CrowdStrike’s latest push into AI security and Microsoft telemetry is less a pair of product updates than a statement of direction. The company is betting that the next major security battleground is no longer just the workstation or the server, but the AI-enabled endpoint, the browser, and the increasingly tangled web of SaaS and cloud services where agents now act on behalf of users. At the same time, CrowdStrike is making a pragmatic move in SIEM: it is opening Falcon Next-Gen SIEM to Microsoft Defender for Endpoint telemetry without forcing customers to deploy a second endpoint sensor. That combination is strategically important because it addresses both the new attack surface created by AI and the old operational burden of moving security data around.
CrowdStrike has spent the last two years turning the Falcon platform into a broader security operating system rather than a single endpoint tool. The company’s roadmap has moved from classic endpoint detection and response toward identity, cloud, data, browser, and now AI workload protection. Its September 2025 move to acquire Pangea was a major signal that it intended to protect the AI lifecycle itself, not merely monitor it from a distance.
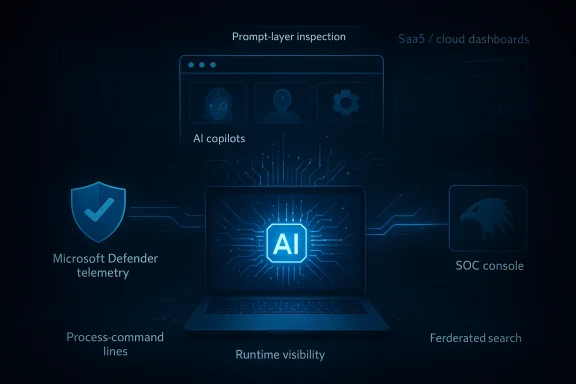
The new AI security features follow that same logic. CrowdStrike is now positioning the endpoint as the place where AI agents often begin their work: running commands, touching files, reaching into data stores, and making network calls that can look legitimate at first glance. That matters because many current security tools still classify behavior using assumptions built for human users and traditional software, not semi-autonomous agents that can act at machine speed. CrowdStrike’s own framing suggests it sees agentic behavior as a category that must be modeled, discovered, and governed directly.
The SIEM update is equally revealing, but for a different reason. CrowdStrike has long tried to break the old tradeoff between endpoint visibility and platform sprawl, and its Next-Gen SIEM product is designed to reduce ingestion overhead, search duplication, and correlation delays. Adding Microsoft Defender for Endpoint telemetry without another sensor is a practical concession to how enterprises actually run their environments, especially those that are standardized on Microsoft for endpoint protection but want a richer SOC layer elsewhere.
What makes this release notable is the blend of defensive necessity and competitive maneuvering. The AI tools help CrowdStrike claim authority in a fast-forming market for AI security, while the SIEM integration strengthens its pitch to customers who do not want platform rip-and-replace projects. In a market where Microsoft, Palo Alto Networks, SentinelOne, and others are all trying to define the security stack around AI, identity, and operational consolidation, CrowdStrike is trying to be the vendor that can meet customers in the middle.
That scale matters because shadow AI is not just a compliance issue. It can become an access-control issue, a data-loss issue, and an identity issue all at once. If an AI app can invoke tools, query enterprise data, or trigger workflows, then it inherits privileges that were originally designed for humans. That is why CrowdStrike’s emphasis on runtime visibility is significant: the company is arguing that the threat is not merely the presence of AI software, but what it does after it starts executing.
The company also says it can identify AI applications, agents, large language model runtimes, MCP servers, and development tools on endpoints, linking them to asset context and privilege exposure. That is important because discovery without context is only half a control. Security teams need to know whether the app is experimental, unmanaged, privileged, or attached to critical data paths. Blind inventory is not enough when the software itself can reason, call tools, and take action.
Key implications include:
The browser is also where managed and unmanaged workflows collide. Employees may use a corporate device during the day, then continue work in personal browser sessions or web apps that security teams do not fully control. If an AI agent is operating in that environment, it can touch data, execute actions, and cross boundaries that were never designed for autonomous behavior. CrowdStrike’s move into browser runtime protection therefore looks less like a side project and more like a necessary layer in an AI-era control stack.
CrowdStrike’s claim that it can extend runtime protection into the browser is therefore strategically aligned with the broader industry shift toward continuous authorization and in-session control. That also fits the company’s January 2026 SGNL acquisition announcement, which explicitly tied identity security to human, non-human, and AI agent identities. In other words, the browser is no longer just where users browse; it is where identities act.
A useful way to read this shift is as follows:
The governance angle matters just as much as detection. Enterprises do not simply want to block all AI; they want to distinguish approved uses from shadow deployments, and they want to identify which systems are allowed to process which classes of data. CrowdStrike’s framing suggests that prompt-layer controls are meant to help organizations enforce policy around data leakage, unauthorized use, and policy violations without forcing them to prohibit AI altogether.
That is why the expansion to include agents, runtimes, and SaaS workflows is so important. If CrowdStrike only watched prompts, it would still miss a large portion of AI-assisted activity. By correlating prompt behavior with endpoint, browser, and cloud telemetry, the company is trying to reduce the blind spots that make AI governance difficult in the first place.
Notable governance themes include:
This is where the enterprise-versus-consumer divide becomes especially relevant. Consumer AI use is mostly a data exposure concern, but enterprise AI use can become an operations concern. Once an agent can act inside a business process, the risks include unauthorized changes, incorrect automation, excessive data access, and policy drift. CrowdStrike’s emphasis on monitoring AI data flows suggests it is trying to prevent AI from becoming an invisible automation layer with no meaningful audit trail.
This is not a trivial architectural shift. If the industry accepts that AI agents are privileged actors, then security controls must follow them through the workflow lifecycle rather than just checking credentials at login. That also changes the compliance picture, because audit teams will want to know who or what acted, what permissions were used, and whether the action was authorized at the time. Static access reviews are going to look increasingly inadequate for this model.
This matters because many security teams are not looking to replace every endpoint tool at once. They want to improve analytics, unify workflows, and reduce operational fragmentation. If Microsoft telemetry can flow into Falcon Next-Gen SIEM while retaining Falcon’s correlation, threat intel, and search capabilities, then CrowdStrike can compete for the SOC layer even in Microsoft-heavy environments. That is a classic land-and-expand move, but with less friction than a full endpoint rip-and-replace.
From a buyer’s perspective, the benefit is straightforward. Organizations can preserve an existing Microsoft deployment while still using CrowdStrike for search, correlation, case management, and threat-hunting. From CrowdStrike’s perspective, the benefit is subtler but more valuable: it gets to sit above competing endpoint ecosystems without forcing customers to choose a single vendor everywhere. That is the kind of pragmatic openness enterprises tend to reward.
The main effects are:
In practice, SIEM migration costs are often driven less by the software license and more by ingestion, storage, and operational retraining. If a platform can stream data more efficiently, search across sources without copying everything into one place, and translate old queries into a new syntax, it lowers the psychological and financial barriers to moving off legacy systems. CrowdStrike is effectively selling not just SIEM performance, but migration relief.
Onum is also strategically interesting because streaming pipelines help move analysis closer to the source. That reduces duplication, can improve responsiveness, and may lower storage costs if customers do not have to centralize every log before analysis. The deeper message is that CrowdStrike wants SIEM to feel less like a giant data lake project and more like a living, real-time workflow layer. That is a compelling pitch for security teams overwhelmed by telemetry volume.
A simple way to view the SIEM stack changes:
At the same time, CrowdStrike is pushing hard on the idea that it can protect AI across the stack—endpoint, browser, SaaS, cloud, identity, and SOC operations. That creates pressure on rivals that may have strong endpoint or SIEM products but weaker stories around AI governance or browser runtime protection. In that sense, CrowdStrike is trying to define the terms of the market before competitors can settle into narrower categories.
For buyers, the competition is healthy, but it can also create confusion. Every vendor now claims to be the right place to secure AI, manage identities, and consolidate the SOC. The practical question is no longer which platform has the best story in isolation; it is which one fits the customer’s actual operating model without triggering a rearchitecture. That is where integrations like Microsoft Defender for Endpoint become especially valuable.
Another key question is whether CrowdStrike can preserve momentum without making Falcon feel like a patchwork of adjacent products. The company is clearly building a wider security architecture, but the more categories it touches, the more it has to explain how each one fits into a single operating model. If it gets that right, the company could become one of the defining vendors of the AI security era; if it gets it wrong, customers may see an ambitious platform with too many moving parts.
Source: SecurityBrief New Zealand https://securitybrief.co.nz/story/crowdstrike-adds-ai-security-tools-microsoft-siem/
 Overview
Overview
CrowdStrike has spent the last two years turning the Falcon platform into a broader security operating system rather than a single endpoint tool. The company’s roadmap has moved from classic endpoint detection and response toward identity, cloud, data, browser, and now AI workload protection. Its September 2025 move to acquire Pangea was a major signal that it intended to protect the AI lifecycle itself, not merely monitor it from a distance.The new AI security features follow that same logic. CrowdStrike is now positioning the endpoint as the place where AI agents often begin their work: running commands, touching files, reaching into data stores, and making network calls that can look legitimate at first glance. That matters because many current security tools still classify behavior using assumptions built for human users and traditional software, not semi-autonomous agents that can act at machine speed. CrowdStrike’s own framing suggests it sees agentic behavior as a category that must be modeled, discovered, and governed directly.
The SIEM update is equally revealing, but for a different reason. CrowdStrike has long tried to break the old tradeoff between endpoint visibility and platform sprawl, and its Next-Gen SIEM product is designed to reduce ingestion overhead, search duplication, and correlation delays. Adding Microsoft Defender for Endpoint telemetry without another sensor is a practical concession to how enterprises actually run their environments, especially those that are standardized on Microsoft for endpoint protection but want a richer SOC layer elsewhere.
What makes this release notable is the blend of defensive necessity and competitive maneuvering. The AI tools help CrowdStrike claim authority in a fast-forming market for AI security, while the SIEM integration strengthens its pitch to customers who do not want platform rip-and-replace projects. In a market where Microsoft, Palo Alto Networks, SentinelOne, and others are all trying to define the security stack around AI, identity, and operational consolidation, CrowdStrike is trying to be the vendor that can meet customers in the middle.
Why AI Security Has Moved to the Endpoint
The endpoint has quietly become the most important place to understand enterprise AI usage. Employees now run consumer chatbots, embedded copilots, local AI runtimes, and developer tools from the same laptops they use to access sensitive documents and internal systems. That creates a problem for security teams because AI software often blends into normal application traffic while still being capable of executing sensitive actions. CrowdStrike says it sees more than 1,800 distinct AI applications and nearly 160 million unique application instances across its customer base, which suggests adoption is already far beyond the narrow set of officially sanctioned tools.That scale matters because shadow AI is not just a compliance issue. It can become an access-control issue, a data-loss issue, and an identity issue all at once. If an AI app can invoke tools, query enterprise data, or trigger workflows, then it inherits privileges that were originally designed for humans. That is why CrowdStrike’s emphasis on runtime visibility is significant: the company is arguing that the threat is not merely the presence of AI software, but what it does after it starts executing.
The new visibility problem
CrowdStrike’s endpoint approach focuses on commands, scripts, file activity, and network connections generated by AI-enabled software. That is a practical choice because these are the artifacts analysts already use to reconstruct malicious behavior, but the presence of AI makes the timeline more complex. A prompt might lead to a shell command, which leads to a file copy, which triggers an API call, and the chain can look routine unless the origin process is traced correctly.The company also says it can identify AI applications, agents, large language model runtimes, MCP servers, and development tools on endpoints, linking them to asset context and privilege exposure. That is important because discovery without context is only half a control. Security teams need to know whether the app is experimental, unmanaged, privileged, or attached to critical data paths. Blind inventory is not enough when the software itself can reason, call tools, and take action.
Key implications include:
- Discovery now has to include AI runtimes, not just standard software inventory.
- Context matters more than labels because sanctioned and unsanctioned AI often look similar.
- Privilege exposure is becoming a first-class part of endpoint risk scoring.
- Runtime telemetry is the difference between noticing an app and understanding its behavior.
Browser Security Becomes AI Security
CrowdStrike’s browser story is increasingly central to its AI strategy. The company’s Seraphic acquisition, announced in January 2026, was explicitly framed as a way to turn any browser into a secure enterprise browser. That makes sense because many AI-assisted workflows now happen in browser tabs, browser extensions, and web-based copilots rather than in standalone applications.The browser is also where managed and unmanaged workflows collide. Employees may use a corporate device during the day, then continue work in personal browser sessions or web apps that security teams do not fully control. If an AI agent is operating in that environment, it can touch data, execute actions, and cross boundaries that were never designed for autonomous behavior. CrowdStrike’s move into browser runtime protection therefore looks less like a side project and more like a necessary layer in an AI-era control stack.
Why the browser is a control plane
The browser has become a kind of universal client for modern work. It is the front end for SaaS, identity providers, cloud consoles, copilots, and internal web tools, which makes it an obvious place for AI agents to live and operate. If a security vendor can observe and enforce policy there, it can catch risky behavior before it fans out into multiple downstream systems.CrowdStrike’s claim that it can extend runtime protection into the browser is therefore strategically aligned with the broader industry shift toward continuous authorization and in-session control. That also fits the company’s January 2026 SGNL acquisition announcement, which explicitly tied identity security to human, non-human, and AI agent identities. In other words, the browser is no longer just where users browse; it is where identities act.
A useful way to read this shift is as follows:
- Endpoints generate the first behavioral signals.
- Browsers carry the interactive workflows.
- SaaS and cloud platforms execute the business logic.
- Identity controls decide whether those actions should continue.
Prompt-Layer Inspection and AI App Governance
One of the more concrete additions in the announcement is prompt-layer inspection for desktop AI applications such as ChatGPT, Gemini, Claude, DeepSeek, Microsoft Copilot, O365 Copilot, GitHub Copilot, and Cursor. That is an important signal because security teams have often been forced to choose between network-level controls that miss semantic context and application-level controls that lack coverage. Prompt inspection tries to bridge that gap by making the human-AI interaction visible as a governance object.The governance angle matters just as much as detection. Enterprises do not simply want to block all AI; they want to distinguish approved uses from shadow deployments, and they want to identify which systems are allowed to process which classes of data. CrowdStrike’s framing suggests that prompt-layer controls are meant to help organizations enforce policy around data leakage, unauthorized use, and policy violations without forcing them to prohibit AI altogether.
What prompt inspection can and cannot do
Prompt inspection is attractive because it can expose risky intent before it becomes a downstream action. If a user or agent tries to paste sensitive data into an external model, or if an application generates a prompt that includes confidential context, that event becomes visible to the security stack. But prompt inspection is not a silver bullet, because a determined actor can shift to local models, indirect tool usage, or alternate interfaces that evade simple pattern matching. Coverage, not certainty, is the realistic goal here.That is why the expansion to include agents, runtimes, and SaaS workflows is so important. If CrowdStrike only watched prompts, it would still miss a large portion of AI-assisted activity. By correlating prompt behavior with endpoint, browser, and cloud telemetry, the company is trying to reduce the blind spots that make AI governance difficult in the first place.
Notable governance themes include:
- Shadow AI discovery across managed endpoints and adjacent environments.
- Prompt-layer policy enforcement for major desktop AI tools.
- Data-flow monitoring to identify leaks or unauthorized sharing.
- Behavior correlation to connect prompts with actual execution.
SaaS and Cloud Extend the AI Attack Surface
CrowdStrike is also extending AI oversight into SaaS and cloud environments, including Microsoft Copilot for Power Platform, Salesforce Agentforce, ChatGPT Enterprise, OpenAI Enterprise GPT, and Nexos.ai. That is a logical progression, because AI agents do not stay on a single device once they start orchestrating business tasks. They reach into ticketing systems, CRM platforms, code repositories, and cloud APIs, often under broad or inherited permissions.This is where the enterprise-versus-consumer divide becomes especially relevant. Consumer AI use is mostly a data exposure concern, but enterprise AI use can become an operations concern. Once an agent can act inside a business process, the risks include unauthorized changes, incorrect automation, excessive data access, and policy drift. CrowdStrike’s emphasis on monitoring AI data flows suggests it is trying to prevent AI from becoming an invisible automation layer with no meaningful audit trail.
The identity problem for non-human actors
A central issue in this market is that AI agents are increasingly behaving like identities, but traditional identity systems were built around people. That means they struggle with ephemeral access, delegated authority, and machine-speed decision-making. CrowdStrike’s January 2026 SGNL acquisition announcement makes clear that it sees continuous dynamic authorization as the answer, with access granted and revoked based on real-time risk rather than standing privileges.This is not a trivial architectural shift. If the industry accepts that AI agents are privileged actors, then security controls must follow them through the workflow lifecycle rather than just checking credentials at login. That also changes the compliance picture, because audit teams will want to know who or what acted, what permissions were used, and whether the action was authorized at the time. Static access reviews are going to look increasingly inadequate for this model.
Why the Microsoft Defender for Endpoint Integration Matters
The SIEM announcement is more practical than flashy, but arguably just as important. Falcon Next-Gen SIEM can now ingest and correlate telemetry from Microsoft Defender for Endpoint without deploying a Falcon endpoint sensor. For customers already committed to Microsoft’s endpoint stack, that removes a major obstacle to trying CrowdStrike’s SIEM and response workflows.This matters because many security teams are not looking to replace every endpoint tool at once. They want to improve analytics, unify workflows, and reduce operational fragmentation. If Microsoft telemetry can flow into Falcon Next-Gen SIEM while retaining Falcon’s correlation, threat intel, and search capabilities, then CrowdStrike can compete for the SOC layer even in Microsoft-heavy environments. That is a classic land-and-expand move, but with less friction than a full endpoint rip-and-replace.
Interoperability over replacement
The integration also speaks to a larger market trend: enterprise buyers increasingly want interoperability, not exclusivity. CrowdStrike’s own public messaging has emphasized open and extensible architecture for years, and its SIEM ecosystem announcements show a long-running effort to support numerous third-party sources. Adding Microsoft Defender telemetry is therefore not a one-off concession; it is consistent with a broader platform strategy.From a buyer’s perspective, the benefit is straightforward. Organizations can preserve an existing Microsoft deployment while still using CrowdStrike for search, correlation, case management, and threat-hunting. From CrowdStrike’s perspective, the benefit is subtler but more valuable: it gets to sit above competing endpoint ecosystems without forcing customers to choose a single vendor everywhere. That is the kind of pragmatic openness enterprises tend to reward.
The main effects are:
- Lower adoption friction for Microsoft-standardized organizations.
- Better SOC consolidation without a duplicate sensor rollout.
- Faster incident response by combining Defender telemetry with Falcon analytics.
- More credible platform positioning in mixed-vendor environments.
SIEM Economics, Data Movement, and Onum
CrowdStrike’s SIEM update also includes native Falcon Onum real-time data pipelines, federated search across third-party stores, integration of external indicators of compromise, and a Query Translation Agent that can convert legacy searches, including Splunk searches, into CrowdStrike Query Language. Taken together, these are aimed at one of the ugliest parts of SIEM modernization: the data plumbing.In practice, SIEM migration costs are often driven less by the software license and more by ingestion, storage, and operational retraining. If a platform can stream data more efficiently, search across sources without copying everything into one place, and translate old queries into a new syntax, it lowers the psychological and financial barriers to moving off legacy systems. CrowdStrike is effectively selling not just SIEM performance, but migration relief.
Why query translation is more than convenience
The Query Translation Agent is a smart move because query syntax is one of the biggest hidden lock-ins in security operations. Teams that have spent years building Splunk searches, dashboards, and detections do not want to rewrite everything manually. Automated translation is not perfect, but even partial conversion can accelerate onboarding and reduce the amount of specialist labor required to evaluate a new platform.Onum is also strategically interesting because streaming pipelines help move analysis closer to the source. That reduces duplication, can improve responsiveness, and may lower storage costs if customers do not have to centralize every log before analysis. The deeper message is that CrowdStrike wants SIEM to feel less like a giant data lake project and more like a living, real-time workflow layer. That is a compelling pitch for security teams overwhelmed by telemetry volume.
A simple way to view the SIEM stack changes:
- Ingest less expensively
- Search where data lives
- Translate legacy workflows
- Correlate across vendors in real time
Competitive Pressure Across the Security Stack
CrowdStrike’s announcement should also be read in the context of intense platform competition. Microsoft is deepening its own AI security and Sentinel strategy, while CrowdStrike is trying to prove that it can coexist with Microsoft where necessary and outflank it where possible. The Defender integration is therefore less a peace treaty than a tactical bridge that allows CrowdStrike to remain relevant in Microsoft-centric accounts.At the same time, CrowdStrike is pushing hard on the idea that it can protect AI across the stack—endpoint, browser, SaaS, cloud, identity, and SOC operations. That creates pressure on rivals that may have strong endpoint or SIEM products but weaker stories around AI governance or browser runtime protection. In that sense, CrowdStrike is trying to define the terms of the market before competitors can settle into narrower categories.
Where rivals may respond
The most likely competitive response is not simply a feature-for-feature clone. Instead, vendors will probably emphasize their own strengths: Microsoft will lean into platform integration and native telemetry, while others will stress lower cost, simpler deployment, or more mature governance controls. CrowdStrike’s challenge is to keep broadening without making Falcon feel too sprawling or too dependent on acquisition-driven integration.For buyers, the competition is healthy, but it can also create confusion. Every vendor now claims to be the right place to secure AI, manage identities, and consolidate the SOC. The practical question is no longer which platform has the best story in isolation; it is which one fits the customer’s actual operating model without triggering a rearchitecture. That is where integrations like Microsoft Defender for Endpoint become especially valuable.
Strengths and Opportunities
CrowdStrike’s strategy has several clear advantages. It is moving early on AI security, it is packaging the story in a way that connects endpoint, browser, SaaS, cloud, identity, and SIEM, and it is offering interoperability rather than demanding a full-stack migration. That combination gives the company multiple ways to win a budget conversation, especially in enterprises that are already worried about shadow AI and SIEM sprawl. The platform story is coherent, which is not something every security vendor can say.- Early positioning in AI detection and response across the AI lifecycle.
- Strong runtime visibility at the endpoint, browser, and SaaS layers.
- Better fit for hybrid environments that already use Microsoft Defender.
- Reduced migration friction through query translation and federated search.
- Improved governance for shadow AI and unauthorized agent behavior.
- A broader identity story that reflects non-human and AI agents.
- A platform narrative that links security operations with AI-era risk.
Risks and Concerns
The challenge for CrowdStrike is execution. The company is stitching together acquisitions, integrations, and new product categories quickly, and customers will judge it on whether those pieces work seamlessly rather than on how ambitious the roadmap looks. There is also a risk that “AI security” becomes too broad a label, causing buyers to struggle with what is genuinely new versus what is rebranded endpoint or SaaS control.- Integration complexity could outpace customer adoption.
- Feature overlap may confuse buyers already using Microsoft or other platforms.
- AI security hype could outstrip practical maturity in some controls.
- Acquisition dependence may slow product coherence if integrations lag.
- Operational overload is possible if SIEM and AI features expand faster than teams can absorb them.
- False positives may rise if prompt and runtime detections are too noisy.
- Privacy and compliance concerns may emerge around prompt-layer inspection and behavioral capture.
What to Watch Next
The next phase of this story will likely be less about the announcement itself and more about customer proof. Enterprises will want to know how the AI controls behave in real workloads, whether Microsoft telemetry integration is truly smooth, and how much value the new SIEM tooling delivers compared with established alternatives. They will also be watching whether CrowdStrike can turn its AI security messaging into measurable outcomes rather than another category slogan. Proof beats positioning in cybersecurity every time.Another key question is whether CrowdStrike can preserve momentum without making Falcon feel like a patchwork of adjacent products. The company is clearly building a wider security architecture, but the more categories it touches, the more it has to explain how each one fits into a single operating model. If it gets that right, the company could become one of the defining vendors of the AI security era; if it gets it wrong, customers may see an ambitious platform with too many moving parts.
- How customers use AI governance in live enterprise deployments.
- Whether Defender telemetry integration reduces SOC friction in practice.
- How rapidly the AI security category becomes a budget line item.
- The pace of browser-security adoption as AI workflows move off the endpoint.
- The impact on SIEM migration decisions, especially for Splunk-heavy shops.
Source: SecurityBrief New Zealand https://securitybrief.co.nz/story/crowdstrike-adds-ai-security-tools-microsoft-siem/
Last edited: