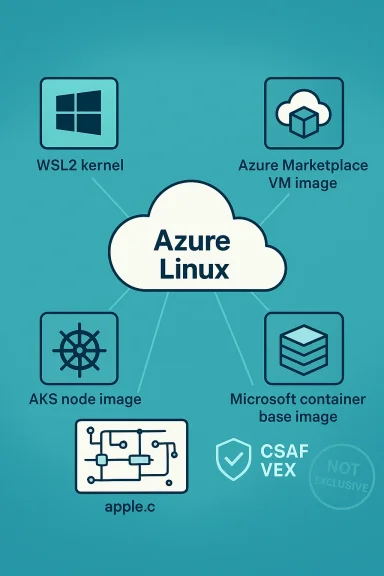
Microsoft’s short MSRC phrasing that “Azure Linux includes this open‑source library and is therefore potentially affected” is an authoritative, product‑scoped inventory statement — but it is not a certificate of exclusivity: Azure Linux is the only Microsoft product Microsoft has publicly attested so far to include the upstream NVMe code implicated by CVE‑2024‑43913, yet other Microsoft artifacts that ship or embed Linux kernels could still carry the same vulnerable driver until they are individually inventoried or attested.
CVE‑2024‑43913 is a Linux‑kernel vulnerability addressed upstream in August 2024 and described in public vulnerability databases as “nvme: apple: fix device reference counting.” The flaw stems from incorrect pairing of nvme_init_ctrl() and nvme_uninit_ctrl() in Apple’s NVMe driver, which could leak controller device memory on certain error paths (a tagset failure), producing availability problems on affected hosts. The fix split allocation and initialization logic to make cleanup deterministic and to ensure nvme_uninit_ctrl() is always called after a successful init.
From a technical standpoint this is a resource‑lifetime bug (CWE‑401): it doesn’t change cryptographic primitives or access controls, but it can steadily consume kernel resources and in the worst case cause stability or DoS symptoms on hosts that load the Apple NVMe driver. Multiple distro trackers and advisories (Ubuntu, Debian, SUSE, vendor errata and OSV) record fixes and mapped kernel series (fixed in kernel stable backports and specified kernel versions).
Why Microsoft’s VEX/CSAF approach matters:
Longer operational framing: any Microsoft artifact that ships a Linux kernel buildrable commit range and the Apple NVMe driver (or a backport of it) could, in principle, carry the same vulnerability until Microsoft either attests those products as Not Affected or Known Affected in its VEX/CSAF feed — or until you verify them via your own artifact scanning and SBOMs. Common places where the same upstream kernel code can appear include Azure Marketplace images, vendor curated VM images, AKS node images, WSL2 kernels, or appliance/edge images distributed by Microsoft or partners.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE‑2024‑43913 is a Linux‑kernel vulnerability addressed upstream in August 2024 and described in public vulnerability databases as “nvme: apple: fix device reference counting.” The flaw stems from incorrect pairing of nvme_init_ctrl() and nvme_uninit_ctrl() in Apple’s NVMe driver, which could leak controller device memory on certain error paths (a tagset failure), producing availability problems on affected hosts. The fix split allocation and initialization logic to make cleanup deterministic and to ensure nvme_uninit_ctrl() is always called after a successful init.From a technical standpoint this is a resource‑lifetime bug (CWE‑401): it doesn’t change cryptographic primitives or access controls, but it can steadily consume kernel resources and in the worst case cause stability or DoS symptoms on hosts that load the Apple NVMe driver. Multiple distro trackers and advisories (Ubuntu, Debian, SUSE, vendor errata and OSV) record fixes and mapped kernel series (fixed in kernel stable backports and specified kernel versions).
What Microsoft actually said — and why that phrasing matters
Microsoft’s Security Response Center (MSRC) has adopted a machine‑readable attestation model (CSAF/VEX) and began a phased rollout that started with Azure Linux. For many third‑party CVEs the MSRC advisory text contains one of two short inventory sentences: either “Product X includes this open‑source library and is therefore potentially affected” or a “Not affected” / “Under investigation” attestation. Those product‑scoped attestations are intentionally narrow: they state what Microsoft has inspected and confirmed for a named product family, not a global statement about all Microsoft artifacts.Why Microsoft’s VEX/CSAF approach matters:
- It gives actionable certainty for the named prtomers know they must treat their images as in‑scope).
- It enables automation (security tooling can parse machine‑readable attestation to prioritize remediation).
- But it also creates a perception risk: absent other attestations, customers may mistakenly infer exclusivity — that only Azure Linux carries the component — which is not what Microsoft’s statement intends.
Short, operational answer to the user’s question
- Is Azure Linux the only Microsoft product that includes this open‑source library and is therefore potentially affected by CVE‑2024‑43913?
Longer operational framing: any Microsoft artifact that ships a Linux kernel buildrable commit range and the Apple NVMe driver (or a backport of it) could, in principle, carry the same vulnerability until Microsoft either attests those products as Not Affected or Known Affected in its VEX/CSAF feed — or until you verify them via your own artifact scanning and SBOMs. Common places where the same upstream kernel code can appear include Azure Marketplace images, vendor curated VM images, AKS node images, WSL2 kernels, or appliance/edge images distributed by Microsoft or partners.
Technical verification: how to prove whether a given Microsoft artifact is affected
When a vendor’s advisory names one product, defenders still need an artifact‑level verification workflow. Here’s a checklist you can frk for Microsoft images and for any other vendor artifacts.- Inventory artifacts that run Linux kernels in your estate:
- Azure Linux images (already attested).
- Azure Marketplace images and curated VM images.
- AKS node images and custom node pools.
- WSL2 kernels shipped by Windows Update.
- Any Microsoft‑published container base images that include kernel modules or build toolchains.
- Partner/appliance images acquired through Microsoft’s marketplace.
- Identify kernel versions and builds:
- Boot a representative image and run uname -a / cat /proc/version to get the kernel version and build identifier.
- Inspect kernel config (zcat /proc/config.gz or check the distro’s kernel-config package) to determine if the Apple NVMe driver (drivers/nvme/host/apple.c) is included or built as a module.
- Map kernel version to upstream commits:
- Use OSV / NVD / distro advisories and the upstream kernel commit list to find whether the vulnerable commit range is present in that version. OSV and the kernel stable commit history both list the commits that introduced and fixed CVE‑2024‑43913.
- If the module is present, check for the fix:
- Compare your package changelog or kernel package metadata against the upstream commit IDs (OSV lists the kernel stable commit links and fixed ranges, which lets you verify whether the fix is included). If your kernel package changelog names the backport commit or the vendor advisory lists the fixed version (Ubuntu’s USN entries do this), treat that as authoritative.
- If you cannot patch immediately, apply mitigations:
- Avoid loading the apple NVMe driver (blacklist the module) on hosts that do not need Apple NVMe support.
- Where the driver is built‑in, plan an expedited kernel update or a rebuild with the fix. (Blacklisting may be d or OEM kernels.)
Why attestation for one product is useful — and why it’s limited
Strengths- Clarity for customers: The MSRC Azure Linux attestation reduces immediate uncertaintomers and allows automation and prioritization of patching workflows. Microsoft’s VEX/CSAF publishing program is designed to support this exact automation use case.
- Speed: Vendors can triage and publish product‑scoped attestations faster than they can enumerate every binary they ship; starting with Azure Linux makes sense operationally.
- Inventory incompleteness: Microsoft builds and ships many Linux kernel artifacts and images. A product‑level attestation for Azure Linux is not evidence that every Microsoft image or kernel is free of the vulnerable code. Absence of attestation is not the same as proof of absence.
- Binary and build reuse: The same upstream driver or backport may be pulled into many images via shared build tooling or vendor packaging. A vulnerability in upstream source propagates through artifacts depending on build choices (kernel version, enabled CONFIG_ flags, vendor backports).
Recommended remediation and verification t customers
Follow this prioritized, pragmatic playbook to reduce exposure and operational risk across Microsoft‑supplied artifacts.- Immediate (hours):
- Patch Azure Linux images first, per MSRC guidance. Microsoft’s attestation makes Azure Linux a highest‑priority remediation target.
- Inventory any Azure VMs and AKS node pools that run Azure Linux images and stage kernel package updates into test slots.
- Near term (1–7 days):
- Run artifact discovery for other Microsoft images you consume:
- Harvest SBOMs from vendor pages or use image scanners to detect presence of the apple NVMe code.
- Inspect WSL2 kernel versines (Windows brings a Microsoft‑supplied kernel to WSL2 workloads — check the shipped version and config).
- For images you cannot patch immediately, apply targeted mitigations (module blacklisting, access restrictions, or host isolation).
- Medium term (1–4 weeks):
- Rebuild or redeploy patched kernels where required. Prefer vendor‑supplied fixed packages (Ubuntu USNs, SUSE errata, Debian trackeovide package‑level mappings).
- Integrate MSRC VEX/CSAF attestations into your vulnerability automation once they become available for additional Microsoft products; this will allow you to treat Microsoft’s attestations as authoritative in tooling.
- Ongoing:
- Treat vendor attestations as inputs to your artifact inventory rather than conclusive proofs. Continue to run periodic SBOM scans and image inspections for software you run or publish.
How to check Microsoft artifacts specifically (concrete checks)
- WSL2 kernels:
- On Windows hosts, check the WSL2 kernel package version delivered by Windows Update or the kernel shipped with WSL2 distributions. If the kernel version predates the fixed kernel stable branch (for example, kernels earlier than the fixed upstream versions listed in OSV), assume further verification is needed.
- Azure Marketplace / VM images:
- Boot an image and check uname -a and the kernel package changelog. For managed images, check the marketplace listing metadata and any published SBOM/VEX attestations for that image family. If Microsoft has not published a VEX attestation for that image, treat the artifact as unverified.
- AKS / Kubernetes node pools:
- Confirm the node image type and kernel version (node-level uname / /var/log/dpkg/rpm package metadata). If nodes run vendor kernels that include the vulnerable tree, schedule rolling upgrades to patched node images.
- Microsoft‑provided containers and SDKs:
- Container base images rarely carry kernel drivers, but build toolchains or published artifacts (e.g., signed kernel modules in appliances) can. Scan images for able source or module names and check linked SBOMs.
Critical analysis — strengths and risks of Microsoft’s approach
Strengths- Microsoft’s early attestation for Azure Linux gives a clear, executable signal to users who run that distro, reducing time‑to‑remediation. Machine‑readable VEX/CSAF files scale better for automation than prose advisories.
- Publishing attestation data for a curated product (Azure Linux / formerly CBL‑Mariner) lets Microsoft close a practical gap: many customers consume Azure Linux images directly and needed precise mapping.
- The phased rollout leaves a temporary “attestation gap” for other Microsoft artifacts. Customers who depend on multiple Microsoft images can be left uncertain about which Microsoft artifacts are carriers — and many customers will lack the internal tooling to instrument every image, kernel, and build artifact at scale.
- The semantics of “includes this library” are sometimes misunderstood; defenders may assume a single attested product implies company‑wide exclusivity. That misunderstanding carries operational risk if teams deprioritize artifact scans for other images.
- Finally, backport fragmentation across vendors means that fixed‑version numbers don’t always tell the whole story; you must verify that the specific kernel package or build you run includes the upstream commit that contains the fix (OSV and kernel stable commit links can help here).
Practical detection signals & forensic steps
If you suspect exploitation or resource exhaustion tied to this CVE, collect:- Kernel logs (dmesg, journalctl -k) for controller allocation errors or memory allocation failures in NVMe or apple NVMe paths.
- /proc and driver debugfs counters related to NVMe controllers and device counts.
- Kernel package version and full uname output for correlation with OSV/NVD/Ubuntu advisories.
- Preserve dmesg and kdump data before any reboot when feasible.
- Reproduce in a controlled lab using the same kernel package or image to confirm symptoms.
- Confirm fix presence by checking for the upstream commit IDs referenced in OSV/kernel stable notes applied to your kernel package.
Bottom line and recommended next steps
- Treat Microsoft’s Azure Linux attestation as authoritative for Azure Linux: patch those images immediately per vendor guidance. Microsoft’s VEX/CSAF program is directly intended to make that easy and machine‑actionable.
- Do not infer exclusivity from that attestation. Inventory and verify other Microsoft‑supplied kernels and images in your environment — WSL2 kernels, Marketplace images, AKS nodes, and appliance images can all carry upstream kernel code depending on build choices.
- Use the upstream and distro signals to confirm the presence of the fix: OSV lists kernel commit references and the fixed kernel ranges; distro advisories (Ubuntu USNs, Debian trackers, SLES errata) list package‑level fixes that you should install.
- Incorporate Microsoft’s CSAF/VEX feed into your patch‑automation pipeline as the company expands attestations beyond Azure Linux; until VEX covers additional products, rely on artifact‑level checks and SBOMs to close blind spots.
Source: MSRC Security Update Guide - Microsoft Security Response Center