ConnectSecure’s latest update adds unified, cross‑distribution Linux patching and a built‑in local patch repository to its MSP‑focused ConnectSecure platform, promising to let managed service providers patch Red Hat, Ubuntu, Debian and CentOS from a single console while cutting the manual work traditionally associated with heterogeneous Linux fleets.
For MSPs, patch management has long been the simplest‑sounding problem with the nastiest operational edge cases. Many service desks run multi‑tenant Windows, macOS, and Linux estates that span different distributions, package managers, life‑cycle policies and reboot behaviors. That fragmentation inflates labor costs, complicates reporting, and creates blind spots that show up as compliance gaps or exploitable vulnerabilities in customer environments.
ConnectSecure—positioning itself as a vulnerability and compliance management platform tailored to MSPs—has announced a cross‑platform Linux patching capability that aims to collapse that fragmentation into a single workflow. In the same release the company also introduced a local, centralized patch repository that uses an on‑site probe agent to download updates once and distribute them internally. ConnectSecure calls out potential manual‑effort savings “up to 80%,” frames the change as removing the “Linux tax” for channel partners, and says the update helps MSPs bid confidently on larger, Linux‑heavy deals in sectors such as healthcare and FinTech.
This is a practical, commercially sensible move for a vendor chasing MSP budgets: Linux dominates cloud and server workloads, and MSPs that lack efficient Linux tooling risk losing customer opportunities or eating hours of low‑margin remediation work.
However, enterprise tools like SUSE Multi‑Linux Manager or Red Hat Satellite are more feature‑rich for full infrastructure lifecycle needs and larger, on‑prem estates; Canonical provides native livepatch and image management for Ubuntu; Automox and Action1 are mature SaaS patching alternatives with strong multi‑tenant, cross‑platform support. The right choice depends on an MSP’s customer base, target verticals, and architectural preferences.
That said, claims like “up to 80% reduction in manual patching” should be treated as vendor guidance until MSPs validate them in their own environments. Important capabilities—especially live kernel patching, container/image lifecycle management, rollback automation and a detailed supported distribution matrix—are not clearly detailed in the initial messaging and are critical to whether the feature shifts from a procedural helper to a strategic platform capability.
For many MSPs, the right next step is a targeted PoC: run ConnectSecure’s Linux patching on a representative set of customer systems (branch offices, cloud VMs, one Kubernetes node pool) and measure the operational delta against your current workflow. If the PoC confirms time savings, lower failure rates, and trustworthy reporting, integrating a multi‑tenant Linux patch capability into your service catalog can unlock higher‑value infrastructure offers and reduce audit‑related risk.
The competitive landscape is crowded and capable—enterprise offerings (SUSE Multi‑Linux Manager, Red Hat Satellite), cloud‑native competitors (Automox, Action1) and distribution vendor tooling (Canonical Landscape + Livepatch) all address overlapping needs. ConnectSecure’s differentiator is the integrated vulnerability → patching loop in a platform aimed specifically at MSP business models. That’s appealing, but the real test will be in operational resilience, trusted package handling, and how well the tool integrates into the MSP’s existing automation, ticketing, and billing ecosystems.
Source: ChannelE2E ConnectSecure Delivers Unified Linux Patching Capabilities for MSPs to Serve Customers
 Background / Overview
Background / Overview
For MSPs, patch management has long been the simplest‑sounding problem with the nastiest operational edge cases. Many service desks run multi‑tenant Windows, macOS, and Linux estates that span different distributions, package managers, life‑cycle policies and reboot behaviors. That fragmentation inflates labor costs, complicates reporting, and creates blind spots that show up as compliance gaps or exploitable vulnerabilities in customer environments.ConnectSecure—positioning itself as a vulnerability and compliance management platform tailored to MSPs—has announced a cross‑platform Linux patching capability that aims to collapse that fragmentation into a single workflow. In the same release the company also introduced a local, centralized patch repository that uses an on‑site probe agent to download updates once and distribute them internally. ConnectSecure calls out potential manual‑effort savings “up to 80%,” frames the change as removing the “Linux tax” for channel partners, and says the update helps MSPs bid confidently on larger, Linux‑heavy deals in sectors such as healthcare and FinTech.
This is a practical, commercially sensible move for a vendor chasing MSP budgets: Linux dominates cloud and server workloads, and MSPs that lack efficient Linux tooling risk losing customer opportunities or eating hours of low‑margin remediation work.
What ConnectSecure added — feature snapshot
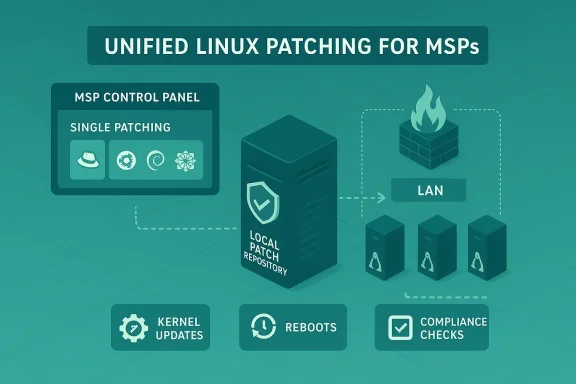
- Unified cross‑distro patching: A single management pane for kernel and OS updates across Red Hat, Ubuntu, Debian and CentOS.
- Centralized, local patch repository: A probe/relay agent downloads scheduled OS updates once and distributes them across the customer LAN, keeping patch traffic inside the firewall and reducing redundant internet downloads.
- MSP‑oriented workflows: Automation, scheduling, and reporting designed to match multi‑tenant service models and help reduce technician time spent on distro‑specific patch chores.
- Reporting and compliance integration: Linux patch status becomes visible inside the same vulnerability / compliance reports MSPs already use for Windows and cloud assets.
Why this matters for MSPs (business case)
- Operational scale and margin pressure
MSPs operate on thin margins. Manual, command‑line driven Linux patching—log into each server, run apt/dnf/zypper, handle dependency conflicts, schedule reboots—does not scale. Automation and centralized orchestration reduce ticket time and let technicians focus on billable engineering or proactive services. - Cloud and server market realities
A majority of public cloud compute is Linux‑based; large cloud providers and infrastructure services are heavily Linux‑oriented. For MSPs that want to serve server‑heavy or cloud‑native customers, practical Linux tooling is table stakes. The new ConnectSecure capability is explicitly billed as enabling MSPs to confidently chase Linux‑centric contracts. - Consolidated reporting and liability reduction
Historically, many MSPs would deliver polished Windows patch reports while their Linux hosts remained a “black box.” Bringing Linux patch status into the same reporting framework reduces audit risk and simplifies conversations with customers about residual risk and remediation responsibility. - Bandwidth and topology optimization
The local patch repository feature addresses real problems for MSPs working with distributed customers or low‑bandwidth sites. A single download and local distribution avoids wasting WAN bandwidth and accelerates large deployments.
Technical deep dive: how a cross‑distro approach has to work
Patching across Linux distributions is not genuinely “one button” unless the platform handles the different underlying mechanics:- Package managers differ: apt (Debian/Ubuntu), dnf/yum (RHEL/CentOS), zypper (SUSE) and their internal semantics (transaction semantics, dependency resolution, package naming) must be abstracted. A successful unified system implements a distribution‑aware engine that translates policies and converts high‑level patch intents into distro‑specific actions.
- Kernel updates and reboots: Kernel updates almost always require reboots unless live kernel patching (kpatch, Canonical Livepatch, KernelCare, Ksplice) is used. For enterprise Linux environments, managing restart windows and coordinating multi‑system reboots is as important as fetching packages. The vendor announcement does not appear to advertise integrated livepatching capabilities, so MSPs should confirm whether ConnectSecure supports livepatch engines or simply automates package distribution and reboot scheduling.
- Repository mirroring vs caching: The “probe agent as centralized patch repository” model mimics patterns MSPs already use (apt‑cacher/ng, yum‑cache, SUSE’s Retail Branch Server). The probe must validate package signatures, keep metadata updated, and securely serve packages over the LAN. This reduces outbound bandwidth but introduces an elevated‑privilege service inside customer networks that must be hardened and monitored.
- Kernel refinements and custom kernels: Some customers run vendor or custom kernels (e.g., appliances, OEM kernels, vendor‑supported RHEL kernels). A unified patch tool must detect these variants and avoid incorrectly applying incompatible kernel packages, or at least flag them for manual review.
- Containers and immutable images: For cloud‑native environments the picture is more complex. Patching a host OS does not update container images. Proper container security requires image scanning, upstream image rebuilds, and orchestration‑level rollout strategies (e.g., redeploy new images to Kubernetes). The ConnectSecure announcement focuses on OS/kernel patching — MSPs should confirm whether the platform integrates image security tooling or whether container image remediation remains a separate activity.
Strengths and practical advantages
- Reduced tool sprawl: Many MSPs currently juggle distro‑specific tooling and manual playbooks. A single, multi‑tenant console that automates common tasks reduces complexity for service desks and lowers training costs.
- Bandwidth‑efficient distribution: The centralized repository/relay model is a mature, well‑proven technique for large or low‑bandwidth sites. It speeds deployments and reduces external traffic—valuable for remote branches or regulated networks.
- MSP‑first product design: The messaging and product packaging prioritize multi‑tenant needs, role separation, and margin‑preserving automation—important for partners that bill by the device or technician hour rather than by project.
- Market timing: As organizations continue migrating server workloads to Linux and containers, MSPs with confident Linux patching capabilities can expand into higher‑margin infrastructure services and compliance work in regulated verticals.
Risks, unknowns and cautionary points
- Vendor claims need verification
ConnectSecure states a potential “up to 80%” reduction in manual patching effort. That sounds plausible as a vendor metric, but it is a marketing claim until validated by real POC results in diverse customer environments. MSPs should insist on a proof‑of‑concept (PoC) that measures actual labor, failure rates, and time‑to‑compliance across their specific distro mixtures. - No advertised live kernel patching
The release does not mention integrated livepatch technologies. For customers where reboots are expensive (high‑availability services, stateful databases), lack of livepatch support limits risk reduction. MSPs should ask whether ConnectSecure integrates with kpatch, Canonical Livepatch, KernelCare or other livepatch providers. - Supply‑chain and repository trust
A central on‑site repository agent becomes a high‑value asset: if compromised, it could distribute malicious packages across the LAN. MSPs must confirm the agent enforces package signature validation, supports reproducible metadata checks, communicates securely back to the control plane, and has strong access controls and monitoring in place. - Handling of EOL and centric distro changes
The Linux distribution ecosystem keeps changing—CentOS moved to CentOS Stream, vendor lifecycles shift, and alternative RHEL rebuilds (Rocky, Alma) gained traction. A vendor tool must be explicit about which distribution versions it supports, how it responds to EOL kernels, and whether it can manage RHEL subscription entitlements or SUSE/Canonical commercial channels. - Containerized and ephemeral workloads
Patching transient cloud workloads and ephemeral containers is a different operational model. ConnectSecure’s focus on OS-level patching is necessary but not sufficient for customers leaning heavily on microservices and immutable infrastructure. MSPs should validate how the platform maps to containers, Kubernetes nodes, and image rebuild workflows. - Integration surface with RMM/PSA and SLAs
Patch orchestration cannot be an island. MSPs will want ConnectSecure to integrate with their RMM, PSA, ticketing, and backup platforms to coordinate maintenance windows, automate rollback on failed patches, and link compliance evidence to billing. Confirm the depth of integrations, multi‑tenant role models, and alerting capabilities.
How ConnectSecure compares with alternatives (operational perspective)
The market already contains several established approaches to Linux fleet management:- SUSE Multi‑Linux Manager / SUSE Manager — enterprise‑grade lifecycle and patch management across many distributions. Designed for large, heterogeneous server estates and full lifecycle operations (image building, provisioning, configuration). SUSE’s product is an infrastructure‑centric, on‑prem or hybrid solution, typically positioned for larger enterprise footprints.
- Red Hat Satellite — focused on Red Hat Enterprise Linux and Red Hat ecosystem customers; strong subscription and entitlement management, provisioning and content views. Best for RHEL‑centric environments.
- Canonical Landscape + Livepatch — Canonical’s managed offering for Ubuntu fleets with integrated live kernel patching and image management. Good fit for Ubuntu‑heavy estates and for MSPs serving cloud workloads built on Ubuntu.
- Automox, Action1 and other cloud‑native patching platforms — cross‑platform SaaS products with multi‑tenant capabilities and strong Linux support. These solutions are built for distributed endpoints and are commonly used by MSPs looking for a cloud‑native operational model.
- ManageEngine / Ivanti / Kaseya / NinjaOne — RMM vendors often include patching modules that cover Linux to varying degrees; these packages are familiar to MSPs but can be inconsistent across distributions.
However, enterprise tools like SUSE Multi‑Linux Manager or Red Hat Satellite are more feature‑rich for full infrastructure lifecycle needs and larger, on‑prem estates; Canonical provides native livepatch and image management for Ubuntu; Automox and Action1 are mature SaaS patching alternatives with strong multi‑tenant, cross‑platform support. The right choice depends on an MSP’s customer base, target verticals, and architectural preferences.
Practical checklist MSPs should use in evaluation and POC
Before replacing current Linux patching workflows, MSPs should validate ConnectSecure against these concrete points:- Supported distributions and versions
- Confirm exact distro/version matrix (e.g., RHEL 7/8/9, Ubuntu 18.04/20.04/22.04/24.04, Debian stable branches, CentOS Stream / Rocky / Alma compatibility).
- Livepatch and reboot handling
- Does the platform integrate with KernelCare, kpatch, Canonical Livepatch or similar?
- How are reboots scheduled and coordinated across clusters? Are pre‑ and post‑checks automated?
- Repository integrity and security
- Does the on‑site probe verify package signatures and metadata?
- What hardening and logging exist for the probe? Can it be placed in an air‑gapped environment?
- Rollback and failure remediation
- If a patch breaks a service, can the system automatically roll back to previous package versions or orchestrate mitigation steps?
- Container and Kubernetes strategy
- How does ConnectSecure treat container hosts vs images? Is there integration for image scanning or CI/CD pipelines?
- Integration and automation
- Confirm connectors for RMM, PSA, backup, SIEM and ticketing tools. Can patch actions create and close tickets automatically?
- Multi‑tenant security model
- Does the console enforce strict role‑based access and tenant separation? Can technicians be scoped to customer‑level views only?
- Reporting and compliance evidence
- Can the platform produce audit‑grade reports for PCI, HIPAA, SOC2, etc., that include Linux patch state?
- Performance and bandwidth behavior
- Test the probe in high‑latency and low‑bandwidth scenarios. Measure local distribution speed and WAN savings.
- Commercial terms and support
- Multi‑tenant pricing, support SLAs, number of endpoints per tenant, and training/partner enablement for technicians.
Operational playbook additions for MSPs adopting a unified Linux patcher
- Standardize discovery: ensure agents and probes discover correct OS families and kernel variants.
- Create staging channels: mirror production channels into a pre‑production pool for critical services.
- Automate pre‑checks: disk space, package locks, dependent service health and backups.
- Schedule maintenance windows and no‑impact windows by tier: database clusters, web tiers, dev/test.
- Coordinate container image rebuilds and orchestration updates where needed.
- Document rollback steps per distro and integrate with runbooks in your PSA.
- Measure and report: patch compliance, mean time to remediate (MTTR), and technician time saved.
Verdict and strategic implications
ConnectSecure’s unified Linux patching and local patch repository are pragmatic additions that align with the needs of MSPs increasingly asked to manage heterogeneous, cloud‑heavy server estates. The product addresses real pain points: tool fragmentation, wasted download bandwidth, and the visibility gap between vulnerability scanning and remediation.That said, claims like “up to 80% reduction in manual patching” should be treated as vendor guidance until MSPs validate them in their own environments. Important capabilities—especially live kernel patching, container/image lifecycle management, rollback automation and a detailed supported distribution matrix—are not clearly detailed in the initial messaging and are critical to whether the feature shifts from a procedural helper to a strategic platform capability.
For many MSPs, the right next step is a targeted PoC: run ConnectSecure’s Linux patching on a representative set of customer systems (branch offices, cloud VMs, one Kubernetes node pool) and measure the operational delta against your current workflow. If the PoC confirms time savings, lower failure rates, and trustworthy reporting, integrating a multi‑tenant Linux patch capability into your service catalog can unlock higher‑value infrastructure offers and reduce audit‑related risk.
The competitive landscape is crowded and capable—enterprise offerings (SUSE Multi‑Linux Manager, Red Hat Satellite), cloud‑native competitors (Automox, Action1) and distribution vendor tooling (Canonical Landscape + Livepatch) all address overlapping needs. ConnectSecure’s differentiator is the integrated vulnerability → patching loop in a platform aimed specifically at MSP business models. That’s appealing, but the real test will be in operational resilience, trusted package handling, and how well the tool integrates into the MSP’s existing automation, ticketing, and billing ecosystems.
Final recommendations for MSP decision makers
- Do a proof‑of‑concept that measures labor hours, patch compliance, and outage incidents before committing.
- Require explicit answers from ConnectSecure on livepatching support, container image remediation, and supported distro/version lists.
- Validate the security posture of any on‑site probe: package signature verification, secure channeling, and audit logging must be non‑negotiable.
- Compare total cost of ownership, not just headline price—include technician time savings, WAN bandwidth delta, and integration development costs.
- Keep an eye on complementary tools: mixing ConnectSecure’s patch orchestration with container image scanning and your RMM’s automation may produce the most complete managed service.
Source: ChannelE2E ConnectSecure Delivers Unified Linux Patching Capabilities for MSPs to Serve Customers