Microsoft’s brief, machine‑readable advisory that “Azure Linux includes this open‑source library and is therefore potentially affected” is accurate — but it is a product‑scoped attestation, not a blanket guarantee that no other Microsoft product could carry the same vulnerable ksmbd code.
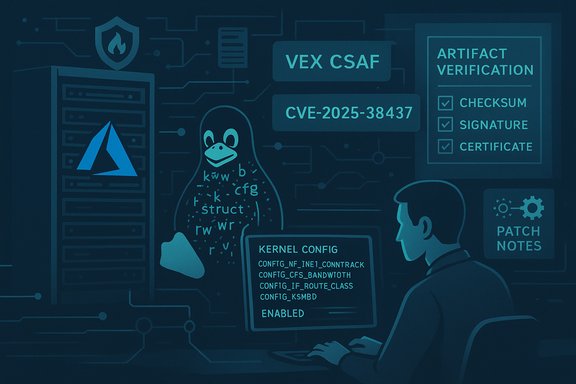
CVE‑2025‑38437 is an upstream Linux kernel vulnerability in the in‑kernel SMB server subsystem ksmbd described as “fix potential use‑after‑free in oplock/lease break ack.” The upstream description and public trackers show the defect can occur when ksmbd response pinning fails and code later dereferences freed opinfo structures or calls release helpers twice; the upstream fixes are small, surgical changes to close the lifetime race and prevent a use‑after‑free. Public vulnerability databases (NVD, distro trackers) and upstream stable commits all record the same root cause and the same corrective commits. Microsoft’s Security Response Center (MSRC) has published a concise product attestation in machine‑readable VEX/CSAF form stating that the Azure Linux distribution (the Microsoft‑published Linux distro lineage) includes the implicated open‑source component and is therefore potentially affected. Microsoft also publicly committed to expand its VEX/CSAF coverage over time and update CVE mappings if additional Microsoft products are later found to ship the same upstream code. That phased rollout began with Azure Linux and is meant to provide deterministic, automatable signals for customers running Microsoft‑published Linux images.
Longer, operationally accurate answer: Azure Linux is currently the only Microsoft product Microsoft has publicly attested to include the vulnerable ksmbd component for CVE‑2025‑38437, and that makes Azure Linux the highest‑priority Microsoft product for remediation where it is used. However, because Linux kernel inclusion is an artifact‑level property (driven by kernel version, CONFIG_ build flags, and packaging choices), other Microsoft‑supplied kernel artifacts may also include ksmbd until they are inventoried and attested or verified by artifact inspection. Treat the MSRC attestation as definitive for Azure Linux and treat everything else as unverified* until proven otherwise.
Key phrases to track in your automation and monitoring: CVE‑2025‑38437, ksmbd use‑after‑free, Azure Linux VEX/CSAF, ksmbd oplock lease break ack, Microsoft attestation, kernel vulnerability, WSL2 kernel verification, kernel config CONFIG_KSMBD, Marketplace image SBOM.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE‑2025‑38437 is an upstream Linux kernel vulnerability in the in‑kernel SMB server subsystem ksmbd described as “fix potential use‑after‑free in oplock/lease break ack.” The upstream description and public trackers show the defect can occur when ksmbd response pinning fails and code later dereferences freed opinfo structures or calls release helpers twice; the upstream fixes are small, surgical changes to close the lifetime race and prevent a use‑after‑free. Public vulnerability databases (NVD, distro trackers) and upstream stable commits all record the same root cause and the same corrective commits. Microsoft’s Security Response Center (MSRC) has published a concise product attestation in machine‑readable VEX/CSAF form stating that the Azure Linux distribution (the Microsoft‑published Linux distro lineage) includes the implicated open‑source component and is therefore potentially affected. Microsoft also publicly committed to expand its VEX/CSAF coverage over time and update CVE mappings if additional Microsoft products are later found to ship the same upstream code. That phased rollout began with Azure Linux and is meant to provide deterministic, automatable signals for customers running Microsoft‑published Linux images. What the MSRC sentence actually means
Product‑scoped attestation, not exclusivity
Microsoft’s wording is intentionally narrow and machine readable: it documents what Microsoft has validated and mapped so far. In practice that means:- Authoritative for Azure Linux: If you run official Azure Linux images, the MSRC attestation is the canonical signal that those images were inventoried and the vulnerable ksmbd component was found there — treat that as actionable.
- Not a proof‑of‑absence for other products: The absence of a VEX/CSAF attestation for another Microsoft product (for example, WSL2 kernels, linux‑azure kernel packages used in some VM SKUs, AKS node images, or Marketplace appliances) is not proof those products do not contain the vulnerable kernel code. It is simply an absence of attestation — Microsoft’s inventory work is phased and ongoing.
Why vendors publish VEX/CSAF per product
VEX/CSAF lets vendors map upstream CVEs to specific product SKUs. Microsoft began with Azure Linux to deliver a high‑confidence, machine‑readable inventory for one product family and will expand coverage as inventory work completes. This is good supply‑chain hygiene, but it creates a window where other artifacts remain unverified unless explicitly attested or inspected.Is Azure Linux the only Microsoft product potentially affected?
Short answer: No — not necessarily.Longer, operationally accurate answer: Azure Linux is currently the only Microsoft product Microsoft has publicly attested to include the vulnerable ksmbd component for CVE‑2025‑38437, and that makes Azure Linux the highest‑priority Microsoft product for remediation where it is used. However, because Linux kernel inclusion is an artifact‑level property (driven by kernel version, CONFIG_ build flags, and packaging choices), other Microsoft‑supplied kernel artifacts may also include ksmbd until they are inventoried and attested or verified by artifact inspection. Treat the MSRC attestation as definitive for Azure Linux and treat everything else as unverified* until proven otherwise.
Which Microsoft artifacts could, in theory, carry the same upstream code?
- WSL2 kernel binaries that Microsoft publishes for Windows Subsystem for Linux. Microsoft maintains the WSL2 kernel sources and publishes kernel builds; whether those builds include ksmbd depends on the kernel configuration used for those WSL releases.
- linux‑azure kernels or Azure‑tuned kernels shipped as part of specific VM SKUs. Kernel packaging for VM images can differ from the Azure Linux distro kernel.
- AKS node images, curated Marketplace VM images, or vendor appliances that include Linux kernel binaries Microsoft or partners publish. These may use different kernels or kernel configs.
- Third‑party Marketplace appliances or partner‑provided images hosted in Azure — inventory and patching are typically the publisher’s responsibility; Microsoft’s Azure Linux attestation does not automatically cover those images.
Practical verification checklist (artifact‑level steps)
Operators should treat Microsoft’s attestation as a signal for Azure Linux and take the following artifact‑level verification steps for any Microsoft‑supplied Linux artifact in their estate.1. Identify the artifact(s)
- List all Microsoft‑supplied or Microsoft‑published Linux artifacts you run:
- Azure Linux images (attested).
- WSL2 instances and the WSL kernel binary.
- linux‑azure kernels in VM images.
- AKS node images and Marketplace appliances.
- For each artifact, record the kernel version and the package identity.
2. Confirm whether ksmbd is present in the kernel build
- If you can run commands on the host:
- lsmod | egrep -i 'ksmbd'
- zcat /proc/config.gz | grep -i KSMBD || grep -i ksmbd /boot/config-$(uname -r)
- modinfo ksmbd (if present as a module)
- If you cannot run code (e.g., for some Marketplace appliances), request the vendor or publisher provide:
- kernel config (CONFIG_KSMBD and related options),
- SBOM or VEX/CSAF attestation,
- kernel package changelog that references the upstream commit or CVE.
3. Cross‑check kernel version against upstream fixes
- Map the kernel version and package version to upstream commits and distro advisories (NVD, Debian/Ubuntu trackers, vendor advisories). Upstream commits fixing CVE‑2025‑38437 are merged into stable kernel trees and have been referenced by distro advisories. Use the distro tracker (Ubuntu, Debian) and NVD for confirmation.
4. Confirm the fix is present in your kernel package
- RPM/DEB changelogs or vendor advisories should explicitly reference CVE‑2025‑38437 or the upstream commit IDs.
- For Azure Linux, consume Microsoft’s VEX/CSAF attestation and the distro’s patch advisory to ensure the fix is included.
5. If the fix is not present, apply mitigations or patch
- Schedule patching as the primary remedy: upgrade kernel package to a release that includes the upstream fix, then reboot.
- If patching is delayed, apply mitigations (see next section).
Short‑term mitigations and risk reduction
When immediate patching is infeasible or when you must protect an unverified artifact, apply the following mitigations:- Network segmentation / firewalling: Block or restrict SMB server ports (TCP 445 and 139) and any other channels that allow untrusted peers to interact with ksmbd‑enabled hosts.
- Unload or disable ksmbd where possible: If ksmbd is a loadable module, remove it (rmmod ksmbd) or disable the service that brings it up. Confirm your environment does not rely on in‑kernel SMB server functionality before doing so.
- Host hardening: Limit user namespaces, disallow untrusted local users from creating network endpoints that reach ksmbd, and reduce the attack surface of multi‑tenant hosts by isolating untrusted workloads.
- Device and service isolation: Move SMB‑exposing workloads to patched hosts or to user‑space Samba with up‑to‑date packages if that is faster to patch for your environment.
- Monitoring: Add focused log and kernel oops monitoring for ksmbd‑related WARNs or KASAN messages; use dmesg/journalctl, and instrument kernel logs centrally so you can detect anomalous use‑after‑free traces quickly.
Detection and monitoring guidance
- Search kernel logs (dmesg, journalctl -k) for ksmbd WARNs, oopses, or KASAN traces referencing opinfo or ksmbd_session objects.
- Track system level indicators:
- Sudden increases in ksmbd‑related slab allocations.
- Repeated kernel warnings during SMB lease/oplock operations.
- Integrate vendor feeds and VEX/CSAF into your vulnerability management tools so that an update to a Microsoft attestation automatically flags affected assets. Microsoft’s VEX/CSAF feeds and provider metadata are the intended automation inputs for this purpose.
Operational impact and prioritization
- Azure Linux customers: treat the Microsoft attestation as the authoritative signal — patch as soon as a patched kernel package is available and schedule reboots accordingly. Azure Linux is the highest priority Microsoft product to remediate because Microsoft has already validated its presence there.
- Mixed Windows + Linux estates / WSL users: WSL2 users should check whether their WSL kernel binary includes ksmbd or whether the WSL kernel build config includes KSMBD. If Microsoft publishes a WSL VEX attestation later, use that; until then, perform artifact inspection.
- Marketplace images and third‑party appliances: do not assume the Azure Linux attestation covers these; obtain SBOMs or attestations from the image publisher and insist on explicit CVE mappings or patch timelines.
- High‑value or multi‑tenant services: prioritize patching or worker migration away from unpatched hosts; a kernel use‑after‑free is primarily an availability and stability risk but may enable more severe chained exploitation in specific environments.
Why the nuance matters: inventory vs. code presence
Kernel code inclusion is an artifact‑level property: the same upstream driver may or may not be present in a particular kernel binary depending on which configuration flags were enabled at build time, whether the driver was built into the kernel image or as a module, or whether the vendor backported the fix. This is why Microsoft’s VEX/CSAF approach is a pragmatic improvement — it tells customers which product images were validated — but it does not replace artifact verification when your fleet includes many different images and distributions. Treat the Azure Linux VEX as authoritative for Azure Linux and use artifact checks or vendor attestations for everything else.Cross‑checking the facts (verification of claims)
- The technical description of CVE‑2025‑38437 and the upstream fixes are documented in mainstream vulnerability trackers and distro advisories (NVD, Ubuntu, Debian), which confirm the use‑after‑free and the nature of the fix.
- Microsoft’s public VEX/CSAF rollout blog explains the phased approach (starting with Azure Linux) and Microsoft’s commitment to expand attestations — that blog is the primary public record for Microsoft’s attestation strategy. Use it to automate ingestion of Microsoft’s product‑level attestations.
- Independent operational commentary and practical verification playbooks (security analyst and operator briefings) consistently draw the same operational conclusion: Microsoft’s attestation is authoritative for Azure Linux, but absence of attestation elsewhere is not proof of absence; artifact checks are required.
Recommendations — a concrete playbook (step‑by‑step)
- Immediately identify and list all Azure Linux instances and apply the vendor‑provided kernel patch. Use automation (patch management) to target these images first since Microsoft has attested Azure Linux.
- Inventory all other Microsoft‑distributed kernel artifacts you run (WSL2, AKS nodes, linux‑azure images, Marketplace appliances). For each, perform the verification checklist in this article.
- If an artifact cannot be inspected, demand an SBOM/VEX attestation or vendor changelog that references CVE‑2025‑38437 before trusting it as patched.
- For hosts that cannot be patched quickly, apply mitigations (firewall SMB ports, unload ksmbd module where feasible, isolate tenants). Monitor kernel logs centrally for ksmbd‑related anomalies.
- Subscribe to Microsoft’s CSAF/VEX feed and your distro/vendor advisories to automate detection when Microsoft expands attestations to additional products.
Notable strengths of Microsoft’s disclosure approach — and the residual risks
Strengths:- Machine‑readable VEX/CSAF gives automation-friendly signals to accelerate triage for the Microsoft product family that has been attested (Azure Linux).
- Public commitment to expand coverage reduces ambiguity and sets an expectation for Microsoft to update attestations as inventory work completes.
- Phased rollout leaves unverified artifacts: until Microsoft attests additional products or publishers supply SBOMs, other Microsoft kernel artifacts remain unverified and may carry the vulnerable code.
- Build variability: even within Microsoft, kernel build configs differ. Two images can contain different modules and therefore different exposure profiles.
- Supply‑chain gaps: third‑party Marketplace images and partner appliances require explicit attestations from the image publisher; Microsoft’s Azure Linux attestation does not automatically extend to partner images.
Conclusion
Microsoft’s statement that Azure Linux includes this open‑source library and is therefore potentially affected is accurate and actionable for Azure Linux customers: it is a machine‑readable, authoritative attestation for that product family and should drive immediate remediation where Azure Linux is used. However, it should not be read as an exclusive, product‑wide denial for Microsoft’s entire portfolio. Kernel code inclusion is an artifact‑level property and must be verified per artifact for WSL2, linux‑azure kernels, AKS node images, Marketplace appliances, and other Microsoft‑distributed artifacts. Until a Microsoft VEX/CSAF attestation or vendor SBOM explicitly covers a product, treat that product as unverified and apply the verification checklist and mitigations in this feature to reduce operational risk.Key phrases to track in your automation and monitoring: CVE‑2025‑38437, ksmbd use‑after‑free, Azure Linux VEX/CSAF, ksmbd oplock lease break ack, Microsoft attestation, kernel vulnerability, WSL2 kernel verification, kernel config CONFIG_KSMBD, Marketplace image SBOM.
Source: MSRC Security Update Guide - Microsoft Security Response Center