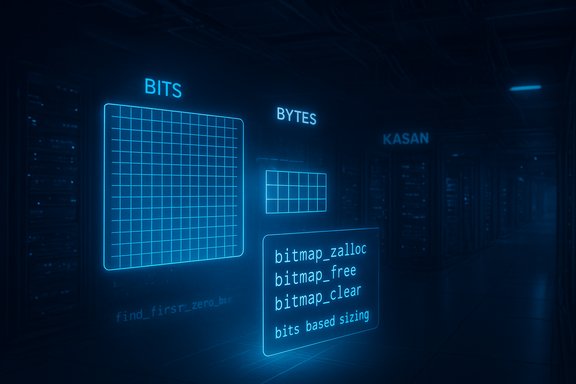
A subtle but dangerous memory-handling bug in the Linux kernel’s mpi3mr SCSI driver — tracked as CVE-2023-53376 — has been fixed upstream after maintainers discovered that the driver was calculating bitmap sizes in bytes while calling bitmap helper functions that expect sizes in bits, allowing out‑of‑bounds memory access that triggers KASAN slab-out-of-bounds errors during certain firmware operations (notably observed during firmware download to eHBA‑9600 devices). The correction replaces ad‑hoc byte arithmetic and kzalloc/krealloc usage with the kernel’s bitmap helpers (bitmap_zalloc, bitmap_free, bitmap_clear) and moves bitmap bookkeeping to use a bits-based field; distributions and vendors have issued patches and kernel updates, and system administrators should prioritize kernel updates or apply mitigations for hosts using the mpi3mr driver.
The mpi3mr driver is the in‑kernel driver that handles MPI3-based Broadcom/LSI storage controllers; it is compiled as the module “mpi3mr” when enabled in kernel config. It supports modern Fusion‑MPT/MPI3 SAS and RAID HW families and is used in servers that rely on Broadcom/LSI HBAs and eHBA devices. The bug at the center of CVE-2023-53376 was discovered when KASAN (Kernel Address Sanitizer) reported slab out‑of‑bounds during firmware download activity on an eHBA‑9600 device, and tracing showed the problem originated in a bitmap operation (find_first_zero_bit) used during event acknowledgment handling. At a technical level, the issue arises from a unit mismatch: the driver allocated and tracked bitmap sizes in bytes, but the kernel bitmap helper functions (which are designed to operate on bit count and internally work with arrays of unsigned long words) were invoked using those byte-based values. That mismatch can leave bitmap buffers smaller than the helper functions expect, causing reads or writes past the end of an allocated slab. The upstream fix standardizes on the kernel bitmap API: store sizes as numbers of bits, allocate with bitmap_zalloc, reallocate with bitmap_resize helpers, clear with bitmap_clear, and free with bitmap_free. The change also removes obsolete byte-size fields from the driver's structures.
Administrators should prioritize vendor kernel updates from their distribution or appliance vendor, validate the running kernel and module status for mpi3mr, and adopt the mitigation path that balances availability against security for their environment. The upstream fix demonstrates good engineering hygiene — rely on well‑tested kernel helpers rather than bespoke allocation math — but the responsibility remains with operators to apply those fixes promptly.
CVE‑2023‑53376 is a concrete example of how a seemingly small unit mismatch (bytes vs bits) in low‑level code can ripple into real system instability and potential security exposure. The path forward is straightforward: identify affected hosts, update kernels or apply temporary mitigations, and verify that the driver no longer emits KASAN errors.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The mpi3mr driver is the in‑kernel driver that handles MPI3-based Broadcom/LSI storage controllers; it is compiled as the module “mpi3mr” when enabled in kernel config. It supports modern Fusion‑MPT/MPI3 SAS and RAID HW families and is used in servers that rely on Broadcom/LSI HBAs and eHBA devices. The bug at the center of CVE-2023-53376 was discovered when KASAN (Kernel Address Sanitizer) reported slab out‑of‑bounds during firmware download activity on an eHBA‑9600 device, and tracing showed the problem originated in a bitmap operation (find_first_zero_bit) used during event acknowledgment handling. At a technical level, the issue arises from a unit mismatch: the driver allocated and tracked bitmap sizes in bytes, but the kernel bitmap helper functions (which are designed to operate on bit count and internally work with arrays of unsigned long words) were invoked using those byte-based values. That mismatch can leave bitmap buffers smaller than the helper functions expect, causing reads or writes past the end of an allocated slab. The upstream fix standardizes on the kernel bitmap API: store sizes as numbers of bits, allocate with bitmap_zalloc, reallocate with bitmap_resize helpers, clear with bitmap_clear, and free with bitmap_free. The change also removes obsolete byte-size fields from the driver's structures. Why this matters: a plain‑English threat model
Memory corruption bugs in kernel drivers are inherently risky because they operate at the highest privilege level. In this case:- The bug causes out‑of‑bounds memory access, detected by KASAN as slab-out-of-bounds. That symptom indicates the kernel can read or write beyond allocated buffers, potentially corrupting kernel memory.
- The observable trigger reported in vendor data was a firmware download to a specific device class (eHBA‑9600). That implies the fault occurs during controller management operations rather than ordinary block I/O — the attack surface is therefore tied to code paths that interact with controller firmware or management utilities.
- Exploitation complexity appears non‑trivial: the vulnerable code is in a hardware‑specific driver path, so an attacker would generally need either access to the host (local) or the ability to induce firmware download operations (which are often administrative). No confirmed public exploit or proof‑of‑concept (PoC) has been found at publication time. Detection signatures were added to some scanners, indicating increased operational interest but not proving active exploitation.
Technical deep dive: what went wrong and how it was fixed
The bitmap ABI mismatch
Linux provides a coherent bitmap API designed to manage bitmaps as a count of bits. The core helpers — find_first_zero_bit, test_and_set_bit, bitmap_zalloc, bitmap_free, bitmap_clear — assume the caller supplies the number of bits (or operates on a memory region sized in unsigned long words). The mpi3mr driver, however, used byte counts to compute allocation sizes and used kzalloc/krealloc to create those areas, then invoked the bitmap helpers with those byte-based values. Because the helpers align and operate in words, this mismatch could allow helpers to index past the allocated buffer when the kernel computes which word and bit to access. The practical consequence observed was KASAN detecting slab-out-of-bounds in find_first_zero_bit during event-ack handling.The actual code and the fix
Upstream patches replace the manual byte-count arithmetic with a bits-based approach. Key changes include:- Replace kzalloc/krealloc on bitmap memory with bitmap_zalloc and appropriate bitmap resizing APIs so allocations and internal bookkeeping follow the bitmap helpers’ expectations.
- Replace explicit memset clearing of bitmap memory with bitmap_clear, ensuring the helper semantics are respected.
- Remove bitmap byte-size fields from the driver’s private structs and replace them with bits-count fields where required (for example, dev_handle_bitmap_bits).
- Change calls that find or set bits (find_first_zero_bit, test_and_set_bit, clear_bit) to use bit counts consistently and to operate on memory allocated by bitmap_zalloc.
Who is affected (systems and distributions)
Affected systems are those with kernels that include the mpi3mr driver exposing the buggy code paths and where the driver is active (either built‑in or loaded as module). That includes many server distributions running kernels in affected ranges and systems that use Broadcom/LSI MPI3 family HBAs (PCI vendor 1000 — Broadcom/LSI). Not all installations of Linux are vulnerable in practice: the bug was observed in a firmware download scenario for the eHBA‑9600 platform. Distribution responses and fixes:- Debian marked the issue and lists the fix as included in a kernel update (fixed in package version corresponding to kernel 6.1.20‑1 for their packaging). Administrators using Debian stable/unstable kernels should check package status and update accordingly.
- Red Hat released advisories and listed the issue in upstream tracking; RHEL kernel package updates (kernel-core) contain the fix in recommended kernel builds (e.g., RHEL9 kernel-core updates referenced in vendor advisories). Security scanners and trackers map the fix to RHSA notices.
- Ubuntu published a CVE entry and assigned a Medium priority; Ubuntu kernels that pick up the mpi3mr patchset will be updated in their normal point releases.
- Multiple vulnerability databases (NVD, OSV, Snyk, CVE aggregators) reflect the upstream commit references and distribution fixes; the kernel commit identifiers referenced in public trackers show the exact commits that implement bit-count based management.
Risk analysis: stability, security and exploitability
- Stability: This bug manifested as KASAN slab-out-of-bounds, which reliably destabilizes a kernel (panic, oops, or unpredictable memory corruption). In production systems with affected HBAs and firmware operations, this can cause crashes and data-plane interruptions; therefore, the operational impact can be high even if exploitation is hard.
- Security: Memory corruption in the kernel is potentially exploitable for privilege escalation or code execution, but exploitation feasibility depends on many factors (address space layout, mitigation mechanisms, whether the vulnerable code path can be driven with attacker-controlled input, and whether it is reachable from unprivileged contexts). The current public data indicates the bug was observed during firmware download code paths — typically privileged operations — which reduces immediate remote exploit risk, but does not remove it. Conservative practitioners should treat kernel memory corruption bugs as high‑risk until proven otherwise.
- Exploitation status: There is no publicly confirmed PoC exploit as of the last reported advisories. Security scanner vendors added detection capabilities, and CVE aggregators flagged the issue, but evidence of active weaponization has not been published in public exploit repositories. That said, presence of detection signatures typically precedes increased scanning and research activity.
Immediate mitigation options (for patching lag or emergency response)
If a kernel update cannot be applied immediately, operators can consider the following mitigations — weigh each option based on availability, planned maintenance windows, and whether the host uses the mpi3mr driver for production I/O:- Update kernels (preferred):
- Check your running kernel version (uname -r) and packaging channels.
- Apply distribution kernel updates from your vendor: apt/aptitude on Debian/Ubuntu, dnf/yum on RHEL/CentOS/Fedora/Oracle, zypper on SUSE, etc.
- Reboot into the updated kernel. This fully applies the upstream kernel fix.
- Blacklist the mpi3mr module (temporary, will disable the HBA and attached storage path):
- Create a file /etc/modprobe.d/blacklist-mpi3mr.conf with:
- echo "blacklist mpi3mr" > /etc/modprobe.d/blacklist-mpi3mr.conf
- Or unload the module immediately: modprobe -r mpi3mr (only if not in use).
- This prevents the driver from loading; it is a blunt instrument and will remove access to devices controlled by the HBA. Use only if you can tolerate loss of attached storage or if that storage is not required for boot. Confirm module name and live usage before blacklisting.
- Restrict management operations:
- Where feasible, avoid performing controller firmware downloads and other out‑of‑band management on hosts until patched. Restrict access to management tools (storcli/sg3_utils) and interfaces that may trigger the vulnerable code path.
- Monitoring and detection:
- Enable KASAN in test environments to reproduce and verify the issue where practical.
- Monitor kernel logs for KASAN slab-out-of-bounds messages and for traces that reference mpi3mr call sites (e.g., find_first_zero_bit in mpi3mr_send_event_ack). Detection rules added to commercial and open scanners may help identify affected hosts.
Practical patching steps by distribution (examples)
Below are practical examples administrators can adapt to their environment. Always validate package names and repository policies for your site.- Debian / Ubuntu (APT-based systems)
- Update package lists and upgrade kernel packages:
- sudo apt update
- sudo apt upgrade --with-new-pkgs
- If your site pins kernels, install the specific kernel package that contains the fix (check distro advisories for the exact package name and version; Debian tracked the fix to kernel 6.1.20-1 in their metadata).
- Reboot into the updated kernel and validate the mpi3mr module is either updated or absent if blacklisted.
- Red Hat / RHEL / CentOS / Oracle Linux (DNF/YUM)
- On RHEL/OEL systems, install vendor kernel updates (e.g., kernel-core) as provided in the security advisory stream. Snyk and vendor trackers mapped the fix to kernel-core updates in RHEL9 series; consult your Red Hat advisory for the exact build. Example commands:
- sudo dnf update kernel-core
- sudo reboot
- Verify the running kernel package has the advisory or changelog entry referencing the mpi3mr bitmap fix.
- SUSE (Zypper) and other vendors
- Use the vendor's update mechanisms and consult vendor advisories for patched kernel versions. For all distributions: after update and reboot, verify the kernel version and module status (uname -a; lsmod | grep mpi3mr).
Verification checklist for operators
- Identify whether the host loads mpi3mr:
- lsmod | grep mpi3mr
- grep -i mpi3mr /lib/modules/$(uname -r)/modules.dep
- Confirm the hardware using lspci (look for Broadcom/LSI Fusion‑MPT/MPI3 device IDs).
- Check kernel package metadata for fixes:
- On Debian/Ubuntu: apt changelog linux-image-$(uname -r) or check security tracker entries.
- On RHEL/CentOS: rpm -q --changelog kernel-core | grep mpi3mr or consult Red Hat advisories linked in vendor portals.
- Inspect dmesg and journalctl for KASAN or mpi3mr-related warnings:
- journalctl -k | grep -E "KASAN|mpi3mr|evtack|find_first_zero_bit"
- Any KASAN slab-out-of-bounds reports referencing mpi3mr indicate you have hit the buggy code path.
- Apply vendor kernel update and reboot (preferred remediation).
Strengths of the upstream fix — why it’s a sound remediation
- The patch uses the kernel’s own bitmap helpers, removing hand‑rolled arithmetic mistakes and aligning allocation semantics with the helper APIs. Using bitmap_zalloc/bitmap_free/bitmap_clear reduces the chance of future ABI mismatches and leverages kernel-maintained behavior for alignment and word-size semantics. That’s both more robust and easier to audit than bespoke kzalloc-based handling.
- The fix is narrowly scoped: it corrects the unit mismatch and reduces the driver’s attack surface by standardizing allocation and clearing operations. Developers also removed obsolete fields, reducing structural code complexity and potential future confusion.
- The upstream patch landed in stable series branches and prompted distribution packaging updates; multiple distros have already integrated the fix into kernel updates, enabling operators to remediate via normal update processes.
Risks and caveats
- The vulnerability is hardware‑specific in its observed manifestation (firmware download to eHBA‑9600), which reduces the universal exploitability surface, but it does not eliminate risk: any driver code that uses the incorrect bitmap bookkeeping could be triggered by privileged or misused management operations.
- Distribution lag: kernel fixes must be backported and packaged by distributors; environments running long‑term kernels, vendor‑custom kernels, or appliances may take longer to receive updates. Administrators of such systems must coordinate with vendors and potentially accept downtime for kernel upgrades.
- Blacklisting mpi3mr is disruptive: removing the driver disables access to attached storage devices controlled by the HBA. For many production systems that is not acceptable, so blacklisting is only an emergency measure.
- Lack of public exploit information should not be interpreted as no risk. Kernel memory corruption is a desirable target for attackers and aggressive exploit development often follows public disclosure of root causes and patch details.
Recommendations and next steps (executive summary)
- Treat CVE‑2023‑53376 as a high‑priority kernel bug for systems that use mpi3mr-controlled HBAs or perform controller firmware operations.
- Apply vendor‑supplied kernel updates as soon as your testing and change windows allow. Use distribution security advisories to identify fixed kernel package versions (Debian listed a fix in 6.1.20‑1; Red Hat and others have mapped fixes into their kernel-core updates).
- If you cannot update immediately, restrict or postpone firmware‑download and management operations to patched systems only, and consider blacklisting the mpi3mr module only if you can accept device removal.
- Monitor kernel logs for KASAN slab-out-of-bounds messages and use detection signatures from your vulnerability scanner to locate at‑risk hosts.
- For teams maintaining kernel builds or custom images, incorporate the upstream commit that moves bitmap management to bit counts and bitmap_zalloc/bitmap_free semantics; audit other driver code for similar byte/bit mismatches.
Final analysis: why this matters to WindowsForum readers
While CVE‑2023‑53376 is a Linux kernel issue, the broader lesson is universal: device drivers are a frequent source of critical vulnerabilities because they interact with hardware, perform complex memory management, and run with kernel privileges. For infrastructure operators and those building mixed OS environments, this vulnerability is a reminder to maintain firmware and driver patch discipline across the entire stack — whether the host OS is Linux, Windows, or hypervisor images that expose HBA passthrough. In mixed environments where Windows servers access shared storage arrays or where Linux is used as storage controllers, ensure both kernel/driver patches and management‑plane operations are coordinated and tested.Administrators should prioritize vendor kernel updates from their distribution or appliance vendor, validate the running kernel and module status for mpi3mr, and adopt the mitigation path that balances availability against security for their environment. The upstream fix demonstrates good engineering hygiene — rely on well‑tested kernel helpers rather than bespoke allocation math — but the responsibility remains with operators to apply those fixes promptly.
CVE‑2023‑53376 is a concrete example of how a seemingly small unit mismatch (bytes vs bits) in low‑level code can ripple into real system instability and potential security exposure. The path forward is straightforward: identify affected hosts, update kernels or apply temporary mitigations, and verify that the driver no longer emits KASAN errors.
Source: MSRC Security Update Guide - Microsoft Security Response Center