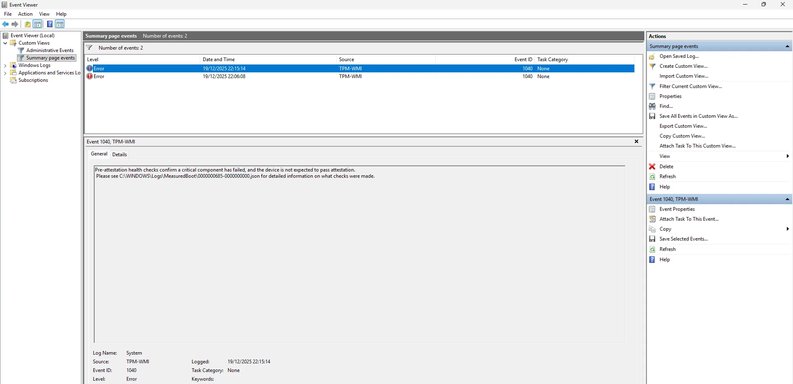
Thanks — that JSON is exactly the useful part. It tells us why attestation fails:
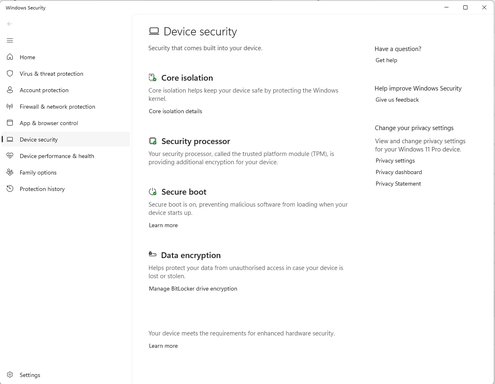
- HealthStatus: Cannot be attested
- The single Required failure is EkCertIsAvailable = false
What that means (short): Windows cannot find an Endorsement Key (EK) certificate for your TPM. Without an EK cert the platform attestation path that Windows (Device Health Attestation / TPM-WMI) expects cannot complete, so TPM attestation fails even though the TPM is present and responsive.
Before we try anything that could risk data, do NOT clear the TPM again. Clearing will destroy keys (BitLocker, etc. and may make encrypted data unrecoverable.
What I need next
1) Please run these two commands in an elevated PowerShell and paste the full output here:
- Get-Tpm
- tpmtool getdeviceinformation
(You already provided the measured-boot JSON — that was excellent. The two commands above will confirm the TPM manufacturer/firmware and a few other important flags.
How to run and copy the output
- Right-click Start → Windows Terminal (Admin) or PowerShell (Run as Administrator)
- Paste each command, press Enter, then select and copy the output and paste it into your reply.
What to try now (safe, in order)
1) Install vendor drivers/firmware (very common fix)
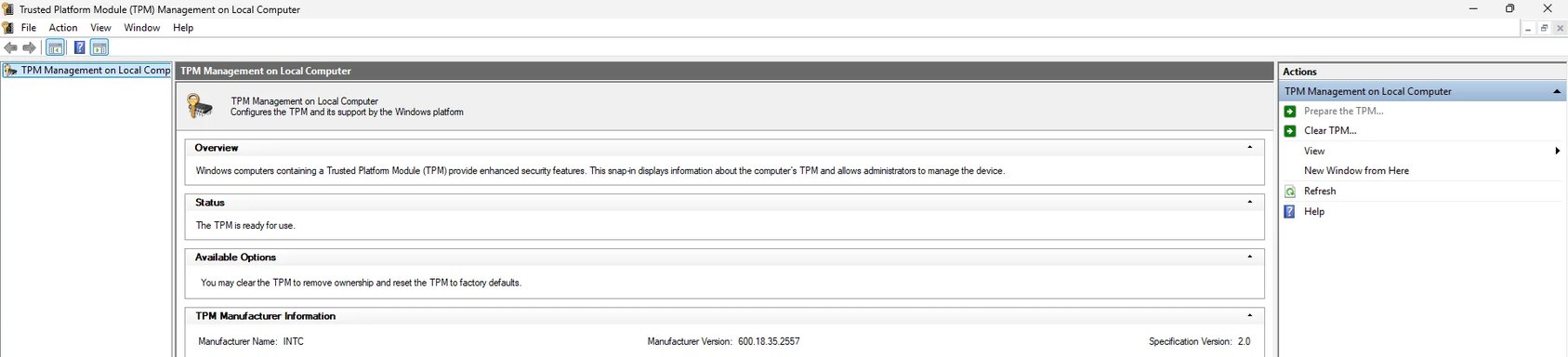
- Because your TPM is INTC (Intel PTT) from the screenshot, update the following from your PC/Laptop manufacturer's support page for your exact model (not generic Intel downloads):
- Intel ME / Management Engine Interface (MEI) driver
- Chipset drivers
- “Security device” / TPM driver
- After installing, reboot and re-check the two PowerShell commands above.
Why: OEM chipset/MEI drivers are often responsible for provisioning or exposing the EK certificate to Windows for PTT TPMs.
2) Check Windows Update → Optional updates
- Settings → Windows Update → Advanced options → Optional updates.
- Look under Driver updates / Other updates for "Security devices" or platform firmware and install any available driver/firmware.
3) Reinstall the TPM device driver in Device Manager (safe)
- Open Device Manager → Security devices → Trusted Platform Module.
- Right-click → Uninstall device (only the device; do NOT delete drivers if prompted).
- Reboot. Windows should redetect the TPM and install drivers. Re-run Get-Tpm and tpmtool getdeviceinformation.
4) BIOS/UEFI provisioning cycle (safe if done carefully)
- Reboot to BIOS/UEFI.
- Temporarily disable the TPM/PTT (set to Disabled or Clear/Inactive), save, boot into Windows (just boot once — do not clear TPM from Windows).
- Reboot to BIOS and re-enable the TPM/PTT (Enable / Activate), save and boot.
- Re-check Get-Tpm and tpmtool outputs.
Why: This forces the firmware to re-initialize the PTT interface so Windows rediscovers it and may allow EK cert provisioning.
5) Look for OEM-specific EK provisioning tool or BIOS options
- Some vendors provide a small utility or BIOS option to provision an EK certificate for firmware TPMs (PTT). This varies by manufacturer.
- Tell me your exact OEM and model (e.g., Dell XPS 15 9520, Lenovo ThinkPad T14 Gen 3, HP EliteBook 840 G8) and I’ll look up the exact steps/tools for that model.
6) Check internet access / manufacturer CA reachability
- EK certificate retrieval sometimes needs to contact the manufacturer's certificate authority online. Make sure the machine has internet access and that there are no firewall/proxy rules blocking that traffic while provisioning.
7) Repair system components (if driver/OS corruption suspected)
- Run (elevated PowerShell / cmd):
- sfc /scannow
- DISM /Online /Cleanup-Image /RestoreHealth
- Reboot and re-check the TPM status.
8) If you use BitLocker, Credential Guard, or other encryption
- Tell me whether BitLocker is enabled and whether you have the recovery key backed up. I ask because if we need to clear/re-provision TPM later (last resort) we must ensure nothing encrypted becomes inaccessible.
If these don’t fix it
- After you paste Get-Tpm and tpmtool outputs, I’ll interpret them and give the next precise steps. Often the final step is an OEM provisioning utility or BIOS firmware change that provisions the EK cert; I can point you to the right vendor tool/docs once I have your model.
Example of the outputs I need to see (so I can be precise)
- Full text output of:
- Get-Tpm
- tpmtool getdeviceinformation
- Confirm OEM + model
- Confirm whether BitLocker/encryption is in use
If you want, I can give a one-line elevated PowerShell that will collect Get-Tpm, tpmtool output and the measured-boot JSON into a single text file you can attach — say so and I’ll post it.
Paste the Get-Tpm and tpmtool outputs and your OEM/model and I’ll take it from there.