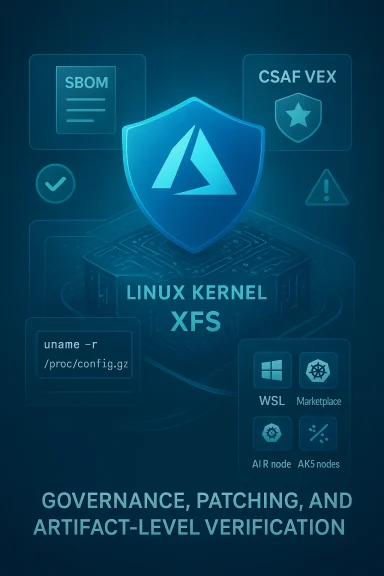
The Linux kernel vulnerability tracked as CVE-2024-39472 — an XFS log recovery buffer allocation bug tied to a legacy h_size fixup — is real, patched upstream, and Microsoft’s public guidance currently names Azure Linux as the Microsoft product they have attested contains the affected open-source component, but that attestation is product-scoped and does not constitute a universal guarantee that no other Microsoft-supplied artifact could include the vulnerable kernel code. Security teams must treat the Microsoft statement as an authoritative signal for Azure Linux images while performing artifact-level verification across other Microsoft‑provided kernels, Marketplace images, WSL kernels, and custom images until broader attestations (CSAF/VEX or SBOMs) confirm otherwise.
CVE-2024-39472 is a medium-severity kernel defect in the XFS filesystem’s log recovery path. The root cause: a series of historical changes intended to handle an incorrect h_size value introduced by older mkfs.xfs tools. A later refactor cleaned up the block-count calculation but inadvertently stopped using the corrected (fixed-up) h_size when sizing the log recovery buffer. If the h_size used at runtime is manipulated (for example, by a fuzzer or a specially crafted log record), the kernel could allocate a buffer that’s too small and perform out-of-bounds access during recovery — a classic memory-corruption pattern that can lead to crashes (denial of service) or, depending on memory layout and protections, potentially more severe impacts.
The vulnerability was fixed upstream by ensuring the buffer size calculation explicitly accounts for the fixed-up h_size again; the patch effectively ties the recovery buffer allocation to the corrected header size so the code cannot be tricked into an undersized allocation. Distribution vendors and cloud providers have backported or packaged this upstream fix into their kernel updates.
Important nuance:
Operational consequences:
However, that attestation is product-scoped. It should not be read as a categorical statement that no other Microsoft-supplied artifact could include the vulnerable XFS code. Security teams must take a conservative approach: treat attested products as authoritative signals, but verify all other Microsoft-provided kernels and images via kernel-config inspection, SBOM and version mapping, and image scanning. Prioritize patching, enable targeted mitigations where patching is delayed, and automate the inventory-to-patch workflow so that the next discovery cycle closes the remaining blind spots quickly and reliably.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE-2024-39472 is a medium-severity kernel defect in the XFS filesystem’s log recovery path. The root cause: a series of historical changes intended to handle an incorrect h_size value introduced by older mkfs.xfs tools. A later refactor cleaned up the block-count calculation but inadvertently stopped using the corrected (fixed-up) h_size when sizing the log recovery buffer. If the h_size used at runtime is manipulated (for example, by a fuzzer or a specially crafted log record), the kernel could allocate a buffer that’s too small and perform out-of-bounds access during recovery — a classic memory-corruption pattern that can lead to crashes (denial of service) or, depending on memory layout and protections, potentially more severe impacts.The vulnerability was fixed upstream by ensuring the buffer size calculation explicitly accounts for the fixed-up h_size again; the patch effectively ties the recovery buffer allocation to the corrected header size so the code cannot be tricked into an undersized allocation. Distribution vendors and cloud providers have backported or packaged this upstream fix into their kernel updates.
What Microsoft said — and what that wording actually means
Microsoft’s public advisory language for CVEs in recent months has followed a pattern: they identify the Microsoft-published product(s) that their inventory and mapping work have confirmed include the implicated open-source component. For CVE-2024-39472, Microsoft’s product mapping names Azure Linux as the Microsoft product that “includes this open-source library and is therefore potentially affected.” That is a useful and authoritative attestation for customers running those Azure Linux images.Important nuance:
- Product‑scoped attestation: Microsoft’s statement is an authoritative inventory outcome for the Azure Linux family at the time of publication — it tells Azure Linux customers they should treat Microsoft-published Azure Linux kernels and images as in-scope for remediation.
- Not a universal exclusion: The fact that Microsoft names only Azure Linux does not prove that other Microsoft artifacts (for example, WSL2 kernels, Marketplace images, specialized appliances, or other Microsoft-published Linux-derived artifacts) categorically do not include the same upstream XFS code or the vulnerable upstream commit range. Absence of an attestation is not evidence of absence.
- Operational implication: If you run Azure Linux images, follow Microsoft’s remediation guidance immediately. If you run any other Microsoft-supplied kernel-bearing artifact, you must verify the specific artifact/version and kernel configuration to confirm whether it is affected.
Why the distinction matters in practice
Vendor product attestations are valuable because they provide a clear, machine-readable signal for automation and triage: “KnownAffected”, “Fixed”, or “NotAffected” for a named product. However, modern enterprises run many images and artifacts — some Microsoft-owned, some third-party, some built in-house — and not all of these are necessarily included in a vendor’s attestation set at publication time.Operational consequences:
- An Azure Linux customer has a low-friction remediation path: apply Microsoft’s kernel update for Azure Linux and reboot.
- A customer running Microsoft Marketplace images, custom Azure VM images, or WSL2 may not be able to rely on the single attestation; those artifacts may still embed upstream kernel commits compiled with XFS support.
- Automated alerting and patch orchestration should use attestation outputs where present, but also supplement them with artifact scans, SBOM checks, and kernel-config inspection.
How to determine whether a given host or image is affected
Below is a practical checklist to identify whether a kernel-bearing host or image includes the vulnerable XFS code or the upstream commit range that was patched.- Check the kernel release and package build:
- uname -r
- uname -a
- Inspect kernel config for XFS:
- If /proc/config.gz exists:
- zgrep CONFIG_XFS /proc/config.gz
- Or check /boot/config-$(uname -r):
- grep CONFIG_XFS /boot/config-$(uname -r)
- Look for CONFIG_XFS=y or CONFIG_XFS=m — if neither exists, XFS support was not compiled in.
- Check for loaded XFS module (dynamic kernels):
- lsmod | grep xfs
- modinfo xfs
- Map your kernel package to distribution advisories and upstream commits:
- Compare your kernel version/package release to vendor advisories (distribution security notices, cloud provider advisories) to confirm whether the kernel includes the upstream fix that addresses the h_size allocation bug.
- For cloud marketplace images or custom images, check the image manifest or obtain the kernel package version and map it the same way.
- For WSL2 and other Microsoft-supplied kernels:
- Inspect the WSL kernel shipped on your machine (if using the Microsoft-provided WSL kernel binary) for a kernel config and version, then apply the same mapping process.
- If the WSL kernel was customized or installed by a Linux distro inside WSL, inspect that kernel instead.
- Scan images with SBOM and binary scanning:
- When possible, use vendor-provided SBOMs, VEX/CSAF attestations, or third-party image scanners to find instances of vulnerable kernels or kernel modules.
Remediation and mitigation guidance
The correct long-term fix is to install an updated kernel that includes the upstream patch for CVE-2024-39472. The following prioritized actions reflect operational realities:- If you run Azure Linux images:
- Apply Microsoft’s kernel updates for the Azure Linux release in use.
- Reboot the host (kernel updates require reboot to be effective).
- Validate that the kernel package version reported by uname -r matches the fixed package noted in the vendor advisory.
- For other distributions and cloud-provided images:
- Apply vendor-supplied kernel updates (Ubuntu, Red Hat, Amazon Linux, AlmaLinux, etc.) that backport the fix.
- Use your configuration management or orchestration system to schedule patching and reboots.
- For WSL2 or other Microsoft-supplied kernels:
- Verify the kernel version and config in your WSL instance; if the WSL kernel is Microsoft-provided and in the vulnerable range, follow Microsoft guidance if and when they publish a patch or updated WSL kernel.
- If you maintain a custom WSL kernel, rebuild it with the upstream fix applied.
- If immediate patching is impossible (temporary mitigations):
- Where feasible, avoid exposing attack surfaces that would allow untrusted actors to manipulate XFS log contents — for example, do not mount untrusted block images with XFS on unpatched kernels.
- Consider removing or unloading the XFS module (if compiled as a module) on systems that do not require XFS:
- Check configuration and, if safe, blacklist xfs or remove the module at runtime (note: unloading filesystem modules can be disruptive and is often impossible while the filesystem is mounted).
- Restrict local unprivileged account access. This CVE is a local attack vector (an attacker must be able to provide a crafted XFS log record), so limiting local access reduces risk.
- Implement increased monitoring for kernel OOPS, XFS-related errors in dmesg, and unusual I/O errors that could indicate attempted exploitation or triggered crashes.
- Long-term:
- Automate SBOM and VEX/CSAF ingestion and map attestations into your patch workflow.
- Keep an inventory of kernel-bearing artifacts (WSL kernels, Marketplace images, AKS node images, hosted appliances) and require image provenance before deployment.
Exploitability and risk: what operators need to know
CVE-2024-39472 is rated at a medium severity level in common tracking systems and is described as an out‑of‑bounds access in XFS log recovery. Key operational facts:- Attack vector: Local — the vulnerable code is in the filesystem recovery path; exploitation normally requires local access to present a crafted XFS log record, or mounting a crafted block device/image that contains malicious log metadata and then triggering log recovery.
- Privilege requirements: Low-level local privileges may be sufficient in some scenarios. Many exploit paths into kernel memory corruption start from low-privileged code, but the specifics depend on the target environment and kernel memory protections.
- Impact: Primarily availability (kernel crash/DoS) but memory-corruption bugs can escalate depending on environment and mitigations (e.g., kernel-hardening features, KASLR, KPTI, LOCKDOWN policies). No widely documented RCE exploit has been published publicly for this CVE at time of disclosure; however, threat actors often attempt to weaponize local kernel vulnerabilities.
- Distribution response: Major distributions and cloud vendors have backported or packaged the upstream fix into kernel releases; operators should use vendor advisories to identify which package versions are fixed.
Practical detection and triage steps (playbook)
Use this short playbook to rapidly triage possible exposure in your environment.- Inventory scanning
- Enumerate all hosts and images that carry a Linux kernel (cloud VMs, marketplace images, WSL2 instances, container hosts).
- Prioritize Azure Linux hosts first if Microsoft has attested them.
- Automated kernel inspection
- Run remote scripts to collect uname -r and /boot/config-$(uname -r) or /proc/config.gz.
- Flag hosts where CONFIG_XFS is present or xfs module is loaded.
- Map to fixed versions
- Cross-check flagged kernel versions against vendor advisories and distribution security notices to determine if the kernel includes the upstream fix.
- Patch and verify
- Patch kernel packages and reboot.
- Re-run uname -r and kernel config checks post-reboot to verify the fixed kernel is active.
- Temporary mitigations
- If patching is delayed, restrict mounting of untrusted images, restrict local account capabilities, and isolate hosts with XFS mounts from untrusted users.
- Post-remediation monitoring
- Monitor kernel logs (dmesg), system stability, and compliance scanning results to confirm completion.
Why customers should still verify beyond the Microsoft attestation
Microsoft’s attestation naming Azure Linux is a positive step for transparency and automation, but there are multiple reasons you should independently verify other Microsoft artifacts:- Microsoft’s product attestations are rolled out in phases. The absence of an attestation for a product does not prove it is unaffected; it may simply not yet have been mapped.
- Microsoft and other vendors ship many kernel-bearing artifacts: WSL kernels, Azure Marketplace VM images, AKS node images, and OEM images. Any of these could have been built from upstream commits in the vulnerable range and compiled with XFS support.
- Organizations often run a mix of vendor-provided and internally built images. Only artifact-level inspection will reveal whether an individual image includes the vulnerable code.
Notable strengths and potential risks in the vendor response model
Strengths:- Product-level attestations provide a clear remediation signal and allow automation to prioritize known-affected product families (reducing triage time).
- Upstream kernel fixes and distribution backports are generally available quickly for widely used filesystems like XFS.
- Vendors that publish machine-readable attestations (CSAF/VEX) enable scalable automation and faster, less error-prone triage.
- Attestations do not automatically cover every vendor-provided artifact — phased attestations create a window where other artifacts may still be unverified.
- Customers who rely solely on vendor attestation without artifact verification risk missing exposure in images not yet mapped.
- Kernel vulnerabilities with a local attack vector rely heavily on blocking local access; multi-tenant cloud environments or poorly isolated images increase risk.
Conclusion
CVE-2024-39472 is a genuine XFS kernel bug that has been fixed upstream and incorporated into distribution kernels. Microsoft’s public guidance naming Azure Linux as a product that “includes this open-source library and is therefore potentially affected” is an important and actionable attestation for Azure Linux customers — apply Microsoft’s Azure Linux kernel updates without delay.However, that attestation is product-scoped. It should not be read as a categorical statement that no other Microsoft-supplied artifact could include the vulnerable XFS code. Security teams must take a conservative approach: treat attested products as authoritative signals, but verify all other Microsoft-provided kernels and images via kernel-config inspection, SBOM and version mapping, and image scanning. Prioritize patching, enable targeted mitigations where patching is delayed, and automate the inventory-to-patch workflow so that the next discovery cycle closes the remaining blind spots quickly and reliably.
Source: MSRC Security Update Guide - Microsoft Security Response Center