Microsoft’s short, public mapping that “Azure Linux includes this open‑source library and is therefore potentially affected” is a precise product‑level attestation — useful, authoritative for Azure Linux customers, and deliberately not a categorical guarantee that no other Microsoft product ever ships the same vulnerable Linux kernel code. ps://www.microsoft.com/en-us/msrc/blog/2025/10/toward-greater-transparency-machine-readable-vulnerability-exploitability-xchange-for-azure-linux)
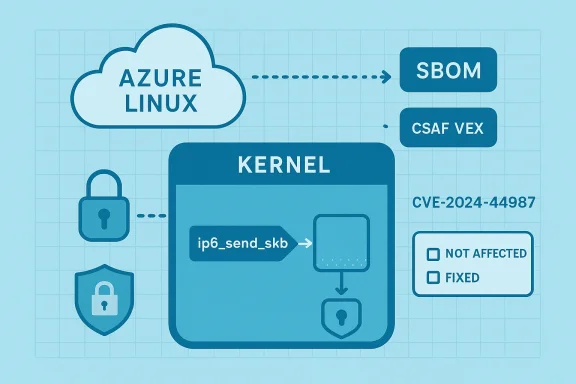
CVE-2024-44987 is a Linux kernel security defect reported by syzbot and tracked publicly as an IPv6 use‑after‑free (UAF) in the ip6_send_skb() code path. The upstream kernel maintainers describe the root cause as dereferencing a route pointer (rt) after ip6_local_out() has returned, without holding the required RCU read lock; that race leads to a possible UAF and memory corruption. The kernel CVE announcement documents the bug, the KASAN trace that exposed it, and the stable commits that close the race.
Practically speaking, the vulnerability is a local‑access kernel memory safety issue: an attacker with local write/execute capability on a host could trigger memory corruption through the IPv6 transmit path. Public scoring varies by vendor, but community sources place the base impact at high (CVSS v3.x scores reported around 7.8), while some distro advisories classify the practical impact for their images as medium because exploitation is constrained by local access requirements. Regardless, the upstream guidance is clear: install the kernel updates that include the fix or apply the upstream commits.
From a technical standpoint, the bug is well described and fixed upstream; distribution vendors have begun shipping updates and advisories that map the fix into distro kernels. The most reliable defender‑facing path is the one the kernel community recommends: install a vendor‑supplied kernel that contains the upstream fixes, or apply the upstream patch set under careful change control.
In short: Azure Linux is the Microsoft product Microsoft has publicly confirmed for CVE‑2024‑44987 — and that confirmation is meaningful for Azure Linux customers. However, the inherent realities of shared upstream code, multiple vendor artifacts, and phased attestation rollouts mean Azure Linux is not, in practice, guaranteed to be the only Microsoft product that could carry the vulnerable ip6_send_skb() code. Until Microsoft’s VEX/CSAF coverage expands and other products are explicitly ruled out or marked fixed, operators should verify other Microsoft artifacts in their environments using SBOMs, package metadata, and vendor advisories — and apply updates where needed.
Conclusion
Treat Microsoft’s Azure Linux attestation as an authoritative, actionable inventory signal for the Azure Linux family — patch those images now. Treat the absence of attestations for other Microsoft products as lack of information, not evidence of safety. Use the technical kernel commits and vendor advisories to confirm whether each Microsoft artifact you run includes the upstream fix; automate what you can, verify what you must, and prioritize patching where Microsoft has already confirmed exposure.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE-2024-44987 is a Linux kernel security defect reported by syzbot and tracked publicly as an IPv6 use‑after‑free (UAF) in the ip6_send_skb() code path. The upstream kernel maintainers describe the root cause as dereferencing a route pointer (rt) after ip6_local_out() has returned, without holding the required RCU read lock; that race leads to a possible UAF and memory corruption. The kernel CVE announcement documents the bug, the KASAN trace that exposed it, and the stable commits that close the race.Practically speaking, the vulnerability is a local‑access kernel memory safety issue: an attacker with local write/execute capability on a host could trigger memory corruption through the IPv6 transmit path. Public scoring varies by vendor, but community sources place the base impact at high (CVSS v3.x scores reported around 7.8), while some distro advisories classify the practical impact for their images as medium because exploitation is constrained by local access requirements. Regardless, the upstream guidance is clear: install the kernel updates that include the fix or apply the upstream commits.
What Microsoft actually said — and what that wording means
The literal MSRC mapping
Microsoft’s public advisory language for some third‑party CVEs follows a short, consistent pattern: when Microsoft has inspected a Microsoft product image and found the implicated upstream component, the MSRC entry will say something like “Azure Linux includes this open‑source library and is therefore potentially nce is an inventory attestation — it confirms Microsoft’s inspection of the Azure Linux artifacts and a finding that the upstream code is present. Microsoft also states it will expand its machine‑readable CSAF/VEX mappings and update CVE records if additional Microsoft products are later identified as carriers.Attestation ≠ exclusivity
This language is not the same thing as, and should not be read as, an exclusivity guarantee. A product‑level attestation says: “we checked this product and it contains the upstream component,” not “we checked every Microsoft product and only this product contains it.” Microsoft’s public posture around VEX/CSAF makes that distinction explicit: the company started publishing machine‑readable VEX attestations beginning with Azure Linux and will incrementally onboard more products and update mappings when discoveries are made. That rollout schedule is procedural — it explains how Microsoft will reduce blind spots over time, but it does not retroactively prove that other artifacts are unaffected.The short, precise answer to the user’s question
- Is Azure Linux the only Microsoft product that includes the open‑source library and is therefore potentially affected by CVE‑2024‑44987?
Why the distinction matters to defenders and operators
Kernel code is an artifact‑level property
Whether a particular Microsoft image or product carries the vulnerable code depends on three independent factors:- Kernel version and upstream commit range (which commits are merged or backported).
- Kernel configuration (CONFIG_* flags enabling or disabling IPv6 subsystems).
- Packaging and distribution choices (is the code compiled in, built as a module, or trimmed out).
Operational consequences
- For customers running Azure Linux images, Microsoft’s attestation is a direct signal: treat those images as in‑scope, follow Microsoft’s update recommendations, and patch promptly.
- For customers running other Microsoft images or appliances (WSL2 kernel updates, Azure Marketplace images, AKS node images, custom VM images created from Microsoft base images), do not assume safety based solely on the absence of an MSRC attestation. Instead, perform artifact‑level verification (SBOM/package inspection) or await an explicit Microsoft VEX/CSAF update.
Technical details (for engineers)
What the bug is and why RCU matters
- The vulnerability sits in net/ipv6/ip6_output.c, inside ip6_send_skb(). After ip6_local_out() returns, code continued to dereference a route object (rt) without holding rcu_read_lock(), producing a race where the route could be freed concurrently — the textbook use‑after‑free scenario in the kernel. The kernel‑level sanitizer (KASAN) reported this under syzbot testing, producing a slab UAF stack trace that guided the upstream fix.
- The correct approach is to guarantee the lifetime of the route object across the dereference, usually by holding the RCU read lock across the code path or switching to RCU‑aware accessors. Upstream kernel commits apply that fix pattern and have been backported into multiple stable branches.
Which kernel commits/versions fix it
The linux‑cve‑announce entry and distribution advisories list the stable commits that close the issue and the kernel versions where the fix first appears. Upstream maintainers marked the bug as introduced long ago (in early 2.6.x history) but fixed in more recent stable releases via targeted commits. Operators should rely on vendor‑shipped kernel updates or the specific upstream commits rather than attempting piecemeal cherry‑picks unless they understand backport risk.How to determine whether your Microsoft‑supplied artifact is affected
Follow these concrete steps — a checklist you can apply to any Microsoft artifact you operate:- Identify the artifact and where its kernel or runtime was built from (image SKU, version, and published SBOM if available).
- Determine the kernel version or git commit range shipped in that artifact. If you cannot get a kernel version from the vendor metadata, boot the image and run uname -r and inspect /proc/version or packaged kernel RPM/DEB metadata.
- Cross‑reference the kernel version against the upstream CVE mappings and the kernel‑stable git commits that fix CVE‑2024‑44987. If the kernel version predates the fix commits and no vendor backport has been applied, treat it as possibly affected.
- Inspect kernel configuration if possible. If IPv6 transmit code (net/ipv6) is disabled by CONFIG settings in the build, the attack surface may be reduced, though disabling IPv6 is not a universal mitigation for environments that require IPv6.
- Check MSRC’s CSAF/VEX catalog and Microsoft CVE pages for updates. Microsoft has committed to publishing VEX attestations and updating records when additional products are discovered to ship the implicated component. Use the vendor attestations as authoritative when present.
Practical mitigations and response actions
- Prioritize patching Microsoft‑attested Azure Linux images first: those are explicitly in‑scope. Microsoft’s attestations exist to enable exactly the prioritized response of patching known affected artifacts.
- For other Microsoft images (WSL2, Azure VM SKUs, AKS node images, marketplace appliances), perform the artifact verification checklist above. If verification is not possible or reveals an older kernel, treat the artifact as vulnerable until the vendor publishes a Not Affected/Fixed attestation.
- If you manage many images or a large fleet, automate detection:
- Use image scanning tools that can read kernel package RPM/DEB versions and map them to CVE fixes.
- Ingest Microsoft’s machine‑readable CSAF/VEX files when available to automate product‑level triage.
- Maintain an internal SBOM and inventory that ties runtime artifacts back to the kernel versions they include.
- As a short‑term hardening measure, reduce local exposure to untrusted users where possible: isolate multi‑tenant workloads, lower privileges for containers/VMs, and restrict local access vectors. This is defensive in depth and does not replace patching.
Cross‑checking Microsoft’s wording with independent records
To produce a verifiable mapping you can rely on today, cross‑reference at least two independent sources:- Upstream kernel announcement (linux‑cve‑announce) provides the technical description, KASAN trace origin, and the specific stable commits that close CVE‑2024‑44987. This is the canonical technical narrative for what changed and why.
- Distribution advisories (Oracle Linux, Amazon Linux, Azure Linux notices) show which distros have packaged and published fixes for their kernel builds. Those advisories confirm that vendors shipping kernel images for cloud and distro consumers have rolled the upstream fix into their update streams. For example, Oracle’s CVE entry and Amazon Linux’s ALAS advisory list the CVE and their remediation packages.
- Microsoft’s public MSRC wording and VEX rollout statement explain Microsoft’s inventory and attestation approach — naming Azure Linux as the product checked while committing to expand attestations to other products over time. Treat the MSRC wording as an authoritative inventory signal for the artifacts it names.
Risks, limits, and things to watch
Risk: false security from omission
- The absence of a Microsoft attestation for a product is not proof that the product is safe. Because Microsoft’s initial VEX rollout prioritized Azure Linux, many other Microsoft artifacts may remain un‑attested simply due to the phased implementation. Relying on absence of mention as an indicator of absence of risk is a dangerous operational assumption.
Risk: backports and inconsistent patching
- Vendors sometimes backport fixes into older kernel branches in ways that are not obvious from version numbers alone. A vendor may have applied the fix to a 5.x or 4.x branch while the version string appears older. Conversely, a kernel with a later version number could be missing a targeted backport if the vendor re‑built from a snapshot that predates the fix. This makes automated version checks error‑prone unless the vendor’s changelog or SBOM explicitly documents the patch. Cross‑check vendor advisories and CVE trackers for the presence of the fix.
Risk: incomplete automation
- Automated scanners and third‑party feeds may lag vendor attestations or misclassify artifacts when vendor VEX/CSAF files are not yet published. Where possible, combine automated scanning with manual confirmation for high‑value artifacts.
Recommendations — prioritized checklist for IT teams
- Patch Azure Linux images immediately: Microsoft has attested Azure Linux as a carrier and vendors/maintainers have packaged updates. Apply the vendor kernel updates as a priority.
- Inventory Microsoft artifacts in your environment that carry Linux kernels (AKS nodes, Azure VM SKUs, WSL2 kernel on developer machines, Marketplace appliances). Use SBOMs, image metadata, and package queries to find kernel versions and package IDs.
- Cross‑reference identified kernel versions against the upstream CVE fixes listed in linux‑cve‑announce and the distro advisories. If the kernel predates the fix, treat the artifact as potentially affected.
- If artifact verification is infeasible, isolate or restrict access to minimize local‑attacker attack surface until the artifact is validated or patched.
- Subscribe to MSRC CSAF/VEX feeds and vendor advisories for automated ingestion as Microsoft expands attestations beyond Azure Linux. When Microsoft marks additional products as Known Affected / Fixed, update your triage and patching accordingly.
Final analysis and outlook
Microsoft’s message that “Azure Linux includes this open‑source library and is therefore potentially affected” is a clear, operationally useful attestation: if you run Azure Linux, act now and install the updates Microsoft publishes. At the same time, the statement is deliberately scoped and procedural: Microsoft will expand its CSAF/VEX attestations and update CVE records if it finds additional Microsoft products that ship the same upstream component. That means customers who run other Microsoft artifacts should not assume safety by default; they should verify artifact contents or wait for Microsoft to publish additional attestations.From a technical standpoint, the bug is well described and fixed upstream; distribution vendors have begun shipping updates and advisories that map the fix into distro kernels. The most reliable defender‑facing path is the one the kernel community recommends: install a vendor‑supplied kernel that contains the upstream fixes, or apply the upstream patch set under careful change control.
In short: Azure Linux is the Microsoft product Microsoft has publicly confirmed for CVE‑2024‑44987 — and that confirmation is meaningful for Azure Linux customers. However, the inherent realities of shared upstream code, multiple vendor artifacts, and phased attestation rollouts mean Azure Linux is not, in practice, guaranteed to be the only Microsoft product that could carry the vulnerable ip6_send_skb() code. Until Microsoft’s VEX/CSAF coverage expands and other products are explicitly ruled out or marked fixed, operators should verify other Microsoft artifacts in their environments using SBOMs, package metadata, and vendor advisories — and apply updates where needed.
Conclusion
Treat Microsoft’s Azure Linux attestation as an authoritative, actionable inventory signal for the Azure Linux family — patch those images now. Treat the absence of attestations for other Microsoft products as lack of information, not evidence of safety. Use the technical kernel commits and vendor advisories to confirm whether each Microsoft artifact you run includes the upstream fix; automate what you can, verify what you must, and prioritize patching where Microsoft has already confirmed exposure.
Source: MSRC Security Update Guide - Microsoft Security Response Center