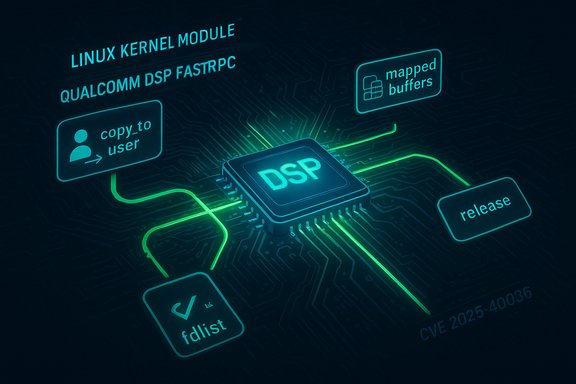
The Linux kernel received a targeted fix for a resource‑management bug in the FastRPC driver after maintainers discovered a path in fastrpc_put_args that could return early on copy_to_user failure without releasing mapped buffers, potentially leaking mapping references and exhausting kernel resources.
FastRPC is a miscellaneous kernel driver used primarily on platforms with Qualcomm DSPs to implement fast remote procedure call semantics between the host CPU and a digital signal processor. The recently assigned identifier CVE‑2025‑40036 records a small but important correctness fix: when copy_to_user fails inside fastrpc_put_args, the code previously returned early without cleaning up an fdlist that the DSP may have updated, leaving mapped buffers referenced and preventing their release. The upstream remedy redirects the failure path to a centralized cleanup sequence so all mapped buffers are released before returning. This is a classic example of a local kernel resource‑management bug: not an immediate remote code‑execution (RCE) problem, but one that can cause resource exhaustion, subtle stability regressions, and in some environments — when combined with other primitives — contribute to more serious compromises. The maintenance patch is small, surgical, and has been merged into the stable trees and distribution backports.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
FastRPC is a miscellaneous kernel driver used primarily on platforms with Qualcomm DSPs to implement fast remote procedure call semantics between the host CPU and a digital signal processor. The recently assigned identifier CVE‑2025‑40036 records a small but important correctness fix: when copy_to_user fails inside fastrpc_put_args, the code previously returned early without cleaning up an fdlist that the DSP may have updated, leaving mapped buffers referenced and preventing their release. The upstream remedy redirects the failure path to a centralized cleanup sequence so all mapped buffers are released before returning. This is a classic example of a local kernel resource‑management bug: not an immediate remote code‑execution (RCE) problem, but one that can cause resource exhaustion, subtle stability regressions, and in some environments — when combined with other primitives — contribute to more serious compromises. The maintenance patch is small, surgical, and has been merged into the stable trees and distribution backports. What the vulnerability is (technical summary)
- The vulnerable function: fastrpc_put_args in drivers/misc/fastrpc.c.
- The failing call: copy_to_user invoked when copying argument buffers from kernel to user space representations (or vice versa depending on context).
- The root cause: on a copy_to_user failure the function returned immediately without executing cleanup code that iterates the fdlist (an array of mapped buffer descriptors updated by the DSP), so mapped pages or map references could remain held.
- The impact: a map leak — i.e., kernel resources (mappings/fdlist entries) are not released — which can lead to memory/resource exhaustion or long‑running leaks that destabilize systems or drivers relying on finite mapping tables.
- The fix: allocate and use a local return-status variable, and on copy_to_user failure jump to a cleanup label that releases all mapped buffers before returning the failure code to caller. That ensures consistent cleanup regardless of intermediate failures.
Why this matters: practical impact and attack model
At first glance this is not a sensational CVE — no immediate unauthenticated remote RCE was reported — but the operational and security implications are non‑trivial for certain environments.- Local attack vector: exploitation requires the ability to interact with the FastRPC device interface, which is typically local (processes on the host interacting with the driver). In multi‑tenant systems, CI runners, container hosts, or devices where untrusted code can access device ioctls, this amounts to an attacker‑controllable local interface.
- Resource exhaustion & denial‑of‑service: repeated triggering of the failing path can accumulate leaked mappings until a resource limit is hit — this can crash or hang processes, provoke oopses, or disable the driver, producing denial‑of‑service for DSP‑dependent workloads.
- Chaining risk: information‑leaks and resource faults are commonly used as stepping stones in exploit chains. A local leak combined with heap grooming, timing windows, or other driver bugs can increase the chance of creating a more powerful primitive such as arbitrary memory read/write. While there is no public proof‑of‑concept converting this specific leak into an escalation vector at time of publication, defenders should treat local kernel faults as high‑value primitives for attackers with a foothold.
The upstream fix and verification
The kernel patch was authored and submitted as a stable fix; it was reviewed and signed off by maintainers and then merged into the stable release branches. The key behavioral change is straightforward: detour failing copy_to_user outcomes to a dedicated cleanup label that iterates the fdlist and calls the map‑release helper for each mapped entry, then return the previously captured error code. This eliminates the early‑return leak path. The change is present in multiple stable commits and has been included in the kernel stable patch series. Independent vulnerability databases (NVD/OSV/CVEdetails and other trackers) recorded the CVE description and referenced the stable kernel commits as the authoritative fix set. Those sources summarize the same root cause and remediation steps — a good signal that the upstream description, patch intent, and distribution mapping are consistent across independent trackers.Patching and mitigation guidance (operational playbook)
Patching kernel code requires care and testing. Follow this prioritized runbook when addressing CVE‑2025‑40036:- Inventory
- Identify hosts running kernels that include the FastRPC driver (check for drivers/misc/fastrpc existence).
- For each host, capture uname -r, kernel config (zcat /proc/config.gz or your distribution’s package info), and whether the DSP/Fastrpc device is used in production workloads.
- Map to upstream/stable commits
- Confirm whether your kernel package contains the stable commit(s) that implement the fix (the stable commit IDs are present in kernel changelogs and the stable patch series).
- If you build kernels in‑house, incorporate the upstream commit into your branch and recompile with your configuration.
- Stage and test
- Apply the updated kernel or vendor package to a small pilot group that exercises DSP workloads.
- Validate DSP functionality, device ioctls, and any vendor binary components that depend on the FastRPC interactions.
- Monitor kernel logs for regression traces and ensure map release paths are exercised in both success and failure cases.
- Roll out
- Roll out in waves from low‑risk to high‑risk hosts.
- For embedded or OEM devices, coordinate with the vendor for official images; if the vendor cannot provide updates promptly, isolate or restrict access to the device until a vendor image is available.
- Monitoring and compensations
- Add kernel log alerts for repeated map allocations, warnings about unreleased mappings, or unexpected fdlist sizes.
- Use resource controls and limits to reduce exposure: restrict which processes can open the FastRPC device, apply strict SELinux/LSM policies around device access, and limit untrusted code execution privileges on hosts that expose device ioctls.
Detection and hunting recommendations
Because this bug is a cleanup leak rather than an immediate crash or code‑execution bug, detection should focus on abnormal resource usage and error traces:- Kernel logs: search for error traces around the fastrpc driver or unexpected return codes from fastrpc_put_args. Look for messages indicating resource limits or map allocations not being freed.
- Telemetry: instrument kernel memory and mapping metrics where possible. Sudden, sustained growth in mapped buffers or mapping table usage tied to processes interacting with the DSP device is a signal.
- Behavior: repeated failures in user space that interact with the fastrpc device (failed copy_to_user sequences) correlated with growing fdlist entries indicate the leak path.
- EDR/host telemetry: flag processes that repeatedly open or ioctl the FastRPC device and then exit without releasing resources. Add anomaly detection for processes that perform many map operations on device files.
Risk analysis — strengths of the fix and remaining caveats
Strengths- Surgical and low‑regression: the upstream change is minimal and preserves intended functionality while improving error‑path correctness. This reduces the chance of unintended side‑effects and eases backports.
- Upstream and tracker agreement: multiple independent trackers and stable commit streams document the same change and commit IDs, improving confidence that the patch addresses the exact code path described.
- Clear remediation: unlike some VM or protocol bugs that require architectural changes, this one is a straightforward error‑path cleanup that can be backported easily by distribution kernel maintainers.
- Vendor lag for embedded/OEM kernels: devices that ship with vendor‑provided kernels (especially Android OEM kernels or appliance images) can lag upstream changes. These images may incorporate their own kernel versions or diverging drivers and might not receive timely backports. Operators should coordinate with vendors and apply compensating controls if immediate updates are not available.
- Local attack vector still meaningful: because the attack vector is local, any service that permits untrusted code execution or guest access to device interfaces (for example, build agents, CI runners, or container hosts with device passthrough) remains exposed until patched. Treat such hosts as high priority for the update.
- No public PoC ≠ no exploitability: there is no public PoC that demonstrates conversion of this leak into a full privilege escalation as of the upstream patch notes, but resource leaks and memory mismanagement are frequently used in chained exploits. Maintain defensive posture and patch promptly.
- There is no credible public evidence that CVE‑2025‑40036 has been used in targeted or opportunistic in‑the‑wild exploit campaigns at the time the kernel patch was merged. If evidence of exploitation surfaces later, that timeline should be treated separately and defenders should re‑prioritize accordingly.
For vendors and maintainers: best practices and backport guidance
For distribution and OEM kernel maintainers, the recommended approach is:- Apply the upstream stable commit(s) to the vendor kernel branch, honoring any local driver changes and preserving ABI/compatibility layers.
- Ensure regression tests for RPC/fastRPC and DSP interactions run as part of the kernel CI pipeline to capture functional regressions early.
- Where possible, publish a clear advisory mapping the affected upstream commit IDs to vendor kernel package versions and provide explicit package builds for customers.
- Communicate timelines and mitigations clearly: if a vendor image cannot be updated in the short term, publish configuration or isolation guidance to protect users (for example, disabling device access by unprivileged users or using LSM constraints).
Conclusion: how operators should treat CVE‑2025‑40036
CVE‑2025‑40036 is a correctness and resource‑management vulnerability in the FastRPC kernel driver that is fixed by redirecting error paths to a cleanup routine. The fix is tiny, low‑risk, and already merged into stable kernel branches. However, the practical security risk depends on your environment:- High priority: multi‑tenant hosts, CI/build agents, development platforms that allow untrusted device interactions, and any embedded/OEM images where patch cadence is uncertain.
- Medium priority: single‑user desktops and servers where FastRPC is present but device access is restricted.
- Low priority: hosts that do not include the fastrpc driver or do not expose the device to untrusted processes.
- Inventory kernels and confirm whether your package contains the stable commits that implement the fix.
- Apply the updated kernel or vendor patch, stage and test DSP workloads, and then roll out in waves.
- If vendor updates are not immediately available for embedded devices, isolate, restrict device access, or use LSM/AppArmor/SELinux rules to prevent untrusted processes from opening the FastRPC device.
- Monitor kernel logs and mapping resource metrics for anomalous growth and apply the detection rules described above.
Source: MSRC Security Update Guide - Microsoft Security Response Center