Microsoft’s CVE-2026-0390 is another reminder that Secure Boot is only as strong as the trust chain behind it. The vulnerability, described by Microsoft as a UEFI Secure Boot security feature bypass, affects the Windows Boot Loader and is framed as a local issue that could let an authorized attacker sidestep a security control during startup. In practical terms, that means the problem is not remote code execution in the classic sense, but rather a way to weaken one of the most important protections in modern PC firmware security. Because this class of flaw strikes at the boot process itself, it has outsized implications for enterprise fleets, endpoint hardening, and post-compromise persistence.
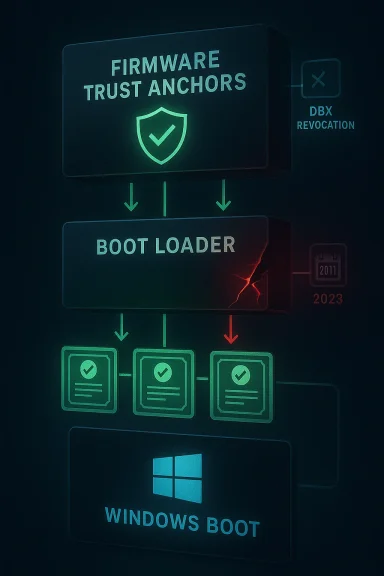
Secure Boot has become one of those technologies that most users never think about until something goes wrong. It is designed to ensure that only trusted, digitally signed boot components are allowed to execute before Windows starts, which helps block bootkits, rootkits, and tampering that would otherwise operate beneath the operating system. Microsoft’s own guidance repeatedly emphasizes that Secure Boot protects the early boot chain and that revocation data in DBX is the mechanism used to block known-bad loaders and policies.
That trust model matters because boot-level compromise is qualitatively different from ordinary malware infection. If an attacker can alter or subvert what runs before the OS, they can potentially disable code integrity, interfere with BitLocker validation, or gain persistence that survives reinstall attempts and evades many endpoint tools. Microsoft’s past Secure Boot advisories have described exactly those outcomes, including the ability to load test-signed code or bypass integrity validation for BitLocker and Device Encryption.
The industry has already lived through several major Secure Boot bypass cycles. Microsoft has patched and revoked vulnerable boot managers and policies in the past, and the lesson has been consistent: fixing the bug alone is often not enough if the vulnerable binary remains trusted somewhere in the chain. That is why revocation, not just patching, has become a core part of the Secure Boot response playbook.
The timing of CVE-2026-0390 also intersects with an important certificate transition. Microsoft says the long-lived Secure Boot certificates issued in 2011 begin expiring in June 2026 and run out by October 2026, which means devices must migrate to the newer 2023 certificates to keep receiving early-boot security updates. In other words, this is not just a vulnerability story; it is happening during a major trust-anchor refresh for the entire Windows Secure Boot ecosystem.
That makes the risk more strategic than tactical. Organizations that have treated Secure Boot as a one-time deployment checkbox are now facing a period in which certificate rollover, DBX maintenance, and firmware hygiene all matter at once. That combination is exactly where attackers like to look, because the operational complexity creates gaps that security teams may not notice until exploitation or boot failures appear.
The summary that circulated in Microsoft-focused security coverage describes the issue as a reliance on untrusted inputs in a security decision in Windows Boot Loader, allowing an authorized attacker to bypass a local security feature. That is the kind of language Microsoft has used before for boot-loader vulnerabilities where a maliciously crafted input, configuration, or on-disk object causes the loader to make the wrong trust decision. It suggests the flaw may live in validation logic, parsing logic, or a decision point that should have been hardened.
The issue also appears to be tied to the Windows Boot Loader, not a third-party shim or a random OEM boot app. That means the blast radius potentially extends across a large swath of Windows systems that rely on the same Microsoft boot trust infrastructure. Even when a flaw is local, a shared boot component can turn a single bug into a platform-wide concern.
The problem is compounded by the fact that UEFI firmware ecosystems are fragmented. Even when Microsoft issues a fix, the system may also need firmware updates, DBX updates, boot manager replacements, or certificate rollovers before the protection is complete. Microsoft has explicitly documented that devices unable to receive the new 2023 Secure Boot certificates will lose the ability to receive future early-boot security updates, which means the ecosystem has a built-in dependency on maintenance discipline.
Microsoft’s previous revocation stories also show why patching is not the end of the story. If vulnerable binaries remain signed and accepted, attackers can continue to use them even after the underlying code flaw is known. That is why DBX updates and certificate transitions matter as much as the CVE itself.
The risk is especially acute where BitLocker, Device Encryption, and compliance baselines depend on boot-chain trust. Microsoft has repeatedly noted that Secure Boot bypasses can interfere with integrity validation for those protections. That means the issue is not only about malware; it is also about the assumptions that make loss prevention, device attestation, and recovery workflows reliable.
There is also a reporting and detection challenge. Traditional EDR tools are strongest once the OS is running, but Secure Boot bypasses are designed to operate before those tools are in play. That means administrators need to rely more on firmware inventory, boot-event telemetry, compliance reports, and vendor guidance than on ordinary antivirus logic.
The practical consumer issue is whether the device receives updates consistently. Microsoft’s guidance makes clear that the aging 2011 certificates are being replaced, and systems that fail to migrate may lose the ability to accept future revocations and protections. That means consumers who ignore firmware and Windows updates may unknowingly be carrying a shrinking security margin.
There is also a psychological problem with Secure Boot issues: because they are invisible when everything is working, users underestimate their importance. The system boots, Windows loads, and nothing obviously looks broken. Yet the ability to trust that boot path is what underpins device encryption and higher-level protections.
This matters because expired certificates can freeze the ecosystem in place. If a device cannot receive the new trust material, then future DBX updates and boot-chain mitigations may no longer land correctly, leaving it more exposed to newly discovered boot-level bugs. Microsoft says devices without the updated certificates will continue to boot and function, but they will lose the ability to receive new early-boot protections.
The transition also creates potential compatibility issues, especially for older or custom-built systems. Microsoft’s guidance notes that devices manufactured since 2012 may have expiring versions of the certificates and need updates, which is a polite way of saying the installed base is broad and uneven. Broad, uneven fleets are where security timelines become operational projects rather than simple patches.
Microsoft’s response pattern has also become more mature. Instead of merely fixing the local flaw, the company has leaned on blacklisting and revocation to prevent the vulnerable boot artifact from being trusted again. That approach is essential because boot-chain attackers often reuse signed components as long as the ecosystem still accepts them.
The distinction is important because it changes how defenders should prioritize the bug. A traditional exploitable vulnerability often attracts attention because it is loud. A bypass vulnerability deserves attention because it quietly expands what other attacks can do. That multiplier effect is why these issues often age into major incident-response headaches.
The second concern is operational drift. Microsoft has made clear that certificate expiration in 2026 will limit the ability to apply future early-boot protections on devices that fail to migrate. That means organizations are not just patching a CVE; they are being asked to modernize a trust foundation under time pressure.
What matters now is execution. Microsoft can publish the fix, but OEMs, IT departments, cloud operators, and end users still have to carry it through to every machine that matters. That is often where security stories stop being technical and start being organizational, because the last mile is where old hardware, custom images, and delayed maintenance all come back into view.
In the end, CVE-2026-0390 is significant not because it is the loudest Windows bug of the month, but because it touches the trust machinery underneath everything else. Secure Boot failures are dangerous precisely when they are treated as niche problems, and the coming certificate expiration deadline ensures this one will have a life well beyond its initial patch cycle. If Microsoft, OEMs, and enterprise admins handle the transition carefully, the ecosystem can emerge stronger; if they do not, attackers will be waiting at the boot screen.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
Secure Boot has become one of those technologies that most users never think about until something goes wrong. It is designed to ensure that only trusted, digitally signed boot components are allowed to execute before Windows starts, which helps block bootkits, rootkits, and tampering that would otherwise operate beneath the operating system. Microsoft’s own guidance repeatedly emphasizes that Secure Boot protects the early boot chain and that revocation data in DBX is the mechanism used to block known-bad loaders and policies.That trust model matters because boot-level compromise is qualitatively different from ordinary malware infection. If an attacker can alter or subvert what runs before the OS, they can potentially disable code integrity, interfere with BitLocker validation, or gain persistence that survives reinstall attempts and evades many endpoint tools. Microsoft’s past Secure Boot advisories have described exactly those outcomes, including the ability to load test-signed code or bypass integrity validation for BitLocker and Device Encryption.
The industry has already lived through several major Secure Boot bypass cycles. Microsoft has patched and revoked vulnerable boot managers and policies in the past, and the lesson has been consistent: fixing the bug alone is often not enough if the vulnerable binary remains trusted somewhere in the chain. That is why revocation, not just patching, has become a core part of the Secure Boot response playbook.
The timing of CVE-2026-0390 also intersects with an important certificate transition. Microsoft says the long-lived Secure Boot certificates issued in 2011 begin expiring in June 2026 and run out by October 2026, which means devices must migrate to the newer 2023 certificates to keep receiving early-boot security updates. In other words, this is not just a vulnerability story; it is happening during a major trust-anchor refresh for the entire Windows Secure Boot ecosystem.
That makes the risk more strategic than tactical. Organizations that have treated Secure Boot as a one-time deployment checkbox are now facing a period in which certificate rollover, DBX maintenance, and firmware hygiene all matter at once. That combination is exactly where attackers like to look, because the operational complexity creates gaps that security teams may not notice until exploitation or boot failures appear.
What Microsoft Says About CVE-2026-0390
Microsoft’s update guide entry for CVE-2026-0390 identifies it as a UEFI Secure Boot Security Feature Bypass Vulnerability and classifies it under the security feature bypass category rather than remote execution or elevation of privilege. The wording matters: Microsoft is signaling that the flaw weakens a protection boundary instead of directly delivering code execution by itself. That distinction often translates into a lower CVSS-style urgency for some consumers, but a much higher strategic concern for defenders who understand boot-chain abuse.The summary that circulated in Microsoft-focused security coverage describes the issue as a reliance on untrusted inputs in a security decision in Windows Boot Loader, allowing an authorized attacker to bypass a local security feature. That is the kind of language Microsoft has used before for boot-loader vulnerabilities where a maliciously crafted input, configuration, or on-disk object causes the loader to make the wrong trust decision. It suggests the flaw may live in validation logic, parsing logic, or a decision point that should have been hardened.
Why the wording matters
The phrase “authorized attacker” is worth unpacking. In Microsoft vulnerability language, that usually means an attacker already has local access or elevated privileges, not that the vulnerability is exploitable from the internet. That makes this a post-compromise weapon, but a powerful one, because it can turn a foothold into durable boot-level persistence.The issue also appears to be tied to the Windows Boot Loader, not a third-party shim or a random OEM boot app. That means the blast radius potentially extends across a large swath of Windows systems that rely on the same Microsoft boot trust infrastructure. Even when a flaw is local, a shared boot component can turn a single bug into a platform-wide concern.
- The vulnerability is categorized as a security feature bypass.
- Microsoft’s description points to untrusted input in a boot-time security decision.
- The likely attacker model is local and authorized, not anonymous remote.
- The practical risk is boot-chain compromise, not just nuisance behavior.
- The real-world impact depends on whether revocation and update channels are current.
How Secure Boot Bypasses Usually Work
Secure Boot bypasses generally exploit a weakness in how the platform validates trust before the operating system loads. In older cases, Microsoft has described attackers installing an affected boot manager or policy, then using that trusted component to disable code integrity checks or bypass BitLocker validation. The pattern is familiar: exploit the fact that the boot chain is supposed to be trusted, then use a flawed trusted component against the platform itself.The problem is compounded by the fact that UEFI firmware ecosystems are fragmented. Even when Microsoft issues a fix, the system may also need firmware updates, DBX updates, boot manager replacements, or certificate rollovers before the protection is complete. Microsoft has explicitly documented that devices unable to receive the new 2023 Secure Boot certificates will lose the ability to receive future early-boot security updates, which means the ecosystem has a built-in dependency on maintenance discipline.
The trust chain in practice
The Secure Boot chain starts with firmware trust anchors, then moves into the boot manager, then into the OS loader and kernel integrity checks. If an attacker can bend one of those links, the protections downstream can become much less meaningful. That is why boot-loader flaws are so sensitive: they sit at the chokepoint where trust is established.Microsoft’s previous revocation stories also show why patching is not the end of the story. If vulnerable binaries remain signed and accepted, attackers can continue to use them even after the underlying code flaw is known. That is why DBX updates and certificate transitions matter as much as the CVE itself.
- A patched but still-trusted boot component can remain exploitable.
- DBX updates revoke known-bad artifacts in firmware trust stores.
- Certificate expiration can complicate the delivery of future revocations.
- Boot-chain security depends on both software updates and firmware hygiene.
- Legacy devices are at higher risk if they miss key maintenance milestones.
Why This Matters for Enterprises
For enterprises, CVE-2026-0390 is less about a single Windows patch and more about fleet integrity. A successful Secure Boot bypass can create persistent compromise that survives standard OS reimaging, undermines device compliance, and complicates incident response. If attackers can manipulate the boot path, they may gain a foothold that is harder to detect than kernel malware and harder to evict than user-mode implants.The risk is especially acute where BitLocker, Device Encryption, and compliance baselines depend on boot-chain trust. Microsoft has repeatedly noted that Secure Boot bypasses can interfere with integrity validation for those protections. That means the issue is not only about malware; it is also about the assumptions that make loss prevention, device attestation, and recovery workflows reliable.
Enterprise operational impact
IT teams should expect to treat this class of vulnerability as part of a broader firmware lifecycle problem. Devices may need the Windows update that fixes the flaw, a separate boot manager update, and, in some environments, certificate migration to the 2023 Secure Boot chain. Missing any one of those steps can leave the system in a partially protected state.There is also a reporting and detection challenge. Traditional EDR tools are strongest once the OS is running, but Secure Boot bypasses are designed to operate before those tools are in play. That means administrators need to rely more on firmware inventory, boot-event telemetry, compliance reports, and vendor guidance than on ordinary antivirus logic.
- Enterprise risk is concentrated in persistence and tamper resistance.
- Compliance exposure grows if devices miss the 2023 certificate transition.
- Recovery becomes harder when the boot path itself is untrusted.
- Incident response may require offline remediation or firmware intervention.
- High-value systems deserve priority because boot compromise multiplies downstream impact.
Consumer Impact and Real-World Exposure
For consumers, the immediate risk is narrower than for enterprise administrators, but it is still serious. Most home users will not be targeted by sophisticated boot-chain attacks, yet the consequences of a compromise can be severe because boot-level persistence is difficult to spot. If malware survives reinstall attempts or evades common security tools, the user experience becomes one of unexplained instability and repeated reinfection.The practical consumer issue is whether the device receives updates consistently. Microsoft’s guidance makes clear that the aging 2011 certificates are being replaced, and systems that fail to migrate may lose the ability to accept future revocations and protections. That means consumers who ignore firmware and Windows updates may unknowingly be carrying a shrinking security margin.
Home-user threat model
Most home users should think of CVE-2026-0390 as a reason to keep Secure Boot enabled and Windows fully updated. That sounds basic, but the most damaging boot-chain attacks tend to hit systems where patching is inconsistent or where users disable protections for convenience. The best defense for consumers is usually boring maintenance, not heroic incident response.There is also a psychological problem with Secure Boot issues: because they are invisible when everything is working, users underestimate their importance. The system boots, Windows loads, and nothing obviously looks broken. Yet the ability to trust that boot path is what underpins device encryption and higher-level protections.
- Keep Secure Boot enabled unless there is a documented reason not to.
- Apply Windows and firmware updates promptly.
- Avoid unofficial boot tools unless you understand the security tradeoff.
- Treat unexplained boot behavior as a potential warning sign.
- Back up important data before major firmware or trust-anchor changes.
The Certificate Expiration Problem
The Secure Boot certificate expiration timeline is a major part of the story. Microsoft says the current Microsoft Secure Boot certificates issued in 2011 begin expiring in June 2026 and expire by October 2026, while the newer 2023 certificates are intended to preserve long-term trust and revocation capability. That is a tight operational window for a mechanism that affects millions of devices and multiple generations of firmware.This matters because expired certificates can freeze the ecosystem in place. If a device cannot receive the new trust material, then future DBX updates and boot-chain mitigations may no longer land correctly, leaving it more exposed to newly discovered boot-level bugs. Microsoft says devices without the updated certificates will continue to boot and function, but they will lose the ability to receive new early-boot protections.
Why expiration changes the risk equation
Expiration is not a theoretical event in firmware security. It forces organizations to choose between upgrading trust infrastructure now or accepting less flexibility later when revocations are needed. That is why Microsoft is pushing certificate updates ahead of June 2026 rather than waiting for the deadline.The transition also creates potential compatibility issues, especially for older or custom-built systems. Microsoft’s guidance notes that devices manufactured since 2012 may have expiring versions of the certificates and need updates, which is a polite way of saying the installed base is broad and uneven. Broad, uneven fleets are where security timelines become operational projects rather than simple patches.
- 2011 certificates are beginning to expire in June 2026.
- Expiration runs through October 2026.
- Devices need the 2023 certificate chain to keep receiving future boot protections.
- The issue affects both consumer and enterprise devices.
- Firmware lag is now a security risk, not just an IT nuisance.
How This Fits Microsoft’s Broader Security Pattern
Microsoft has a long history of treating Secure Boot bypasses as a distinct class of vulnerability because they punch holes in a foundational control. Earlier advisories such as CVE-2016-3320, CVE-2016-3287, and CVE-2016-7247 all focused on flawed boot managers or policies being loaded and then used to weaken the system’s trust model. The pattern is remarkably consistent across the years: the flaw itself may be narrow, but the defensive value of the patched control is broad.Microsoft’s response pattern has also become more mature. Instead of merely fixing the local flaw, the company has leaned on blacklisting and revocation to prevent the vulnerable boot artifact from being trusted again. That approach is essential because boot-chain attackers often reuse signed components as long as the ecosystem still accepts them.
Security feature bypass as a category
Microsoft has historically used the security feature bypass label for issues that do not always look dramatic on their own but meaningfully weaken a defense layer. The company’s older blog posts explain that bypasses may not directly execute code, yet they still matter because they reduce the cost of later exploitation or persistence. CVE-2026-0390 fits that historical pattern well.The distinction is important because it changes how defenders should prioritize the bug. A traditional exploitable vulnerability often attracts attention because it is loud. A bypass vulnerability deserves attention because it quietly expands what other attacks can do. That multiplier effect is why these issues often age into major incident-response headaches.
- The vulnerability class is old, but the operational stakes are still rising.
- Microsoft has repeatedly relied on revocation as a fix strategy.
- Secure Boot bypasses often become enablers for other attacks.
- The boot chain is a trust boundary, not just a startup routine.
- The “feature bypass” label should not be mistaken for low importance.
Strengths and Opportunities
The good news is that Microsoft has not left defenders without a roadmap. The company has already documented the certificate transition, the Secure Boot revocation architecture, and the types of maintenance steps organizations need to take to stay protected. That gives administrators a chance to turn a vulnerability announcement into a broader firmware-hygiene project rather than a last-minute scramble.- Microsoft has a well-established revocation mechanism through DBX.
- The 2023 certificate chain provides a forward path.
- Security teams can fold this into existing firmware lifecycle management.
- The issue reinforces the value of defense in depth at boot time.
- Enterprises can improve posture by auditing Secure Boot state now.
- This is an opportunity to reduce legacy trust dependencies before June 2026.
- Clear Microsoft guidance makes large-scale planning more achievable than in past boot-related incidents.
Risks and Concerns
The main concern is that boot-level vulnerabilities are disproportionately valuable to attackers. A successful bypass can create persistence below the OS, complicate detection, and undermine the credibility of a device’s security state. In the worst cases, it can also interfere with the very mechanisms that should help recover the device, which is why these bugs often outlive the headline moment.The second concern is operational drift. Microsoft has made clear that certificate expiration in 2026 will limit the ability to apply future early-boot protections on devices that fail to migrate. That means organizations are not just patching a CVE; they are being asked to modernize a trust foundation under time pressure.
- Devices that miss updates may lose future boot-level revocations.
- Legacy systems may be harder to bring onto the 2023 trust chain.
- Boot bypasses can be used for persistence and tampering.
- Security tools may have limited visibility before the OS loads.
- Compatibility issues can slow down rollout in mixed hardware fleets.
- Users who ignore firmware prompts may remain exposed longer than they realize.
- Partial remediation can create a false sense of safety.
Looking Ahead
The next few months will be a test of how well the Windows ecosystem can coordinate around Secure Boot modernization. Microsoft’s warning about 2011 certificate expiration means the industry cannot treat firmware trust as an indefinitely renewable resource. At the same time, CVE-2026-0390 reinforces why revocation and certificate hygiene are not optional extras but core parts of the security model.What matters now is execution. Microsoft can publish the fix, but OEMs, IT departments, cloud operators, and end users still have to carry it through to every machine that matters. That is often where security stories stop being technical and start being organizational, because the last mile is where old hardware, custom images, and delayed maintenance all come back into view.
Items to watch
- Whether Microsoft issues additional guidance on revocation or affected boot components.
- How quickly OEMs and enterprises complete the 2023 certificate transition.
- Whether any public proof-of-concept or deeper technical analysis emerges.
- Whether related boot-chain vulnerabilities appear around the same trust boundary.
- How smoothly legacy devices handle the new Secure Boot certificate lifecycle.
In the end, CVE-2026-0390 is significant not because it is the loudest Windows bug of the month, but because it touches the trust machinery underneath everything else. Secure Boot failures are dangerous precisely when they are treated as niche problems, and the coming certificate expiration deadline ensures this one will have a life well beyond its initial patch cycle. If Microsoft, OEMs, and enterprise admins handle the transition carefully, the ecosystem can emerge stronger; if they do not, attackers will be waiting at the boot screen.
Source: MSRC Security Update Guide - Microsoft Security Response Center
Last edited: