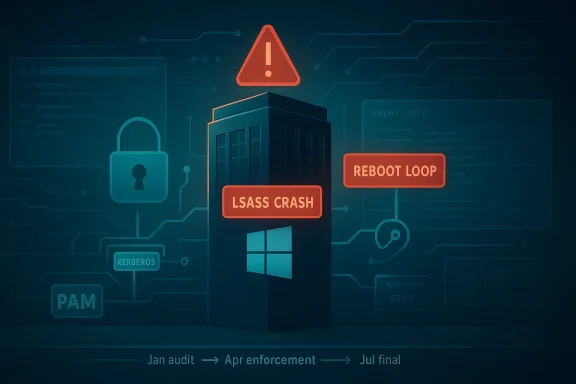
The April 2026 Windows security cycle is already proving to be one of the most consequential update months in recent memory for enterprise identity teams. Microsoft has confirmed a Kerberos hardening change that begins in April 2026, and that shift is landing at the same time administrators are watching for reports of LSASS crashes, domain controller reboot loops, and fragile behavior in Privileged Access Management environments. The combination is exactly the sort of thing that makes Windows patch Tuesday feel less like routine maintenance and more like a controlled burn. (techcommunity.microsoft.com)
At a high level, the story is not simply that “an update broke Windows.” The more important point is that Microsoft has been steadily tightening Kerberos defaults and identity protections, and that hardening can expose hidden dependencies in older infrastructures. In April 2026, Microsoft moved into the second deployment phase of its RC4 deprecation effort, changing default ticket behavior on supported domain controllers and pushing organizations away from legacy encryption assumptions. (techcommunity.microsoft.com)
That matters because domain controllers are not ordinary servers. They sit at the center of authentication, policy enforcement, and trust. When a domain controller fails, entire fleets of users, services, and automation pipelines can follow it into the void, which is why even a narrow issue can have a wide blast radius. Microsoft’s own documentation on LSASS failures shows how a crash in the Local Security Authority Subsystem Service can prevent sign-in, stop services, and trigger an automatic restart. (learn.microsoft.com)
The current concern is especially acute in environments that rely on non-Global Catalog domain controllers and PAM workflows, because those deployments often carry the most sensitive authentication paths. If a change in encryption behavior or an adjacent identity bug creates a crash condition, the result is not just inconvenience. It can become an authentication outage that looks, from the outside, like a complete infrastructure failure. (techcommunity.microsoft.com)
There is also a historical pattern here that enterprise administrators will recognize immediately. Microsoft has repeatedly had to address LSASS-related instability on domain controllers over the years, including prior out-of-band fixes and update advisories. That history does not mean every new report is the same bug, but it does explain why administrators treat anything touching LSASS, Kerberos, or DC boot behavior as high-risk by default. (learn.microsoft.com)
In that January phase, Microsoft introduced audit events and a temporary registry control to let administrators see where old authentication habits still existed. In April, the default behavior changes became operationally meaningful. The practical consequence is that accounts without explicit Kerberos encryption settings may no longer negotiate RC4 implicitly and instead receive AES-based tickets, which is safer but potentially disruptive for legacy applications and service accounts. (techcommunity.microsoft.com)
This is not a random modernization effort. Microsoft is addressing known Kerberos weaknesses and information disclosure risks, and the hardening path is meant to culminate in full enforcement by July 2026. That timeline is important because it gives IT teams a brief transition window, not an indefinite grace period. Organizations that treat April as a preview rather than a real migration deadline may discover that the final enforcement step is much harder than expected. (techcommunity.microsoft.com)
At the same time, Microsoft’s documentation on LSASS failures shows the classic symptom set administrators fear: sign-in failures, service start problems, event-log noise, and in some cases a crash that leads directly to a restart. Even when the immediate trigger is different from the RC4 changes, the operational effect is the same. A domain controller that cannot stay up is a domain controller that cannot be trusted. (learn.microsoft.com)
The big lesson is that modern Windows patching is increasingly about security compatibility, not just binary compatibility. A patch can be perfectly correct from a security standpoint and still break workflows that depend on outdated assumptions about encryption, ticket negotiation, or identity behavior. That is why Microsoft keeps emphasizing staged deployment and log review, because the modern Windows server stack is far more interdependent than it used to be. (techcommunity.microsoft.com)
That confirmation is important for administrators because it explains why some legacy environments may suddenly behave differently after patching. If a service account, application, or appliance was quietly relying on RC4 by default, the update can expose that dependency immediately. In other words, the update may not be “breaking” the system so much as revealing that the system was already living on borrowed time. (techcommunity.microsoft.com)
Microsoft’s guidance also tells the same story in reverse: keep watching the System event log for Kerberos-related audit events, identify remaining dependencies, and enable enforcement only when warning or blocking events stop appearing. That is a classic enterprise-hardening workflow, but it depends on organizations actually reading the logs and not treating them as background noise. (techcommunity.microsoft.com)
In practical terms, LSASS is not just “another service.” It is the process that enforces security policy and handles core identity operations. If a security update alters ticket behavior or a dependency inside the authentication stack misbehaves, LSASS is often where the problem surfaces first. That makes the process both a symptom and a causal layer, which is why diagnosis can be tricky. (learn.microsoft.com)
This also explains why incident response around LSASS is so high stakes. A workstation can usually be rebooted and recovered with little drama. A domain controller, by contrast, may take the rest of the forest down with it if it is the wrong controller at the wrong time. When that controller is part of a PAM flow, the loss of privileged access paths can make remediation far harder. (techcommunity.microsoft.com)
This is why PAM-related incidents get so much attention from enterprise teams. A normal authentication hiccup may affect a few users. A PAM failure can block domain admins, emergency responders, and automation identities all at once. The result is not just operational pain; it is a resilience problem that can delay incident containment. (techcommunity.microsoft.com)
There is also a subtle architectural issue here. PAM environments often rely on clean separation between privileged and standard access, which means the infrastructure is intentionally more segmented and policy-heavy. That makes it excellent from a security standpoint, but also more vulnerable to changes that affect ticketing, domain trust, or policy lookups. Security controls do not remove fragility; they often redistribute it. (techcommunity.microsoft.com)
For enterprises, however, the story is much harsher. Many organizations still carry hybrid identity baggage, older service accounts, and software appliances that were never fully modernized. Those environments may pass functional tests while quietly relying on implicit RC4 behavior or brittle sign-in paths that fail only after the update reaches the wrong controller. (techcommunity.microsoft.com)
The difference lies in dependency depth. Home systems use the OS in one way; enterprises use it in dozens of ways simultaneously. That means a single authentication change can affect file servers, directory sync, VPN gateways, admin portals, backup systems, and privileged workflows at the same time. Complexity is the multiplier here, not the update itself. (techcommunity.microsoft.com)
There are a few practical priorities that should come first. Identify which controllers are non-Global Catalog servers, confirm whether PAM paths depend on them, and review any accounts or services that still rely on implicit Kerberos settings. Then compare that inventory with the update timeline so you know whether you are in the audit, enforcement, or remediation phase. (techcommunity.microsoft.com)
It is also worth emphasizing that not every fix is a patch. Microsoft’s guidance on LSASS failures includes environmental correction steps such as checking directory objects, reviewing password policy containers, and understanding whether the failure is actually an AD configuration problem rather than a pure update defect. In other words, root cause analysis matters as much as update rollback. (learn.microsoft.com)
What enterprise teams should care about most is not the headline, but the migration path. If your organization still has unreviewed RC4 usage, uncertain PAM dependencies, or domain controllers that were never stress-tested under modern Kerberos defaults, the April 2026 cycle is your warning shot. The real objective is not merely to survive this month’s updates, but to enter July 2026 with no surprises left in the authentication stack. (techcommunity.microsoft.com)
Source: thewincentral.com Windows April 2026 update bug, LSASS crash, reboot loop fix - WinCentral
 Overview
Overview
At a high level, the story is not simply that “an update broke Windows.” The more important point is that Microsoft has been steadily tightening Kerberos defaults and identity protections, and that hardening can expose hidden dependencies in older infrastructures. In April 2026, Microsoft moved into the second deployment phase of its RC4 deprecation effort, changing default ticket behavior on supported domain controllers and pushing organizations away from legacy encryption assumptions. (techcommunity.microsoft.com)That matters because domain controllers are not ordinary servers. They sit at the center of authentication, policy enforcement, and trust. When a domain controller fails, entire fleets of users, services, and automation pipelines can follow it into the void, which is why even a narrow issue can have a wide blast radius. Microsoft’s own documentation on LSASS failures shows how a crash in the Local Security Authority Subsystem Service can prevent sign-in, stop services, and trigger an automatic restart. (learn.microsoft.com)
The current concern is especially acute in environments that rely on non-Global Catalog domain controllers and PAM workflows, because those deployments often carry the most sensitive authentication paths. If a change in encryption behavior or an adjacent identity bug creates a crash condition, the result is not just inconvenience. It can become an authentication outage that looks, from the outside, like a complete infrastructure failure. (techcommunity.microsoft.com)
There is also a historical pattern here that enterprise administrators will recognize immediately. Microsoft has repeatedly had to address LSASS-related instability on domain controllers over the years, including prior out-of-band fixes and update advisories. That history does not mean every new report is the same bug, but it does explain why administrators treat anything touching LSASS, Kerberos, or DC boot behavior as high-risk by default. (learn.microsoft.com)
Why this month feels different
The reason April 2026 stands out is timing. Microsoft is not only delivering routine security fixes; it is also advancing a multi-phase Kerberos enforcement plan that can surface previously invisible technical debt. That means a production environment may appear stable in staging, then fail under real-world authentication patterns once the default behavior changes in earnest. (techcommunity.microsoft.com)- Identity hardening is now colliding with legacy trust models.
- LSASS remains a single point of failure for many domain operations.
- PAM architectures are especially sensitive to authentication regressions.
- Domain controller reboot loops turn a software bug into an availability crisis.
- Short-term testing windows are no longer enough for complex enterprises. (techcommunity.microsoft.com)
Background
To understand why administrators are worried, it helps to step back and look at what Microsoft has been changing over the last year. The company has been steering Windows domain controllers away from RC4 and toward stronger encryption behavior, beginning with an initial audit phase in January 2026 and progressing into enforcement in April 2026. The January phase was designed to help organizations find RC4 dependencies before behavior actually changed, which is a smart idea in theory and a painful one in practice if nobody acted on the warnings. (techcommunity.microsoft.com)In that January phase, Microsoft introduced audit events and a temporary registry control to let administrators see where old authentication habits still existed. In April, the default behavior changes became operationally meaningful. The practical consequence is that accounts without explicit Kerberos encryption settings may no longer negotiate RC4 implicitly and instead receive AES-based tickets, which is safer but potentially disruptive for legacy applications and service accounts. (techcommunity.microsoft.com)
This is not a random modernization effort. Microsoft is addressing known Kerberos weaknesses and information disclosure risks, and the hardening path is meant to culminate in full enforcement by July 2026. That timeline is important because it gives IT teams a brief transition window, not an indefinite grace period. Organizations that treat April as a preview rather than a real migration deadline may discover that the final enforcement step is much harder than expected. (techcommunity.microsoft.com)
At the same time, Microsoft’s documentation on LSASS failures shows the classic symptom set administrators fear: sign-in failures, service start problems, event-log noise, and in some cases a crash that leads directly to a restart. Even when the immediate trigger is different from the RC4 changes, the operational effect is the same. A domain controller that cannot stay up is a domain controller that cannot be trusted. (learn.microsoft.com)
The big lesson is that modern Windows patching is increasingly about security compatibility, not just binary compatibility. A patch can be perfectly correct from a security standpoint and still break workflows that depend on outdated assumptions about encryption, ticket negotiation, or identity behavior. That is why Microsoft keeps emphasizing staged deployment and log review, because the modern Windows server stack is far more interdependent than it used to be. (techcommunity.microsoft.com)
The domain controller problem in plain English
A domain controller is the gatekeeper for login, policy, and trust. If its security subsystem fails, the rest of the environment loses its anchor point. That is why reboot loops are so destructive: they remove the one system every other system relies on to come back online cleanly. (learn.microsoft.com)- Authentication can fail before users even see a desktop.
- Services can stop during startup because logon tokens are unavailable.
- DNS and time services can be affected when LSASS is unstable.
- Recovery becomes difficult when the controller never reaches a healthy state.
- One bad reboot cycle can snowball into a site-wide incident. (learn.microsoft.com)
What Microsoft Has Confirmed
Microsoft’s April 2026 messaging is significant because it confirms the direction of travel even if it does not, by itself, confirm every third-party bug report floating around the web. The company has explicitly said that Windows updates released in April 2026 and later begin the second phase of Kerberos protection changes, and that domain controllers will default to AES-SHA1 behavior for accounts without explicit encryption settings. (techcommunity.microsoft.com)That confirmation is important for administrators because it explains why some legacy environments may suddenly behave differently after patching. If a service account, application, or appliance was quietly relying on RC4 by default, the update can expose that dependency immediately. In other words, the update may not be “breaking” the system so much as revealing that the system was already living on borrowed time. (techcommunity.microsoft.com)
Microsoft’s guidance also tells the same story in reverse: keep watching the System event log for Kerberos-related audit events, identify remaining dependencies, and enable enforcement only when warning or blocking events stop appearing. That is a classic enterprise-hardening workflow, but it depends on organizations actually reading the logs and not treating them as background noise. (techcommunity.microsoft.com)
What this does not yet prove
What the Microsoft sources do not yet prove, at least from the material available here, is that the April 2026 update universally causes LSASS crashes on all affected systems. The update clearly changes Kerberos behavior, and LSASS is central to authentication, but a direct Microsoft bulletin tying a broad reboot-loop defect to every affected server version was not surfaced in the sources reviewed. That means reports of LSASS crash loops should be treated as credible but environment-specific until Microsoft publishes a matching advisory. (techcommunity.microsoft.com)- Microsoft has confirmed the Kerberos RC4 hardening timeline.
- Microsoft has confirmed April 2026 behavior changes on domain controllers.
- Microsoft has documented LSASS crash/restart symptoms on domain controllers.
- A universal, single-bulletin root cause for every reboot-loop report was not established in the available official material.
- Operational correlation is not the same as a formal Microsoft RCA. (techcommunity.microsoft.com)
Why LSASS Matters So Much
LSASS sits at the heart of Windows authentication, which is why it is one of the most sensitive processes in the operating system. When it stops responding or crashes, the effects are usually immediate: users cannot log in normally, services fail to start, and the machine may shut down or reboot as part of its protection logic. Microsoft’s own troubleshooting guidance describes those symptoms in detail. (learn.microsoft.com)In practical terms, LSASS is not just “another service.” It is the process that enforces security policy and handles core identity operations. If a security update alters ticket behavior or a dependency inside the authentication stack misbehaves, LSASS is often where the problem surfaces first. That makes the process both a symptom and a causal layer, which is why diagnosis can be tricky. (learn.microsoft.com)
This also explains why incident response around LSASS is so high stakes. A workstation can usually be rebooted and recovered with little drama. A domain controller, by contrast, may take the rest of the forest down with it if it is the wrong controller at the wrong time. When that controller is part of a PAM flow, the loss of privileged access paths can make remediation far harder. (techcommunity.microsoft.com)
Common LSASS failure patterns
Microsoft’s documented sign-in failure patterns align with what admins tend to see in the field: a login prompt that accepts credentials but does not proceed, cached credentials working only when the network is disconnected, and system logs pointing toward authentication failure. Those signals should trigger immediate triage on any domain controller. (learn.microsoft.com)- Post-reboot sign-in hangs are a classic warning sign.
- Cached credentials working offline can hint at directory-side failure.
- Unexpected reboots often follow LSASS termination.
- Service logon errors may appear before the full crash cycle.
- Event logs and ETL traces matter more than the visible symptom. (learn.microsoft.com)
The PAM Angle
Privileged Access Management systems are designed to reduce risk by tightening control around elevated credentials, time-limited access, and auditability. But that design also creates concentration risk. If the authentication layer underneath PAM becomes unstable, administrators may lose the very pathways they need to recover the environment. (techcommunity.microsoft.com)This is why PAM-related incidents get so much attention from enterprise teams. A normal authentication hiccup may affect a few users. A PAM failure can block domain admins, emergency responders, and automation identities all at once. The result is not just operational pain; it is a resilience problem that can delay incident containment. (techcommunity.microsoft.com)
There is also a subtle architectural issue here. PAM environments often rely on clean separation between privileged and standard access, which means the infrastructure is intentionally more segmented and policy-heavy. That makes it excellent from a security standpoint, but also more vulnerable to changes that affect ticketing, domain trust, or policy lookups. Security controls do not remove fragility; they often redistribute it. (techcommunity.microsoft.com)
Why enterprises feel this first
Consumer Windows users may never notice a Kerberos hardening transition beyond the occasional login oddity. Enterprises do because they run the systems most likely to depend on explicit, legacy, or cross-system authentication behavior. The more customized the environment, the more likely an update will surface something that vanilla home systems never had to support. (techcommunity.microsoft.com)- PAM vaults depend on stable identity flows.
- Tiered admin models increase reliance on domain controller consistency.
- Emergency access paths can be unexpectedly blocked.
- Automation accounts often hide legacy Kerberos settings.
- The more mature the security program, the more update friction it can reveal. (techcommunity.microsoft.com)
Enterprise vs Consumer Impact
For consumers, the most relevant takeaway is simple: this is not a general Windows desktop catastrophe. The risk surface is concentrated around domain controllers, authentication infrastructure, and server roles, not typical personal PCs. That does not make the issue trivial, but it does mean the average home user is unlikely to experience LSASS reboot loops as described in enterprise incident reports. (techcommunity.microsoft.com)For enterprises, however, the story is much harsher. Many organizations still carry hybrid identity baggage, older service accounts, and software appliances that were never fully modernized. Those environments may pass functional tests while quietly relying on implicit RC4 behavior or brittle sign-in paths that fail only after the update reaches the wrong controller. (techcommunity.microsoft.com)
The difference lies in dependency depth. Home systems use the OS in one way; enterprises use it in dozens of ways simultaneously. That means a single authentication change can affect file servers, directory sync, VPN gateways, admin portals, backup systems, and privileged workflows at the same time. Complexity is the multiplier here, not the update itself. (techcommunity.microsoft.com)
What hybrid shops should remember
Hybrid environments have the hardest job because they straddle both cloud and on-prem identity. If the on-prem domain controller side becomes unstable, the cloud side may not save you quickly enough, especially if the failure hits privileged authentication or directory synchronization. In that sense, hybrid can be more resilient in theory and more brittle in practice. (techcommunity.microsoft.com)- Cloud integration does not eliminate domain controller dependence.
- Directory sync can be slowed or interrupted by DC instability.
- Admin break-glass accounts must be tested outside normal flows.
- Legacy NTLM or RC4 dependencies should be considered suspect.
- Rollback plans matter more than “wait and see” optimism. (techcommunity.microsoft.com)
How Administrators Should Respond
The immediate operational lesson is to slow down, inventory carefully, and avoid broad rollout until you know exactly where your authentication dependencies live. Microsoft’s staged hardening approach is essentially an invitation to test; enterprises that skip the invitation tend to pay for it later in downtime and emergency recovery work. (techcommunity.microsoft.com)There are a few practical priorities that should come first. Identify which controllers are non-Global Catalog servers, confirm whether PAM paths depend on them, and review any accounts or services that still rely on implicit Kerberos settings. Then compare that inventory with the update timeline so you know whether you are in the audit, enforcement, or remediation phase. (techcommunity.microsoft.com)
It is also worth emphasizing that not every fix is a patch. Microsoft’s guidance on LSASS failures includes environmental correction steps such as checking directory objects, reviewing password policy containers, and understanding whether the failure is actually an AD configuration problem rather than a pure update defect. In other words, root cause analysis matters as much as update rollback. (learn.microsoft.com)
A sensible response sequence
- Pause broad deployment of the April 2026 security updates on production domain controllers.
- Check domain controller roles and identify the servers most likely to affect privileged access.
- Review Kerberos audit events and isolate accounts still depending on legacy encryption behavior.
- Validate emergency access and PAM break-glass procedures on isolated test systems.
- Monitor LSASS and reboot behavior after patching a single controller first. (techcommunity.microsoft.com)
Strengths and Opportunities
The upside of this situation is that Microsoft is not leaving organizations completely blind. The Kerberos hardening roadmap includes an audit phase, explicit event logging, and a transition period before full enforcement. That gives disciplined IT teams a real chance to clean up technical debt before July 2026, which is a much better outcome than a surprise cutover. (techcommunity.microsoft.com)- Early audit events can reveal hidden RC4 dependencies.
- Temporary registry controls provide limited transition flexibility.
- Security posture improves when legacy encryption is removed.
- PAM modernization can be accelerated by the update pressure.
- Testing discipline will produce a cleaner directory architecture.
- Log visibility is improving at exactly the right time.
- Forced modernization can eliminate years of deferred cleanup. (techcommunity.microsoft.com)
Risks and Concerns
The downside is just as obvious: hardening changes are landing in environments where operational tolerance is low and architectural debt is often high. If the issue in the wild is truly tied to LSASS crashes and reboot loops, then the risk is no longer theoretical. It becomes a possible availability event with authentication, security, and business continuity consequences all at once. (learn.microsoft.com)- Domain controller reboot loops can cascade into enterprise-wide outages.
- PAM lockouts may leave administrators without recovery paths.
- Legacy service accounts may fail when RC4 is no longer negotiated.
- Hybrid environments may experience partial, confusing failures.
- Misdiagnosis can waste critical recovery time.
- Delayed patch testing increases the odds of a bad rollout.
- Security-first updates can still produce unacceptable downtime if tested poorly. (techcommunity.microsoft.com)
Looking Ahead
The next few weeks will tell us whether the April 2026 reports remain a narrow enterprise-specific problem or broaden into a more formal Microsoft support issue. Watch for additional release-health notes, support bulletins, and clarified mitigation guidance, because that is where Microsoft typically distinguishes between a general security change and a specific product defect. The absence of a single universal fix today does not mean one will not arrive soon. (techcommunity.microsoft.com)What enterprise teams should care about most is not the headline, but the migration path. If your organization still has unreviewed RC4 usage, uncertain PAM dependencies, or domain controllers that were never stress-tested under modern Kerberos defaults, the April 2026 cycle is your warning shot. The real objective is not merely to survive this month’s updates, but to enter July 2026 with no surprises left in the authentication stack. (techcommunity.microsoft.com)
- Monitor Microsoft release health for new entries tied to LSASS or domain controllers.
- Track RC4 audit logs before enforcement tightens further.
- Rehearse rollback and recovery on isolated controllers.
- Validate PAM break-glass access under real outage conditions.
- Inventory legacy Kerberos dependencies before they become outages. (techcommunity.microsoft.com)
Source: thewincentral.com Windows April 2026 update bug, LSASS crash, reboot loop fix - WinCentral