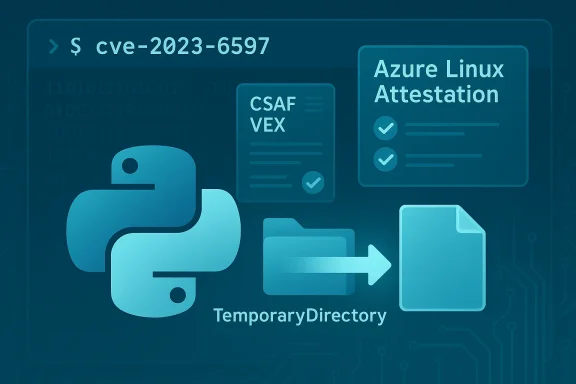
A subtle bug in CPython’s tempfile library—tracked as CVE‑2023‑6597—has raised practical and procedural questions for defenders about scope: Microsoft’s Security Response Center (MSRC) has published a product‑level attestation saying Azure Linux includes the affected open‑source component and is therefore potentially affected. That statement is factual and actionable for Azure Linux users, but it is not a technical guarantee that no other Microsoft product can contain the vulnerable code. In short: Azure Linux is the only Microsoft product the company has publicly attested as including the vulnerable library so far, but absence of an attestation is not the same as proof of absence — every Microsoft artifact should be verified on its own merits.
CVE‑2023‑6597 was assigned to a defect in CPython’s tempfile.TemporaryDirectory cleanup logic: when cleanup encounters permission‑related errors it can dereference symbolic links and operate on the link target rather than the link itself. That behavior can let an actor who can run or influence privileged Python processes cause permission changes on files outside the temporary directory by planting symlinks that point to them. The vulnerability affects multiple Python 3.x releases and was widely published in vendor advisories and distribution security trackers.
This article explains the technical mechanics of the bug, enumerates realistic threat scenarios, details how Microsoft’s product‑level attestation should be interpreted, and gives concrete detection, mitigation and remediation steps for administrators and developers. It also evaluates the strengths and limits of Microsoft’s VEX/CSAF approach to product attestations and explains what defenders should do beyond reading a single vendor advisory.
Microsoft’s Azure Linux attestation is the result of a targeted inventory performed for that product family. It is authoritative for the artifacts examined, but it is not a sweeping technical proof that every Microsoft product has been scanned and found clean. In other words, “attested” = confirmed in scope for that product; “not attested” = not yet confirmed as in or out for other products. This is the same operational model used by other large vendors that are adopting machine‑readable VEX/CSAF attestations.
CVE‑2023‑6597 is a reminder that seemingly small behavior differences in standard libraries (how cleanup handles symlinks) can have outsized security implications when code runs with elevated privileges. Microsoft’s Azure Linux attestation is useful and factual for that product family, but it does not absolve defenders from doing the per‑artifact work needed to confirm whether other Microsoft‑supplied images, binaries, or services also carry the vulnerable CPython implementation. Act promptly on patches, verify artifacts in your environment, and use VEX/CSAF attestations as valuable inputs rather than exhaustive proofs.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE‑2023‑6597 was assigned to a defect in CPython’s tempfile.TemporaryDirectory cleanup logic: when cleanup encounters permission‑related errors it can dereference symbolic links and operate on the link target rather than the link itself. That behavior can let an actor who can run or influence privileged Python processes cause permission changes on files outside the temporary directory by planting symlinks that point to them. The vulnerability affects multiple Python 3.x releases and was widely published in vendor advisories and distribution security trackers.This article explains the technical mechanics of the bug, enumerates realistic threat scenarios, details how Microsoft’s product‑level attestation should be interpreted, and gives concrete detection, mitigation and remediation steps for administrators and developers. It also evaluates the strengths and limits of Microsoft’s VEX/CSAF approach to product attestations and explains what defenders should do beyond reading a single vendor advisory.
What exactly is the bug?
The technical failure mode
At a high level, the bug is about how TemporaryDirectory handles failures while removing files and directories during automatic cleanup:- When TemporaryDirectory removes files it may hit permission‑related errors (for instance, when a file has restrictive mode bits).
- In response, the cleanup code attempted to adjust file permissions so that removal would succeed.
- Critically, that permission fixup code does not always check whether the path is a symbolic link. Instead of operating on the link node itself, it dereferences the link and applies permission changes to the link target.
- If an attacker can create symlinks inside the temp directory that point to sensitive files outside the temp area, cleanup can inadvertently change permissions on those external files.
A succinct exploit scenario
- A privileged Python process (or code executed by an administrator-level task) creates a TemporaryDirectory.
- An untrusted actor who can write into that temporary directory plants a symlink named exploit → /etc/shadow (or another sensitive path).
- Removal of files triggers the cleanup path, which encounters an error and then attempts a chmod/chown on the file path the code sees.
- Because the cleanup code dereferences the symlink, the chmod/chown is applied to /etc/shadow instead of the symlink node, changing permissions on a sensitive file and potentially enabling further local escalation. Multiple distribution advisories reproduce variants of this scenario.
Who and what is affected?
Affected Python versions and the severity
Distribution and vendor advisories list affected CPython releases (examples in upstream and upload advisories vary slightly, but the common set includes Python 3.8, 3.9, 3.10, 3.11 and early 3.12 maintenance releases present at the time of disclosure). The issue was assigned a high CVSS score in several trackers because a local actor can corrupt confidentiality and integrity by enabling unintended permission changes. Refer to vendor advisories and distro security notices for exact patched release numbers for each distribution.Where the problem matters most
- Applications that use TemporaryDirectory in code paths executed by privileged processes (system services, installers, administrative scripts) are high‑risk.
- Multi‑tenant systems (shared build hosts, CI runners, cluster nodes) where an untrusted actor can write into a directory used by a privileged Python process are particularly sensitive.
- Container and VM images that ship a vulnerable CPython binary can expose services that run as root inside the image.
- Services where Python is embedded in a larger product artifact (for example, a packaged management agent) may also be affected if that artifact uses the vulnerable TemporaryDirectory semantics.
Microsoft’s advisory language and how to read it
What Microsoft actually said
Microsoft’s public CVE entries (and the product‑mapping information published under the CSAF/VEX program) include a short, factual statement that Azure Linux includes the open‑source library and is therefore potentially affected. That is an accurate, product‑scoped inventory result: Microsoft has inspected Azure Linux artifacts and found the implicated upstream component. The company also says it will update the CVE/VEX files if it later identifies additional Microsoft products carrying the component.Why that wording does not mean “Azure Linux is the only product that could ever be affected”
Large vendors ship thousands of artifacts across many product families. A single upstream component (a Python standard library module, a Linux kernel driver, an SSL library, etc.) can appear in some artifacts and not others depending on build choices, packaging decisions, kernel config flags, backports and vendor-specific patches.Microsoft’s Azure Linux attestation is the result of a targeted inventory performed for that product family. It is authoritative for the artifacts examined, but it is not a sweeping technical proof that every Microsoft product has been scanned and found clean. In other words, “attested” = confirmed in scope for that product; “not attested” = not yet confirmed as in or out for other products. This is the same operational model used by other large vendors that are adopting machine‑readable VEX/CSAF attestations.
Cross‑checking Microsoft’s claim — practical verification steps
If your estate includes Microsoft images, binaries, or services and you need to know whether they carry the vulnerable Python component, follow these steps:- Inventory the artifacts you run (VM images, container images, marketplace images, WSL kernels, managed agent packages).
- For each artifact, determine whether it includes CPython and the specific tempfile implementation (check binary packages, site‑packages, embedded Python interpreters).
- If you have the artifact locally, use straightforward checks such as:
- Run python -c "import tempfile, inspect; print(inspect.getsource(tempfile.TemporaryDirectory))" to view the implementation (on artifacts that allow running python).
- Inspect package metadata (distribution packages, wheel metadata, pip freeze in virtual environments).
- Where artifact‑level inspection is impractical (closed managed services), rely on vendor attestations and vendor support channels; treat a product attestation as affirmative for included products and treat non‑attested products as unverified until verified by you or the vendor.
Detection and mitigation (practical, prioritized)
Immediate, high‑priority actions
- Patch CPython: Upgrade to the patched Python versions supplied by your OS vendor or upstream Python builds. Distribution advisories list fixed package versions — apply those updates to all systems that install or embed Python. Vendor advisories such as Ubuntu, Amazon Linux and Red Hat provide distro‑specific packages and timelines.
- Avoid running untrusted code in privileged contexts: Where feasible, run Python services under least privilege. If a process must run with elevated privileges, ensure input directories are created and owned by the service and are not writable by untrusted users.
- Change cleanup behavior in high‑risk code paths: If you cannot patch immediately, avoid using TemporaryDirectory in privileged code paths or replace it with a guarded wrapper that:
- Refuses to operate on user‑writable top‑level temp directories, or
- Inspects and refuses to follow symlinks during cleanup (use lstat rather than stat; check os.path.islink before changing mode).
Many vendors and security advisories published example workarounds that check for symlinks before applying chmod/chown.
Medium‑term actions for enterprises
- Scan container/VM images: Rebuild and republish images that contain vulnerable CPython packages. Use an image scanning tool capable of identifying the CPython version and the vulnerable library implementation.
- Harden CI and build agents: Ensure that build artifacts are produced in controlled, non‑shared temp spaces; set restrictive umasks and avoid running build steps as root unless strictly necessary.
- Monitor for accidental permission changes: Alert on unexpected chmod/chown operations to sensitive system paths originating from Python processes; this can catch exploitation attempts or misconfiguration.
Why Microsoft’s VEX/CSAF approach is useful — and where defenders must remain wary
Strengths: transparency and machine‑readable inventory
Microsoft’s decision to publish machine‑readable CSAF/VEX attestations (the VEX pilot started in October 2025) is a material win for defenders. VEX provides deterministic, automatable answers for product‑level impact (for the artifacts the vendor has inventoried), which reduces noisy triage work and accelerates patch prioritization across large estates. The MSRC blog on the rollout explains the benefits and the phased approach Microsoft is using.Limits: phased coverage, per‑artifact differences, and human expectations
- Phased coverage: Microsoft started with Azure Linux. That means the first published attestations cover one product family; other products will be onboarded over time. The initial attestation does not imply systematic scanning of every Microsoft artifact in parallel.
- Per‑artifact variability: Whether a given artifact contains a vulnerable upstream component depends on build choices, packaging and backports. A vulnerability in an upstream project can exist in one Microsoft image and not in another built from a different upstream snapshot or with different compile flags.
- Operational misread: Some readers falsely interpret a single product attestation as an exclusivity guarantee. That interpretation is incorrect and dangerous; it risks leaving other artifacts unverified and unpatched even when they carry the same vulnerable code. Several independent explainers of Microsoft’s VEX pilot emphasize this nuance and recommend per‑artifact verification.
Practical guidance for Microsoft customers (checklist)
- If you run Azure Linux images or services based on Azure Linux: treat the CVE as confirmed in scope and apply available patches immediately. Azure Linux attestation in MSRC/VEX is a definitive signal for that product family.
- If you run other Microsoft images (WSL distributions provided by Microsoft, Marketplace VM images, container base images, packaged agents, desktop products that embed Python):
- Don’t assume “not listed” == “not affected.” Inventory and verify each artifact.
- If you cannot verify locally, open a support ticket with Microsoft and ask for artifact‑level VEX/CSAF attestations or for the company to update the CVE mapping if artifacts are found to contain the component.
- Implement detection: add alerts for unexpected permission changes to system files coming from Python process owners and binary paths.
- Review run‑as‑root policies: eliminate unnecessary privileged execution of Python programs. Use capability reduction, sandboxing and privilege separation wherever possible.
- Automate image rebuilds: integrate CVE detection with your image‑build pipeline so that any image that pulls a vulnerable CPython gets rebuilt and republished with patched packages.
Risk analysis: how bad could things get?
Worst‑case impact and realistic constraints
- If an attacker can reliably make a privileged process load and execute code that writes into its TemporaryDirectory, the bug could be used to change permissions on critical files and escalate further. On systems where Python runs as root or under an admin account, that path is credible and high risk.
- However, exploitation requires a local ability to write into a directory that a privileged process will clean up. The vulnerability is not a remote code execution vector by itself; it is a local privilege escalation / integrity corruption primitive under realistic constraints. Distribution and vendor advisories assign a high severity because of the damage that can follow from successful local exploitation.
Attack surface in Microsoft ecosystems
Several Microsoft‑supplied artifacts could carry the vulnerable library: Azure Marketplace images, container images in Microsoft’s registries, management agents, or WSL components that embed CPython. Whether each artifact is actually affected is a per‑artifact question that depends on whether the particular artifact shipped the affected CPython implementation and whether the vulnerable cleanup path is reachable in the shipped configuration. That is why Microsoft’s product‑level attestation for Azure Linux is useful but not exhaustive: it documents a confirmed carrier, while leaving other artifacts to be verified.How to audit and validate at scale
- Build an automated artifact scanner that:
- Extracts Python binaries/wheels from images.
- Checks Python version and compares the installed tempfile implementation against patched upstream commits.
- For Windows or mixed environments where Python is embedded, create a mapping from product installers to Python runtime components and scan installer payloads before deployment.
- In heavily regulated or high‑risk environments, require vendor VEX/CSAF attestations before accepting third‑party images into your catalog. Microsoft’s VEX program makes this easier for the product families it has onboarded; press vendors for expanded coverage and per‑artifact attestations where needed.
Final assessment: strengths, shortfalls, and recommended posture
Microsoft’s public statement that Azure Linux includes this open‑source library and is therefore potentially affected is an accurate and helpful inventory result. It demonstrates two positive developments: (1) vendors are producing machine‑readable attestations to reduce ambiguity, and (2) Microsoft is starting those attestations with Azure Linux, a product family where immediate customer clarity is valuable. But defenders must not let a product‑scoped attestation lull them into complacency about other artifacts. The underlying technical reality is that the same upstream code can and does appear in many places; until every artifact is verified or attested, each artifact remains a potential risk. Treat the MSRC attestation as authoritative for the artifact named, and as incomplete for the rest of the vendor’s catalog until they publish otherwise.Recommended next steps (summary)
- Apply vendor‑provided Python patches to all systems and images immediately where available.
- Audit your estate for privileged Python processes and remove unnecessary root execution.
- Scan images and artifacts for CPython versions and the tempfile implementation; rebuild affected images.
- Add detection for suspicious permission changes originating from Python runtimes.
- Where Microsoft artifacts are used and you cannot verify them locally, request per‑artifact VEX/CSAF attestations or open a support case; assume “not attested” = “unverified” until proven otherwise.
CVE‑2023‑6597 is a reminder that seemingly small behavior differences in standard libraries (how cleanup handles symlinks) can have outsized security implications when code runs with elevated privileges. Microsoft’s Azure Linux attestation is useful and factual for that product family, but it does not absolve defenders from doing the per‑artifact work needed to confirm whether other Microsoft‑supplied images, binaries, or services also carry the vulnerable CPython implementation. Act promptly on patches, verify artifacts in your environment, and use VEX/CSAF attestations as valuable inputs rather than exhaustive proofs.
Source: MSRC Security Update Guide - Microsoft Security Response Center