Microsoft’s brief MSRC attestation that “Azure Linux includes this open‑source library and is therefore potentially affected” is accurate — but it is a product‑scoped inventory statement, not a categorical proof that no other Microsoft product or image can contain the same vulnerable Linux kernel code.
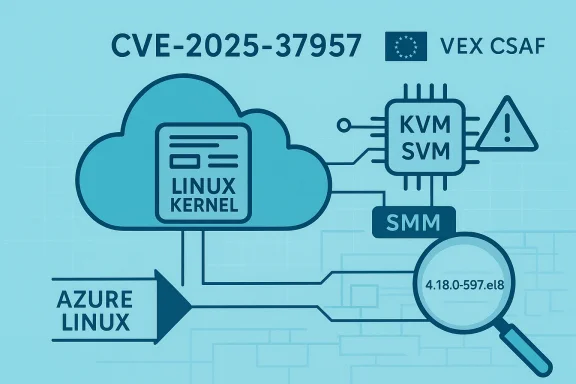
CVE‑2025‑37957 is a Linux kernel vulnerability in the KVM SVM codepath that concerns how the hypervisor handles System Management Mode (SMM) during a SHUTDOWN interception. Under a crafted sequence (reported as reproducible with Syzkaller), a virtual CPU (vCPU) that has been driven into SMM via a KVM_SMI ioctl can be left in SMM when KVM forces an INIT after a SHUTDOWN interception; that mis‑ordering triggers a kernel WARN and undefined behavior. The upstream fix forces KVM to exit SMM mode before applying INIT on SHUTDOWN interception, closing the race/logic gap.
Security vendors and distributors classify the flaw as an important, host/guest‑adjacent kernel correctness bug with CVSS scores in the mid‑7 range (NVD and vendor score variants; see vendor advisories). The issue is primarily an availability and stability risk — kernel WARNs, vCPU panics, or guest/host instability under nested or manipulated SMM conditions — rather than a straightforward remote code‑execution primitive.
Microsoft’s public advisory text for the CVE (the line you quoted) is typical of the new machine‑readable VEX/CSAF attestation approach: it indicates that Microsoft has mapped the upstream vulnerable component to a specific Microsoft product (Azure Linux) and has published that attestation; Microsoft also says it will update the CVE/VEX entry if additional Microsoft products are later identified. This is a transparency and inventory statement, not a global exclusion.
However, that statement is not a guarantee that Azure Linux is the only Microsoft product that could possibly contain the vulnerable Linux kernel code. Absence of a VEX/CSAF line for other Microsoft products simply means Microsoft’s inventory and attestation work for those products is not yet complete or published; it does not prove those products are unaffected. Operators must therefore verify per artifact — especially WSL kernels, Marketplace images, and any Microsoft‑distributed kernels in their estate — and apply upstream or vendor patches as soon as practical.
The bottom line for defenders: treat the Azure Linux attestation as urgent and authoritative for Azure Linux, but extend your inquiry and remediation to other Microsoft artifacts you run — inventory, inspect, and patch. Microsoft’s VEX rollout will make future attestations clearer, but until then, operational verification remains the only reliable way to establish whether a given Microsoft artifact is affected.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE‑2025‑37957 is a Linux kernel vulnerability in the KVM SVM codepath that concerns how the hypervisor handles System Management Mode (SMM) during a SHUTDOWN interception. Under a crafted sequence (reported as reproducible with Syzkaller), a virtual CPU (vCPU) that has been driven into SMM via a KVM_SMI ioctl can be left in SMM when KVM forces an INIT after a SHUTDOWN interception; that mis‑ordering triggers a kernel WARN and undefined behavior. The upstream fix forces KVM to exit SMM mode before applying INIT on SHUTDOWN interception, closing the race/logic gap.Security vendors and distributors classify the flaw as an important, host/guest‑adjacent kernel correctness bug with CVSS scores in the mid‑7 range (NVD and vendor score variants; see vendor advisories). The issue is primarily an availability and stability risk — kernel WARNs, vCPU panics, or guest/host instability under nested or manipulated SMM conditions — rather than a straightforward remote code‑execution primitive.
Microsoft’s public advisory text for the CVE (the line you quoted) is typical of the new machine‑readable VEX/CSAF attestation approach: it indicates that Microsoft has mapped the upstream vulnerable component to a specific Microsoft product (Azure Linux) and has published that attestation; Microsoft also says it will update the CVE/VEX entry if additional Microsoft products are later identified. This is a transparency and inventory statement, not a global exclusion.
What Microsoft’s attestation actually says — and what it doesn’t
The safe, literal reading
- Microsoft confirmed that one of its products, Azure Linux, includes the implicated upstream component and therefore that product family is potentially affected. That confirmation is authoritative for Azure Linux images.
What the attestation does not mean
- The attestation does not mean other Microsoft artifacts (other Linux kernels Microsoft builds or ships, Marketplace images, WSL2 kernels, or custom Azure images built from Microsoft bases) categorically do not include the same vulnerable code. Absence of an attestation is not proof of absence. Independent verification is required for other images.
- The wording does not change the underlying technical scope of the CVE: it’s an upstream Linux kernel fix. Any compiled kernel binary that contains the pre‑fix commit range is potentially vulnerable if it exposes the relevant KVM SVM codepath. That includes kernels Microsoft builds and distributes if those kernels incorporate the un‑fixed upstream commits.
Why people read “Azure Linux only” — and why that can be dangerous
There are practical reasons readers might interpret Microsoft’s single‑sentence advisory as “Azure Linux only”:- Microsoft chose a phased, product‑first rollout for machine‑readable VEX/CSAF attestations, starting with the Azure Linux distribution to validate the process and data. That means initial VEX entries will show Azure Linux as “known affected” sooner than other product inventories are completed.
- The advisory language is short and technical audiences often scan for a single line that names a product; if that single line names Azure Linux and nothing else, casual readers can mistake “attested product” for “only product.” Windows Forum analyses and community threads have observed this recurring pattern and repeatedly caution operators not to assume exclusivity.
Which Microsoft artifacts could plausibly carry the vulnerable code?
It’s helpful to think of Microsoft’s Linux‑related artifacts in categories and evaluate where the upstream KVM SVM code might appear:- Azure Linux images (attested): Microsoft has completed inventory and attested these images as including the implicated component; treat them as confirmed in‑scope until patched.
- Azure Marketplace or curated VM/container images: Marketplace images sometimes include Microsoft‑built kernel packages or vendor kernels; those images must be checked individually. Absence of a Microsoft VEX statement does not guarantee they are clean.
- WSL2 kernel builds: Microsoft maintains a WSL2 Linux kernel fork and publishes kernel sources/binary artifacts for WSL. That kernel historically includes a broad swath of Linux subsystems (including DRM/gpu code and, in many builds, virtualization support). Whether a particular WSL kernel build is vulnerable depends on its kernel version and whether the vulnerable commit range is present. Local inspection is required. Do not assume WSL kernels are safe simply because they are not named in the MSRC line.
- Other Microsoft‑distributed kernels (container hosts, Azure‑hosted hypervisor tooling, CI images): Any Microsoft‑distributed kernel image that was built from an upstream tree before the fix may contain the vulnerable code. Microsoft’s promise to update CVE/VEX records if more products are identified means they will expand attestations over time; until then, independent checks are required.
Technical summary of CVE‑2025‑37957 (concise)
- Component: Linux kernel — KVM SVM backend (x86 AMD SVM path).
- Root cause: KVM did not forcibly exit SMM before issuing an INIT on SHUTDOWN interception; prior fixes for nested mode did not account for SMM. The result: a WARN and undefined state under a crafted sequence (enter SMM, cause consecutive exceptions and triple fault, then KVM forces INIT while still in SMM).
- Impact classification: Host/guest stability, kernel WARNs, possible guest or host availability impact under manipulated conditions; not widely reported as a remote exploit in the wild at disclosure.
- Typical remediation: upstream kernel patch — force exit from SMM on SHUTDOWN interception — backport to stable trees and distribution kernels by vendors.
Practical guidance for administrators and defenders
1) Treat Microsoft’s Azure Linux attestation as authoritative security guidance for Azure Linux images — and act quickly
If you run Azure Linux images in production (VMs, container hosts, AKS node pools built on Azure Linux), follow Microsoft’s patch guidance and the distribution’s security advisories and remediate promptly. MSRC’s VEX/CSAF attestation is a direct signal to prioritize Azure Linux assets.2) Inventory Microsoft‑distributed Linux artifacts in your estate
Do not stop at “Azure Linux.” Identify and record where Microsoft‑built Linux kernels or Microsoft‑published images are used:- WSL2 instances on developer and CI hosts that use the Microsoft WSL kernel.
- Marketplace VM images and curated container base images published by Microsoft.
- Any Azure Marketplace images that include Microsoft packaging.
- Azure VM images used as CI/build agents or ephemeral hosts that could host nested virtualization tests.
- Run uname -r on Linux hosts and record kernel version strings.
- For packaged kernels, check package changelogs for backports or CVE fixes.
- Inspect kernel module trees for the KVM SVM files: ls /lib/modules/$(uname -r)/kernel/arch/x86/kvm and grep for svm.c presence.
3) Verify whether WSL2 kernels in your environment include the vulnerable commit range
WSL2’s kernel builds vary by release and build date. If your developers use WSL2 with the Microsoft‑provided kernel (not a user‑compiled kernel), verify the kernel version and whether Microsoft has published a WSL kernel advisory or patched WSL build. If you run nested virtualization or fuzzing workloads inside WSL, prioritize patching.4) Mitigation where immediate patching is infeasible
If you cannot immediately update kernels across a heterogeneous estate, consider short‑term mitigations to reduce attack surface/reachability:- Avoid running untrusted guests or nested virtualization on hosts that use vulnerable kernels.
- Disable nested virtualization in environments where it is not required.
- Limit capabilities or ioctl surfaces for processes that might invoke KVM_SMI-like functionality (this is an advanced, environment‑specific control).
- Apply vendor kernel upgrades or backports as they become available; vendors typically publish advisories with specific package names and versions.
5) Watch for updated attestations and vendor advisories
Microsoft’s VEX/CSAF program is explicitly phased: initial attestations focused on Azure Linux and will expand. Monitor MSRC for updates to the CVE entry and new VEX lines naming additional Microsoft products; vendors (Red Hat, Debian, Ubuntu, Amazon Linux, etc.) also publish distribution advisories that identify affected kernel package versions and fixes. Cross‑correlate these sources rather than relying on a single statement.Evidence and cross‑checks (what I used to verify claims)
- Distribution and vendor advisories list CVE‑2025‑37957 with descriptions and fixed package versions (Amazon Linux advisory listing fixed kernel6.12 package; Red Hat and other vendor summaries reflect the same root cause and remediation approach). These entries corroborate the technical description and severity.
- Independent vulnerability trackers and analysis summaries (Wiz, OffSeq, Threat Radar) summarize the exploit sequence, Syzkaller reproduction, and upstream fix details; they align with upstream kernel changelogs and the vendor advisories.
- Microsoft’s own transparency blog explains the phased VEX/CSAF rollout (October 2025 start) and the product‑scoped approach that produced Azure Linux‑first attestations; Microsoft explicitly promises to update CVE/VEX entries if more products are positively identified as carriers of the implicated component. That confirms the procedural nature of the single‑line attestation you quoted.
- Community analysis and operational guidance (Windows Forum threads and articles) repeatedly emphasize the point of product‑scoped attestation vs. exclusivity and provide pragmatic steps administrators can use to check other Microsoft artifacts. Those community writeups mirror the conclusions above.
Risks, uncertainties, and unverifiable points
- Microsoft’s attestation process is reliable for Azure Linux images but the presence of the vulnerable code in other Microsoft artifacts is an artifact‑by‑artifact question. Unless Microsoft explicitly attests a product as “Not Affected” or “Fixed,” the only way to be certain is to inspect that specific image/kernel. I cannot, from the public advisories alone, prove a negative for every Microsoft product. This is an inherent inventory problem across large vendors.
- Whether WSL2 kernels in your environment include the vulnerable commit depends on the exact WSL kernel build/version in use; public WSL kernel source trees and build notes indicate WSL kernels include many upstream subsystems including GPU and virtualization components, but concrete vulnerability exposure varies by build. That must be checked per‑host. Do not assume all WSL installations are safe or unsafe without checking.
- There’s no public, widespread exploitation reported for CVE‑2025‑37957 at disclosure; the primary impact is stability. However, attacker creativity in cloud and nested virtualization contexts means availability or targeted denial‑of‑service against multi‑tenant hosts is a real operational concern. The mitigation posture should reflect that risk even where no public exploit is known.
A short, practical checklist (for security teams)
- Identify all Microsoft‑distributed Linux kernels and images in your estate: Azure Linux, WSL2 kernels, Marketplace images, curated images.
- For each identified artifact, check kernel version and vendor patch status (uname -r; package changelog).
- If a kernel is within the affected commit range, schedule an immediate update to a patched vendor kernel or apply the vendor backport.
- Where patching will be delayed, apply temporary mitigations: disable nested virtualization, avoid running untrusted guests on those hosts, and restrict build/test pipelines that use nested virtualization.
- Subscribe to MSRC and distribution advisories and re‑check the CVE/VEX entry for Microsoft products — Microsoft has pledged to update the CVE/VEX mapping if more products are identified.
Conclusion
Microsoft’s statement that “Azure Linux includes this open‑source library and is therefore potentially affected” is a clear, actionable attestation that applies to Azure Linux images and should be treated as an authoritative signal to patch and remediate those images.However, that statement is not a guarantee that Azure Linux is the only Microsoft product that could possibly contain the vulnerable Linux kernel code. Absence of a VEX/CSAF line for other Microsoft products simply means Microsoft’s inventory and attestation work for those products is not yet complete or published; it does not prove those products are unaffected. Operators must therefore verify per artifact — especially WSL kernels, Marketplace images, and any Microsoft‑distributed kernels in their estate — and apply upstream or vendor patches as soon as practical.
The bottom line for defenders: treat the Azure Linux attestation as urgent and authoritative for Azure Linux, but extend your inquiry and remediation to other Microsoft artifacts you run — inventory, inspect, and patch. Microsoft’s VEX rollout will make future attestations clearer, but until then, operational verification remains the only reliable way to establish whether a given Microsoft artifact is affected.
Source: MSRC Security Update Guide - Microsoft Security Response Center