Microsoft’s brief advisory — that “Azure Linux includes this open‑source library and is therefore potentially affected” — is accurate as a product‑level attestation, but it is not a technical guarantee that no other Microsoft product can include the same vulnerable upstream component.
Background / Overview
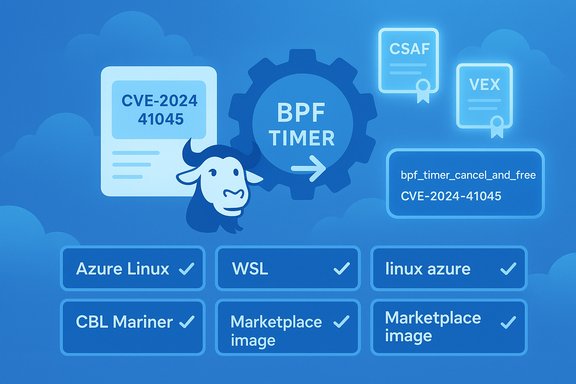
The vulnerability tracked as CVE‑2024‑41045 is a Linux‑kernel BPF subsystem fix described upstream as “bpf: Defer work in bpf_timer_cancel_and_free.” The patch changes the way the kernel cancels and frees BPF timers: rather than attempting synchronous cancellation in contexts that can deadlock or produce use‑after‑free (UAF) races, the code defers cancellation/free work onto a global workqueue and adjusts lifecycle handling to avoid races between timer callbacks and canceller code paths. The public vulnerability records describe this as a correctness/availability bug in the kernel’s BPF timer teardown path, with potential crash, deadlock, or UAF outcomes when certain concurrent sequences occur. Several independent vulnerability trackers and major distributions have cataloged the issue, released advisories or fixed kernel updates, and classified its practical impact as medium in typical deployments. Distributors such as Ubuntu, Debian, Red Hat and Amazon Linux maintain advisory entries showing the CVE details and mapping it into their package streams. The independent records agree on the root cause (concurrent timer callbacks / cancellation races in the BPF timer code) and on the upstream remediation approach (defer cancel/free work to avoid deadlock and UAF windows).What Microsoft actually said — parsing the MSRC language
Microsoft’s CVE update guide for this issue contains a concise operational statement: Azure Linux includes this open‑source library and is therefore potentially affected. The MSRC entry also notes Microsoft’s commitment to publish machine‑readable CSAF/VEX attestations for product inventories and to update CVE/VEX records if additional Microsoft products are found to ship the same component. That two‑part wording is important: it is (a) an attestation of what Microsoft has already validated for the named product family (Azure Linux) and (b) a procedural promise to extend the attestation set if further inventories reveal additional impacted products.Put plainly: Microsoft is telling customers that it has checked the Azure Linux images and found the upstream kernel code in question, so Azure Linux is confirmed in‑scope for the CVE. At the same time, Microsoft is not asserting that every other Microsoft product has been checked and found clean; instead the company will update the product mapping if further internal artifacts are discovered to include the vulnerable code. That phased, product‑scoped attestation model is deliberate and useful — but the practical takeaway for operators is not to assume that silence on other products equals safety.
Short answer to the user’s question
- No — Azure Linux is not necessarily the only Microsoft product that could include the vulnerable BPF timer code.
- Yes — Azure Linux is the only Microsoft product Microsoft has publicly attested to include the implicated open‑source component at the time the MSRC entry was published.
Why the distinction matters (technical and operational context)
Large vendors ship many different artifacts and images. Whether a given upstream source file or kernel subsystem appears in a product depends on build provenance and configuration, including:- Kernel version and patch level (different kernel trees include or omit commits).
- Kernel configuration (CONFIG_* flags) — features can be built‑in, modular, or absent.
- Packaging and build pipelines — Microsoft’s various Linux artifacts (Azure VM images, linux‑azure kernels used for certain VM SKUs, the WSL2 kernel, CBL‑Mariner derived artifacts, and Marketplace images) are produced by distinct pipelines and may differ in which kernel subsystems are enabled.
- Statically linked binaries and embedded artifacts — Go‑built or statically‑linked userland programs can embed vulnerable library code even if a system package is updated, so an image could carry risk from baked‑in binaries.
- Marketplace / partner images — third‑party images hosted in Azure Marketplace may ship different kernel builds than Microsoft’s official Azure Linux images.
Cross‑checks and verification (what independent sources show)
To avoid vendor‑only dependence and to validate the technical facts:- The NVD entry for CVE‑2024‑41045 documents the upstream description and the remediation approach; NVD’s text matches the kernel maintainers’ intent to defer cancel/free work to avoid deadlocks and UAFs.
- Distribution advisories (Ubuntu, Debian, Red Hat and Amazon Linux trackers) list the issue, map the CVE into their kernel package timelines, and reference fixed package versions or backport efforts. These independent trackers confirm the bug’s root cause and the presence of fixes in vendor kernels.
Technical implications of CVE‑2024‑41045
- Affected subsystem: BPF timer cancellation and free path inside the kernel’s BPF subsystem.
- Root cause: Race / deadlock / UAF potential when two timer callbacks can attempt to cancel each other or when freeing map elements containing timers interacts badly with hrtimer cancel semantics.
- Practical impact: kernel crashes, deadlocks, or use‑after‑free outcomes that cause instability or denial‑of‑service of the host or guest. The attack vector is local (an attacker or untrusted process able to load or manipulate BPF maps and timers); this is not a simple remote, unauthenticated worm‑style vulnerability.
Practical verification: how to check whether a Microsoft artifact you run is affected
Artifact‑level verification is the only reliable method. The following steps and commands help determine if a given image or kernel contains the vulnerable code or the fix.- Verify the kernel version and vendor package:
- uname -a
- cat /proc/version
- dpkg -l linux-image-* (Debian/Ubuntu)
- rpm -q kernel (RHEL/CentOS/Amazon Linux)
Use the distribution advisories to map kernel package versions to the fixed commits. Distributor trackers (Ubuntu, Debian, Red Hat) list fixed package versions for affected releases.
- Check for backported fixes in package changelogs:
- apt changelog linux-image-$(uname -r) (or check /usr/share/doc/*/changelog.Debian.gz)
- rpm -q --changelog kernel | less
Backport notes often mention specific commit hashes or CVE identifiers.
- Inspect kernel configuration and module list (to determine whether relevant BPF and timer code is present):
- zgrep CONFIG_BPF /proc/config.gz (if /proc/config.gz exists)
- grep -i bpf /boot/config-$(uname -r)
- lsmod | grep bpf
Presence of BPF support and the specific timers module options indicates potential exposure.
- For WSL2:
- WSL uses a Microsoft‑built kernel binary. Check the shipped kernel version: wsl --status or check the published WSL kernel repo and deployed kernel binary used by your Windows host. If the kernel version in use predates the fix, WSL instances could be affected. Microsoft publishes WSL kernel builds and configuration publicly; those artifacts must be inspected or cross‑checked against Microsoft’s VEX outputs.
- For Azure Marketplace or partner images:
- Treat each Marketplace image as a separate artifact. Boot a test instance, run uname -r and the package checks above, and consult the publisher’s advisory or changelog.
- If the image is third‑party, request the SBOM or ask the publisher for a VEX/CSAF attestation.
- Inspect container images and statically linked binaries:
- For images that may contain baked‑in Go or static binaries that use BPF, extract layers and inspect binaries (strings, ldd, file) to identify embedded runtimes or code patterns that interact with BPF timers.
Recommended mitigation and remediation steps
- For Azure Linux (attested by Microsoft): apply the vendor-provided kernel updates and reboot as instructed. Microsoft’s attestation means Azure Linux images are confirmed carriers and should be prioritized.
- For other Microsoft artifacts you operate (WSL kernels, linux‑azure kernels in VM SKUs, CBL‑Mariner images, Marketplace images, and custom Microsoft images):
- Inventory all artifacts.
- Perform the verification checks above.
- If an artifact is found to be affected, schedule patching/rebuild and reboot.
- If you cannot patch immediately, apply compensating controls (see below).
- Compensating and risk‑reduction controls until patching is possible:
- Restrict who can load, update, or use BPF in production hosts (limit CAP_SYS_ADMIN or privileges that allow loading BPF programs).
- Disable unprivileged BPF where feasible: set kernel.unprivileged_bpf_disabled (or equivalent distribution/configuration knob) to prevent unprivileged BPF use.
- Harden container runtime policies: avoid mounting admin interfaces or exposing /dev/* devices to untrusted containers; use seccomp, AppArmor or SELinux to deny BPF program loading.
- Monitor dmesg and kernel logs for OOPS traces, WATCHDOG/lockup signs or bpf-related errors indicating attempts to exercise the buggy code path.
- Isolate hosts running untrusted workloads or third‑party images until they are validated and updated.
- Automate ingestion of CSAF/VEX artifacts: configure your vulnerability automation to consume Microsoft’s CSAF/VEX outputs and map them to your asset inventory. Microsoft has said it began publishing machine‑readable attestations (CSAF/VEX) and will expand coverage beyond Azure Linux over time; automating VEX ingestion allows you to detect when Microsoft updates the product mapping.
Risks, strengths and the broader transparency context
Strengths of Microsoft’s approach- Machine‑readable attestations (CSAF/VEX) are powerful: when a vendor provides precise product‑level mappings, automation can deterministically triage and prioritize patching for the named artifacts.
- Microsoft’s public commitment to expand attestations and update CVE entries if more products are identified reduces ambiguity over time and gives customers an authoritative source for Azure Linux immediately.
- A phased VEX rollout means short‑term coverage gaps: until Microsoft completes inventory for all product families, absence of a VEX entry for a product is not proof that product is free of the vulnerable component.
- Large vendors and cloud platforms ship many separately built artifacts and third‑party Marketplace images; those create a long tail that can be overlooked if one assumes that a single attestation covers everything.
- Some vulnerabilities, especially in kernel subsystems, may be present in vendor backports or in third‑party kernels even if the mainline kernel in one product is patched — artifact inspection is necessary.
- Human operational processes often lag behind patch publication. Even when attestations and fixes are available, the practical risk is driven by how quickly organizations can identify affected artifacts and deploy fixes.
Concrete operational checklist (actionable)
- Prioritize Azure Linux images in your estate:
- Confirm which VMs use Azure Linux images and apply the Microsoft‑supplied kernel updates immediately. Reboot where required.
- Inventory other Microsoft kernel artifacts:
- WSL installations: check kernel version used by WSL and compare to vendor fix.
- Marketplace images: boot test instances and inspect kernels.
- CBL‑Mariner and linux‑azure derived artifacts: inspect package versions and changelogs.
- Automate cross‑checks:
- Ingest vendor VEX/CSAF outputs into your vulnerability management pipeline.
- Map VEX product entries to your asset inventory and generate remediation tickets.
- Harden BPF usage and limit privileges:
- Restrict unprivileged BPF and limit program loading permissions until artifacts are patched.
- Apply container runtime policies to prevent privileged hosts from being abused.
- Monitor and validate:
- Watch kernel logs for OOPS or bpf-related errors.
- After patching, validate by reproducing relevant BPF tests if you maintain a test harness; observe that previously seen OOPS/crash signatures are absent.
- Track Microsoft VEX/CSAF updates:
- Microsoft has committed to expanding attestations and will update CVE entries when additional products are identified; ensure your automation subscribes to these feeds.
Final assessment and conclusion
Microsoft’s public statement — that Azure Linux includes the open‑source library and is therefore potentially affected — is both accurate and operationally useful: it gives Azure Linux customers an authoritative, machine‑readable signal to act on now.However, that statement is intentionally scoped to the product family Microsoft has inventory‑checked. It is not a technical guarantee that other Microsoft products (WSL kernels, linux‑azure kernel builds used by some VM SKUs, CBL‑Mariner artifacts, Microsoft‑published Marketplace images, or third‑party images hosted in Azure) cannot include the same upstream BPF timer code. Any Microsoft artifact that ships a kernel built from an upstream tree containing the affected commits — and that compiles in the relevant BPF/timer code — could be impacted until it is validated or patched. Artifact‑level verification (kernel version, kernel config, change‑log mapping, or an authoritative VEX/CSAF attestation) is the only reliable way to confirm exposure for any non‑attested Microsoft product. Operationally: treat Microsoft’s attestation as a high‑fidelity “yes” for Azure Linux and patch those images immediately. At the same time, inventory and validate every Microsoft artifact you run; do not assume safety from the absence of a published attestation. Use SBOM/VEX automation where possible, harden BPF usage, and apply compensating controls if immediate patching is not feasible. The combination of vendor attestations, independent tracker cross‑checks and per‑artifact verification gives the defensible, auditable path to remediation in mixed enterprise and cloud estates.
Source: MSRC Security Update Guide - Microsoft Security Response Center