Azure Linux being named in an MSRC advisory does not mean it is the only Microsoft product that could include the vulnerable Linux code — it is the only product Microsoft has attested to contain the upstream component so far, and determining whether other Microsoft artifacts are affected requires artifact-level verification of the kernel builds and configurations those products ship.
Background / Overview
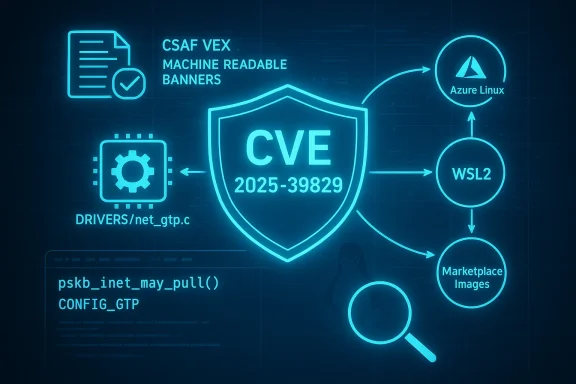
The defect tracked as CVE‑2024‑44999 is a Linux kernel robustness bug in the GTP (GPRS Tunneling Protocol) networking implementation. Upstream maintainers describe the issue as a failure to pull IPv4/IPv6 headers into the skb->head buffer before accessing fields, which leads to use of uninitialized memory as reported by KMSAN/syzbot. The affected source file is drivers/net/gtp.c; the upstream team has assigned the fix and published the commits that remediate the problem. (lists.openwall.net)Short, technical summary:
- Component: Linux kernel GTP implementation (drivers/net/gtp.c). (lists.openwall.net)
- Root cause: accessing IPv4/IPv6 header fields before ensuring header bytes are present in skb->head; fixed by adding pskb_inet_may_pull() calls. (lists.openwall.net)
- Introduced: upstream commit in 4.7; fixed across multiple stable trees and later kernels (fixes landed in stable branches including 4.19.321, 5.4.283, 5.10.225, 5.15.166, 6.1.107, 6.6.48, 6.10.7, and 6.11-rc4). (lists.openwall.net)
What Microsoft actually said — reading the MSRC wording
Microsoft’s public advisory for CVE entries has adopted a machine‑readable VEX/CSAF approach and — for certain third‑party Linux kernel CVEs — has published product‑scoped attestations. In MSRC’s language you will commonly find a statement formatted like:“One of the main benefits to our customers who choose to use the Azure Linux distro is the commitment to keep it up to date with the most recent and most secure versions of the open source libraries with which the distro is composed. Microsoft is committed to transparency in this work which is why we began publishing CSAF/VEX in October 2025. … If impact to additional products is identified, we will update the CVE to reflect this.”
That FAQ-style line is a product attestation: it confirms Microsoft has inventoried Azure Linux and found that Azure Linux does include the upstream component that contains the vulnerable code, and thus Azure Linux images are within scope until patched. It does not, however, state that no other Microsoft product could ever include the same code.
This phrasing is deliberate and operational: Microsoft started publishing CSAF/VEX attestations in a phased rollout (beginning with Azure Linux) to give customers machine-readable guidance about which Microsoft products are known-affected, under investigation, or fixed. The attestation covers a named product family (Azure Linux) and the kernel builds or package versions Microsoft has validated for that product. It is not intended to be a blanket, global inventory of eve ships.
Does that mean Azure Linux is the only Microsoft product that includes the vulnerable code?
Short answer: No — not necessarily. Microsoft’s attestation is a statement of what the company has validated and published to customers so far. It is an authoritative product-level signal for Azure Linux, but it is not, by itself, a comprehensive guarantee that other Microsoft products (images, binaries, or services) do not include the same upstream source file or vulnerable kernel build.Why this distinction matters:
- Kernel source code is upstream and shared. The GTP implementation lives in the mainline kernel. Any product that ships a Linux kernel build that includes the affected upstream commit range and enables the relevant configuration options could carry the vulnerability. Microsoft produces multiple distinct kernel artifacts across its product portfolio (for example, Azure Linux images, specialized Azure Marketplace images, the WSL2 kernel binaries, and other Linux-based offerings). Whether those artifacts include drivers/net/gtp.c — and which upstream commits they contain — depends on:
- The exact kernel version and stable-tree commits used in the build.
- The kernel CONFIG_* options chosen when the kernel was compiled (a driver can be present but built out as a module or omitted entirely).
- Whether the product maintainers backported the security fix into their kernel tree or shipped a stable kernel version that already contains the fix. (lists.openwall.net)
- Microsoft’s VEX/CSAF rollout is phased. Microsoft intentionally started the VEX/CSAF publication with Azure Linux to prove the nd automation; adding attestations for other Microsoft products is an ongoing process. The MSRC FAQ explicitly commits to updating CVE entries if additional products are identified as carriers. That means the current published list of Microsoft-inventoried products is a snapshot of Microsoft’s inventory status at the time of publication, not an exhaustive catalog of all possible carriers.
- Absence of an attestation is not proof of absence. Many organizations — vendors and defenders alike — assume that if a vendor doesn’t name a product in an advisory it is “not affected.” For upstream, shared libraries and kernel components this assumption is unsafe: the definitive way to know is to check the product’s shipped artifacts or published SBOM/VEX/CSAF for the presence of the upstream source and kernel version.
Practical implications for administrators and defenders
If you run Azure Linux- Treat Microsoft’s attestation as authoritative for those Azure Linux images: apply the kernel updates Microsoft recommends (or their distribution’s updated kernel packages) as soon as practical. Microsoft’s VEX/CSAF output for Azure Linux tells you which product builds are known-affected or fixed, and that is actionable.
- Don’t assume “not listed” equals “clean.” Instead, verify. There are three practical approaches:
- Check public attestations and SBOM/VEX/CSAF output for the product in question. Microsoft’s CSAF/VEX corpus is growing; consult the product’s VEX/CSAF entry (if present) to see whether it has been assessed. If a product’s VEX entry is absent, escalate to the vendor or request an attestation.
- Inspect the shipped kernel artifact locally. Simple commands you can run on an image or VM will tell you whether thvulnerable driver and which upstream version it includes:
- Extract kernel version and config:
- uname -a
- zgrep CONFIG_GTP /proc/config.gz (or review /boot/config-$(uname -r))
- Inspect for the driver file in the kernel source tree on packaged source RPMs / kernel-source packages, or:
- For running kernels, search for the module or vmlinux symbol that would indicate the GTP code is present.
- Cross-check the kernel version and vendor backports against the upstream affected/fixed commits listed by the Linux kernel CVE announcement. If the running kernel’s commit range predates the fix, treat it as potentially vulnerable until the fix is backported. (lists.openwall.net)
- Automate fleet scans. For fleet owners, incorporate:
- Kernel-version fingerprints (exact version + vendor-specific backport notation),
- Kernel config checks for the relevant module/driver,
- SBOM harvesting where available,
- A VEX/CSAF ingestion pipeline that maps vendor attestations to deployed artifacts.
Technical remediation and mitigation details
Upstream guidance is straightforward: update to a kernel that includes the upstream fix or cherry‑pick the stable-tree commit that adds the pskb_inet_may_pull() guard calls into the GTP transmit code path. The Linux kernel CVE announcement lists the exact commits in each stable tree that remediate the issue; distribution maintainers either ship updated kernels or backport the fix into their tree. (lists.openwall.net)Why updating the kernel is the recommendation:
- The fix is a code-level defensive change in the kernel network path; the safest and supported approach is to take a vendor-supplied kernel upgrade or the upstream stable patch rather than attempting to patch running systems in the field.
- Cherry-picking individual commits is error‑prone and not supported by the upstream kernel community as a general practice; the kernel team recommends updating to a fixed stable kernel release where possible. (lists.openwall.net)
- Apply compensating controls:
- Limit exposure of services and hosts that process tunneled GTP traffic where feasible.
- Enforce strict network segmentation: GTP is used in mobile network tunneling — hosts that do not need to handle such traffic should not be reachable from networks where such packets might arrive.
- Deploy kernel hardening controls and monitoring to detect anomalous kernel oopses or KMSAN-like warnings if available in your test fleet.
- Public trackers classify this as a serious robustness issue (CVSS 7.1), but exploitation requiring remote code execution is not indicated in the public writeups. The practical impact leans toward information-leak or denial-of-service in impacted configurations. Nevertheless, the graded severity and the presence of uninitialized read paths make the bug worth patching quickly in exposed environments.
How to verify whether a Microsoft artifact (other than Azure Linux) contains the vulnerable kernel code
You will need to perform one or more of the following artifact inspections:- For a shipped image (VM image, container base image, WSL kernel, etc.):
- Boot the image or mount its kernel package.
- Run uname -r and obtain the kernel version string and package metadata.
- Inspect the kernel config for flags that enable GTP (search for CONFIG_GTP or related options).
- If you have the kernel source package (or the vendor-provided source RPM), search for drivers/net/gtp.c and its commit metadata to determine whether the backported fix is present.
- For WSL2 kernels and other Microsoft-provided kernel binaries:
- Microsoft publishes WSL kernel sources or provides kernel release notes for their WSL kernels; cross-check published WSL kernel version and patch notes with the upstream fix commit list.
- If you lack public traces, request a VEX/CSAF attestation for the specific product SKU from Microsoft, or ask for the SBOM/kernel-source package that corresponds to the product. Microsoft has committed to publishing VEX/CSAF outputs over time and to updating CVEs when additional products are identified. (microsoft.com)
- For large fleets:
- Automate the above checks and feed results into your CVE triage pipeline. Match kernel-version fingerprints and the list of known fixed commit hashes to quickly classify hosts as fixed or vulnerable.
Why Microsoft’s product-scoped language is good practice — and where it falls short for defenders
Strengths of Microsoft’s approach- Transparency and machine-readability: publishing VEX/CSAF files (starting with Azure Linux) is an important advance because it allows automated tooling to ingest vendor attestations and reduce false positives. Microsoft’s blog and MSRC posts make clear this was a deliberate phased approach.
- Actionable guidance for Azure Linux customers: for customers who run the attested product, the guidance is clear — patch the Azure Linux kernel/policy. That reduces uncertainty for a large, clearly scoped customer group.
- Potential for misunderstanding: defenders might mistakenly interpret “Azure Linux includes this open-source library and is therefore potentially affected” as a global statement that no other Microsoft artifacts are at risk. That would be an unsafe assumption, because upstream, shared components can be present across multiple product artifacts.
- Phased rollout leaves coverage gaps: until the vendor’s VEX/CSAF coverage is complete across its product catalog, customers running other Microsoft artifacts must still perform artifact-level verification or request attestations. This is a transient operational burden while the vendor’s inventory publication catches up.
Recommendations — what security teams should do now
- If you run Azure Linux images:
- Prioritize applying the kernel updates Microsoft or the Azure Linux project has published for CVE‑2024‑44999. Treat Microsoft’s attestation as definitive inventory for that product family.
- If you run other Microsoft-provided images or services (WSL, Marketplace images, managed nodes, etc.):
- Do not assume absence of a listing equals safe. Run artifact checks (kernel version + config + source package), ingest Microsoft VEX/CSAF outputs as they are published, and open a support attestation request with Microsoft for any Microsoft product you operate where you need a definitive answer.
- If you operate a mixed Linux fleet:
- Map all kernel artifacts to upstream commit ranges and the list of fixes supplied in the Linux kernel CVE announcement. Use that mapping to automatically tag hosts as vulnerable/unknown/fixed.
- Apply network segmentation and exposure-limiting compensations where immediate patching is not possible.
- For security vendors and SOC teams:
- Ingest Microsoft’s CSAF/VEX feeds and map vendor attestations to deployed artifacts.
- Treat vendor attestations as a high‑fidelity signal where present; where absent, escalate to artifact inspection.
- If you need help verifying specific Microsoft artifacts:
- Collect the kernel image/package and run the “how to verify” checks above, or request Microsoft’s VEX/CSAF attestation for the specific SKU. Microsoft has committed to updating CVE entries if it finds additional products that ship the vulnerable component; request an update if you believe your artifact should be assessed.
Conclusion
Microsoft’s MSRC attestation that “Azure Linux includes this open‑source library and is therefore potentially affected” is an important, authoritative statement for customers who run Azure Linux images. It is not — and was never intended to be — a universal exclusionary statement that no other Microsoft product could include the vulnerable Linux kernel code. Because kernel components like drivers/net/gtp.c are upstream and may appear in multiple kernel builds and product artifacts, defenders must verify other Microsoft artifacts explicitly (via VEX/CSAF attestation, SBOMs, or direct artifact inspection) rather than infer safety from the absence of a product name in a single attestation. Microsoft has begun publishing VEX/CSAF attestations (October 2025) and has committed to update CVEs if further product impacts are identified; until that inventory coverage is complete, artifact-level verification and prompt patching remain the reliable path to risk reduction.Source: MSRC Security Update Guide - Microsoft Security Response Center