A subtle bug in the Linux kernel’s eBPF fentry attach path — tracked as CVE-2023-53221 — can leave behind allocated BPF trampoline images when an fentry attach fails, producing a persistent memory leak that, if abused at scale, can deny availability to services and systems; this behavior is reproducible, has been cataloged by multiple vendors and vulnerability databases, and should be treated as a local, availability-impacting vulnerability that administrators must remediate promptly.
The extended Berkeley Packet Filter (eBPF) is now a central part of modern Linux observability, security, and networking stacks. It allows user-supplied programs to be verified and JIT-compiled into kernel-executable trampolines that are dynamically linked into kernel execution paths. The kernel’s fentry/fexit hooks provide method-style instrument points that require the kernel and libbpf to create small trampoline images to bridge user-supplied BPF logic into native kernel callers.
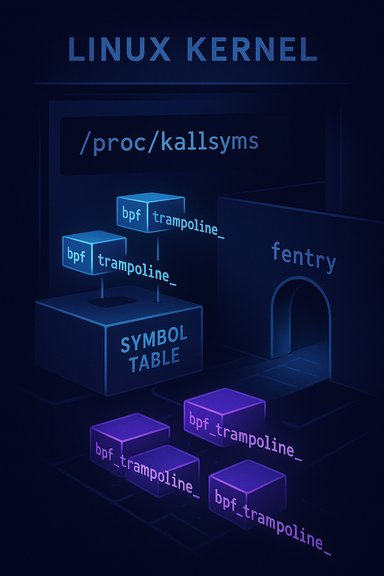
CVE-2023-53221 is a correctness/cleanup bug in that attach path: when an fentry attach attempt fails, the kernel did not always free the allocated trampoline image, leaving it resident and visible under kernel symbol tables (for example, in /proc/kallsyms). Multiple public trackers reproduce the verifier and repro steps and confirm the same root cause and fix approach.
CVE-2023-53221 describes a failure path: if the attach attempt fails (for example because the target kernel symbol was freed after early boot or because the attach target is unavailable), the trampoline allocation was not always freed. The residual trampoline remains registered as a kernel symbol (bpftrampoline<id>) and consumes kernel code memory until the next reboot or until the kernel frees it by a later code-path that is not guaranteed to run.
Short-term mitigations and compensating controls for environments that cannot immediately update:
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
The extended Berkeley Packet Filter (eBPF) is now a central part of modern Linux observability, security, and networking stacks. It allows user-supplied programs to be verified and JIT-compiled into kernel-executable trampolines that are dynamically linked into kernel execution paths. The kernel’s fentry/fexit hooks provide method-style instrument points that require the kernel and libbpf to create small trampoline images to bridge user-supplied BPF logic into native kernel callers.CVE-2023-53221 is a correctness/cleanup bug in that attach path: when an fentry attach attempt fails, the kernel did not always free the allocated trampoline image, leaving it resident and visible under kernel symbol tables (for example, in /proc/kallsyms). Multiple public trackers reproduce the verifier and repro steps and confirm the same root cause and fix approach.
Technical overview — what the bug actually does
The trampoline allocation and the failed attach window
When an fentry program is loaded, the kernel (and libbpf) allocate a small trampoline image — a native-code snippet that calls the loaded BPF program from the kernel function entry. If the attach sequence completes successfully the trampoline is installed, used, and later freed when the program is unloaded.CVE-2023-53221 describes a failure path: if the attach attempt fails (for example because the target kernel symbol was freed after early boot or because the attach target is unavailable), the trampoline allocation was not always freed. The residual trampoline remains registered as a kernel symbol (bpftrampoline<id>) and consumes kernel code memory until the next reboot or until the kernel frees it by a later code-path that is not guaranteed to run.
Reproducer evidence found in trackers
The public reproducer is small and instructive. A minimal eBPF program that declares an fentry section for a function that no longer exists (for example, SEC("fentry/trap_init") int fentry_run { return 0; }) will fail to attach because the function was freed after kernel init. After the failed attach, observers can find one or more bpf_trampoline symbols in /proc/kallsyms and via bpftool, confirming the trampoline image is left behind. Distributors and NVD reproduce this exact sequence in their advisories.Why libbpf may show multiple trampolines
Libbpf may attempt multiple attach strategies — for example, falling back from fentry to raw tracepoint attach. This fallback can produce multiple allocated trampolines where one ends up unused; the net result is memory that is not reclaimed in the failure path, which makes the leak visible and persistent until reboot or until a subsequent cleanup path reclaims it (if any).Scope and affected systems
- Affected component: the kernel’s eBPF fentry attach path and the trampoline allocation lifecycle, across kernels with the vulnerable commit range. This is a kernel-level issue and therefore affects any Linux distribution whose shipped kernel included the problematic code prior to the fix.
- Attack vector: local. An attacker needs the ability to load eBPF programs of the fentry type, or to trigger a load path that exercises the attach failure. Whether that is possible without privileges depends on host policy (for example kernel.unprivileged_bpf_disabled, and capability gating such as CAP_BPF/CAP_SYS_ADMIN). Many hardened environments disallow unprivileged bpf loads and so are less exposed; developer machines, permissive container images, and some CI runners are more exposed.
- Practical consequence: availability impact (denial-of-service or progressive resource exhaustion). A single attach failure leaves a small slab of kernel code resident; repeated or automated exploitation can accumulate trampolines until kernel code memory is exhausted or until observable capacity thresholds are hit, causing service disruption. This makes the vulnerability particularly salient in shared, multi-tenant or long-uptime systems.
Detection and reproduction — how operators can verify exposure
Operators and researchers have a straightforward set of checks to detect presence or exploitation attempts:- Search kernel symbol table for bpf_trampoline entries:
- cat /proc/kallsyms | grep bpf_trampoline
- Use bpftool to inspect BPF program attachments and BTF info:
- bpftool prog show
- bpftool btf dump file /sys/kernel/btf/vmlinux | grep "FUNC 'trap_init'"
- Reproduce in a controlled test by compiling a tiny fentry program that targets a freed or non-existent kernel function (use isolated test host or VM). If the attach fails and trampolines appear in /proc/kallsyms, the behavior matches the published reproducer sequences.
Why this matters: availability, accumulation, and operational impact
A leak of executable kernel memory is not trivial — code pages used by the JIT and trampoline system are a constrained resource. Unbounded or repeated creation of trampolines can lead to:- Increased kernel memory pressure and potential exhaustion of code-size limits;
- Kernel instability as code-generation bookkeeping grows or other subsystems are impacted;
- Persistent degradation in multi-tenant or long-running hosts where reboots are rare;
- A denial-of-service pattern that can be triggered repeatedly by local untrusted users or processes that are permitted to load fentry programs.
Mitigation and remediation guidance
Applying vendor-supplied kernel updates that include the upstream fix is the definitive remediation. The upstream change ensures the trampoline image is freed on attach failure and that the allocation lifecycle is correctly handled across all attach/fallback cases.Short-term mitigations and compensating controls for environments that cannot immediately update:
- Disable unprivileged BPF program loading:
- Set kernel.unprivileged_bpf_disabled = 1 (sysctl or /etc/sysctl.conf) to prevent non-privileged users from using the bpf syscall on hosts where this is appropriate. This reduces the risk that untrusted user processes can trigger repeated attach failures.
- Restrict capabilities:
- Ensure that CAP_BPF and CAP_SYS_ADMIN are granted only to trusted users or service accounts. Audit container and CI runners that might allow escalated access to BPF loading.
- Audit and restrict eBPF tooling:
- Temporarily limit or review deployment of new eBPF-based tooling (XDP, Cilium, Falco, tc filters, or other agents) until hosts are patched. Any service that loads untrusted BPF programs should be considered higher risk.
- Monitor kernel logs:
- Alert on repeated verifier failures, bpf load failures, or unusual kernel symbol table growth. Monitor for bpf_trampoline entries and unexpected kernel memory growth.
Step-by-step remediation and validation playbook
Follow this concise runbook to remediate and validate hosts:- Inventory: Identify hosts that run kernels with eBPF enabled and that allow BPF program loading. Prioritize:
- Multi-tenant hosts and containers,
- Developer-build hosts,
- Hosts running BPF-heavy agents (observability or networking).
- Acquire patches: Use your distribution’s trusted channels (apt, yum, zypper) to obtain kernel packages that list the upstream fix or CVE in their changelogs. Confirm package-level mapping via your distro’s security tracker.
- Test in a pilot: Boot a representative test host into the updated kernel and exercise eBPF workloads to check for regressions.
- Deploy: Stage the rollout (pilot → broader ring → production) and monitor kernel logs and service health during each stage.
- Validate: After patching, verify absence of persistent bpf_trampoline entries and that bpftool shows expected program attachment state. Re-run previously failing reproducer tests in a safe environment to confirm the bouncing trampoline is no longer left behind.
Cross-referencing and verification
To ensure accuracy and support operational decisions, cross-check the following independent sources before acting:- The National Vulnerability Database (NVD) entry for CVE-2023-53221 documents the reproducer and the root-cause description. Use it to confirm the technical reproduction steps.
- Distribution security trackers (Debian, Ubuntu, etc. map fixed package versions and stable-tree backports and are the authoritative source for which packaged kernel versions contain the remediation.
- Community and vendor advisories provide operational playbooks and short-term mitigations (disabling unprivileged BPF, capability gating, monitoring guidance) that are practical to implement while patches are staged.
Operational risk analysis — strengths of the fix and residual risks
Strengths:- The upstream fix is targeted and low-risk: it corrects the allocation/freeing lifecycle in the fentry attach failure path without wholesale redesign of the eBPF attach model. This makes it straightforward to backport into stable kernels and for distributions to package.
- Detection is practical: the kernel symbol table and bpftool provide observable artifacts that operators can use to detect residual artifacts or attempted exploitation.
- Embedded and OEM kernels: vendors that ship custom kernels or slow update cadences often create a long tail where devices may remain exposed for months or years. These systems require extra operational compensations (isolation, capability restriction).
- Accumulation attack model: while a single attach failure leaks only a small amount of kernel memory, repeated automated exploitation can accumulate until availability thresholds are breached. Detection requires vigilant telemetry and alerting focused on kernel-symbol growth and unusual BPF load patterns.
- Unverified exploitation claims: there is no authoritative public evidence at disclosure time of active exploitation of CVE-2023-53221 in the wild; however, absence of public PoC or active exploitation reporting is not proof of safety. Operators should treat that as unverifiable and act based on exposure and operational risk.
For security teams: hunting and telemetry guidance
Prioritize the following telemetry and hunting signals when triaging potential hits:- Kernel logs (dmesg, journalctl -k) containing repeated verifier failures or unusual BPF attach errors.
- Presence of bpf*trampoline** symbols in /proc/kallsyms.
- Sudden growth in kernel code or JIT-related memory consumption on hosts that run long-lived BPF workloads.
- Correlation between process activity that loads BPF programs and any subsequent symbol-table artifacts or kernel OOM/instability events.
Conclusion and recommended priorities
CVE-2023-53221 is a pragmatic, local-attack availability issue: a missing free in the fentry attach failure path leaves BPF trampolines resident in kernel memory. While not a guaranteed remote code execution vector, its consequences are meaningful for systems that allow unprivileged or frequent BPF program loading, and for long-running or multi-tenant hosts where reboots are rare. Administrators should prioritize:- Confirming whether their kernels include the vulnerable code (consult vendor advisories and package changelogs).
- Applying vendor-supplied kernel patches that include the upstream fix as the primary remediation.
- Implementing compensating controls where patching cannot be immediate: disable unprivileged BPF, restrict CAP_BPF/CAP_SYS_ADMIN, and audit eBPF tooling.
- Monitoring for bpf_trampoline artifacts and unusual kernel-symbol growth, and testing patched kernels in a pilot ring before broad rollout.
Source: MSRC Security Update Guide - Microsoft Security Response Center