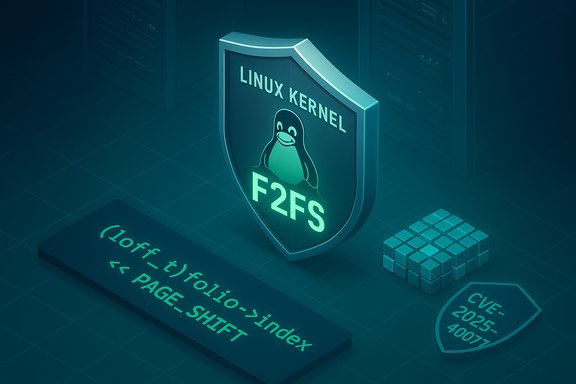
The Linux kernel has been assigned CVE‑2025‑40077 for a narrowly scoped arithmetic fix in the F2FS filesystem: a single-line defensive cast (casting folio->index to loff_t before shifting) prevents a left‑shift arithmetic overflow that could otherwise produce incorrect offsets during compressed‑cluster truncation. The upstream patch is intentionally minimal, landed in stable trees, and has been picked up by the kernel stable releases; operators should treat this as a low‑surface, high‑value patch to apply quickly on systems that use F2FS or run kernels compiled with F2FS support.
F2FS (Flash-Friendly File System) is used across Linux distributions and in many embedded and mobile devices as an optimized filesystem for flash-based media. The newly published CVE‑2025‑40077 describes a correctness/overflow fix inside fs/f2fs/compress.c: when computing a byte offset from a folio index, the code performed a left shift of folio->index without an explicit cast to a wide signed integer type, which can overflow if folio->index is stored in a narrower or unsigned type. The upstream remedy is simple and surgical: cast folio->index to loff_t before applying the left shift, ensuring the arithmetic is done in an appropriately sized signed type. Why this mattered: left‑shift operations are not benign in kernel code when applied to values whose type width or signedness hasn't been considered. An overflow at this arithmetic point can produce a miscomputed start offset for a folio, which in turn may lead to out‑of‑range memory operations, driver assertions, or kernel oopses. Because this code runs in kernel context, even small arithmetic mistakes can produce availability-impacting faults; the upstream maintainers chose a small, low‑risk cast to fix the condition without altering higher‑level semantics.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
F2FS (Flash-Friendly File System) is used across Linux distributions and in many embedded and mobile devices as an optimized filesystem for flash-based media. The newly published CVE‑2025‑40077 describes a correctness/overflow fix inside fs/f2fs/compress.c: when computing a byte offset from a folio index, the code performed a left shift of folio->index without an explicit cast to a wide signed integer type, which can overflow if folio->index is stored in a narrower or unsigned type. The upstream remedy is simple and surgical: cast folio->index to loff_t before applying the left shift, ensuring the arithmetic is done in an appropriately sized signed type. Why this mattered: left‑shift operations are not benign in kernel code when applied to values whose type width or signedness hasn't been considered. An overflow at this arithmetic point can produce a miscomputed start offset for a folio, which in turn may lead to out‑of‑range memory operations, driver assertions, or kernel oopses. Because this code runs in kernel context, even small arithmetic mistakes can produce availability-impacting faults; the upstream maintainers chose a small, low‑risk cast to fix the condition without altering higher‑level semantics. What changed: the patch and its intent
The technical delta, in plain terms
The patch alters one line in fs/f2fs/compress.c inside the function that truncates partial clusters on compressed inodes. The original code computed the folio start offset like this:- loff_t start = folio->index << PAGE_SHIFT;
- loff_t start = (loff_t)folio->index << PAGE_SHIFT;
Why a cast, not broader refactor?
Kernel maintainers prefer surgical fixes for localized arithmetic mistakes: a cast is the smallest change that preserves correct behavior for valid inputs while removing a corner-case arithmetic wrap. This is a standard defensive‑coding pattern in the kernel tree — when an expression mixes types of different widths, an explicit promotion clarifies intent and prevents implicit, platform-dependent wrap or truncation. The patch avoids changing the logic of cluster truncation while eliminating an exploitable or crash‑provoking arithmetic corner case.Impact assessment: who is affected and how dangerous is it?
Affected population
- Any Linux kernel build that includes the vulnerable commit range in fs/f2fs/compress.c is potentially affected. OSV and the NVD record identify the upstream commits that introduced and fixed the code, which makes it possible to map affected versions precisely.
- Commonly impacted installations are desktop and server systems that mount F2FS partitions, as well as Android devices or embedded appliances that use vendor kernels built with F2FS enabled.
- Vendor kernels and embedded forks (OEM Android kernels, appliance images) are the highest‑risk targets in practice because vendor patch cycles and backport policies vary. Embedded images that rarely receive updates may remain vulnerable longer.
Exploitability and typical impact
- The change fixes an arithmetic overflow that could result in incorrect offsets. The dominant operational outcome for this class of error is availability: kernel oops, driver failure, or filesystem inconsistency leading to hangs or crashes rather than an obvious remote code execution vector.
- There is no public, confirmed proof‑of‑concept exploit published as of the initial CVE listing and upstream commit; watchers across vulnerability feeds show no active exploit campaigns tied to this CVE at publication time. Treat claims of weaponization as unverified until independent PoCs are published.
- Severity estimates vary: some commercial trackers (which derive CVSS scores heuristically) assign moderate to high numeric values, but NVD initially describes the issue as a resolved kernel arithmetic bug without a detailed CVSS in its first publication. Use vendor advisories and distribution trackers to decide local priority.
Attack model (realistic)
- Local actor: the vulnerability is not a remote network service bug that attackers can trivially reach from the network. An attacker needs the ability to interact with the filesystem on the host, e.g., by mounting or writing crafted content that triggers the truncate path, or by running code on the host that exercises F2FS compressed inode truncation.
- Multi‑tenant risk: in cloud or shared hosting, a local fault that can crash the host kernel is high‑impact because it affects all tenants. For such environments the priority for the patch should be elevated.
Timeline and traceability
- Patch submission: the upstream patch was posted to the LKML/f2fs patchwork thread in early August 2025 by the maintainer (Chao Yu), with a concise commit message describing the necessary cast and referencing the commit that introduced partial truncation support.
- Stable tree inclusion: the fix was cherry‑picked into the stable kernel trees and appeared in stable kernel update batches (the stable patch mailbox and stable‑review threads show inclusion into 6.17 and other stable branches).
- CVE assignment and public listing: NVD published the CVE record and description on October 28, 2025, listing the kernel.org stable commit references as authoritative proof of the fix. OSV, CVE aggregators, and vulnerability feeds mirrored the record shortly thereafter.
Practical remediation and mitigation steps
The definitive remediation is to install a kernel update that contains the upstream fix and reboot the host into that patched kernel. The following is a practical, prioritized checklist for administrators.Immediate 0–24 hour actions
- Inventory hosts that use F2FS or may mount F2FS partitions:
- Check which filesystems are in use: cat /etc/fstab and findmnt -t f2fs
- Confirm kernel support: grep f2fs /proc/filesystems and lsmod | grep f2fs
- Determine current kernel versions: uname -r
- Check vendor advisories and your package manager for kernel packages that mention CVE‑2025‑40077, or that reference the upstream commit IDs that fix the issue. Distribution security trackers will map the upstream commit to vendor package versions.
- Schedule a tested kernel update and reboot for hosts that mount F2FS, prioritizing multi‑tenant and production systems.
If you cannot patch immediately (short‑term mitigations)
- Prevent untrusted users or processes from mounting or manipulating F2FS images: restrict who can run mount or use loopback devices.
- Limit exposure for systems that process untrusted images: move image‑processing workloads to isolated hosts without F2FS support until patched.
- Increase monitoring: add alerts for unusual kernel oops or F2FS trace messages in dmesg/journalctl that occur in high frequency. Operational telemetry is an effective guardrail until patches are applied.
Post‑patch validation
- Confirm kernel changelog or package release notes reference the CVE or the upstream commit ID.
- Reboot and validate the host: check for F2FS mount behavior, run filesystem operations that exercise compressed cluster truncation in test environments if feasible, and verify that kernel logs no longer show the old error path or oopses.
Detection, hunting, and incident response
Because the bug is arithmetic/correctness‑oriented, detection should focus on operational symptoms rather than signatures:- Hunt for recent kernel oops/panic entries that reference F2FS code paths (fs/f2fs/compress.c) or stack traces containing compress.c symbols.
- Alert on repeated truncated‑cluster related messages or on repeated folio‑related warnings in kernel logs.
- If you suspect an in‑the‑wild attempt to provoke the condition, preserve kernel logs and VM/host memory snapshots before rebooting for forensic analysis. A post‑crash capture will be necessary to determine whether the crash was accidental or the result of deliberate triggering.
Risk analysis: strengths of the fix and residual caveats
Strengths
- Minimal blast radius: the fix is one line (a cast) that does not change the algorithm’s semantics for valid inputs. That reduces regression probability and makes the change safe for backporting across many stable kernel branches.
- Fast to backport: distribution maintainers can easily apply the small change to older stable releases without wholesale redesign of the compression/truncation logic. OSV and stable review threads indicate the fix appeared in stable trees promptly.
Residual risks and caveats
- Distribution and vendor lag: not every vendor kernel or embedded fork will pick up the backport at the same time. Appliance images and OEM Android kernels can remain vulnerable until the vendor issues an update. Administrators must confirm vendor advisories rather than assume the upstream fix implies immediate coverage.
- Local attack vector persists until patched: because the vulnerability is addressable by local interactions, systems that allow untrusted code execution or file mounting are exposed until they receive the patch.
- Severity ambiguity: initial CVE records may omit a fully validated CVSS score. Some commercial trackers supply numerical scores (for example, Tenable lists an estimated severity), but these are vendor estimates; presume the NVD/OSV authoritative descriptions and prioritize based on your operational exposure.
Recommended playbook (concise, operational)
- Identify — Find hosts with F2FS mounts and kernel builds that predate the stable fix.
- Commands: uname -r; findmnt -t f2fs; grep f2fs /proc/filesystems; lsmod | grep f2fs
- Map — Check your distro security tracker for CVE‑2025‑40077 package mappings; request vendor guidance for OEM devices.
- Patch — Stage and deploy kernel updates from your distribution or vendor; reboot hosts into the patched kernel.
- Validate — Confirm the kernel changelog includes the fix or the referenced upstream commit IDs; run functional smoke tests for storage and filesystem behavior.
- Monitor — Add kernel log alerts for F2FS crash signatures and track post‑patch stability metrics.
What we verified and what remains unverified
- Verified:
- The upstream patch and commit text that insert the cast in fs/f2fs/compress.c are publicly visible in the kernel mailing lists and stable commit history.
- NVD and OSV list CVE‑2025‑40077 with the same commit references and the short description that the fix casts folio->index to loff_t to avoid overflow.
- Distribution‑level propagation is the canonical remediation path: maintainers will backport the fix into distribution kernels and publish advisories.
- Claims to treat with caution:
- Any assertion that CVE‑2025‑40077 enables remote code execution or has been exploited in the wild is not corroborated by authoritative trackers at the time of writing. No public PoC or active exploit campaign tied specifically to this CVE has been validated in the public record. Treat such claims as unverified until researchers publish technical confirmation.
Broader lessons for operators and kernel reviewers
- Small arithmetic errors matter: left shifts, multiplications, and mixed‑width arithmetic in kernel code are perennial sources of correctness and security issues. The fix here is small but necessary because kernel arithmetic mistakes are often catastrophic in practice.
- Surgical fixes are preferable for safety: maintainers responsibly applied the smallest change that addresses the root cause without altering intended behavior for valid inputs. That pattern reduces regression risk and speeds distribution backports.
- Embedded and vendor kernels are the weakest link: organizations should inventory vendor images and push for transparent patch schedules from OEMs; fleet owners must treat vendor kernels as a critical dependency for operational security.
Conclusion
CVE‑2025‑40077 is a focused correctness fix in the F2FS compression truncation code that resolves a left‑shift overflow by casting folio->index to a suitably wide type before arithmetic. The remedy is minimal and low risk, and upstream/stable kernel trees already include the change; the practical action for administrators is straightforward: identify systems that run F2FS or vendor kernels that may include the vulnerable code, apply vendor/distribution kernel updates that include the fix, and reboot into the patched kernel. Until those updates are applied, hosts that allow local unprivileged filesystem interactions or that run untrusted workloads remain exposed to potential kernel crashes or instability. The fix demonstrates how tiny, well‑targeted patches can remove outsized operational risk when they are quickly applied and properly validated.Source: MSRC Security Update Guide - Microsoft Security Response Center