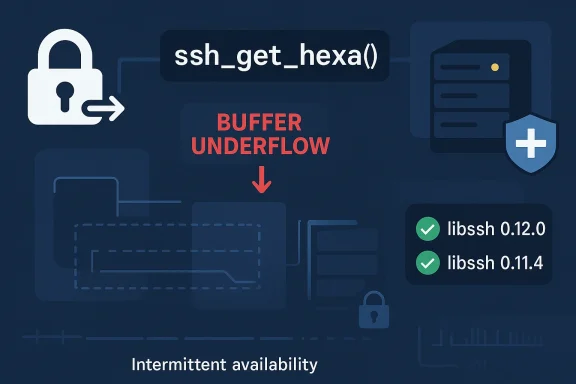
Performance degradation and intermittent interruption are the key operational consequences Microsoft records for CVE-2026-0966, a libssh issue caused by a buffer underflow in
libssh is not a niche component tucked away in a corner of the stack. It is a widely used SSH client and server library that underpins automation, file transfer workflows, bastion-host administration, embedded devices, and developer tooling, and the project itself notes major users such as GitHub, KDE, and Cockpit. That makes security findings in libssh especially relevant because a flaw in a parsing or helper routine can ripple into many products that inherit the library’s behavior. (libssh.org)
The specific function named in this CVE,
This is also not an isolated event. In the same February 2026 release note, libssh lists multiple security issues, including CVE-2026-0964, CVE-2026-0965, CVE-2026-0967, and CVE-2026-0968, plus an SFTP-related buffer overrun issue. That clustering suggests a broader hardening pass rather than a single bug fix, and it reinforces the reality that mature networking libraries still accumulate parsing hazards over time. (libssh.org)
For Windows administrators and enterprise security teams, the practical question is not just whether the bug exists, but what the failure mode means in production. Microsoft’s vulnerability guidance frames this issue as a condition where resources remain partially available or available only some of the time, which is less dramatic than a total outage but still significant for services that depend on reliable SSH-based workflows. In the real world, partial availability can be enough to break automation pipelines, stall deployments, or create confusing intermittent failures that are hard to diagnose. (libssh.org)
The naming of
A buffer underflow in a helper routine also tends to be a sign of input validation friction somewhere earlier in the call chain. The function itself may not be the only problem; it may simply be the place where incorrect assumptions finally become visible. In other words, the vulnerability is often as much about how data is prepared as it is about the final conversion step. That distinction matters for remediation, because patching the function is necessary but understanding the input path is what prevents recurrence. (libssh.org)
The release also introduced major feature additions, including post-quantum key exchange mechanisms, FIDO2/U2F support, sshsig signatures, and GSSAPI key exchange. That combination of new functionality and security remediation is common in open-source infrastructure projects: innovation and hardening move together, and the cost of supporting modern cryptography is often a larger code surface that must be defended carefully. (libssh.org)
The public release note shows the project backported the security fixes to both 0.12.0 and 0.11.4, indicating that current and previous supported branches were both covered. For administrators, that is the ideal outcome because it reduces the chance of version fragmentation leaving holes open across different environments. (libssh.org)
Consumer exposure is narrower but still relevant. Many end users never know libssh exists because they encounter it indirectly through applications, appliances, or services. If one of those products embeds libssh and processes untrusted SSH-related input, the consumer may see symptoms that look like connection failures, repeated retries, or a sluggish application rather than a clearly labeled security error. (libssh.org)
This is especially true in environments that chain SSH-based operations together. A failure in one library call can ripple into scheduled tasks, configuration management runs, or key-based authentication flows. The result can be a compounding delay: one flaky component slows the next, and the next error becomes harder to attribute to the original cause. Operationally, that is exactly how “limited availability” becomes expensive. (libssh.org)
This distinction is important for triage. Organizations often treat total service interruption as an emergency and everything else as a later task, but security teams should be careful not to underestimate “partial availability” issues. In high-availability environments, anything that undermines confidence in session handling can become a serious production incident even if the affected daemon stays nominally alive. (libssh.org)
There is also a strategic consideration. Attackers do not always need a dramatic exploit if a component can be prodded into periodic failure. Repeated low-grade disruption can be enough to interfere with monitoring, create false positives, or undermine trust in a platform. In that sense, availability degradation is a spectrum, not a binary. (libssh.org)
For vendors, the implication is straightforward: customers increasingly expect components to be patched quickly and quietly, with clear version mappings and minimal ambiguity. That is especially true when the library in question underpins infrastructure rather than a standalone app. Trust in the stack often depends less on feature lists than on how boring the security update process feels. (libssh.org)
That creates pressure on downstream vendors to keep pace. If a product line is still pinned to an older, unsupported, or slowly updated libssh fork, it may lag both on features and on safety. Over time, that lag becomes a market liability because enterprise buyers increasingly treat supply-chain security as part of the purchase decision. (libssh.org)
Longer term, the release underscores a persistent truth about infrastructure software: the security story is never finished, especially when the code base evolves to support new cryptographic standards and authentication methods. The challenge for maintainers is to keep broadening capability without letting parsing edges become attack surfaces. That balance is what separates durable platform software from merely functional code. (libssh.org)
Source: MSRC Security Update Guide - Microsoft Security Response Center
ssh_get_hexa() on invalid input. The vulnerability was fixed in the libssh 0.12.0 and 0.11.4 security releases published on February 10, 2026, where it appears alongside several other libssh flaws addressed in the same maintenance cycle. In Microsoft’s terms, the impact description points to a limited availability outcome rather than a full, clean denial-of-service condition, which matters for how defenders should prioritize it. (libssh.org)
 Overview
Overview
libssh is not a niche component tucked away in a corner of the stack. It is a widely used SSH client and server library that underpins automation, file transfer workflows, bastion-host administration, embedded devices, and developer tooling, and the project itself notes major users such as GitHub, KDE, and Cockpit. That makes security findings in libssh especially relevant because a flaw in a parsing or helper routine can ripple into many products that inherit the library’s behavior. (libssh.org)The specific function named in this CVE,
ssh_get_hexa(), is described in the public API documentation as a helper that converts a buffer into a colon-separated hex string. That sounds innocuous, but helper routines are often exactly where malformed input finds leverage: they sit close to data formatting, validation, and conversion logic, and they are sometimes called in edge cases that developers do not test as aggressively as protocol core paths.This is also not an isolated event. In the same February 2026 release note, libssh lists multiple security issues, including CVE-2026-0964, CVE-2026-0965, CVE-2026-0967, and CVE-2026-0968, plus an SFTP-related buffer overrun issue. That clustering suggests a broader hardening pass rather than a single bug fix, and it reinforces the reality that mature networking libraries still accumulate parsing hazards over time. (libssh.org)
For Windows administrators and enterprise security teams, the practical question is not just whether the bug exists, but what the failure mode means in production. Microsoft’s vulnerability guidance frames this issue as a condition where resources remain partially available or available only some of the time, which is less dramatic than a total outage but still significant for services that depend on reliable SSH-based workflows. In the real world, partial availability can be enough to break automation pipelines, stall deployments, or create confusing intermittent failures that are hard to diagnose. (libssh.org)
What CVE-2026-0966 Actually Is
At the technical level, the advisory label is straightforward: buffer underflow. That means the code reads or computes data as if a buffer extends farther than it really does, causing memory access before the intended start of the buffer. In C and C++ code, that can produce anything from harmless error paths to crashes, information disclosure, or undefined behavior, depending on how the surrounding logic is written. (libssh.org)The naming of
ssh_get_hexa() is important because it suggests the flaw lives in a utility conversion path rather than a full handshake state machine. That often lowers the chance of remote code execution but does not eliminate reliability risk. If invalid input can trigger the underflow repeatedly, a process may degrade, restart, or enter a fault loop even if the condition never becomes a full service blackout. (libssh.org)Why “invalid input” matters
The phrase invalid input is doing a lot of work here. It implies the attack surface may depend on malformed packets, corrupted state, or crafted data that causesssh_get_hexa() to receive unexpected content. That usually means defenders should focus on which front-end paths expose libssh to untrusted data, especially if the application accepts SSH traffic from unknown clients or processes externally controlled session material. (libssh.org)A buffer underflow in a helper routine also tends to be a sign of input validation friction somewhere earlier in the call chain. The function itself may not be the only problem; it may simply be the place where incorrect assumptions finally become visible. In other words, the vulnerability is often as much about how data is prepared as it is about the final conversion step. That distinction matters for remediation, because patching the function is necessary but understanding the input path is what prevents recurrence. (libssh.org)
Practical impact
Microsoft’s impact language indicates that the defect does not produce a complete denial of service in the classic sense. Instead, it can reduce performance or interrupt resource availability while leaving the impacted component at least partially usable. That is a subtler but still serious operational problem because intermittent instability is often harder to monitor and troubleshoot than a hard crash. (libssh.org)- The flaw is in a helper conversion function, not a headline protocol feature.
- The condition is tied to invalid input, which increases the value of robust parsing tests.
- The recorded impact emphasizes partial availability, not total outage.
- Repeated triggering may still meaningfully burden affected services.
How libssh’s Security Release Context Shapes the Story
The February 2026 release note is significant because it shows the project treating this issue as part of a broader security maintenance effort. AlongsideCVE-2026-0966, the same advisory bundle addresses traversal, denial-of-service, out-of-bounds read, and buffer overrun conditions. That broader context makes the release look like a comprehensive cleanup, not a narrow one-off fix. (libssh.org)The release also introduced major feature additions, including post-quantum key exchange mechanisms, FIDO2/U2F support, sshsig signatures, and GSSAPI key exchange. That combination of new functionality and security remediation is common in open-source infrastructure projects: innovation and hardening move together, and the cost of supporting modern cryptography is often a larger code surface that must be defended carefully. (libssh.org)
Security release cadence
libssh’s security process states that only supported versions are eligible for security releases, and that coordinated disclosure is handled through its security workflow. That matters because it gives defenders a rough framework for understanding why specific versions get patched and why older branches may not receive the same treatment. Supported version policy is not just administrative language; it defines whether a flaw is likely to be corrected upstream or must be mitigated downstream.The public release note shows the project backported the security fixes to both 0.12.0 and 0.11.4, indicating that current and previous supported branches were both covered. For administrators, that is the ideal outcome because it reduces the chance of version fragmentation leaving holes open across different environments. (libssh.org)
Why the cluster of fixes matters
When a release contains multiple memory-safety and parsing corrections, it often signals a period of concentrated audit work. That does not mean every issue shares the same exploitability, but it does imply that teams using the library should take the whole release seriously rather than cherry-pick a single CVE into a patching queue. In practice, bundled security fixes are often a better operational trigger than any one bug alone. (libssh.org)- The same release fixed multiple security issues.
- The project supports a formal security process for coordinated disclosure.
- Both the current and prior supported branches received backports.
- The release also shipped major feature expansion, increasing the importance of thorough regression testing.
Enterprise Risk Versus Consumer Exposure
For enterprises, the biggest concern is not whether a desktop user notices the issue directly. It is whether software built on libssh becomes intermittently unstable in automated environments, backup tools, CI/CD jobs, SFTP services, bastion gateways, or internal management systems. Those are the places where a partial availability issue can translate into real business disruption even if the underlying process does not fully crash. (libssh.org)Consumer exposure is narrower but still relevant. Many end users never know libssh exists because they encounter it indirectly through applications, appliances, or services. If one of those products embeds libssh and processes untrusted SSH-related input, the consumer may see symptoms that look like connection failures, repeated retries, or a sluggish application rather than a clearly labeled security error. (libssh.org)
Enterprise operational consequences
In enterprise environments, intermittent resource availability can be worse than an outright crash because it resists quick diagnosis. A service that fails only some of the time may trigger alert fatigue, hide behind retries, or appear as a network problem rather than a software flaw. That makes the patching priority depend not only on the CVE label but on the importance of the affected workload. (libssh.org)This is especially true in environments that chain SSH-based operations together. A failure in one library call can ripple into scheduled tasks, configuration management runs, or key-based authentication flows. The result can be a compounding delay: one flaky component slows the next, and the next error becomes harder to attribute to the original cause. Operationally, that is exactly how “limited availability” becomes expensive. (libssh.org)
Consumer-facing symptoms
For consumer-facing software, the issue may show up as a connection that hangs, a transfer that aborts, or a session that must be retried. Because the advisory does not describe total service loss, it is reasonable to expect annoying instability rather than catastrophic outage in many deployments. But “annoying” can still be unacceptable if the software is a gateway to user data or a device-admin interface. (libssh.org)- Enterprise users should look for automation failures and intermittent SSH instability.
- Consumer exposure is likely indirect, through embedded products.
- Partial availability problems are often harder to diagnose than crashes.
- Repeated retries can create the appearance of a network issue rather than a security defect.
What the Severity Language Suggests
Microsoft’s descriptive language matters because it points to a specific class of impact. The wording indicates that even when exploitation is repeatable, the attacker does not gain the ability to completely deny service to legitimate users. That suggests a bounded but real reliability hit rather than a full-service takedown. (libssh.org)This distinction is important for triage. Organizations often treat total service interruption as an emergency and everything else as a later task, but security teams should be careful not to underestimate “partial availability” issues. In high-availability environments, anything that undermines confidence in session handling can become a serious production incident even if the affected daemon stays nominally alive. (libssh.org)
Why limited-impact vulnerabilities still matter
Vulnerability management is not only about catastrophic exploitability. It is also about reliability debt, operational friction, and the cost of ambiguity when a service behaves unpredictably. A bug that only causes intermittent degradation can still consume engineering time, disrupt maintenance windows, and make incident response more difficult. That is a real business cost, not a theoretical one. (libssh.org)There is also a strategic consideration. Attackers do not always need a dramatic exploit if a component can be prodded into periodic failure. Repeated low-grade disruption can be enough to interfere with monitoring, create false positives, or undermine trust in a platform. In that sense, availability degradation is a spectrum, not a binary. (libssh.org)
Relationship to broader memory-safety issues
A buffer underflow belongs to the same family of memory-safety defects that have long troubled C-based infrastructure code. Open-source libraries remain especially exposed because they are reused across many products, and the same parser or helper may be called in contexts its original author never expected. The technical lesson is familiar but unavoidable: memory-safety issues in foundational libraries remain a recurring source of operational risk. (libssh.org)- The impact is bounded, but not trivial.
- The flaw can still create real production disruption.
- Availability bugs often generate hidden operational cost.
- Memory-safety problems in shared libraries remain a recurring pattern.
The Patch and Mitigation Picture
The good news is that the project has already issued fixed releases. The security advisory explicitly identifies libssh 0.12.0 and 0.11.4 as the releases containing the remediation, which is the most direct answer for teams tracking exposure. If your software vendor has repackaged libssh, though, the real patch may arrive through the vendor’s own update channel rather than from upstream directly. (libssh.org)What defenders should do first
- Identify whether any internal or third-party software embeds libssh.
- Determine whether those products expose SSH, SFTP, or related parsing paths to untrusted input.
- Check whether the vendor has shipped a patched build based on 0.12.0 or 0.11.4.
- Prioritize internet-facing or automation-critical systems first.
- Test for regressions, especially if the affected software is part of a bastion, transfer, or orchestration workflow.
Why patch testing still matters
Security updates for low-level libraries can create behavioral changes even when the intent is narrowly corrective. In libssh’s case, the release also includes numerous changes to features and compatibility, so environments that depend on older behavior should not assume a drop-in replacement will be perfectly invisible. Patching promptly is important, but so is testing against real workflows before pushing everywhere at once. (libssh.org)- Confirm embedded dependency status, not just direct installs.
- Verify the vendor has incorporated the upstream fix.
- Test for regressions in automation and transfer workflows.
- Treat external-facing SSH services as the first patching tier.
Competitive and Ecosystem Implications
libssh sits in a broader SSH ecosystem that includes other implementations and higher-level products built on top of them. When libssh ships a security release with multiple parsing and memory-safety fixes, it reinforces the competitive advantage of projects that can move quickly on hardening and backports. Security responsiveness is part of reputation now, not an afterthought. (libssh.org)For vendors, the implication is straightforward: customers increasingly expect components to be patched quickly and quietly, with clear version mappings and minimal ambiguity. That is especially true when the library in question underpins infrastructure rather than a standalone app. Trust in the stack often depends less on feature lists than on how boring the security update process feels. (libssh.org)
Why this matters beyond libssh
Open-source infrastructure libraries do not compete only on capability. They compete on maintenance quality, security cadence, and the ability to absorb modern requirements without destabilizing older deployments. The presence of post-quantum key exchange in the same release that fixesCVE-2026-0966 is a reminder that cryptographic modernization and security hygiene now travel together. (libssh.org)That creates pressure on downstream vendors to keep pace. If a product line is still pinned to an older, unsupported, or slowly updated libssh fork, it may lag both on features and on safety. Over time, that lag becomes a market liability because enterprise buyers increasingly treat supply-chain security as part of the purchase decision. (libssh.org)
The message to application developers
Application developers using libssh should take away one practical lesson: library upgrades are part of security posture, not just maintenance housekeeping. If you depend onssh_get_hexa() or any similar helper through an abstraction layer, you inherit the defect whether or not your code ever calls the function directly. The safest assumption is that every transitive dependency deserves a documented update path. (libssh.org)- Fast upstream response helps preserve ecosystem trust.
- Vendors that delay backports can become the weakest link.
- Security and feature modernization increasingly arrive together.
- Library upgrades should be treated as security controls, not optional chores.
Strengths and Opportunities
The upside here is that the issue is already publicly identified, upstream-fixed, and mapped to concrete release versions. That gives defenders something actionable, and it gives the ecosystem a chance to treat the incident as part of a mature maintenance cycle rather than an open-ended mystery. The broader libssh release also shows an active project improving both security and feature support at the same time, which is a healthy sign for infrastructure software. (libssh.org)- The fix is already available in 0.12.0 and 0.11.4.
- The project has a documented security process.
- Multiple adjacent bugs were addressed in the same release, reducing fragmentation.
- The issue is bounded enough to support targeted operational response.
- Teams can use the event to improve dependency inventory and patch discipline.
- The release shows continued investment in modern cryptography and feature evolution.
Risks and Concerns
The downside is that many organizations still lack a complete inventory of the libraries inside their software stack. That means a vulnerability like this can sit unnoticed until a vendor update, a crash report, or a runtime anomaly brings it to the surface. Because the effect is described as partial availability rather than total outage, the problem may also evade the kind of urgent response that more dramatic vulnerabilities receive. (libssh.org)- Embedded copies of libssh may be easy to miss.
- Intermittent failures can be misdiagnosed as network instability.
- Partial availability issues can persist longer than obvious crashes.
- Mixed-version environments may create patching inconsistency.
- Security teams may under-prioritize the flaw because it is not described as a total DoS.
- Feature-heavy maintenance releases can raise the risk of regression anxiety in downstream adopters.
Looking Ahead
The most likely near-term outcome is a routine but important cycle of downstream adoption. Vendors that package libssh will need to pull in the fix, retest their integrations, and explain whether their product is affected by thessh_get_hexa() underflow specifically or by the broader release train that contained it. In the best case, this becomes one more example of a security issue handled before it turns into a public incident. (libssh.org)Longer term, the release underscores a persistent truth about infrastructure software: the security story is never finished, especially when the code base evolves to support new cryptographic standards and authentication methods. The challenge for maintainers is to keep broadening capability without letting parsing edges become attack surfaces. That balance is what separates durable platform software from merely functional code. (libssh.org)
- Track whether your vendors have adopted 0.12.0 or 0.11.4.
- Audit embedded software for hidden libssh dependencies.
- Watch for follow-on advisories involving parsing or memory-safety bugs.
- Validate SSH-heavy automation after patching.
- Use the event to strengthen supply-chain and SBOM practices.
Source: MSRC Security Update Guide - Microsoft Security Response Center