Microsoft’s MSRC entry for CVE‑2025‑37881 correctly identifies a kernel bug in the Aspeed USB vHub gadget driver — but the short MSRC phrasing that “Azure Linux includes this open‑source library and is therefore potentially affected” is a product‑scoped inventory statement, not a categorical guarantee that no other Microsoft product could ship the same vulnerable upstream code.
CVE‑2025‑37881 is a narrowly scoped Linux‑kernel robustness fix: a NULL pointer check was missing in ast_vhub_init_dev(), part of the Aspeed vHub USB gadget driver (drivers/usb/gadget/udc/aspeed‑vhub). The function called devm_kasprintf() to allocate and format a device name; if that allocation failed and returned NULL the code could dereference the pointer and trigger a kernel NULL‑pointer dereference. Upstream maintainers received a patch that inserts a defensive check and returns -ENOMEM when devm_kasprintf() returns NULL. The patch and downstream advisories are public and the vulnerability has been tracked across vendor advisories and the NVD.
This is a local robustness/availability issue. Most public trackers rate the impact as medium and the likely impact category as availability (kernel crash), rather than confidentiality or privilege escalation; exploitation requires local or low‑privilege access to trigger the code path in question. Several Linux distributors (Ubuntu, Debian, SUSE, Oracle, Amazon Linux and others) have recorded the CVE and issued or scheduled fixes in their kernels.
Two important interpretations flow from that wording:
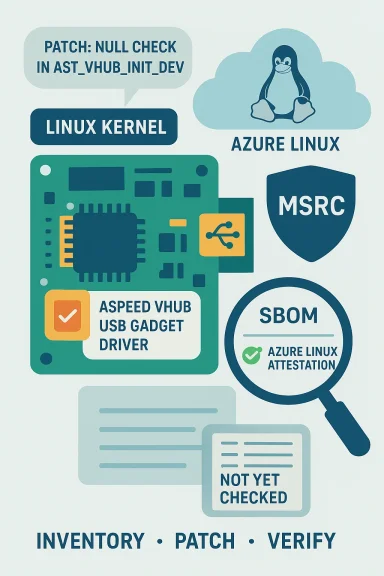
The immediate operational work is straightforward: inventory, patch, and monitor. The strategic work is organizational: keep SBOMs, machine‑readable attestations, and vendor advisories synchronized with your asset inventory so product‑scoped statements speed remediation rather than create false reassurance.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE‑2025‑37881 is a narrowly scoped Linux‑kernel robustness fix: a NULL pointer check was missing in ast_vhub_init_dev(), part of the Aspeed vHub USB gadget driver (drivers/usb/gadget/udc/aspeed‑vhub). The function called devm_kasprintf() to allocate and format a device name; if that allocation failed and returned NULL the code could dereference the pointer and trigger a kernel NULL‑pointer dereference. Upstream maintainers received a patch that inserts a defensive check and returns -ENOMEM when devm_kasprintf() returns NULL. The patch and downstream advisories are public and the vulnerability has been tracked across vendor advisories and the NVD.This is a local robustness/availability issue. Most public trackers rate the impact as medium and the likely impact category as availability (kernel crash), rather than confidentiality or privilege escalation; exploitation requires local or low‑privilege access to trigger the code path in question. Several Linux distributors (Ubuntu, Debian, SUSE, Oracle, Amazon Linux and others) have recorded the CVE and issued or scheduled fixes in their kernels.
What the patch changes (technical details)
The bug and the minimal fix
- The problematic line in ast_vhub_init_dev() called devm_kasprintf() to build a port name (for example "port1").
- devm_kasprintf() can return NULL when memory allocation fails; ast_vhub_init_dev() originally proceeded to use d->name without checking it.
- The fix is a small, defensive insertion:
- if (!d->name) return -ENOMEM;
- This prevents the NULL dereference by aborting the device initialization when the name allocation fails.
Where the driver is configured and when it’s present
- The driver is available under the kernel config item CONFIG_USB_ASPEED_VHUB and commonly built as module
aspeed‑vhubin kernels that include the Aspeed vHub driver; it is present in a wide range of stable kernel branches and vendor kernels. If a kernel build enables that config, the driver will be present either compiled in or as a module. Administrators can check for it in a running system by querying kernel config and loaded modules (commands shown later).
How Microsoft described the exposure (and why that wording matters)
Microsoft’s MSRC advisory (the one quoted by the user) takes the form of a concise mapping: “Azure Linux includes this open‑source library and is therefore potentially affected.” That is an attestation — a statement that, after inventory and analysis, Microsoft has found the implicated upstream component in the Azure Linux product family (the Linux distribution Microsoft publishes for Azure). Microsoft also stated publicly that it is publishing CSAF/VEX attestations and will update CVE mappings if additional Microsoft products are discovered to ship the component.Two important interpretations flow from that wording:
- It is an authoritative yes for Azure Linux: if you run Azure Linux images, treat Microsoft’s attestation as a direct instruction to include those images in your remediation plan.
- It is not an exclusivity statisory does not assert that only Azure Linux can ever ship the vulnerable upstream code. Absence of public attestations for other Microsoft products is not evidence they are unaffected — it may simply mean Microsoft has not yet completed inventory or published attestations for those artifacts. Independent analysis and vendor‑side inventory are still required.
Short answer to the user’s question
No. Azure Linux is the only Microsoft product Microsoft has publicly attested so far to include the Aspeed USB gadget code implicated by CVE‑2025‑37881, but that attestation is product‑scoped and time‑boxed — it is not a technical guarantee that other Microsoft products do not contain the same upstream code. Any Microsoft product that ships a Linux kernel (or kernel modules) which include the Aspeed vHub driver could carry the same defect until it’s verified and patched. Microsoft has said it will update CVE/VEX/CSAF mappings if it finds additional affected products.Why this nuance matters for defenders and asset owners
Supply‑chain and inventory realities
- Large vendors ship many different kernel builds across distributions, cloud images, appliance firmware, container base images, virtual machine images, and embedded devices. An upstream kernel change can appear in many downstream artifacts at different times.
- A single upstream fix (two lines of defensive code, in this case) may be cherry‑picked into stable branches quickly — but only if each downstream artifact’s maintainer applies the patch or rebases to a patched kernel.
- Public product attestations (like MSRC’s Azure Linux note) accelerate remediation in the product they name, but they do not remove the need for independent inventory and verification in adjacent artifacts (for example, a Microsoft service that embeds a custom kernel, a device firmware image produced under a Microsoft brand, or the Microsoft‑maintained WSL kernel).
Real‑world implications of a kernel NULL dereference
- The most likely outcome if the vulnerable code is reached is a kernel oops / panic or a local denial‑of‑service, not silent data theft.
- Environments where untrusted or low‑privilege users can interact with USB gadget code or device initialization — development hosts, certain server BMCs, system management subsystems, or devices exposing virtual gadgets — are the most relevant attack surface.
- In cloud contexts, a guest kernel crash may disrupt a VM or container; if a product contains the vulnerable kernel and it runs untrusted workloads, the availability impact must be considered. Vendor attestations narrow the scope of concern but do not eliminate the need for checks across all artifacts that ship kernels.
Practical guidance: how to determine whether your Microsoft artifacts are affected
Below are concrete, repeatable steps for security and operations teams to identify presence, exposure, and remediation status.1. Inventory and prioritize
- Treat the MSRC Azure Linux attestation as high priority for Azure Linux images — plan to apply vendor kernel updates as soon as they’re available.
- For other Microsoft artifacts (WSL2, Azure Marketplace images, AKS node images, IoT/embedded offerings, appliance images), assume “not yet checked” rather than “not affected” until you confirm.
- Create a short candidate list:
- Any artifact that runs a Linux kernel built from upstream sources (or vendor kernels) where CONFIG_USB_ASPEED_VHUB could be enabled.
- Microsoft‑provided kernels (for example WSL2’s kernel image) and any VM/container images from Microsoft that include a full kernel.
2. Check running systems (commands to run)
Run these checks on systems you manage to detect whether the Aspeed vHub driver is present and whether the kernel version contains the patched commit:- Check for driver module or built‑in config:
- Check kernel config:
- zgrep CONFIG_USB_ASPEED_VHUB /boot/config-$(uname -r) || [ -f /proc/config.gz ] && zgrep CONFIG_USB_ASPEED_VHUB /proc/config.gz
- Look for module:
- modinfo aspeed-vhub 2>/dev/null || modinfo aspeed_vhub 2>/dev/null
- Check loaded modules:
- lsmod | grep -i aspeed
- Search installed module tree:
- find /lib/modules/$(uname -r) -type f -name 'aspeed' -print
- Confirm kernel patch presence:
- Query your distribution’s security tracker for CVE‑2025‑37881 and the corresponding kernel package updates (most distros list fixed kernel versions and advisory numbers).
- If you maintain custom kernels, search the kernel source tree for the ast_vhub_init_dev() patch; upstream commit messages and patch text are available from kernel mailing lists and git logs.
3. For Microsoft‑provided artifacts
- Azure Linux: follow Microsoft’s Azure Linux update channel and apply the kernel updates Microsoft publishes for the distribution as part of the advisory.
- WSL2: if you rely on the Microsoft‑provided WSL2 kernel, check the WSL release notes and kernel package that Microsoft distributes; if WSL uses a kernel image built from upstream source with CONFIG_USB_ASPEED_VHUB enabled, treat it as potentially affected until Microsoft attests otherwise.
- AKS / Marketplace images: verify the exact image SKU in use — vendor images may differ across regions/versions. Microsoft’s commitment to publish CSAF/VEX mappings means MSRC is gradually making these inventories machine‑readable; track those mappings and subscribe to MSRC updates.
4. Remediation and mitigation
- Primary remediation: install the vendor patch or update to a kernel version where the fix is applied.
- Upstream commits were posted to the kernel trees and released into stable branches; vendor kernels such as Ubuntu, Debian, SUSE, Oracle Linux, Amazon Linux and others issued advisories and kernel package fixes. Check your distribution advisory pages (NVD/Ubuntu/Debian/SUSE/ALAS) for the exact package versions that include the patch.
- Short‑term mitigations if you cannot patch immediately:
- Restrict untrusted local access to systems with the vulnerable kernel (reduce the pool of users who can trigger the gadget initialization).
- Limit USB gadget exposure where feasible (e.g., block gadget device nodes in untrusted containers).
- Monitor for kernel oops/panic events in your logs and escalate unexpected kernel crashes for forensic review.
Cross‑checking and verification: what I looked at to validate claims
To ensure technical accuracy I cross‑checked:- The upstream kernel patch and kernel‑mailing‑list posts showing the exact code change adding a NULL check to ast_vhub_init_dev(). Those patches were accepted into stable series and are visible in the kernel mailing lists and patch archives.
- Multiple vendor security trackers and advisories (NVD, Ubuntu, Debian, SUSE, Amazon Linux and Oracle) that record the CVE description and list affected/fixed kernel package lines and distribution statuses. These confirm the vulnerability’s scope, severity, and that multiple distributions have tracked and patched it.
- Microsoft’s MSRC advisory note and the company’s public statement about CSAF/VEX attestations and its commitment to update product mappings if additional Microsoft artifacts are found to be carriers. That MSRC wording is the basis of the user’s question and is central to the analysis here.
- Community and forum analysis that explains the difference between a product‑scoped attestation and a statement of exclusivity, which is critical to interpreting Microsoft’s wording safely.
Risk analysis: strengths, residual risks and recommended posture
Strengths (what’s reassuring)
- The fix is minimal and preventive: inserting a NULL check is a small, low‑risk change that is unlikely to cause regressions.
- Upstream maintainers merged the change into multiple stable kernel branches, and multiple distribution vendors recorded the CVE and published or planned fixes, which speeds downstream remediation.
- Microsoft’s public attestation for Azure Linux is transparent and machine‑readable VEX/CSAF mapping is being rolled out; that increases traceability for administrators using Azure Li.ph](https://archive.ph/2025.12.07-18532...ulnerability/CVE-2024-23848?utm_source=openai))
Residual risks (what to watch for)
- Inventory gaps: the principal operational risk is not knowing which artifacts ship the vulnerable driver. Vendors ship many kernel builds and a single upstream component can be present in multiple product artifacts; product attestation for one item does not prove other artifacts are clean.
- Embedded and custom kernels: appliances, firmware, or custom Microsoft images that embed or recompile kernels may or may not include the fix unless explicitly patched.
- Human process: teams that assume “Microsoft said only Azure Linux is affected” and treat that as a blanket assurance risk being blindsided if another Microsoft kernel artifact is later found to carry the code. Microsoft’s promise to update VEX/CSAF helps, but it is not a substitute for internal verification.
Recommended checklist for WindowsForum readers and enterprise teams
- If you run Azure Linux, prioritize and apply the kernel update(s) Microsoft publishes for the distribution.
- For other Microsoft artifacts (WSL2 kernel, Azure Marketplace images, AKS node images, Microsoft‑distributed virtual appliances), perform explicit inventory checks — search kernel config, modules and package versions — rather than relying on absence of public attestations.
- For all Linux hosts (Microsoft‑provided or otherwise), run the detection commands in the “check running systems” section and consult your distribution’s CVE advisory to confirm whether the kernel package includes the fix.
- If you operate environments where untrusted local users exist, harden access control and logging to detect and mitigate kernel crashes until patches can be applied.
- Subscribe to your distribution security tracker and to Microsoft’s MSRC updates / CSAF/VEX feed so you receive automated notices when Microsoft expands product mappings.
Final assessment
CVE‑2025‑37881 is a real but low‑complexity kernel robustness bug that was fixed upstream with a minimal defensive change. Microsoft’s statement that “Azure Linux includes this open‑source library and is therefore potentially affected” is an accurate and useful inventory result for Azure Linux images, and Microsoft has formally committed to publishing machine‑readable VEX/CSAF attestations and to update mappings if other Microsoft products are later found to include the same upstream component. However, that wording should not be read as an exclusivity guarantee. Any Microsoft product that ships a Linux kernel (or a kernel module tree that includes the Aspeed vHub driver) remains a candidate for exposure until it has been individually inventoried and declared Not Affected or patched. Operators should treat unattested Microsoft artifacts as “not yet checked” and follow the verification and remediation steps above.The immediate operational work is straightforward: inventory, patch, and monitor. The strategic work is organizational: keep SBOMs, machine‑readable attestations, and vendor advisories synchronized with your asset inventory so product‑scoped statements speed remediation rather than create false reassurance.
Source: MSRC Security Update Guide - Microsoft Security Response Center