rule can be changed later by accident. A VPN can be compromised. A flat network can quietly expand as projects accumulate. A patched product version, properly tested and deployed, removes the known vulnerable component from the environment.
The absence of a workaround also means asset inventory becomes non-negotiable. ABB says customers can determine exposure simply by checking whether they run the listed affected product versions; no special analysis tools are needed. That sounds easy until an organization has multiple sites, inherited systems, vendor-managed machines, and engineering laptops that only connect during maintenance events.
The December 2024 Fix Now Has a 2026 Deadline Energy
ABB’s recommended immediate action is to upgrade systems running S+ Engineering 2.2 through 2.4 SP2 to S+ Engineering 2.4 SP2 RU1 or later. The interesting wrinkle is that ABB identifies 2.4 SP2 RU1 as released in December 2024. The CISA republication arrived on April 30, 2026, following ABB’s own April 2026 advisory.That timeline deserves attention. It means some customers may already have had access to a fixed engineering release for well over a year, even if the security framing around these PostgreSQL CVEs is now receiving renewed visibility through CISA. This is not unusual in industrial software, where release updates may include security hardening, dependency refreshes, and defect fixes that do not always trigger immediate sitewide urgency.
The CISA republication changes the incentives. Once a vulnerability set appears in the ICS advisory stream, it becomes easier for auditors, insurers, regulators, and internal risk committees to ask whether a site is exposed. It also becomes easier for adversaries to map public product-version information against known CVE mechanics.
That does not mean every ABB Symphony Plus site is suddenly under active attack. ABB said it had not received information indicating exploitation of S+ Engineering when the advisory was originally issued. But “no known exploitation” is not a strategy. It is a temporary observation, and in OT environments temporary observations have a way of becoming permanent excuses.
Windows Shops Should Treat Engineering Stations as Tier-Zero Assets
Many WindowsForum readers will approach this advisory through the Windows endpoint lens: patch levels, local administrator rights, antivirus, EDR, firewall policy, and remote desktop exposure. Those controls matter, but engineering systems deserve a stricter classification. They are not ordinary desktops with unusual software installed. They are administrative interfaces into industrial environments.If an attacker compromises an engineering workstation or the server components around it, the consequences can move beyond data loss. Configuration integrity, operational availability, and trust in the engineering toolchain all come into play. Even if functional safety systems are not affected, as ABB says in the advisory, the business impact of a compromised engineering environment can still be severe.
The lesson for Windows administrators is to collapse the artificial wall between “plant software” and “IT hygiene.” Engineering stations should have controlled software installation, tightly managed local admin access, strong logging, protected credentials, and remote access paths that assume eventual compromise of user endpoints. If the database component inside the engineering stack is vulnerable, the surrounding Windows environment becomes part of the exploitability story.
This is also where backup and restore practices matter. CVE-2024-7348’s relationship to PostgreSQL utility behavior is a reminder that administrative routines are part of the attack surface. Backups, exports, refreshes, migrations, and maintenance scripts often run with higher privileges than day-to-day users. In a compromised environment, those trusted routines can become execution paths.
The Open-Source Dependency Argument Cuts Both Ways
It is tempting to use advisories like this as evidence against open-source components in industrial products. That would be too easy and mostly wrong. PostgreSQL is widely scrutinized, actively maintained, and transparent about vulnerabilities. The problem is not that ABB used PostgreSQL. The problem is the operational complexity of carrying any third-party component inside a long-lived industrial product.Closed-source embedded components can have the same problem, only with less visibility. Open-source software at least gives defenders public CVEs, upstream release notes, and a broader community of researchers and maintainers. The hard part is turning that visibility into timely product-level updates and site-level deployment.
Industrial vendors sit in the middle of this chain. They must validate upstream fixes against their own applications, document affected versions, issue advisories, and support customers who cannot patch on demand. Customers, meanwhile, must stop treating vendor-integrated components as invisible. If PostgreSQL, OpenSSL, Java, .NET, or a web server is inside a control-system product, it eventually becomes part of the control-system risk register.
The ABB advisory is therefore less an indictment than a case study. It shows how mainstream software vulnerabilities travel downstream into specialized environments where patching is slower, exposure is harder to measure, and operational consequences are more complex than a database server reboot.
CISA’s Republication Is a Visibility Machine, Not a Magic Fix
CISA notes that this advisory is a verbatim republication of ABB PSIRT 7PAA017341 through a CSAF conversion. That detail may sound bureaucratic, but it matters. The government is not rewriting the vendor’s technical analysis; it is amplifying it through the ICS advisory ecosystem so defenders who track CISA feeds see the issue.That model has benefits. It gives asset owners a centralized place to discover advisories across vendors. It also pressures organizations to process industrial vulnerabilities in a more standardized way, with CVEs, affected products, mitigations, and revision histories captured in machine-readable or semi-structured formats.
But republication can also create a false sense of completion. The advisory exists, the CVEs are named, the fix is listed, and the recommended practices are familiar. None of that proves a single plant has upgraded. The hard part begins after publication, when someone must reconcile the advisory against installed versions, maintenance windows, vendor support contracts, and operational constraints.
For defenders, the useful question is not “Did CISA publish this?” It is “Which of our sites run the affected versions, who owns the upgrade, and what compensating controls are verified until it is complete?” Anything less is advisory theater.
The Risk Lives in the Pivot, Not the Perimeter
The advisory’s repeated condition — access to the site’s S+ client/server network — should not lull anyone into complacency. Modern intrusions rarely begin at the final target. They begin with phishing, stolen VPN credentials, exposed remote-management systems, vulnerable edge devices, supplier access, or a compromised IT workstation that can reach too much.That is why the phrase “not internet-facing” is no longer enough. A control-system subnet can be non-public and still be reachable from the wrong internal VLAN. A jump server can be hardened and still share credentials with less protected systems. A firewall can exist and still permit broad access because an old integration required it years ago.
The PostgreSQL bugs in this advisory are post-access accelerants. They matter after an attacker has crossed the first boundary. That is precisely why they are dangerous in environments where internal trust is still over-granted.
The right model is not a castle wall. It is a set of compartments. Engineering systems should not merely be inside the plant network; they should be reachable only by the people, hosts, protocols, and maintenance workflows that genuinely require access. Database services should not be casually exposed across broad subnets. Administrative utilities should not run against untrusted database objects without scrutiny.
Patch Management Needs a Plant-Floor Translation Layer
Enterprise patch management often assumes a repeatable cycle: identify vulnerability, test update, deploy through endpoint management, verify compliance. OT patch management is more conditional. Updates may require vendor involvement, production downtime, safety review, and careful sequencing with other changes.That difference is real, but it should not become an excuse for indefinite deferral. The ABB fix path is clear: move to S+ Engineering 2.4 SP2 RU1 or later. Organizations that cannot do so immediately should document why, define interim controls, and set a target date rather than leaving the issue in a permanent exception queue.
A mature response would start with version discovery. Security teams should determine which ABB Ability Symphony Plus Engineering installations exist, which versions are running, and which networks can reach the S+ client/server components. They should then map users and service accounts with PostgreSQL access, review remote-access paths, and confirm that backups and administrative routines are not creating unnecessary privilege exposure.
The final step is verification. It is not enough to say a control-system network is segmented because the architecture diagram says so. Firewall rules, routing tables, remote-access groups, and actual packet paths should be checked. In industrial security, diagrams often describe the network someone intended to build, not the network that exists after ten years of emergency exceptions.
The ABB Advisory Gives Defenders a Useful, Uncomfortable Checklist
The practical response to this advisory is not mysterious, but it does require discipline. ABB has named the affected versions, identified the fixed release path, and said there are no workarounds. CISA has reinforced the familiar defense-in-depth measures around exposure reduction and remote-access hygiene.The most concrete takeaways are these:
- Organizations running ABB Ability Symphony Plus S+ Engineering 2.2 through 2.4 SP2 should treat those installations as affected unless they have already upgraded to S+ Engineering 2.4 SP2 RU1 or a later release.
- The vulnerabilities require access to the S+ client/server network, so network segmentation and remote-access control are central to reducing near-term risk.
- The absence of a workaround means compensating controls should be temporary safeguards, not substitutes for the vendor update.
- PostgreSQL accounts, privileges, extensions, backup routines, and administrative utilities should be reviewed because the named CVEs involve authenticated database behavior and privilege-boundary failures.
- Sites should verify actual firewall and routing behavior rather than relying solely on historical architecture diagrams or assumptions about OT isolation.
- ABB reported no known exploitation of S+ Engineering at the time of the original advisory, but defenders should not treat that as a reason to delay remediation.
Source: CISA ABB Ability Symphony Plus Engineering | CISA