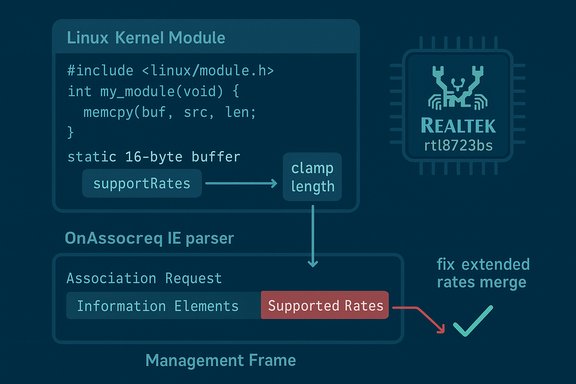
A new Linux kernel CVE has been published that fixes a straightforward—but dangerous—stack buffer overflow in the Realtek staging driver rtl8723bs; the bug allows a malformed wireless Association Request to overflow a 16‑byte stack buffer when parsing the Supported Rates Information Element (IE), and the fix clamps IE lengths and tightens bounds checks to prevent kernel stack corruption.
Staging drivers in the Linux kernel are an important development area: they let hardware vendors and community contributors land device support quickly even while code quality and style are improved over time. The rtl8723bs driver is a Realtek Wi‑Fi driver maintained in the kernel's staging tree; it implements management‑frame parsing for AP (hostapd) and client roles. Recently a pair of IE‑parsing defects were merged into the stable trees that together closed several out‑of‑bounds and overflow problems discovered in the rtl8723bs staging driver. The specific record assigned CVE‑2025‑68255 describes a stack buffer overflow in the OnAssocReq IE parser where the driver used the Supported Rates IE length from an incoming Association Request frame as the length argument to memcpy without clamping it to the destination buffer size. The vulnerable stack buffer (supportRate) is 16 bytes; any advertised IE length greater than 16 bytes can produce a stack overflow. The upstream remedy clamps the IE length before copying and adjusts the Extended Supported Rates merge logic to avoid a second possible overflow.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
Staging drivers in the Linux kernel are an important development area: they let hardware vendors and community contributors land device support quickly even while code quality and style are improved over time. The rtl8723bs driver is a Realtek Wi‑Fi driver maintained in the kernel's staging tree; it implements management‑frame parsing for AP (hostapd) and client roles. Recently a pair of IE‑parsing defects were merged into the stable trees that together closed several out‑of‑bounds and overflow problems discovered in the rtl8723bs staging driver. The specific record assigned CVE‑2025‑68255 describes a stack buffer overflow in the OnAssocReq IE parser where the driver used the Supported Rates IE length from an incoming Association Request frame as the length argument to memcpy without clamping it to the destination buffer size. The vulnerable stack buffer (supportRate) is 16 bytes; any advertised IE length greater than 16 bytes can produce a stack overflow. The upstream remedy clamps the IE length before copying and adjusts the Extended Supported Rates merge logic to avoid a second possible overflow. What the vulnerability is — technical summary
- Component: staging: rtl8723bs (Realtek 8723b(s) Wi‑Fi driver in the kernel staging tree).
- Functionality affected: parsing of Information Elements (IEs) in Association Request and Beacon frames, specifically the Supported Rates and Extended Supported Rates IEs.
- Root cause: the code used the untrusted IE length directly as the memcpy length when copying into a fixed-size 16‑byte stack buffer (supportRate), and a second bounds-check during Extended Supported Rates merging was off by one or otherwise incorrect.
- Impact: stack buffer overflow (kernel stack corruption) which may cause immediate kernel instability (oops/panic) and, in pathological cases or with complex exploitation chains, could increase the theoretical risk of further code‑execution primitives—although public reporting to date classifies this as an availability/memory‑corruption issue rather than a trivially exploitable RCE.
Why the bug matters (operational risk)
Even when a kernel bug does not directly yield remote code execution, the practical consequences can be severe in real environments:- Availability impact: a stack overflow in kernel code frequently produces oopses and reboots. For embedded APs, routers, IoT gateways, or Raspberry Pi devices acting as access points, a single malformed frame could knock the device offline. That is especially critical for infrastructure that relies on wireless control planes or guest networks.
- Long tail of exposure: staging drivers and vendor kernels are often present in embedded and OEM images that lag upstream patches. These devices commonly run for years without kernel updates, lengthening the exposure window.
- Attack model simplicity: no local user account is required—an unauthenticated wireless client within radio range is sufficient to trigger the condition, making testing and exploitation steps comparatively low friction for a motivated attacker with physical proximity.
- Potential for chaining: while there is no public proof‑of‑concept demonstrating reliable privilege escalation or RCE from this specific overflow, stack corruptions in kernel‑space are sensitive; in some contexts they can be combined with other primitives (e.g., information disclosure, other memory errors, or kernel config idiosyncrasies) to widen impact. Operators should treat memory‑safety kernel bugs seriously even when initial scoring emphasizes availability.
What was changed in the kernel (patch mechanics)
The upstream patches are intentionally minimal and defensive—this is the conventional approach for memory‑safety fixes in trusted kernel subsystems:- Clamp IE length: before copying the Supported Rates IE into the 16‑byte supportRate local buffer, the code now clamps ie_len to the destination buffer size so that memcpy cannot be invoked with a length greater than the buffer capacity.
- Fix Extended Supported Rates merging bound check: the merge logic that appends Extended Supported Rates to the supported rate set contained an incorrect bounds check; the patch corrects that check so the code never reads or writes past the receive frame buffer or the destination arrays.
- Small, low‑risk modifications: the change is a short, clear defensive guard around untrusted on‑the‑air data; such fixes are easy to audit and backport into stable kernels and vendor trees with minimal regression risk.
Who is affected
- Any Linux system whose kernel includes the in‑tree staging rtl8723bs driver and the vulnerable code range. This includes:
- Embedded devices and SoC images that use Realtek 8723b(s) Wi‑Fi parts and ship vendor kernels with staging drivers.
- Single‑board computers (e.g., Raspberry Pi derivatives or similar boards) that rely on Broadcom/Realtek combo chips and include the rtl8723bs staging driver.
- Cloud or virtual appliances that intentionally attach or include Linux guest images with the vulnerable kernel (less common, but possible in custom images).
- Windows desktop and server systems are not directly affected by a Linux kernel driver CVE, though mixed environments with Linux guests or appliances in a Windows‑managed estate should still plan remediation for the Linux components.
How to determine exposure in your environment
- Inventory endpoints and devices that use Realtek rtl8723bs hardware or ship vendor kernels that include staging drivers.
- On Linux hosts, check whether the rtl8723bs module is present or built in:
- Run: uname -r to identify the running kernel.
- Check modules: lsmod | grep rtl8723bs
- Inspect kernel config (if available): zcat /proc/config.gz | grep RTL8723 or grep -i rtl8723bs /boot/config-$(uname -r)
- For embedded or vendor images, consult the vendor firmware change log and image build metadata to verify kernel commit versions or whether the vendor has shipped a backport.
- Monitor kernel logs (dmesg/journalctl -k) for OOPS traces containing rtl8723bs symbols or management-frame parsing functions—these lines are the strongest immediate indicators of exploit attempts or accidental malformed frames causing crashes.
Immediate mitigations and operational recommendations
If you cannot patch immediately, consider these compensations to reduce exposure and blast radius:- Avoid operating as an AP on vulnerable hosts: if the device is acting as an access point, consider disabling AP mode or hostapd until the kernel is patched, especially on devices exposed to untrusted wireless clients.
- Isolate wireless management: place the wireless management plane on a more restrictive radio or separate SSID with MAC filtering and client isolation where feasible.
- Block untrusted clients: at the network policy layer, reduce the set of clients that can associate—especially on guest networks or public hotspots.
- Disable or blacklist the rtl8723bs module on hosts where the driver can be unloaded and the wireless interface is not required:
- As root: echo "blacklist rtl8723bs" > /etc/modprobe.d/blacklist-rtl8723bs.conf
- If modular: modprobe -r rtl8723bs
- Note: blacklisting may remove wireless functionality; evaluate operational impact before applying broadly.
- Apply host hardening: enable kdump and kernel crash collection to capture artifacts for post‑mortem if a crash occurs; enable kernel lockdown and reduce unnecessary local services that might provide chaining primitives.
How to verify the fix and patching status
- Obtain the kernel package mapping from your vendor/distribution security advisory. OSV/NVD entries list references to the upstream commits and will be reflected in distribution changelogs. Search for the CVE ID (CVE‑2025‑68255) in your distro's security tracker.
- Check for the upstream commit in your kernel source (if you build custom kernels): use git log --grep="OnAssocReq" or git log --grep="rtl8723bs" against the stable/staging branches to confirm the specific fix commit is present.
- For packaged kernels, confirm the package changelog or vendor advisory explicitly lists the CVE or the upstream stable commit IDs before declaring a host remediated.
- After updating, reboot into the patched kernel and validate the running kernel version (uname -a) and loaded module list (lsmod) to ensure the new kernel is active.
Detection, hunting and telemetry suggestions
- Add host alerts for kernel OOPS and rtl8723bs‑related stack traces in system logs.
- Correlate wireless management‑frame activity (from hostapd or wireless driver debug logs) with kernel oops occurrences—repeated oopses coincident with Association Requests or Beacon processing suggest active attempted triggers.
- Enable KASAN (Kernel Address Sanitizer) in test/lab kernels if you operate a UAT environment for reproductions—KASAN makes memory errors much easier to diagnose for kernel developers.
- For network-level visibility, instrument access points with packet captures for suspicious management frames; look for extremely long Supported Rates or malformed IE lengths (values >16 for Supported Rates IE) in Association Requests. That pattern directly maps to the root cause described in the fix.
How kernel maintainers and vendors treated the fix (context & patterns)
Maintainers favored a conservative, surgical patch: clamp untrusted lengths, correct off‑by‑one checks, and preserve ABI and expected behavior elsewhere. This is the common and recommended pattern for kernel memory‑safety fixes because the changes are easy to review, low risk for regressions, and straightforward to backport into stable and vendor kernels. Historical kernel vulnerability remediation shows that small defensive checks and bounds clamping are preferred over large refactors for quickly mitigating exploitation risk while preserving compatibility.Security scoring and exploitability (practical note)
Public vulnerability trackers initially classify CVE‑2025‑68255 as a stack buffer overflow that is network‑accessible from the radio but requires proximity. Vendors and CVE/NVD records list the issue with standard memory‑corruption descriptors; CVSS and EPSS entries may be populated over the next days as distribution and vendor advisories publish package mappings and exploit telemetry (if any) appears. At publication time there is no widely available exploit proof‑of‑concept; the short remediation window makes proactive patching the recommended course of action.Concrete remediation checklist (operational playbook)
- Inventory: find devices that use rtl8723bs or that have the driver module loaded. Command: lsmod | grep rtl8723bs and check vendor device lists.
- Consult vendor/distro advisories: locate the package version that includes CVE‑2025‑68255. Prefer vendor-supplied kernel packages when available.
- Patch: install the updated kernel package that includes the upstream commits; schedule reboots and apply configuration management controls to enforce rollout.
- Validate: reboot into the patched kernel and confirm uname -r matches the fixed kernel package; check module lists and confirm stability under test workloads.
- Temporary mitigations: if immediate patching is impossible, disable AP mode, isolate the wireless management plane, or blacklist the rtl8723bs module with a plan to revert after patching.
- Post‑patch monitoring: continue to monitor kernel logs and wireless management traffic for anomalies for at least one week after remediation in production.
Final analysis — strengths and residual risks
The public response to CVE‑2025‑68255 demonstrates appropriate kernel‑engineering practice: small, auditable fixes that clamp untrusted inputs and correct boundary logic. That reduces the likelihood of regressions and accelerates vendor backports. The primary strengths of the fix are:- Surgical remediation that addresses the exact root causes without broad rewrites.
- Low regression risk, making backports to stable kernels straightforward.
- Clear detection indicators (IE length > 16 in Association Requests), aiding hunting and forensic work.
- Long‑tail exposure in embedded and OEM devices that seldom receive kernel updates—these devices may remain vulnerable for months or years unless the vendor supplies firmware/kernel updates.
- Local network attack surface: any public or guest Wi‑Fi where untrusted clients may associate is a practical attack surface that must be controlled.
- Potential undiscovered parsing issues: IE parsing is notoriously fraught; while this fix addresses the reported stack overflow and a merge‑bounds bug, adjacent code paths must still be audited, and operators should watch for follow‑on reports.
Conclusion
CVE‑2025‑68255 fixes a straightforward and dangerous stack buffer overflow in the rtl8723bs staging Wi‑Fi driver’s OnAssocReq IE parser by clamping IE lengths and tightening bounds checks—an appropriate, low‑risk patch that eliminates immediate stack corruption risk. Operators who run devices with Realtek rtl8723bs hardware or who ship vendor kernels that include the staging driver must prioritize kernel updates or apply compensating controls (disable AP mode, blacklist the module, or tighten client association policies) until patched kernels are deployed. Vigilance is essential because management‑frame parsing is a physical‑layer attack surface where unauthenticated, proximity‑based triggers can cause large operational impacts if left unresolved.Source: MSRC Security Update Guide - Microsoft Security Response Center