A fortify-source warning in the Linux kernel’s RDMA mlx5 code has been closed out as CVE-2024-26907, and while the fix is narrowly targeted at a compile-time/runtime bounds check in a memcpy path, the practical impact on high-performance network stacks — and on the availability of systems that rely on Mellanox/NVIDIA ConnectX adapters — makes this one of the kernel patches that infrastructure teams should treat as operationally important today.
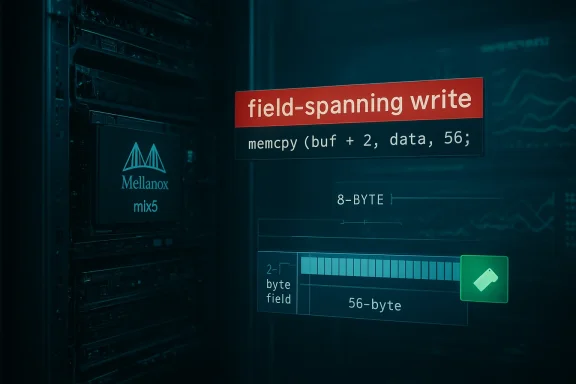
The vulnerability tracked as CVE-2024-26907 stems from a detected field-spanning write in mlx5 driver code when handling the Ethernet (Eth) segment inside a work‑queue entry (WQE). The Fortify/FORTIFY_SOURCE runtime/string-checking instrumentation reported a memcpy that attempted to copy 56 bytes into a two‑byte field (eseg->inline_hdr.start), which triggers a kernel WARNING and can cause instability. NIST’s NVD database records the issue and the diagnostic trace that exposes the offending function: mlx5_ib_post_send.
Distribution and vendor advisories classify this as an important/high fix with a CVSSv3 base score in the high‑severe range (7.8), and multiple mainstream kernels received coordinated patches or backports as part of routine stable kernel releases. Red Hat, Amazon (ALAS), Oracle, AlmaLinux and other vendors have included the change in their kernel errata. These vendor advisories reflect the upstream kernel commits that correct the memcpy/structure layout usage responsible for the Fortify warning.
Practical steps for administrators:
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The vulnerability tracked as CVE-2024-26907 stems from a detected field-spanning write in mlx5 driver code when handling the Ethernet (Eth) segment inside a work‑queue entry (WQE). The Fortify/FORTIFY_SOURCE runtime/string-checking instrumentation reported a memcpy that attempted to copy 56 bytes into a two‑byte field (eseg->inline_hdr.start), which triggers a kernel WARNING and can cause instability. NIST’s NVD database records the issue and the diagnostic trace that exposes the offending function: mlx5_ib_post_send.Distribution and vendor advisories classify this as an important/high fix with a CVSSv3 base score in the high‑severe range (7.8), and multiple mainstream kernels received coordinated patches or backports as part of routine stable kernel releases. Red Hat, Amazon (ALAS), Oracle, AlmaLinux and other vendors have included the change in their kernel errata. These vendor advisories reflect the upstream kernel commits that correct the memcpy/structure layout usage responsible for the Fortify warning.
What exactly happened: the technical root cause
The Fortify/ Gcc “field‑spanning write” check
Modern distributions build kernels with FORTIFY_SOURCE-style protections and compile-time checks that can also emit run-time warnings for suspicious uses of memcpy/memmove when the compiler and libc/runtime can detect a potential out‑of‑bounds or cross‑field write. In this case the check flagged a memcpy that copies more bytes than the size of a single target field, even if the code’s intent is to populate a flexible/inline header region inside a larger structure. The check is useful because it catches accidental, dangerous memory writes; in kernel code it can also reveal places where a structure layout or copy strategy needs to be reworked to be explicit and safe.The mlx5 code path at fault
The offending code appears in drivers/infiniband/hw/mlx5/wr.c around the mlx5_ib_post_send path, when the driver prepares Eth segment inline headers for transmit. The kernel log excerpt captured in several advisories shows the exact runtime trace and the memcpy diagnostic. The practical effect observed by operators is a kernel WARNING (and in some cases oops/crash) when the code path is exercised with particular inline data sizes. The upstream remedy is not a redesign of the hardware stack but a corrective change in how the inline header is populated to avoid a cross-field memcpy that trips Fortify checks.Impact and risk assessment
- Primary impact: Availability. The vendor and kernel descriptions, and the runtime evidence, show this is an availability-first flaw: the observed result is kernel warnings and potential oopses — which lead to service disruption on affected hosts using mlx5 RDMA/InfiniBand adapters. That maps directly to denial‑of‑service conditions for those hosts or services running on them.
- Attack vector and privileges: The CVSS vector assigned by NVD and distribution trackers indicates local attack vector (AV:L), with low attack complexity and low privileges required (PR:L). In plain terms: a local user, process or unprivileged workload that can drive the mlx5 send path (for example, userland RDMA operations) might trigger the condition. This is consistent with a kernel stability/robustness issue rather than a remotely exploitable memory corruption that yields arbitrary code execution.
- Exploitability / confidentiality & integrity: Public advisories and vulnerability databases do not document a reliable path to remote code execution or privilege escalation from this specific memcpy/FORTIFY warning; instead they flag potential kernel memory corruption or undefined behaviour that can be weaponized into repeated availability loss if triggered repeatedly. There is no public proof‑of‑concept demonstrating a remote, unauthenticated exploit chain for arbitrary code execution as of the latest vendor advisories. This absence of PoC should not be read as proof of impossibility — it is an availability‑bias, not an exploitation‑proof.
What vendors and distributions say (affected systems and fixes)
Multiple vendor security trackers include CVE-2024-26907 in their advisories and list the kernel series where the patch was applied. A non‑exhaustive summary of vendor responses:- NVD / common record: NVD documents the diagnostic output and lists the vulnerability with CVSSv3 7.8. This is the canonical CVE record used by many scanners.
- Amazon Linux (ALAS): ALAS lists kernel packages and stable updates where the CVE was fixed across several kernel lines (5.10, 5.15, 5.4) and marks the fix as delivered in their 2024–2025 errata cycle. Administrators using Amazon-provided kernels should treat the ALAS advisories as prescriptive.
- Linux kernel / upstream: The Linux kernel CVE announcements list the individual commits that implement the fix and recommend updating to the latest stable kernel. The public linux‑cve‑announce entry provides commit references for users who need to cherry‑pick fixes for backports. Upstream explicitly warns that cherry‑picking is not recommended except where vendors or distributors backport commits as part of a tested release.
- Vendor backports: RHEL, AlmaLinux, Oracle Linux and other enterprise distributions incorporated the change into kernel errata and provide fixed packages. These patches are commonly included in regular kernel maintenance releases and security errata channels.
Detection: how to know if you’ve been affected
If the mlx5 memcpy condition appears on a host, the most direct signals are kernel logs (dmesg, journalctl) and oops traces. Look for indicators like:- Kernel WARN messages that include the string "memcpy: detected field-spanning write" or the function name mlx5_ib_post_send, and the file/line mentioned in vendor advisories (wr.c). These diagnostic lines are shown in the NVD and distro advisories and are the clearest immediate sign the faulty code path executed.
- Repeated kernel warnings, stack traces, or panics correlated with RDMA or InfiniBand workloads — especially those that perform inline header operations or direct send operations.
- Symptoms at the service level: intermittent network failures, broken RDMA sessions, or unexplained reboots/crashes on systems that host Mellanox/NVIDIA ConnectX adapters.
- Search system logs for the exact diagnostic strings reported in advisories: "memcpy: detected field-spanning write" and "mlx5_ib_post_send". This is a high‑fidelity signal.
- Monitor dmesg and journalctl for recent WARN/oops entries tied to mlx5 modules. Set an alert if these phrases surface.
- If you have a host with Mellanox hardware but the mlx5 driver is modular, check lsmod / modinfo for loaded mlx5 modules and the module version to help map to patched packages.
Mitigation and remediation guidance
The universal, vendor-recommended remedy is to install a kernel that contains the upstream fixes — either through a distribution kernel update or an upstream stable kernel update. The Linux CVE team and distributors consistently recommend updating to the latest stable kernel release for comprehensive safety.Practical steps for administrators:
- Prioritize patching for RDMA hosts. Systems that run RDMA workloads, storage fabrics, or high-performance compute nodes using Mellanox/NVIDIA adapters should be moved to the front of the patch queue.
- Install vendor kernels that include the fix rather than attempting risky single-commit cherry‑picks. Use the vendor-supplied errata or security packages for your distribution (RHEL errata, ALAS advisories, Ubuntu SRU, etc.).
- If patching is temporarily impossible, consider temporary mitigations:
- Unload the mlx5 module on systems where RDMA is not required (this disables RDMA functionality but removes the immediate crash surface). Use modprobe -r mlx5_ib / mlx5_core and observe service impacts before doing so in production.
- Restrict untrusted local users from performing RDMA operations. This can mean limiting access to RDMA device nodes and related user space tools until the kernel is updated.
- In virtualized environments, consider preventing passthrough of the affected adapter to untrusted guests until host kernels are patched.
- Backporting guidance: If you must backport the fix, obtain the exact stable commits referenced by the kernel security announcements and apply them to your vendor kernel tree. Note: upstream guidance discourages unsupported cherry‑picking; do this only with rigorous testing or via vendor-supplied backports.
- Test before rollout: Because kernel updates affect I/O and hardware drivers, stage patches in a test cluster that mirrors production RDMA loads.
Detection controls and hunt/detection rules
Hunting for this issue at scale can be automated by targeting kernel logs and telemetry:- Alert for dmesg or journalctl messages containing:
- "memcpy: detected field-spanning write"
- "mlx5_ib_post_send"
- "wr.c" combined with "mlx5" warnings
- Complement log hunts with hardware inventory feeds: host lists that show Mellanox/NVIDIA ConnectX or mlx5-capable devices should be prioritized.
- Add lightweight eBPF or audit rules to detect invocation of the problematic kernel function (advanced): tracepoints that indicate mlx5_ib_post_send invocation can be monitored for anomalous frequency or arguments that appear in unpatched clusters.
- On systems with centralized logging (SIEM), index the vendor diagnostic phrases and create short‑lived correlation rules mapping RDMA workload spikes with kernel WARN traces.
Operational prioritization: who should care first
- High-performance computing and storage clusters that use RDMA fabrics. Any environment using InfiniBand, RoCE (RDMA over Converged Ethernet), or kernel bypass libraries should treat this as high priority.
- Cloud hosts with direct device attachment or performance-critical networking. Pass‑through of adapters to VMs or container hosts that allow local users to access device nodes.
- Environments with untrusted or multi‑tenant local workloads. Because the attack vector is local, multi‑tenant hosts that permit guest or user workloads to issue RDMA operations present higher risk.
- General-purpose servers that load mlx5 modules but do not use RDMA. These should be scheduled into routine patching, but short‑term mitigations (unloading the driver) are simpler if RDMA is not required.
Strengths of the upstream fix and potential residual risks
- Strengths
- The patch is surgical: upstream commits avoid the problematic cross‑field memcpy and are small, reviewable changes that directly address the Fortify warning and its runtime manifestation.
- Multiple distributors have accepted the fix and shipped it in their kernel errata, reducing the risk that unpatched users will be left without vendor support.
- The diagnostic reporting (Fortify) made a latent code smell visible, enabling a preventative correction rather than large-scale incident remediation.
- Residual risks and caveats
- Local attack vector remains: the vulnerability requires local interaction to trigger, so operator practices that permit untrusted local workloads remain a policy risk.
- Kernel backport complexity: operators who attempt to cherry‑pick individual commits into vendor kernels without full integration testing may introduce regressions. Upstream explicitly warns that single commits should not be transplanted into long-term vendor kernels without care.
- No public PoC ≠ no exploit: while no credible public proof-of-concept demonstrates remote code execution, theoretical memory‑corruption paths can sometimes be chained in ways that are non‑obvious. Treat the absence of public exploitation as a lucky state, not a guarantee.
Recommended action checklist (operational playbook)
- Inventory: Identify all hosts with mlx5 hardware or loaded mlx5 modules.
- Detect: Hunt for kernel log strings (“memcpy: detected field-spanning write”, “mlx5_ib_post_send”) and alert on them.
- Patch: Apply vendor kernel errata that include the CVE‑2024‑26907 fix; prioritize RDMA/InfiniBand hosts.
- Temporary mitigation: If immediate patching isn’t possible, unload the mlx5 modules on non‑RDMA hosts or restrict access to RDMA device nodes.
- Test: Validate patches in a staging environment under representative RDMA loads before wide rollout.
- Monitor: Continue to monitor kernel logs and SR‑IOV/PCI passthrough activity after patching for regressions.
- Document: Record the remediation actions and update incident playbooks to include this class of FORTIFY-source/writable-inline-header issues.
What we could not verify and open questions
- Public evidence of active exploitation in the wild for this specific CVE is not documented in vendor advisories or NVD entries. I could not find any authoritative report of a remote or local exploit chain that results in privilege escalation or code execution stemming directly from this memcpy warning; existing documentation focuses on kernel warnings and availability consequences. This is consistent across NVD, the linux‑cve announcement and vendor errata, and should be considered when assessing threat likelihood.
- The upstream commits referenced by kernel announcements were listed as stable‑tree patches. While the linux‑cve‑announce mail contains commit references suitable for backporting, direct fetching of the git.kernel.org commit pages for some commit IDs may be restricted in certain networks or blocked by automated fetch tooling; use vendor-supplied errata where possible and consult your distro’s kernel maintainers for exact backport guidance.
Conclusion
CVE‑2024‑26907 is a stability‑first vulnerability in the Linux kernel’s RDMA/mlx5 stack that was revealed by Fortify/memcpy run‑time checks. The practical consequence is availability impact — warnings, oopses, and possible DoS on systems that exercise the inline Eth segment path. The fix is available upstream and has been incorporated into vendor kernels; administrators of RDMA‑using infrastructure should prioritize kernel updates, monitor kernel logs for the specific Fortify diagnostic strings, and where necessary apply temporary mitigations such as unloading the mlx5 modules until vendor patches are deployed. Treat the absence of public proofs-of-exploit as not a reason to delay: this is an operational liability for RDMA hosts and should be resolved through the standard patch-and-validate lifecycle documented by your distribution and hardware vendor.Source: MSRC Security Update Guide - Microsoft Security Response Center