Microsoft’s short public answer — that “Azure Linux includes this open‑source library and is therefore potentially affected” — is accurate as a product-level attestation, but it is not a technical guarantee that no other Microsoft product contains the same vulnerable kernel code; operators must treat Azure Linux as a confirmed carrier while performing artifact‑level verification across other Microsoft‑distributed kernels and images.
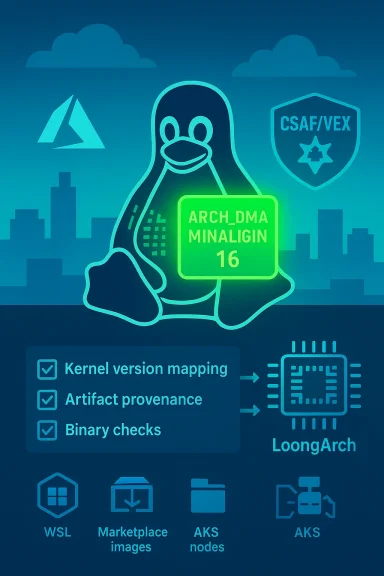
The vulnerability tracked as CVE‑2025‑22049 is a kernel-level correction in the LoongArch architecture support that increases the architecture DMA alignment requirement by raising ARCH_DMA_MINALIGN from 1 to 16 bytes. The rationale is simple: some LoongArch devices (for example, APBDMA-class devices) require 16‑byte alignment for DMA buffers; allocating very small, poorly aligned buffers can let hardware write beyond safe cacheline boundaries and produce incorrect writes or memory-corruption conditions. The upstream Linux CVE announcement records the fix and lists the stable kernel releases that received it.
This is a source-tree, kernel-level change (the touched file is arch/loongarch/include/asm/cache.h), not a userland library patch. That distinction matters operationally: any Microsoft product that ships or manages a Linux kernel binary that contains the vulnerable code or predates the backported fix is a candidate for remediation. Conversely, userland-only packages that do not bundle a kernel binary are not themselves carriers — though they can be impacted by a vulnerable host kernel at runtime.
The upstream stability and fix history are straightforward: the change was merged into a number of kernel branches and stable releases (for example, fixes landed in stable trees such as 6.1.134, 6.6.87, 6.12.23, and in the v6.15 series via the 6.15 merge). Administrators should use those kernel version mappings as the first line of triage when mapping their fleet.
Read strictly, Microsoft’s sentence is an attestation for Azure Linux: it confirms that Microsoft has inspected the Azure Linux build outputs and found the implicated upstream component there. It is not a statement that Microsoft has completed an exhaustive inventory across every Microsoft-distributed kernel, image, or appliance. In practical terms: treat Azure Linux as Known Affected for that CVE until Microsoft declares otherwise for other products.
Multiple independent commentators and community threads have emphasized the same nuance: the attestation reduces noise for Azure Linux customers and gives them direct remediation steps, but absence of an attestation for, say, a WSL kernel or a Marketplace VM image is not proof those artifacts are safe — it simply means they haven’t been attested yet. Vendors with large artifact surfaces commonly roll out attestations in phases; Microsoft has publicly committed to expanding coverage as inventories complete.
Why this distinction matters:
However, the approach has limits and operational caveats:
However, Azure Linux is not necessarily the only Microsoft product that could include the same upstream code. The attestation signals what Microsoft has validated so far, not an exhaustive inventory of every Microsoft artifact. Security teams must therefore combine vendor attestations with artifact-level discovery (kernel version checks, commit presence verification, image metadata inspection) to rule in or out exposure across the rest of their Microsoft-distributed estate. This combined approach — vendor attestations as a signal, artifact verification as the check — is the defensible path forward when managing kernel-level CVEs like CVE‑2025‑22049.
In short: patch Azure Linux immediately and treat Microsoft’s VEX/CSAF attestations as a strong aid — but do not let a single product-level attestation be the final line of defense. Inventory, verify, and automate your way to a complete remediation posture.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The vulnerability tracked as CVE‑2025‑22049 is a kernel-level correction in the LoongArch architecture support that increases the architecture DMA alignment requirement by raising ARCH_DMA_MINALIGN from 1 to 16 bytes. The rationale is simple: some LoongArch devices (for example, APBDMA-class devices) require 16‑byte alignment for DMA buffers; allocating very small, poorly aligned buffers can let hardware write beyond safe cacheline boundaries and produce incorrect writes or memory-corruption conditions. The upstream Linux CVE announcement records the fix and lists the stable kernel releases that received it.This is a source-tree, kernel-level change (the touched file is arch/loongarch/include/asm/cache.h), not a userland library patch. That distinction matters operationally: any Microsoft product that ships or manages a Linux kernel binary that contains the vulnerable code or predates the backported fix is a candidate for remediation. Conversely, userland-only packages that do not bundle a kernel binary are not themselves carriers — though they can be impacted by a vulnerable host kernel at runtime.
The upstream stability and fix history are straightforward: the change was merged into a number of kernel branches and stable releases (for example, fixes landed in stable trees such as 6.1.134, 6.6.87, 6.12.23, and in the v6.15 series via the 6.15 merge). Administrators should use those kernel version mappings as the first line of triage when mapping their fleet.
What Microsoft actually said — and what that wording means
Microsoft’s MSRC entries for some Linux CVEs have followed a concise pattern: a short product-level statement that a specific Microsoft product “includes this open‑source library and is therefore potentially affected,” accompanied by a commitment to publish machine‑readable CSAF/VEX attestations starting in October 2025 and to update CVE mappings if additional Microsoft products are identified as carriers. That transparency move was announced publicly as part of the MSRC’s VEX rollout and is intended to make vendor attestations machine-actionable for downstream tooling.Read strictly, Microsoft’s sentence is an attestation for Azure Linux: it confirms that Microsoft has inspected the Azure Linux build outputs and found the implicated upstream component there. It is not a statement that Microsoft has completed an exhaustive inventory across every Microsoft-distributed kernel, image, or appliance. In practical terms: treat Azure Linux as Known Affected for that CVE until Microsoft declares otherwise for other products.
Multiple independent commentators and community threads have emphasized the same nuance: the attestation reduces noise for Azure Linux customers and gives them direct remediation steps, but absence of an attestation for, say, a WSL kernel or a Marketplace VM image is not proof those artifacts are safe — it simply means they haven’t been attested yet. Vendors with large artifact surfaces commonly roll out attestations in phases; Microsoft has publicly committed to expanding coverage as inventories complete.
Is Azure Linux the only Microsoft product that could be affected?
Short answer: No — not necessarily. Azure Linux is simply the only Microsoft product Microsoft has publicly attested as including the upstream kernel code implicated by the CVE at the time of the advisory. That attestation is authoritative for Azure Linux, but it does not logically or technically exclude other Microsoft artifacts (for example, WSL2 kernel builds, Azure Marketplace images, managed node images for AKS, or specialized kernel builds used by platform services) from containing the same upstream source until those artifacts are separately inventoried and attested.Why this distinction matters:
- Product attestation ≠ exclusivity. Vendors attest when they finish a product inventory; other artifacts may be inventoried later and added to the VEX map.
- Kernel-level CVEs affect any artifact that ships a kernel. If Microsoft ships or publishes compiled Linux kernels across multiple products, each compiled kernel must be checked for the presence of fixed commits or for the vulnerable kernel version range.
- Containers and images may be indirectly affected. A container built from a patched userland is still vulnerable at runtime if it runs on an unpatched host kernel; conversely, a patched host kernel protects containers regardless of their userland contents. This makes both the host kernel and distributed kernel artifacts important to inventory.
Technical verification: what to check and how to confirm exposure
Before you decide a Microsoft artifact is safe or affected, verify the following technical facts. Cross-check each step against at least two independent sources when possible.- Kernel version mapping. Confirm whether your running kernel version includes the stable-tree release that carried the fix. The Linux CVE announcement lists fixed versions (for CVE‑2025‑22049, the fix is recorded in specific stable kernels such as 6.1.134, 6.6.87, 6.12.23, 6.13.11, 6.14.2 and in the v6.15 merge). If your kernel is older than the fixed stable release and you have not applied vendor backports, treat the host as potentially vulnerable.
- Commit presence. If you maintain custom kernels or vendors provide backports, confirm the presence of the specific upstream commit(s) that implemented the change. The upstream announcement and stable-tree commit references are authoritative for this check. When dealing with vendor backports, ensure vendor changelogs map the CVE to precise package builds.
- Artifact provenance. For Microsoft-distributed artifacts, ask or check whether the specific artifact is built from a kernel tree that predates the fix. Examples:
- WSL2 kernels published by Microsoft on their kernel repo may include or omit the fix depending on the WSL kernel version in use; the WSL kernel is a distinct artifact and must be assessed separately.
- Azure Marketplace VM images may carry kernels supplied by the distribution vendor or by Microsoft’s Azure-tuned kernels. Confirm which kernel binary the image contains and map it to the fix.
- Binary-level checks. If you cannot rely on package metadata, inspect the kernel binary or use a deployed node’s dmesg / kernel dmesg for early indicators of LoongArch-related errors in heterogeneous deployments (LoongArch‑specific hardware will be rare outside targeted environments, but the binary check is definitive). When in doubt, rebuild with a patched kernel or apply a vendor-supplied kernel update.
- On a Linux host: check uname and package versions (for example, uname -r and your distro’s kernel package info) and compare to the fixed stable kernels listed in upstream advisories.
- For WSL: check the WSL kernel release or the Microsoft-supplied WSL kernel repository release notes and map to the fixed commits.
- For Marketplace images: extract the kernel version from the image metadata or boot log and validate against the fixed list or vendor advisory.
Practical remediation and mitigation: prioritized actions
If you operate Azure Linux images, Microsoft has already declared them in-scope — patch those first. For broader environments, follow this prioritized checklist:- Immediate (0–24 hours)
- Patch Azure Linux images. Apply Microsoft’s published updates for Azure Linux and redeploy patched images according to your change windows. Treat the attested product as Known Affected.
- Inventory Microsoft-supplied artifacts. Identify WSL kernels, Marketplace images, AKS node images, and any other Microsoft-distributed artefacts you run. Record kernel versions for each.
- Apply temporary isolation. If you cannot immediately patch a host that runs an untrusted workload (multi‑tenant host or developer build host), restrict access and limit unprivileged DMA-capable device assignment where possible.
- Short-term (1–7 days)
- Map kernel versions to upstream fixes. Use the stable-tree version list from the Linux CVE announcement and vendor advisories to decide whether your artifacts are patched, backported, or vulnerable.
- Rebuild or update images. For any image that includes a vulnerable kernel, rebuild with a patched kernel or apply the vendor-supplied patch set. Where vendor livepatching is available and acceptable, use it as an interim mitigation.
- Medium-term (1–8 weeks)
- Adopt automated VEX/CSAF ingestion. Consume Microsoft’s CSAF/VEX attestations (published starting October 22, 2025) so your vulnerability management tooling can automatically interpret which Microsoft artifacts are Known Affected, Not Affected, or Under Investigation. Treat VEX as a structured input — not as a sole source of truth — and combine it with binary-level checks and SBOMs.
- Extend artifact verification. Build scripts, CI checks, or SBOM-based scans that can detect kernel version and patch level across WSL, container images, Marketplace images, and VM templates.
- Long-term
- Establish kernel inventory governance. Big vendors ship many kernels; make kernel provenance part of your image- and artifact-governance process. Track what entity built each kernel and whether that builder’s pipeline consumes vendor backports.
- Request attestations for high-value artifacts. If you operate bespoke or partner-provided Marketplace appliances, ask vendors (including Microsoft, when applicable) to attest whether those artifacts are in-scope for a CVE. Use VEX/CSAF to reduce manual triage when vendors provide it.
Why Microsoft’s VEX/CSAF approach is important — and where it falls short
Microsoft’s decision to publish machine-readable attestations (CSAF/VEX) is a meaningful step toward making large-vendor disclosures actionable. VEX gives security teams clear, machine consumable statements such as Not Affected, Under Investigation, Known Affected, or Fixed for each product‑artifact mapping — information that reduces noisy alerts and speeds triage. The MSRC blog explains why this standardization matters for enterprise automation and faster decision-making.However, the approach has limits and operational caveats:
- Phased rollouts create transient blind spots. Large vendors typically cannot inventory every artifact at once. The attestation for one product (Azure Linux) does not certify all other Microsoft artifacts. Customers must not assume attestation absence equals safety.
- Inventory accuracy depends on build metadata. To attest reliably, vendors need reproducible build provenance and SBOMs that map upstream components to shipped binaries. When provenance is incomplete, attestation mappings can be delayed.
- Tooling adoption is necessary. VEX is only as useful as the downstream toolchain that ingests and acts upon those attestations. Organizations that haven’t automated VEX/CSAF ingestion will still face manual triage burdens.
Risk scenarios and realistic exploitability discussion
CVE‑2025‑22049 is an architecture-specific DMA alignment correctness fix. The practical exploitability depends on your deployment footprint:- If you run LoongArch hardware or software stacks that emulate LoongArch, the risk is real: misaligned DMA buffers can produce hardware writes that cause corruption or incorrect behavior. The upstream patch specifically targets LoongArch‑specific device behavior.
- For most Microsoft cloud customers running x86_64 or ARM64 images, LoongArch-specific kernel fixes will rarely be directly exploitable because the hardware and kernel config differ. However, the general principle applies: any product that ships a kernel containing the vulnerable code path must be inventoried and validated. In other words, architecture specificity lowers the practical exposure footprint but does not absolve artifact verification responsibilities.
- Attack vectors for this class of issue are local or adjacent to device access — a remote attacker without local access to DMA-capable device interfaces is unlikely to exploit the flaw. But in multi‑tenant or cloud provider contexts where devices may be assigned to guest VMs, the tenancy model can create indirect exposure paths. This nuance is why cloud OS teams and image publishers must be explicit about which artifacts include which kernel components.
- Microsoft’s attestation for Azure Linux is verifiable and actionable; whether other Microsoft artifacts currently include the same LoongArch code is a fact that requires inventory checks that Microsoft has promised to perform and publish. Until Microsoft updates the CVE’s VEX mapping, any claim that no other Microsoft product is affected should be considered unverified. Use cautionary language and treat non-attested artifacts as not yet attested, not proven safe.
Checklist for security teams: concrete next steps
- Treat Azure Linux as confirmed in-scope. Patch and redeploy Azure Linux images immediately.
- Inventory Microsoft-distributed artifacts in your environment (WSL kernels, Marketplace images, AKS node images, developer VMs). Record kernel versions.
- Map kernel versions to the upstream fixed versions listed in the Linux CVE announcement. If kernel versions are older, assume vulnerability until verified.
- If you maintain custom kernels, apply the upstream commit(s) or backport vendor fixes, rebuild and test.
- Ingest Microsoft’s CSAF/VEX attestations as they are published and use them to automate prioritization — but keep artifact-level verification as a parallel control.
- Document provenance and SBOMs for your images and maintainers’ attestations so future CVE sweeps are faster and less error-prone.
Final assessment and takeaways
Microsoft’s statement that Azure Linux includes the open-source library and is potentially affected is a useful, authoritative product-level attestation and a direct cue for Azure Linux operators to act now. The MSRC commitment to publish machine-readable CSAF/VEX attestations (started October 22, 2025) will materially improve the downstream automation of vulnerability triage.However, Azure Linux is not necessarily the only Microsoft product that could include the same upstream code. The attestation signals what Microsoft has validated so far, not an exhaustive inventory of every Microsoft artifact. Security teams must therefore combine vendor attestations with artifact-level discovery (kernel version checks, commit presence verification, image metadata inspection) to rule in or out exposure across the rest of their Microsoft-distributed estate. This combined approach — vendor attestations as a signal, artifact verification as the check — is the defensible path forward when managing kernel-level CVEs like CVE‑2025‑22049.
In short: patch Azure Linux immediately and treat Microsoft’s VEX/CSAF attestations as a strong aid — but do not let a single product-level attestation be the final line of defense. Inventory, verify, and automate your way to a complete remediation posture.
Source: MSRC Security Update Guide - Microsoft Security Response Center